Last Updated on March 13, 2026 by Snout0x
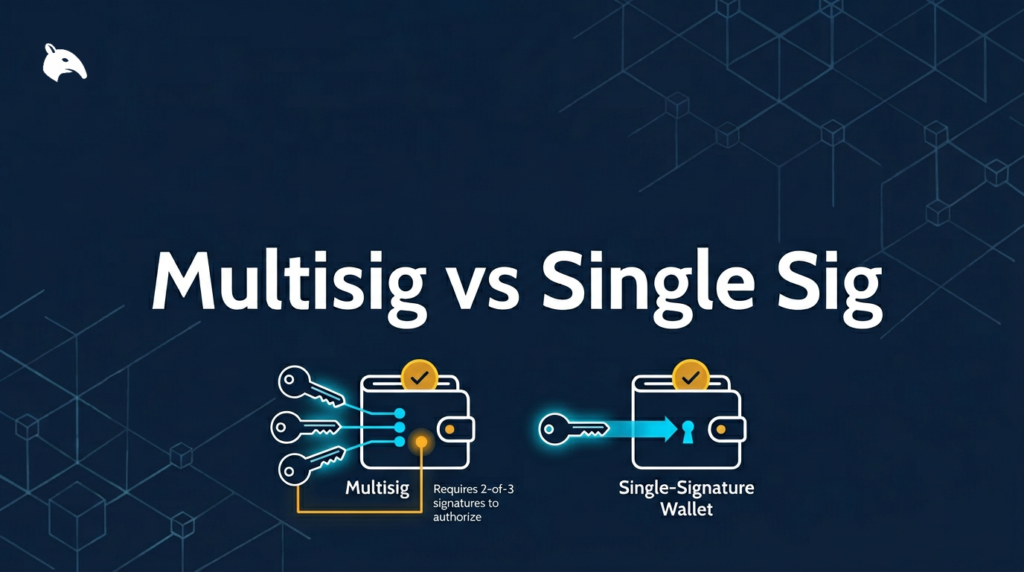
The comparison between a multisig vs single sig wallet comes down to a structural security question: how much risk does a single point of failure represent for your holdings?
For most retail investors, a single-signature wallet is the standard setup and, when managed correctly, provides solid protection. As holdings grow and the risk calculus shifts, multisig introduces a different security architecture built around distributing that single point of failure across multiple keys. This guide covers what each model actually does, where each one fits, and what the real trade-offs look like in practice.
Disclaimer: This content is for educational and informational purposes only and does not constitute financial, investment, tax, or legal advice. Cryptocurrency markets are volatile and involve risk. Always conduct your own research and consult a qualified professional before making financial decisions.
Affiliate Disclosure: Some links in this article may be affiliate links. If you choose to use them, I may earn a commission at no additional cost to you.
5 Key Takeaways
- A single-sig wallet uses one private key to control funds. One compromised or permanently lost key means losing access with no recovery path.
- A multisig wallet requires multiple keys to authorize a transaction, removing the single point of failure that a single-sig wallet carries by design.
- The 2-of-3 configuration is the most practical multisig setup for retail investors: any two of three keys can authorize transactions, so losing one key does not lock you out.
- Multisig adds significant setup and recovery complexity. Implementing it poorly is as dangerous as mismanaging a single-sig wallet.
- For most retail investors, a properly managed single-sig hardware wallet remains the right choice until holdings and risk tolerance justify the added complexity of multisig.
What Is a Single-Signature Wallet?

A single-signature wallet is the standard custody model for most retail crypto investors. One private key controls the wallet, and to authorize any transaction, that key must sign it. Every software wallet, hardware wallet, and most mobile wallet apps operate on this model. The name accurately describes the mechanics: one signature required, one key holds all authority.
