Last Updated on April 13, 2026 by Snout0x
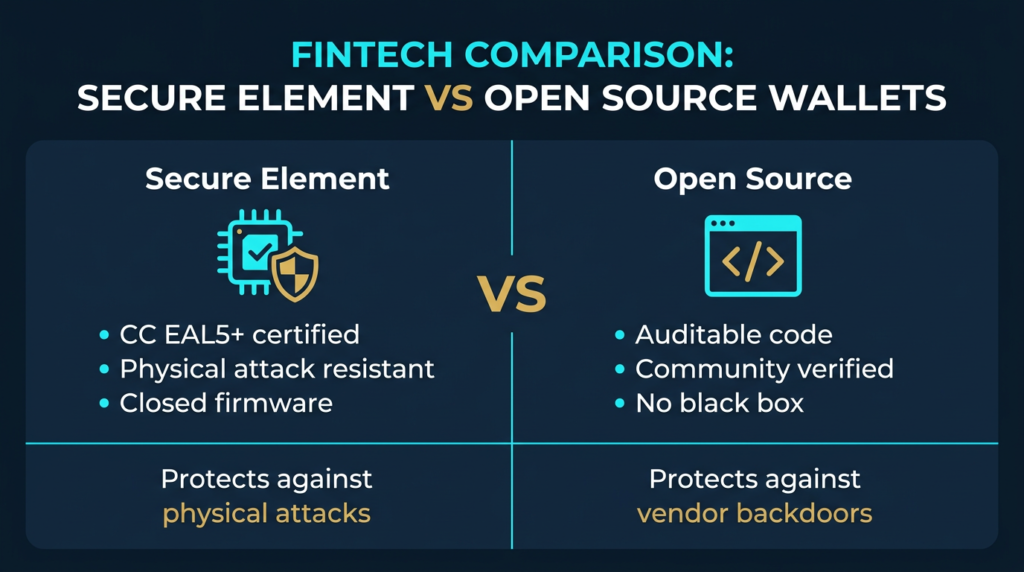
Hardware wallet security sits on two competing philosophies. Secure element wallets embed a certified tamper-resistant chip that stores and processes private keys in complete hardware isolation , an attacker with physical access to the device still cannot extract the key material. Open-source wallets take a different approach: every line of firmware code is publicly available, auditable by anyone, and verifiable against what the manufacturer claims the device actually does. Both approaches have real security credentials. Neither is universally superior. The right choice depends on which threat matters more to you, and this article explains the secure element vs open source trade-off clearly, without oversimplifying either side.
This content is for educational purposes only and should not be considered financial or investment advice.
Disclaimer: This content is for educational and informational purposes only and does not constitute financial, investment, tax, or legal advice. Cryptocurrency markets are volatile and involve risk. Always conduct your own research and consult a qualified professional before making financial decisions.
Affiliate Disclosure: Some links in this article may be affiliate links. If you choose to use them, I may earn a commission at no additional cost to you.
Key Takeaways
- Secure element wallets store private keys inside a tamper-resistant chip certified to resist physical extraction attempts.
- Open-source wallets allow anyone to audit the full firmware codebase and verify no hidden functionality exists.
- Secure elements provide stronger physical attack resistance; open-source firmware eliminates the risk of hidden manufacturer backdoors.
- Some modern wallets now combine both: a certified SE for physical protection alongside fully open firmware for auditability.
- Your threat model , physical theft versus software trust , should drive which design you prioritise.
What Is a Secure Element Wallet?
A secure element (SE) is a dedicated microchip designed specifically to store sensitive cryptographic material and perform cryptographic operations in complete hardware isolation. Unlike standard memory chips, an SE has its own isolated processor, RAM, flash storage, and cryptographic accelerator. All private key operations , generation, storage, and signing , happen entirely inside the chip. The raw private key never leaves it.
Secure elements used in hardware wallets are certified under the Common Criteria (CC) security evaluation framework, typically to EAL5+ or EAL6+ level. These certifications require independent laboratory testing to confirm the chip resists physical attacks including voltage glitching, electromagnetic probing, and side-channel analysis. The certification process is not marketing , it documents specific attack classes the chip has been tested against and confirmed to resist.
In a hardware wallet with a secure element, the signing flow works like this: you initiate a transaction on your computer, the unsigned transaction data is sent to the wallet, the SE signs it internally using the stored private key, and only the completed signature is returned. Your private key never moves outside the chip boundary at any point in this process.
The trade-off is transparency. The firmware running inside a secure element is almost always proprietary. The chip manufacturer controls the SE operating system and users cannot independently audit what happens inside it. This creates a trust dependency: you must trust that the certified chip behaves exactly as its documentation and certification claims , and that no undisclosed capability exists inside the closed firmware.
