Last Updated on March 13, 2026 by Snout0x
Last Updated: February 28, 2026 | Author: Snout0x
Hot vs cold wallets are no longer just a beginner debate. They are the foundation of crypto security in 2026. The way you store your private keys determines whether you truly control your assets or merely hope they remain safe. As exchange failures, browser-based wallet drains, and increasingly sophisticated phishing attacks continue to scale, choosing between hot storage and cold storage is not about convenience, it is about risk architecture.
Understanding this distinction is essential before deciding how to protect your holdings.
Affiliate Disclosure: Some links in this article may be affiliate links. If you choose to use them, I may earn a commission at no additional cost to you. Disclaimer: This content is for educational and informational purposes only and does not constitute financial, investment, tax, or legal advice. Cryptocurrency markets are volatile and involve risk. Always conduct your own research and consult a qualified professional before making financial decisions.
The debate between hot vs cold wallets is no longer academic. In 2026, exchange hacks are industrialized, AI-driven phishing is mainstream, and “Not Your Keys, Not Your Crypto” has gone from a slogan to a survival strategy. Whether you are a long-term holder or an active trader, where you store your private keys is the single most consequential security decision you will make.
Key Takeaways: The 2026 Security Baseline
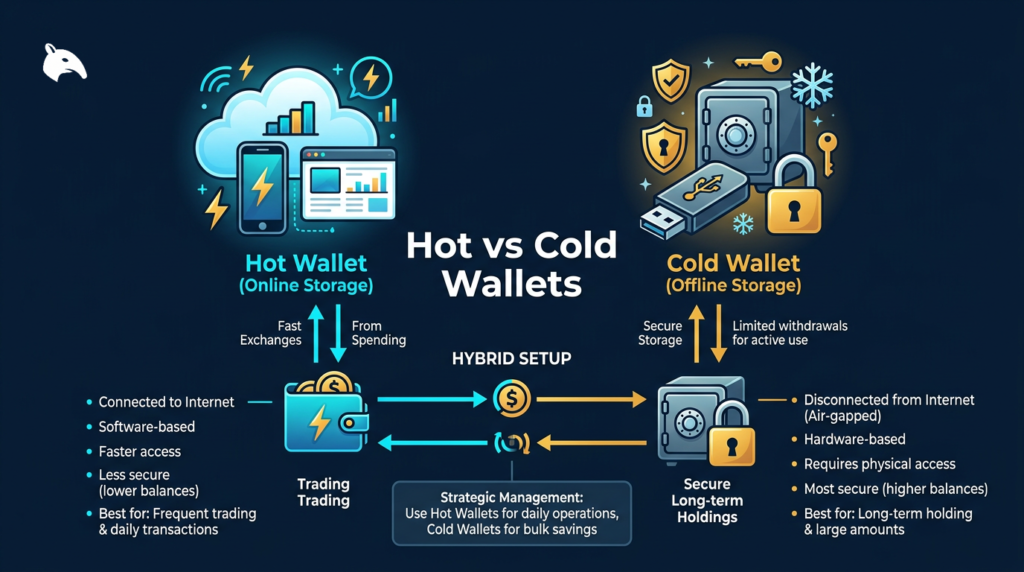
- Hot Wallets vs. Cold Wallets, the Core Difference: Hot wallets (MetaMask, Phantom) keep your private keys on an internet-connected device. Cold wallets (Ledger, Trezor, SafePal) keep them completely offline, making remote attacks physically impossible.
- The 90/10 Rule: Keep no more than 10% of your holdings in hot wallets for active use. The remaining 90% belongs in cold storage.
- Industrialized Threats: In 2026, the threat model has changed. AI-driven phishing, browser extension malware, and deepfake social engineering now target retail holders directly, not just exchanges.
- “Not Your Keys” Is Literal: Funds held on an exchange are not yours. They are an IOU. The Bybit hack in early 2025 drained $1.5 billion in a single afternoon through a third-party vendor compromise, not a direct vault breach.