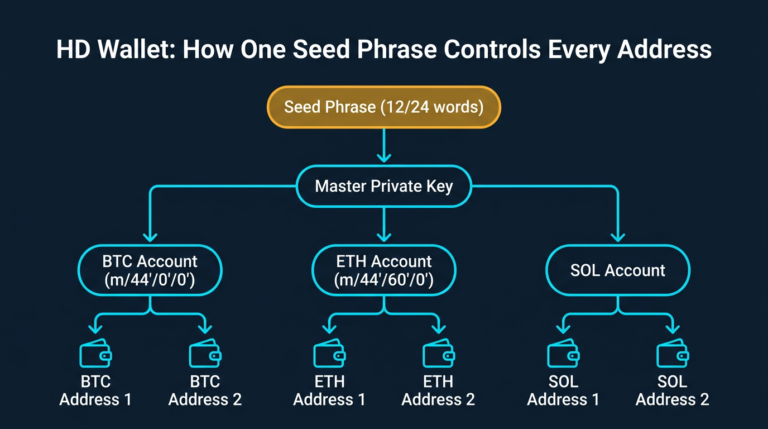
When you set up a hardware device like a Ledger or Trezor, the device generates a private key internally and issues a seed phrase as your human-readable backup. That seed phrase represents the key. Anyone who has access to it has full control over the funds stored at that address. This is not a flaw specific to hardware wallets. It is the defining characteristic of the single-sig model. Control is singular, and so is the risk concentration.
The model is not inherently weak. A hardware wallet with a properly secured, offline seed backup is substantially harder to compromise than a custodial exchange account. The structural limitation is concentration. If the key or its backup is ever exposed, physically destroyed without a valid copy existing, or stolen, there is no recovery path. No second key, no fallback, no override mechanism built into the protocol.
What Is a Multisig Wallet?
A multisig wallet, short for multi-signature wallet, requires more than one private key to authorize a transaction. The configuration is expressed as M-of-N, where M is the minimum number of signatures needed, and N is the total number of keys in the setup. The most widely used retail configuration is 2-of-3: two out of three keys must sign before the network processes a transaction.
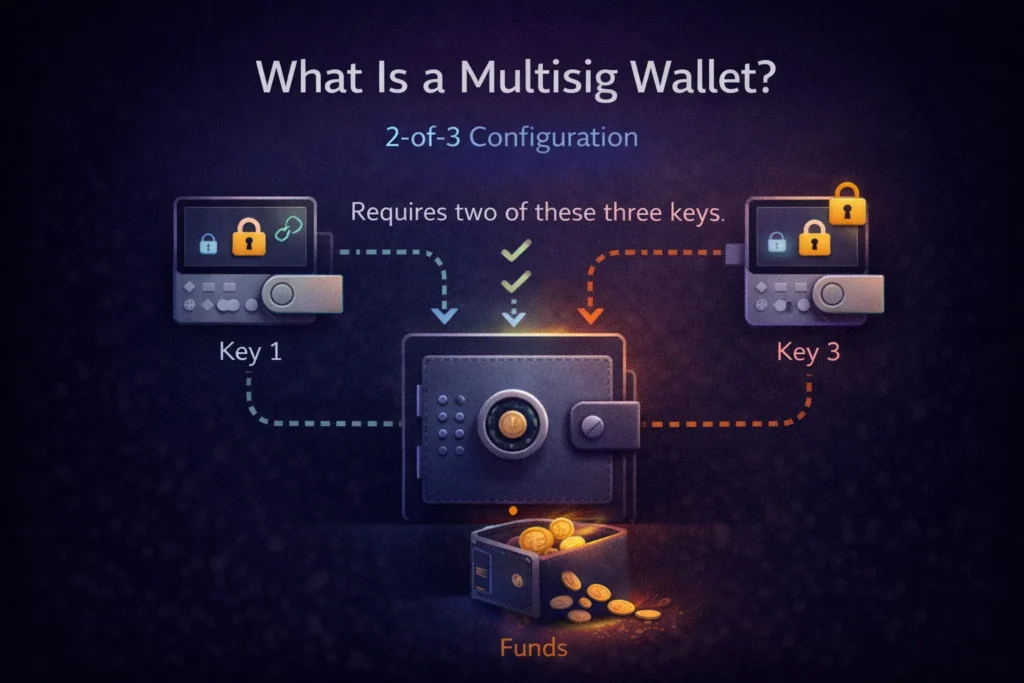
Each key is stored separately, typically on different hardware devices kept in different physical locations. An attacker who compromises one device has not compromised the wallet. They would need to access at least M keys to move any funds. For a standard 2-of-3 setup, that means gaining access to two separate keys stored in two different locations. That structural separation is what makes multisig meaningfully different from single-sig.
