Last Updated on March 13, 2026 by Snout0x
A public key is a cryptographic string derived from your private key that others can use to send you cryptocurrency. It is designed to be shared openly without compromising your security. Every crypto wallet generates a public-private key pair, and understanding how they relate is fundamental to grasping how crypto wallets actually work.
Disclaimer: This content is for educational and informational purposes only and does not constitute financial, investment, tax, or legal advice. Cryptocurrency markets are volatile and involve risk. Always conduct your own research and consult a qualified professional before making financial decisions.
Simple Definition
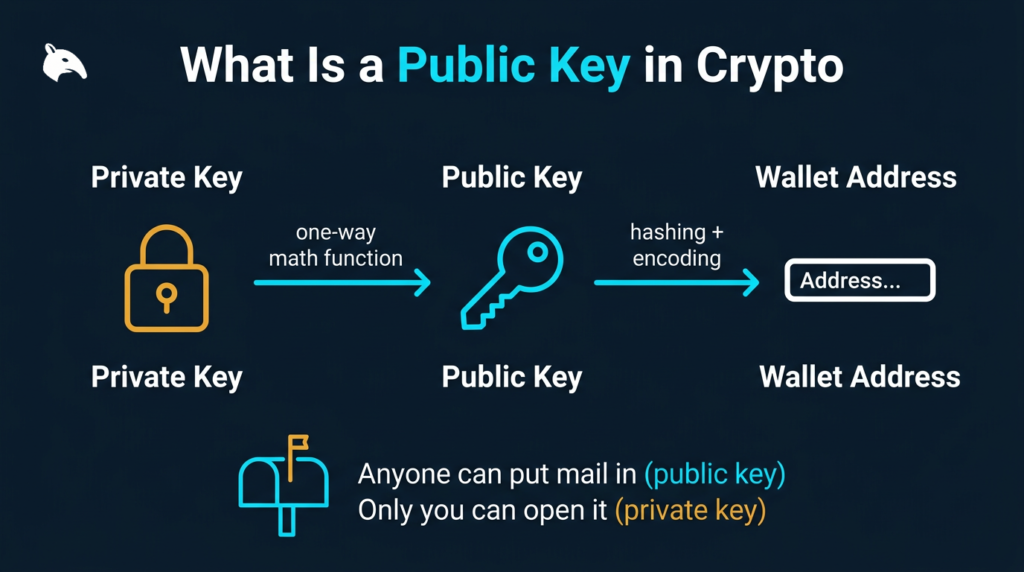
A public key is a large number generated using asymmetric cryptography. It is produced by running a private key through a one-way mathematical function, which means the public key can be shared freely while the private key remains secret.
Think of it like a physical mailbox. Anyone who knows your address can drop in a letter. Only you hold the key to open the box and retrieve what is inside. In this analogy, the mailbox slot is your public key. The key to open the box is your private key.
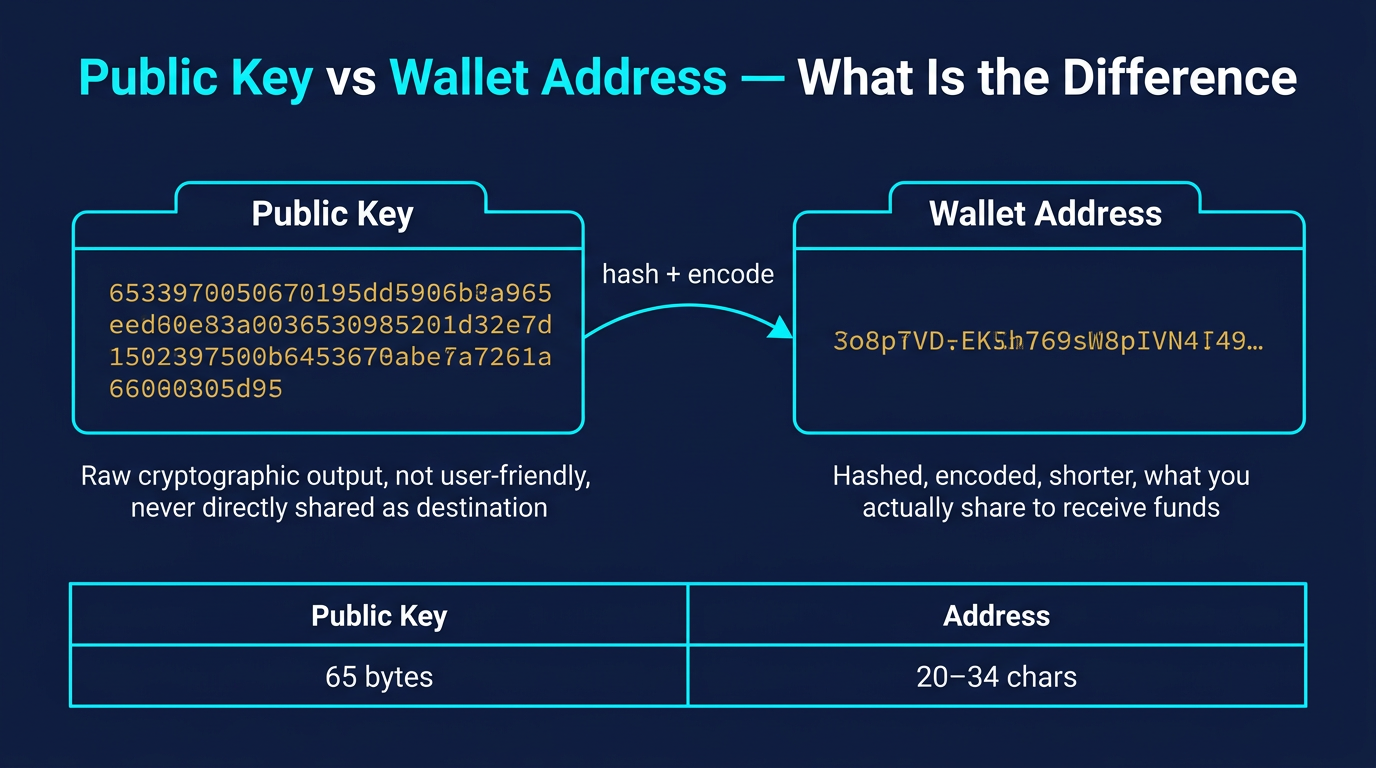
Public keys are also the basis for wallet addresses. A wallet address is not the same as a public key, but it is derived from one through a process of hashing and encoding. The two are mathematically linked, but they are different strings. Confusing them is one of the most common beginner mistakes.
Why It Matters
Public key cryptography solves a specific problem: how do two strangers transact on a public network without either one revealing sensitive information? Before asymmetric cryptography, secure communication required that both parties share a secret in advance. That is impractical at scale. Public key cryptography allows you to publish a receiving address without giving anyone the ability to spend your funds.