- The Quantum Horizon: “Harvest Now, Decrypt Later” is an active threat model. Moving to quantum-resistant hardware today is forward-looking security, not paranoia.
The 2026 Reality Check: Why the Old Rules No Longer Apply
The security environment for crypto holders in 2026 is meaningfully different from even three years ago. Threats have scaled up in sophistication, automation, and reach.
In early 2025, the Lazarus Group orchestrated the Bybit hack, draining $1.5 billion in a single afternoon. They did not target the exchange’s primary vault directly. They compromised a third-party multi-sig vendor (Safe{Wallet}) and used social engineering to trick executives into approving what appeared to be routine transactions. The attack surface was human, not technical.
Separately, deepfake identity synthesis, which clones voice and face in real time, now accounts for a growing share of biometric fraud attempts. These tools are no longer expensive or inaccessible. They are available to organized criminal groups operating at scale, and they are being used specifically to bypass the support verification processes of crypto platforms.
If your primary defense is exchange-based 2FA or a browser hot wallet with a strong password, you are operating with tools designed for the threat model of 2019.
What Is Cold Storage?
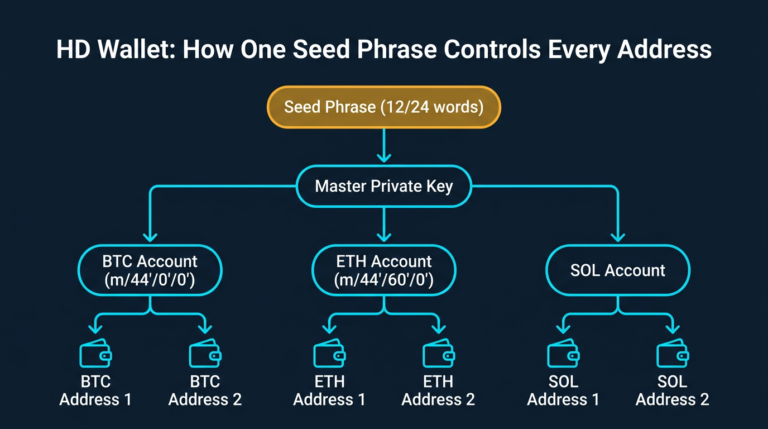
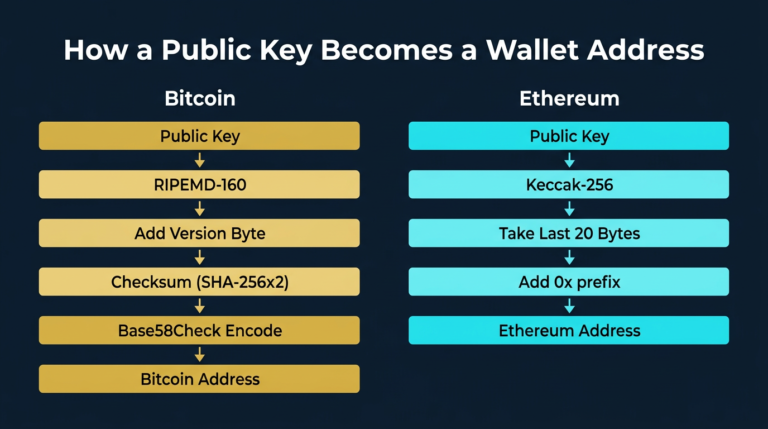
Cold storage means keeping your private keys, the cryptographic proof of ownership for your crypto assets, completely disconnected from the internet. When you use a hardware wallet, your private keys are generated inside a secure chip and never transmitted to any external network. This is the air gap.
Consider this analogy:
- A hot wallet is like carrying $100,000 in cash in a transparent bag through a crowded terminal. It is accessible and visible to everyone around you.
- A cold wallet is like keeping that same value inside a reinforced safe in an undisclosed location. Even if someone knows the safe exists, they cannot access the contents without your physical key and your direct involvement.