Ledger is the most widely deployed example of this model. Its devices use a dual-chip architecture: a general-purpose microcontroller (MCU) handles the user interface and communication, while a certified ST33 secure element handles all private key operations. The SE firmware is closed-source. The MCU firmware is open-source. For a full breakdown of the Ledger security architecture, see the Ledger Nano X security analysis.
What Is an Open-Source Hardware Wallet?
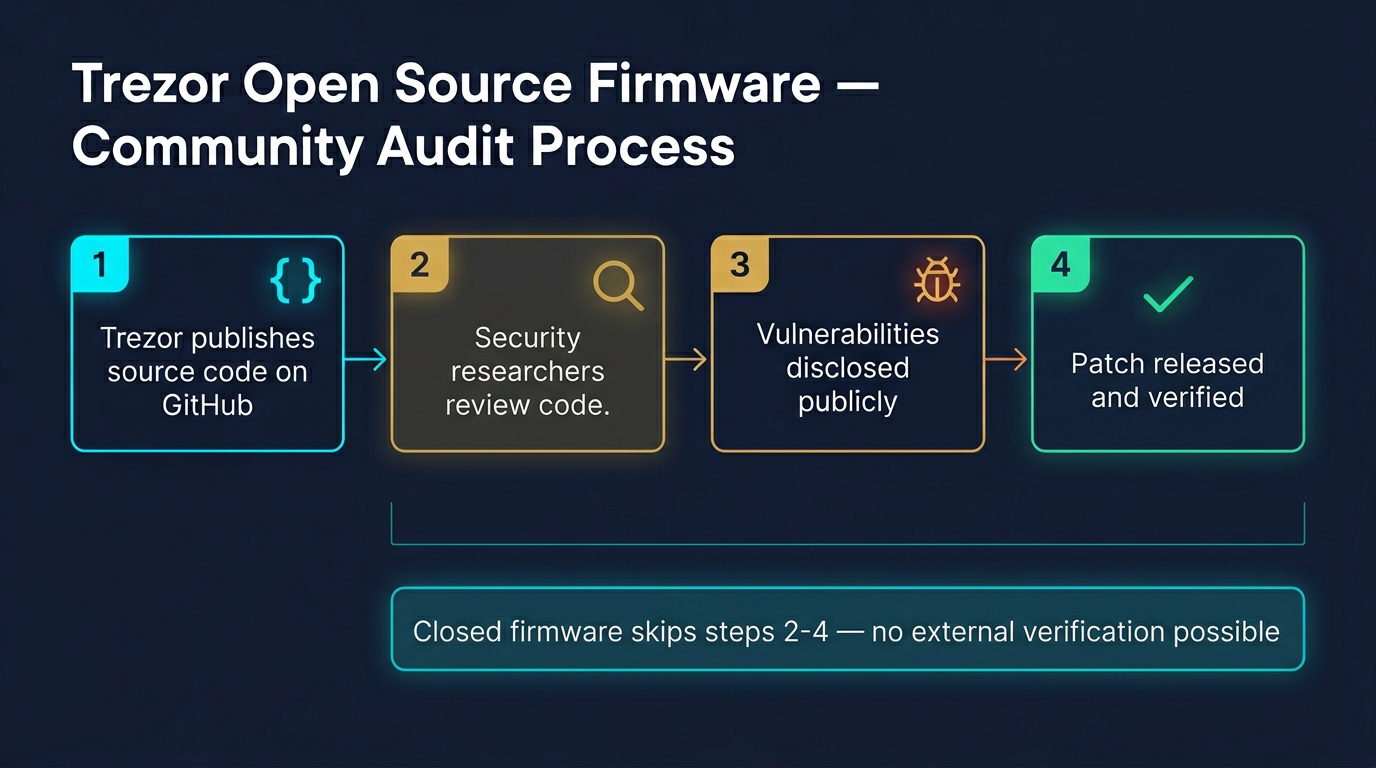
An open-source hardware wallet publishes its complete firmware codebase publicly , typically on GitHub , so that anyone can read it, compile it independently, and verify that the firmware running on the device is exactly what the manufacturer claims it to be. This is the core security argument for open-source: you do not have to trust the manufacturer, because you can verify.
Independent security researchers, cryptographers, and developers can audit open-source firmware for vulnerabilities, hidden functionality, or logic that deviates from what the device is supposed to do. When bugs are found, the community can report them publicly. When fixes are made, anyone can verify the patch is complete and correct.
Trezor built its reputation on this model. The original Trezor One and Model T were fully open-source from firmware to hardware schematics, with no secure element chip. Anyone could verify everything the device did. The limitation was physical attack resistance , without a certified SE, a sufficiently skilled attacker with physical access to the device could attempt to extract key material through hardware attacks on standard microcontroller memory.