Other configurations carry distinct trade-off profiles. A 2-of-2 setup means both keys are always required, which removes single-device risk but introduces a new problem: if either key is permanently lost, funds are locked forever. A 3-of-5 setup provides more redundancy and is common in institutional and organizational contexts. For individual retail investors approaching multisig for the first time, 2-of-3 is the established and widely supported entry point.
How Multisig Works: The Technical Basics
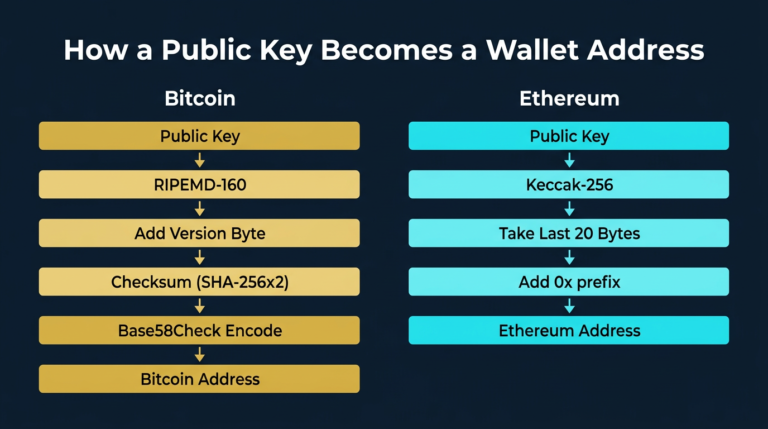
Bitcoin has supported native multisig through its scripting language since early in its development. Transactions can be constructed so that spending from a multisig address requires a valid quorum of cryptographic signatures before the network accepts them. The current standard uses P2WSH, Pay to Witness Script Hash, which is the SegWit-era implementation that improves fee efficiency and is now broadly supported. The Bitcoin Developer Documentation covers the complete technical specification for the scripting mechanics involved.
In practice, retail users interact with multisig through wallet software rather than the protocol layer directly. Sparrow Wallet, Electrum, and Caravan all support native Bitcoin multisig with varying levels of technical exposure. Consumer-focused services like Casa and Unchained Capital have built guided setup workflows on top of these standards to make the process more accessible. The key operational point is that each participating hardware device generates its own key independently. The multisig wallet is then defined by the combination of all those keys and the policy governing how many are required to sign.
Ethereum and EVM-compatible chains do not have native multisig scripting. On those chains, multisig is implemented through smart contracts. Gnosis Safe, now operating under the name Safe, is the most established implementation for Ethereum multisig. It works reliably and has been audited extensively. But it introduces an additional dependency layer that native Bitcoin multisig does not carry: the smart contract itself. Contract bugs, while rare in thoroughly vetted deployments, represent a risk category that is absent from the Bitcoin scripting model.
Multisig vs Single-Sig: A Direct Security Comparison
Looking at specific attack scenarios and operational characteristics side by side clarifies where each model is stronger and where each carries gaps.
| Feature | Single-Sig | Multisig (2-of-3) |
|---|---|---|
| Keys required to transact | 1 | 2 of 3 |
| Single device theft or compromise | Funds at risk | Funds protected |
| Single seed backup lost | Funds at risk | Accessible with remaining two keys |
| Setup complexity | Low | High |
| Recovery complexity | Low | High |
| Bitcoin support | Native | Native (P2WSH) |
| Ethereum support | Native | Smart contract (Safe) |
| Inheritance and estate planning | Straightforward | Requires full documented configuration |
The single-sig model concentrates both its strength and its risk in a single credential. When that credential is managed correctly, the setup is sound. Multisig distributes risk across multiple keys and devices, but it equally distributes the complexity of managing, backing up, and recovering those keys. Neither model is unconditionally superior. Both are only as reliable as the operational discipline behind them.