The distinction matters because, in a hot wallet, your private keys are stored in your browser’s local storage or on an internet-connected device by definition. In a cold wallet, they never leave the device’s secure element chip.
The Architecture of Isolation
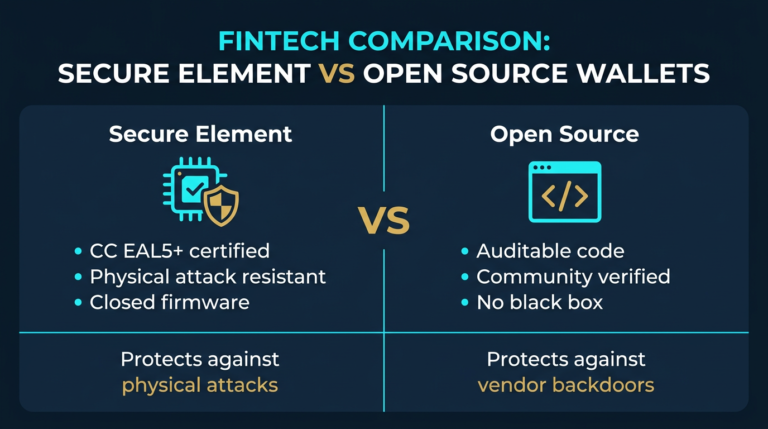
Modern cold storage hardware uses Secure Elements (SE), specialized silicon chips rated EAL5+ or EAL6+, designed to resist physical tampering and side-channel attacks. When you sign a transaction, your computer acts as a blind intermediary:
- The Request: Your computer sends the raw, unsigned transaction data to the hardware wallet.
- The Signing: The secure chip processes and signs the transaction internally, often running a false operation alongside the real one to confuse power-analysis attacks. Your private key never leaves the chip.
- The Return: Only the completed digital signature is sent back to your computer for broadcast.
Even on a fully compromised computer with active malware, an attacker cannot extract your private key through this process. They can see the transaction data. They cannot access the signing key.
Hot vs Cold Wallets: Why the Choice Matters Now
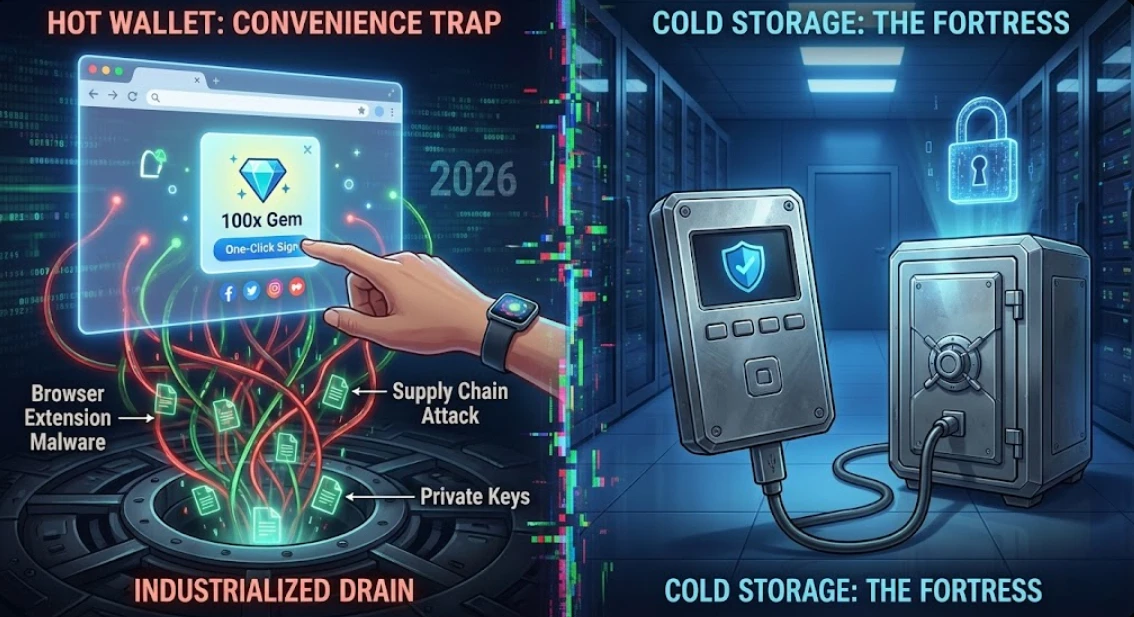
The Convenience Trap: Industrialized Drains
Hot wallets are genuinely useful. They integrate with dApps, DeFi protocols, and NFT platforms. The friction is low. The problem is that in 2026, browser extension malware has become the most common vector for wallet drains among retail holders — and the attacks have become structurally harder to detect.