BitBox02 by Shift Crypto takes a similar approach: fully open-source firmware and hardware design, published documentation, and a strong community audit history. Both Trezor and BitBox02 represent the purest form of the open-source model , verifiable by anyone willing to look.
The Core Security Trade-Off
The tension between secure elements and open-source firmware comes down to two distinct attack classes: physical attacks and trust attacks.
A physical attack involves an adversary gaining physical possession of the hardware wallet and attempting to extract key material through hardware techniques , voltage glitching, microprobing, or cold boot attacks on flash memory. Secure elements are engineered and certified specifically to resist these methods. Open-source wallets running on standard microcontrollers are more vulnerable here, because standard MCU flash memory was not designed with the same extraction resistance requirements.
A trust attack involves the manufacturer , or a state actor that has coerced the manufacturer , including hidden functionality in the firmware that allows private key extraction under specific conditions. Open-source firmware eliminates this risk by making the entire codebase publicly verifiable. A closed secure element cannot be fully audited, which means users must trust that the certified behaviour matches the actual behaviour.
Neither threat is theoretical. Hardware wallet theft and supply chain interception are documented attack vectors. And in 2023, Ledger’s closed SE architecture drew widespread criticism when the company announced a key recovery feature , demonstrating that the closed SE firmware had always contained the architectural capability to export key material, even though users had assumed the hardware guarantee made this impossible. The controversy did not prove Ledger was malicious, but it proved that a closed SE provides a trust guarantee only as strong as the manufacturer’s commitment to using it correctly.
Physical Attack Resistance: Where Secure Elements Win
If your threat model includes physical theft , a device lost, seized, or physically inspected by a sophisticated attacker , secure element architecture provides a meaningful and certified advantage.
Common Criteria EAL5+ and EAL6+ certifications require independent lab testing against specific attack scenarios. A certified SE chip has been evaluated against voltage fault injection, electromagnetic side-channel attacks, and optical probing. These tests are performed by accredited third parties and the results are published in certification reports. This is materially different from a standard microcontroller that was never designed to resist active physical attack.
In practice, most hardware wallet users are not facing adversaries with laboratory-grade chip analysis equipment. But for high-value holdings, long-term cold storage, or environments where device seizure is a realistic risk, the physical protection of a certified SE changes the calculus significantly. The attacker must defeat a certified, lab-tested, tamper-resistant chip , not just read flash memory from an off-the-shelf MCU.
For a broader look at how cold storage protects against physical and remote attacks, see the guide to cold storage in crypto.
Code Transparency: Where Open Source Wins
The security argument for open-source firmware is that trust should not be required. If every line of code is publicly auditable, users do not need to believe the manufacturer’s claims , they can verify them, or rely on the community of researchers who have done so.
This matters because hardware wallet security is only as strong as the firmware running on the device. A signed transaction that is generated correctly by audited firmware is trustworthy. A signed transaction generated by unaudited proprietary firmware is trustworthy only to the extent you trust the manufacturer. These are meaningfully different guarantees.
Open-source firmware also provides reproducibility. With sufficient tooling, a developer can take the published source code, compile it independently, and verify that the compiled binary matches what the manufacturer ships. This eliminates the risk that the manufacturer ships firmware that differs from what they publish. Closed-source firmware cannot provide this guarantee.
The limitation is that open-source provides no guarantee of code quality on its own. Publicly auditable code is only more secure if people actually audit it. Well-resourced open-source projects with active security research communities , like Trezor and BitBox02 , benefit from meaningful external scrutiny. A smaller open-source project with minimal community engagement gets the theoretical benefit of auditability but limited practical benefit.
Can You Have Both?
The secure element vs open source trade-off is not absolute. Several wallets now combine a certified SE with open-source firmware, attempting to capture the physical protection advantage of hardware certification alongside the transparency advantage of publicly auditable code.
The Trezor Safe series (Safe 3, Safe 5, Safe 7) incorporates a certified secure element used for PIN protection and key wrapping, while the main application firmware remains fully open-source. This is a meaningful architectural improvement over the original Trezor models. The SE does not handle all signing operations independently, but it raises the barrier for physical PIN bypass attacks significantly. The auditable firmware still governs what the device actually does with key material.
Keystone‘s hardware wallets take a similar hybrid approach, using a secure element alongside a fully open-source firmware model. For users who want the physical security guarantees of certified hardware without conceding code transparency, these hybrid architectures represent the current state of the art.
It is worth noting that no hybrid architecture eliminates all trade-offs. When an SE is present and its internal firmware is proprietary , even if the surrounding application firmware is open , there remains a trust boundary around the SE chip itself. The hybrid models reduce this boundary significantly compared to a fully closed SE wallet, but they do not eliminate it entirely.