For crypto users, this has direct implications. When you share a wallet address to receive payment, you are sharing information derived from your public key. The sender can verify the transaction is valid without ever touching your private key. The blockchain confirms the transaction using cryptographic proof that links the spending signature back to the public key.
This architecture is also why self-custody is viable at all. You can hold your own keys, receive funds from anyone, and the system works without trusting an intermediary. The public key handles the receiving side. The private key handles authorization. Keep those roles clear and the logic of wallet security becomes much easier to follow.
How It Works
The process begins with a private key, which is a randomly generated 256-bit number. Bitcoin uses an elliptic curve called secp256k1. Running the private key through elliptic curve multiplication produces a public key. This operation is one-directional: someone who has your public key cannot reverse the calculation to retrieve your private key with current computing technology.
The public key is then processed further to produce a wallet address. Bitcoin applies SHA-256 followed by RIPEMD-160 hashing, adds a version byte and checksum, then encodes the result in Base58. Other blockchains use variations of this process, but the core derivation pattern is consistent: private key generates public key, public key generates address.
| Layer | What It Is | Can You Share It? |
|---|---|---|
| Private Key | Root secret for your wallet | Never |
| Public Key | Derived from private key via elliptic curve math | Yes |
| Wallet Address | Derived from public key via hashing and encoding | Yes |
Each layer is mathematically linked to the one before it. The chain of derivation is what makes the system secure. Understanding what a private key actually is gives full context for how this derivation chain works and why protecting the root matters so much.
Common Mistakes
The most common confusion is treating a wallet address and a public key as interchangeable. They are related but not the same. A wallet address is a shorter, encoded form derived from the public key. Sharing your wallet address does not directly expose your raw public key in most modern address formats, including Bitcoin’s SegWit addresses.