The threat has evolved beyond obvious phishing links. Attackers are now running supply chain attacks — purchasing legitimate, well-reviewed browser extensions and pushing malicious updates through official Chrome and Firefox stores. A user who installed a popular productivity extension two years ago may have received a keylogger update specifically designed to target MetaMask credentials without any visible change in behavior.
In 2026, a technique called Extension Hollowing has been documented in the wild: a malicious script embedded inside a legitimate extension’s code, dormant until the user unlocks their wallet, at which point it transmits the mnemonic phrase to a remote server. The extension appears normal. The damage is already done.
Because hot wallets store private keys in browser local storage, no amount of password complexity prevents this class of attack. The key is accessible by design — that is the architectural weakness.
For a broader look at how common security habits compound risk over time, see: 5 “Safe” Crypto Habits That Will Get You Rekt.
The Sovereignty Shift: Protecting Against the Quantum Shadow
The most forward-looking hardware wallets in 2026 are integrating quantum-resistant cryptography. This may seem premature, but the threat model is not about today’s quantum computers — it is about a specific long-range attack strategy called Harvest Now, Decrypt Later (HNDL).
State-level actors and well-resourced criminal organizations are already archiving large volumes of encrypted blockchain data. Their operating assumption is straightforward: in 5–10 years, sufficiently powerful quantum computers will be able to run Shor’s Algorithm against ECDSA (Elliptic Curve Digital Signature Algorithm) signatures — effectively reverse-engineering private keys from publicly visible public keys on the blockchain.
If your cold wallet uses legacy ECDSA without a migration path, assets stored there today may be theoretically vulnerable in the future. NIST-standardized post-quantum algorithms such as ML-DSA and SLH-DSA provide a forward-compatible alternative. Wallets integrating these standards now are offering a genuine long-term security upgrade. For technical context, see the NIST Cryptography Division.

The Air-Gap Reality Check
True air-gapping goes further than simply disabling WiFi. Devices like the SafePal S1 have no Bluetooth, no WiFi, and no active USB data pins. All transaction signing happens via QR code exchange: your phone generates a QR code containing the unsigned transaction, the wallet’s camera reads and signs it offline, then displays a return QR code for your phone to scan and broadcast.
In a threat environment where zero-click exploits can compromise a smartphone through a received message without any user interaction, having a signing device that is physically incapable of network communication is a meaningful security property. It removes an entire class of remote attack vectors.
For a deeper look at what “air-gapped” actually means in practice: Cold Storage Paranoia: Is Your Wallet Actually Air-Gapped?
Common Mistakes in Hot and Cold Wallet Setups
Most holders who get compromised were not using bad tools. They made predictable operational errors. These are the most common:
- Storing your seed phrase digitally. Screenshots, cloud notes, password managers, and email drafts are all accessible to anyone who compromises your accounts. Your seed phrase belongs on paper or metal, stored physically offline, in more than one location.