Security Architecture Comparison
| Security Property | Secure Element (e.g. Ledger) | Open Source (e.g. original Trezor, BitBox02) | Hybrid (e.g. Trezor Safe, Keystone) |
|---|---|---|---|
| Physical attack resistance | High , certified against hardware extraction | Lower , standard MCU flash is more accessible | High , SE covers PIN and key wrapping |
| Firmware auditability | Partial , MCU open, SE closed | Full , all code publicly verifiable | Partial to full , depends on SE scope |
| Backdoor risk | Low but unverifiable in SE | Low , visible in published code | Low , SE scope is limited |
| Supply chain tamper detection | Attestation via SE | Varies , some use MCU attestation | SE-based attestation available |
| Independent reproducibility | MCU firmware only | Full reproducibility possible | Application layer reproducible |
| Common Criteria certification | Yes (CC EAL5+ or EAL6+) | Not typically required or sought | Yes for SE component |
Which One Should You Choose?
The honest answer is that the right hardware wallet depends on your threat model, not on which specification sounds most impressive in a comparison table.
If you are primarily concerned about physical theft or seizure , you travel frequently, store significant value, or operate in environments where confiscation is a realistic risk , a secure element wallet provides meaningful certified hardware protection that open-source-only wallets currently do not match. The certified chip has been independently tested against the attack methods most relevant to this scenario.
If you are primarily concerned about manufacturer trust and hidden firmware capabilities , you distrust closed systems on principle, or you have specific reasons to be concerned about vendor-side access to key material , an open-source wallet with fully auditable firmware addresses this concern directly. You can verify what the device does. No equivalent guarantee is possible with closed SE firmware.
If both concerns are relevant , and for most serious self-custody users they should be , a hybrid architecture that combines a certified SE with open-source application firmware represents the most complete approach currently available. The Trezor Safe series achieves this within the Trezor ecosystem. It is not a perfect solution, but it addresses both attack classes more completely than either pure approach does alone.
For a complete evaluation of hardware wallet options including security rankings, coin support, and price tiers, see the Best Crypto Hardware Wallets security ranking and buyer guide. For a direct head-to-head comparison of how Ledger and Trezor implement these architectural decisions in practice, see the Ledger vs Trezor security model comparison.
What Secure Element vs Open Source Does Not Settle
It is worth being clear about what this debate does not resolve. Neither a certified SE nor open-source firmware protects you from the most common causes of crypto loss: signing a malicious transaction without reviewing it carefully, storing seed phrases insecurely, using a compromised device for setup, or falling for social engineering that tricks you into authorising a legitimate-looking but malicious transaction.
Hardware wallet security architecture is one layer of a complete self-custody security practice. A well-implemented self-custody setup also includes secure seed phrase storage, disciplined transaction verification habits, and a clear understanding of which approvals you are authorising and why.
The secure element vs open source question matters for the hardware layer. The hardware layer is important. But it does not substitute for the operational practices that govern how you use the device day to day.
FAQ
Is a secure element always more secure than open-source firmware?
Not in every scenario. A secure element provides stronger physical attack resistance because the chip is certified against hardware extraction methods. But open-source firmware provides better protection against hidden manufacturer backdoors, because all code is publicly verifiable. The relative advantage depends on which threat class is more relevant to your situation.
Can a hardware wallet have both a secure element and open-source firmware?
Yes. Several modern wallets use this hybrid approach. The Trezor Safe series uses a certified SE for PIN and key wrapping protection while keeping the main application firmware fully open-source. Keystone takes a similar approach. These architectures reduce , though do not fully eliminate , the trade-off between hardware certification and code transparency.
Does open-source firmware mean the wallet has been audited?
Not automatically. Open-source firmware means the code is auditable, not that it has been audited. Well-maintained projects like Trezor and BitBox02 benefit from active security research communities and documented audit histories. A smaller project with published code but minimal community engagement gets less practical security benefit from being open-source, even though the theoretical guarantee is the same.
What does the Ledger Recover controversy tell us about secure elements?
The 2023 Ledger Recover announcement revealed that the closed SE firmware architecture had the architectural capability to export encrypted key shards , a capability many users assumed was impossible given the hardware design. It did not prove Ledger was acting maliciously, but it demonstrated that a closed SE provides a trust guarantee only as strong as the manufacturer’s commitment to how the chip is used. It is a concrete example of why SE firmware transparency matters alongside hardware certification.
Which hardware wallet design is best for most people?
For most retail users, a hybrid architecture , a certified SE combined with open-source application firmware , provides the most complete security posture currently available. If the choice is between a pure SE wallet and a pure open-source wallet, consider your primary threat. Physical theft risk points toward SE. Concerns about vendor trust point toward open source.
Sources
- OWASP Cryptographic Storage Cheat Sheet , cryptographic storage security principles
- MIT Digital Currency Initiative , independent cryptocurrency and cryptographic security research
- Bitcoin Developer Documentation , key management and transaction signing fundamentals