When Multisig Makes Practical Sense for Retail Investors

Multisig becomes a proportionate security response when the value being protected justifies the added complexity. There is no universally agreed number, but practitioners in the Bitcoin security community often reference the $50,000 range as a point where the risk of targeted attack, single-device failure, or physical theft starts to shift the security calculus materially. Below that threshold, a solid self-custody practice with a properly managed hardware wallet covers most realistic threat scenarios for individual investors.
Above that level, the cost-benefit changes in measurable ways. A large enough holding makes targeted theft economically rational for an attacker. A hardware device being stolen or a seed phrase being discovered by someone in your household carries higher consequences at higher values. Multisig structurally reduces several of those attack vectors by requiring simultaneous compromise of multiple separated keys.
There are also scenarios where multisig adds clear value independent of the total amount involved:
- Long-term cold storage is intended to stay untouched for years or decades
- Shared custody arrangements with a trusted partner, co-investor, or family member
- Inheritance planning, where a designated trusted person holds one key as a recovery participant
- Business or organizational crypto holdings where multi-party approval reduces internal risk
If you are already running a layered approach to cold storage, multisig is often the natural next step. Our guide on setting up a 3-tier cold storage architecture covers the layered model that typically precedes a multisig implementation for investors taking long-term security seriously.
When Single-Sig Remains the Right Choice

Single-sig is not a compromise for investors who lack the technical background for multisig. For a large proportion of retail investors, it is the genuinely correct setup for their situation.
If you are new to self-custody, starting with multisig introduces complexity before the foundational habits are solid. Seed phrase management, hardware device security, and recovery testing take time to get right. Adding multi-key complexity before those habits are reliable increases the chance of mistakes that can permanently lock you out of your own funds. The failure mode for a poorly executed multisig setup is irreversible, and that distinction matters.
Single-sig also remains the more practical option in these situations:
- Hot wallets and active trading wallets, where frequent access is necessary
- Holdings that fall below your personal threshold for added operational complexity
- Situations where you cannot store multiple keys securely in physically separate locations
- Coins and tokens on chains where multisig tooling is limited, experimental, or unaudited
For most retail investors, the more immediate issue is not choosing between multisig and single-sig but ensuring funds are off centralized exchanges entirely. The consequences when exchanges freeze withdrawals are well-documented. Our article on why exchange withdrawal pauses will happen again addresses that foundational step before the multisig vs single-sig question even becomes relevant.
The Real Risks of Multisig Most Guides Skip
Multisig is frequently framed as a straightforward security upgrade. It is not. The risks introduced by poor implementation are serious, and they are consistently underrepresented in introductory coverage of the topic.
Incomplete key backups. Every key in the setup must be independently backed up and correctly documented. In a 2-of-3 setup, losing reliable access to two of the three keys is a permanent fund loss event. The backup discipline required for three separate keys, each stored securely and verifiably in separate locations, is considerably higher than managing a single seed phrase. Many people attempting multisig for the first time significantly underestimate this.
Recovery requires full configuration data, not just the keys. Recovering a multisig wallet demands more than having the physical keys available. The process also requires the complete wallet configuration: the M-of-N parameters, which software was used to construct the wallet, the derivation paths for each key, and the extended public key data (xpub) from each participating device. Without this configuration record, funds can be permanently inaccessible even when every key physically exists and is intact.