- Using a hardware wallet but signing blind. If you approve every transaction prompt without reading the details, the hardware wallet’s protections are diminished. Always verify the transaction details on the device screen, not just on your computer. Malicious dApps can alter transaction parameters at the display layer.
- Keeping funds on exchange “temporarily.” The “I’ll move it to cold storage after this trade” habit compounds over months. Set a threshold rule and follow it. See: Exchange Withdrawals Will Pause Again.
- Buying hardware wallets from third-party marketplaces. A tampered device shipped through an unauthorized reseller is a documented attack vector. Always purchase directly from the manufacturer’s official website.
- Ignoring firmware updates. Security patches exist because vulnerabilities are found. A hardware wallet running outdated firmware may have known weaknesses that have since been closed. Check for updates regularly.
Risks to Understand Before Choosing Cold Storage
Cold storage shifts risk away from remote attackers and concentrates it in physical security and personal operational discipline. These are the trade-offs you are taking on:
- Seed phrase loss or destruction. If your 24-word recovery phrase is lost through fire, flood, or misplacement, your funds are permanently inaccessible. No company can recover them. Back up in at least two geographically separate, physically secure locations.
- Physical theft or coercion. A hardware wallet in the wrong hands combined with physical pressure is a real-world risk for high-value holders. Multi-signature setups and geographic distribution of seed phrase backups mitigate this.
- Supply chain compromise. Pre-tampered devices are rare but documented. Purchase only from manufacturer websites with tamper-evident packaging.
- Firmware vulnerabilities. No device is permanently immune to newly discovered exploits. Monitor manufacturer security disclosures and apply updates when available.