A second mistake is assuming that because something is called “public,” it carries no risk at all. Public keys are safe to share in terms of cryptographic security. But on fully transparent blockchains, anyone who links your public key or address to your real identity can trace your complete transaction history. Privacy and security are separate considerations, and both matter.
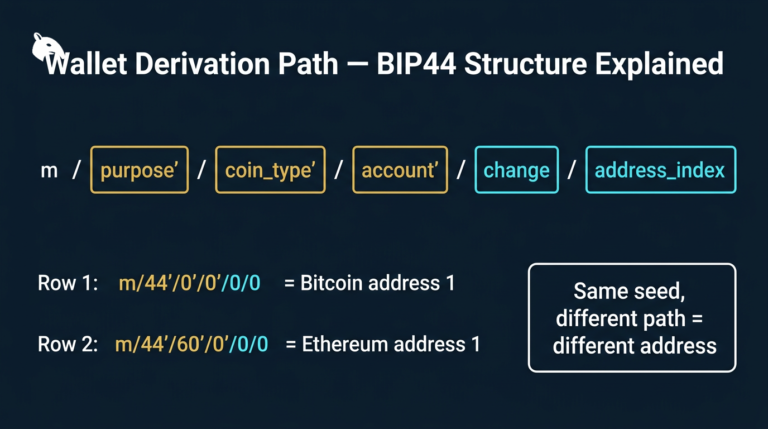
Some users also reuse the same wallet address for every transaction. This is technically functional but it reduces privacy. HD (hierarchical deterministic) wallets generate a fresh address for each transaction, which limits the ability to link transactions to a single owner over time. If privacy is a concern, address reuse is worth avoiding.
One less obvious mistake involves trusting wallet software without verifying it. A wallet that generates weak or predictable private keys produces compromised public keys regardless of how the key derivation math works. Always use reputable, audited wallet software from official sources.
Security and Risk Considerations
Public keys are designed to withstand current attack methods. There is no known practical technique that reverses elliptic curve multiplication to retrieve a private key from a public key. For the vast majority of users, the public key itself is not where the vulnerability lies.
The real risks sit elsewhere in the chain. If your private key or seed phrase is exposed, the public key becomes irrelevant. An attacker holding the private key can sign transactions and drain funds. This is why protection focuses on the private key, not the public key. The public key is safe to expose. The private key is not.
There is a theoretical long-term risk from quantum computing. Future quantum computers could potentially run Shor’s algorithm fast enough to break elliptic curve cryptography. This is not a present threat. The cryptography industry is tracking it, and post-quantum standards are under active development. For now, secp256k1 remains computationally secure.
One practical consideration worth noting is the combination of address reuse and identity exposure. On a transparent blockchain, a wallet address is permanent and public. If you publish a donation address or use the same receiving address repeatedly across public forums, anyone can audit every transaction associated with it. The funds themselves are not at risk, but the financial privacy is gone.
Keeping holdings in cold storage reduces exposure to software-layer attacks, but real security starts with understanding this derivation chain and protecting the root. For anyone evaluating where to store funds, the best crypto wallets for beginners covers the practical decision in full.
Frequently Asked Questions
Can someone steal my crypto using only my public key?
No. A public key cannot sign transactions or authorize spending. Only the corresponding private key can do that. Sharing your public key or wallet address does not give anyone access to your funds.
Is my wallet address the same as my public key?
No, but they are related. Your wallet address is derived from your public key through a hashing and encoding process. They are mathematically linked but are different strings. Most modern addresses do not expose the raw public key directly.
Can a public key be used to find the private key?
Not with current technology. The elliptic curve multiplication used to generate public keys from private keys is a one-way function. Reversing it is not computationally feasible with any hardware that exists today.
Does every transaction use the same public key?
It depends on the wallet type. HD (hierarchical deterministic) wallets generate a new address and corresponding key pair for each transaction to improve privacy. Non-HD wallets reuse the same address, which works but reduces privacy over time.
Is it safe to post my wallet address online?
Posting a wallet address does not compromise your funds. It does expose your full transaction history to anyone who looks, since most blockchains are publicly transparent. Consider the privacy implications before sharing a receiving address in public forums or social profiles.
—