Wallet descriptor and software dependencies. The wallet software used to construct the multisig setup is operationally part of the setup itself. If Sparrow Wallet or Electrum was used with specific parameters, those parameters must be preserved separately from the key backups. The wallet descriptor, which is a compact representation of the full multisig policy, should be stored redundantly alongside the keys. This is where a disproportionate number of first-time multisig setups fail in practice.
Chain and asset coverage is uneven. Bitcoin multisig is mature, widely supported, and battle-tested across years of production use. Ethereum multisig via smart contracts is robust in established deployments. Many smaller chains have limited or experimental multisig tooling that has not been stress-tested at scale. A security strategy built around Bitcoin multisig does not automatically apply to the full range of assets most retail investors hold.
Multisig does not cover all attack vectors. It reduces single-device compromise risk meaningfully. It does not protect against phishing attacks that manipulate you into signing malicious transactions, supply chain attacks on hardware devices at purchase, or social engineering. Security is a system of layered defenses. Multisig addresses one specific part of that system, not the whole of it.
Common Mistakes with Both Setups
Understanding where each model typically fails in practice helps clarify what careful implementation actually requires.
Single-sig mistakes:
- Storing the seed phrase digitally in photos, cloud storage, email drafts, or note apps
- Keeping only one physical backup of the seed phrase in a single location with no off-site copy
- Using a software wallet for significant long-term holdings instead of a hardware device
- Never testing the recovery process to confirm the backup is valid and actually works
Multisig mistakes:
- Choosing a 2-of-2 configuration without understanding that losing either key permanently locks the wallet
- Not recording the full wallet configuration, including the wallet descriptor and each device’s xpub data, separately from the physical keys
- Never running a complete recovery test before relying on the setup for significant holdings
- Using multisig for chains or assets where the tooling is incomplete or has not been independently audited
- Allowing setup complexity to prevent ongoing maintenance as devices age or wallet software receives major updates
Both models reward operational discipline. Fund loss in crypto self-custody is rarely caused by choosing the wrong security model. It is most commonly caused by using the right model carelessly. Whether you use single-sig or multisig, running a full recovery test before loading the wallet with meaningful funds is the single most important validation step in any custody setup.
Sources
- Bitcoin Developer Documentation: developer.bitcoin.org
- BIP-11: M-of-N Standard Transactions: github.com/bitcoin/bips
Frequently Asked Questions
What is a multisig wallet?
A multisig (multi-signature) wallet requires more than one private key to authorize a transaction. In a 2-of-3 setup, two of three keys must sign before funds can move. This removes the single point of failure present in a standard single-sig wallet, where one compromised or lost key results in permanent loss of access.
Is multisig safer than a single-sig hardware wallet?
Multisig reduces specific risks that a single-sig setup cannot address, particularly single-device compromise and targeted physical theft. A single-sig hardware wallet with a properly secured offline seed backup provides strong protection for most retail investors. Multisig adds a structural layer on top of that, but it also introduces setup and recovery complexity that creates its own risks if not managed carefully.
What is the best multisig setup for retail investors?
A 2-of-3 Bitcoin multisig using three separate hardware devices, with properly documented recovery information including the wallet descriptor and xpub data from each device, is the most widely recommended starting point for individual investors. Tools like Sparrow Wallet and Caravan handle the technical construction. Services like Casa and Unchained Capital offer more guided setups for users who prefer a supported approach.
Can you use multisig for Ethereum and altcoins?
Ethereum supports multisig through smart contracts, primarily via Safe (formerly Gnosis Safe). Many altcoins have limited or no native multisig support, depending on their chain architecture. Bitcoin has the most mature, battle-tested, and natively supported multisig implementation. For altcoins with limited tooling, single-sig on a hardware wallet is typically the more reliable custody approach.
What happens if you lose one key in a 2-of-3 multisig setup?
In a 2-of-3 setup, losing one key does not affect your ability to access funds. The two remaining keys meet the threshold required to sign transactions. However, you should treat a lost key as an urgent issue. Replace it and reconstruct your backup configuration as soon as possible to restore the full redundancy that the 2-of-3 structure is designed to provide.