- User error at time of withdrawal. Phishing sites that mimic hardware wallet interfaces, including fake Ledger Live pages and fraudulent MetaMask update prompts, have caused losses even for experienced users. Always verify URLs independently before connecting your device.
The 2026 Cold Storage Arsenal: Top Hardware Wallets
Each of these devices has a distinct philosophy and use case. Choosing the right one depends on your security priorities, technical comfort level, and how frequently you transact.
Trezor Safe 7: Open-Source and Quantum-Ready
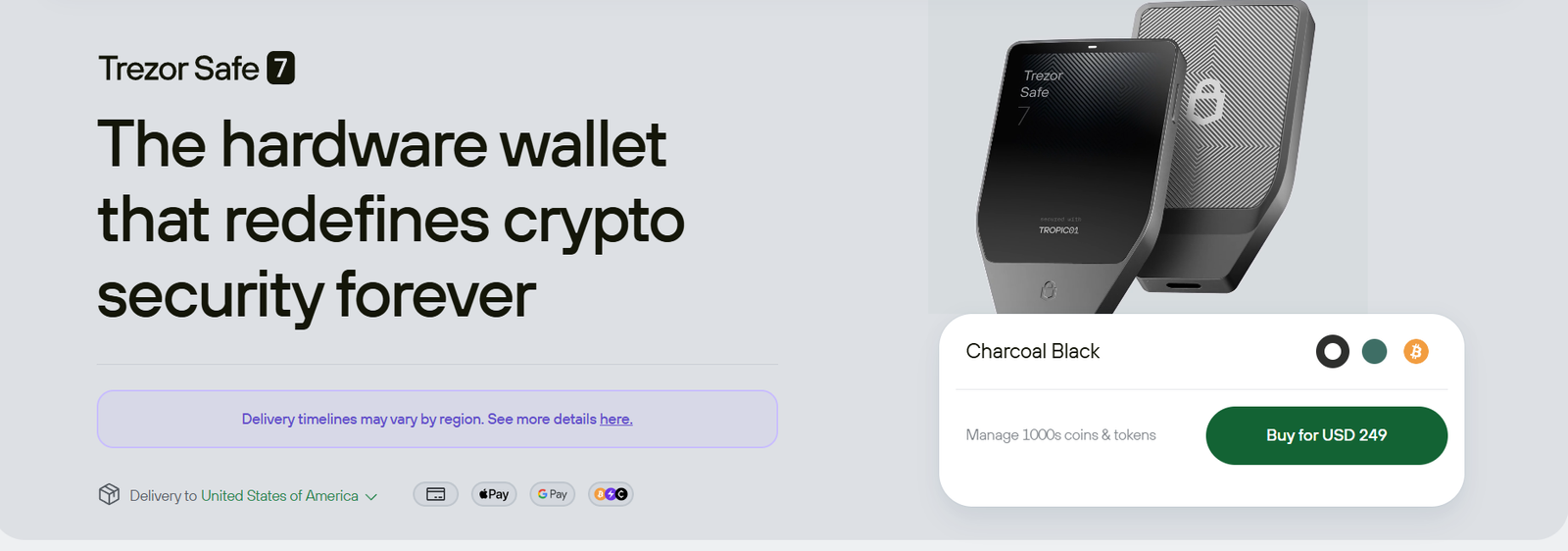
Trezor’s 2026 flagship is fully open-source — the entire codebase is publicly auditable by anyone. In an industry where “trust us” is the norm, this is a meaningful distinction. The Safe 7 introduced the TROPIC01 Secure Element, which addressed previous physical attack vulnerabilities while preserving Trezor’s full transparency model.
It also supports hybrid signature schemes aligned with post-quantum cryptography standards, making it one of the few consumer hardware wallets actively building against the HNDL threat described above. If long-term key security is your priority, this is currently the most credible option on the market.
- Best for: Long-term holders, Bitcoin-focused users, and anyone who prioritizes independently verifiable security.
- Trade-off: Smaller native altcoin ecosystem compared to Ledger’s Ethereum integration.
Buy the Trezor Safe 7 directly from Trezor | Full review: Trezor Safe 7 Review 2026
Ledger Nano X: The Altcoin and NFT Workhorse
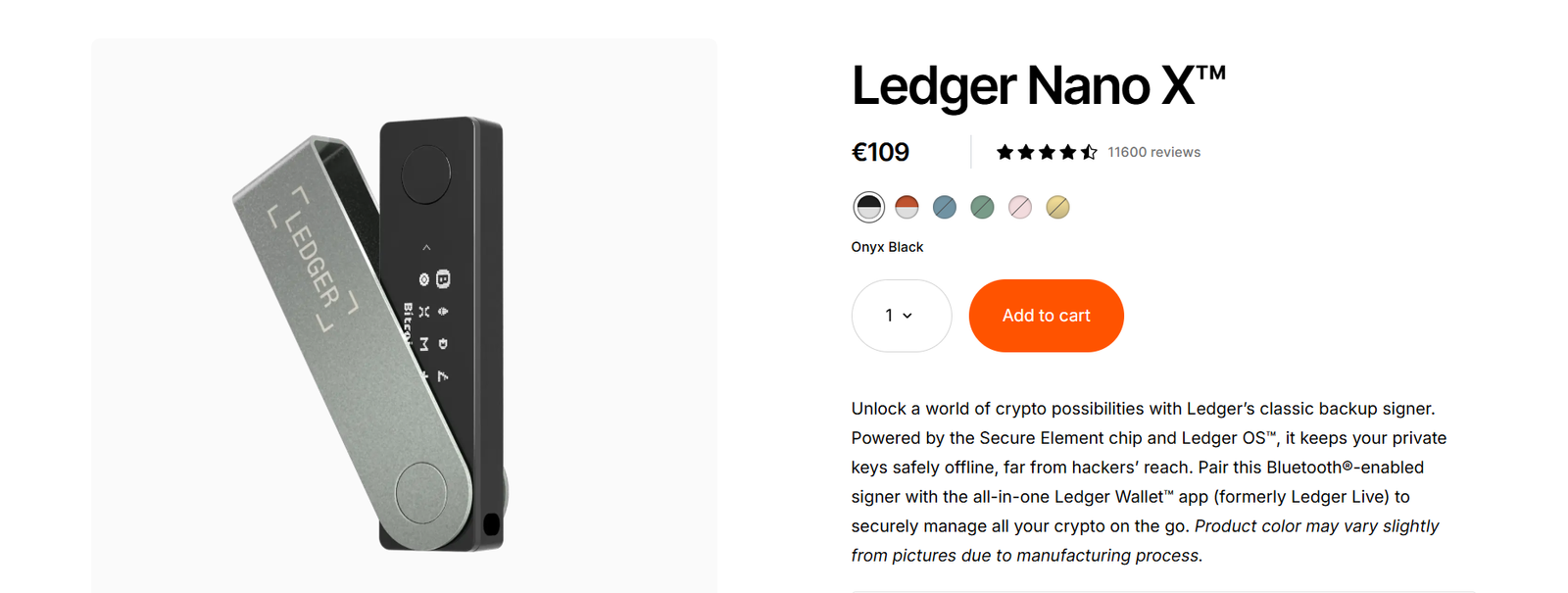
The Ledger Nano X remains the most widely adopted hardware wallet on the market, with broad support for Ethereum-based assets, NFTs, and DeFi protocols. Its Bluetooth connectivity and the Ledger Live app make it the most convenient option for active use across mobile and desktop.
The trade-off is transparency. Ledger uses a closed-source secure element. The hardware security is well-regarded, but independent code audits are not possible in the same way they are for Trezor. The 2026 Global-e breach was a compromise of a third-party payment processor, not the wallet hardware itself, but it resulted in user name and email exposure, increasing phishing risk for those affected. Ledger’s hardware security was not implicated.
- Best for: Active traders, NFT collectors, and users who need broad altcoin support with mobile integration.
- Trade-off: Closed-source firmware; corporate data exposure risk separate from hardware security.
Buy the Ledger Nano X directly from Ledger | Full review: Is Ledger Nano X Safe in 2026?
SafePal S1: Air-Gapped Cold Storage on a Budget
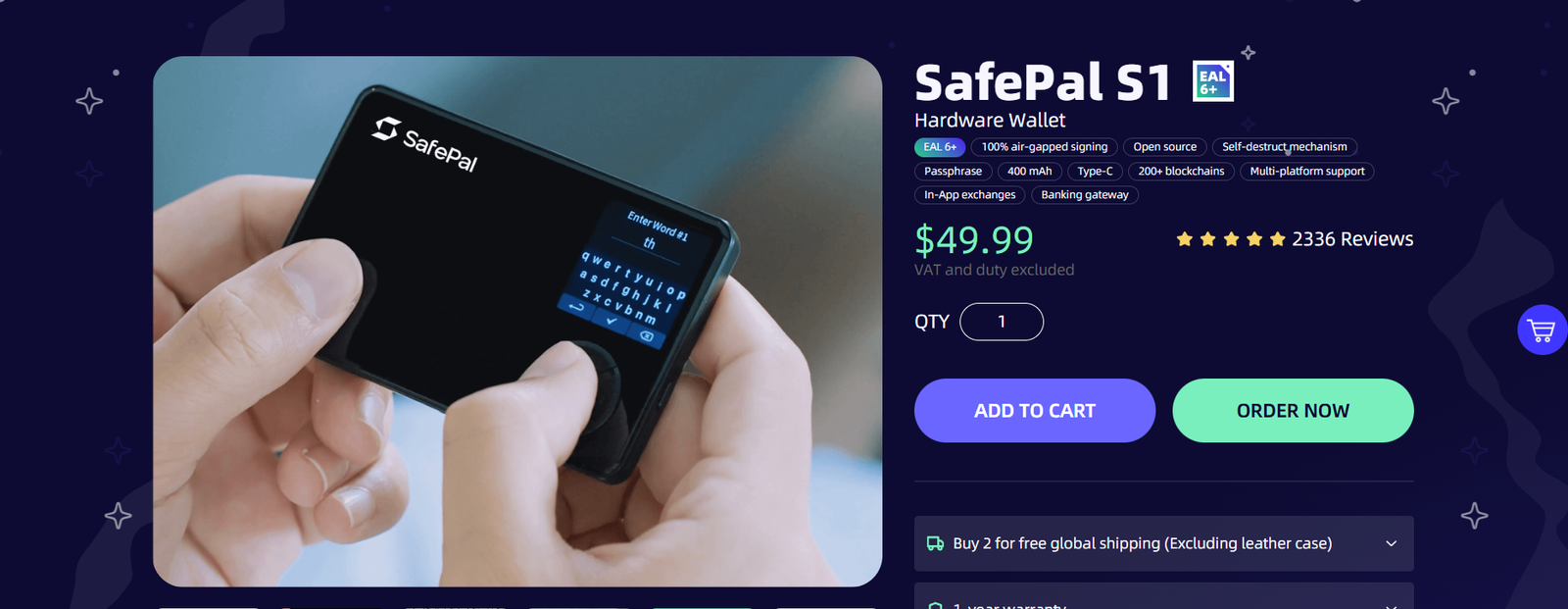
The SafePal S1 is the most aggressively air-gapped consumer hardware wallet available at this price point. It has no Bluetooth, no WiFi, and no functional USB data pins, only a charging connection. All transaction signing is done via QR code. If the device detects a physical tampering attempt, a self-destruct mechanism wipes the secure element.
For under $50, it delivers a security architecture that requires physical device compromise to have any meaningful attack surface. For security-conscious holders who transact infrequently, that is a strong value proposition.
- Best for: Budget-conscious users who want maximum air-gap security and rarely need to transact.
- Trade-off: QR code workflow is less practical for frequent trading. Not suited for active DeFi use.
Buy the SafePal S1 directly from SafePal | Full review: SafePal S1 Review 2026
Read Next
- Ledger Nano X vs. Trezor Safe 7: The 2026 Showdown. A full side-by-side comparison of the two leading hardware wallets.
- 7 Essential Crypto Tools 2026. The tools actually worth using for security, taxes, and trading.
- Best Crypto Wallets for Beginners 2026. If you are new to self-custody, start here.
- Mobile Wallet Security 2026: 5 Critical Risks. Why your phone wallet needs more protection than you are giving it.
- Best Crypto Passive Income 2026. How to earn yield without exposing your cold storage holdings.
Follow on X: @Snout0x for security updates and weekly analysis.
FAQ
Is a hot wallet really that dangerous?
It depends on how you use it. For small amounts used in active trading or DeFi interaction, hot wallets are a reasonable operational tool. For long-term holdings or significant value, they are a structural risk — your private keys are stored in an internet-connected environment, permanently accessible to any successful attack on your browser, device, or installed extensions. Use hot wallets for operational funds only, not as a primary store of value.
Can I use a hardware wallet and still get hacked?
Yes — but the attack vector shifts entirely to social engineering and physical access. If you enter your 24-word seed phrase into a phishing site, or approve a malicious transaction without reading the device screen, no hardware can prevent the loss. The device protects the private key from remote extraction. Your own discipline protects everything else.
What happened in the 2026 Ledger data breach?
The breach involved Global-e, a third-party payment processor used by Ledger, not Ledger’s hardware or firmware. User names, email addresses, and shipping information were exposed. Wallet funds and private keys were not at risk. However, affected users became targets for phishing campaigns using the compromised personal data. Ledger’s hardware security was not implicated.
Why is the Trezor Safe 7 more expensive than the Safe 3?
The Safe 7 includes the TROPIC01 Secure Element with quantum-resistant signature support, a color touchscreen, and the infrastructure for hybrid post-quantum cryptography. The Safe 3 is a capable entry-level device. The Safe 7 is the long-term option for users who want hardware that remains relevant as the cryptographic threat environment evolves over the next decade.