Last Updated on March 11, 2026 by Snout0x
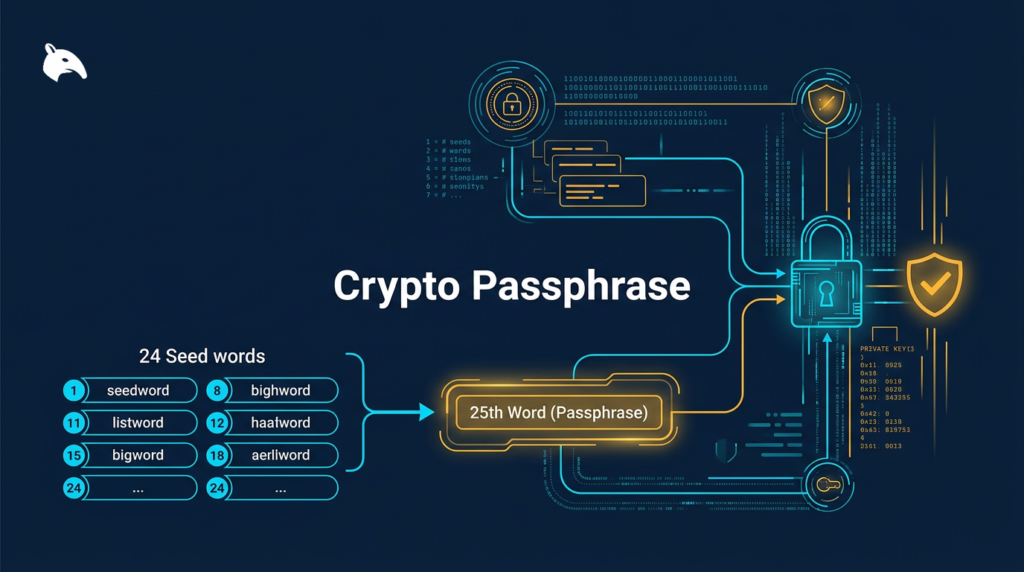
A crypto passphrase is an optional string of characters added to a seed phrase to generate a separate, hidden wallet. It works under the BIP39 standard and is often called the “25th word.” Understanding how it functions, when it adds real value, and where it creates serious risk is important for anyone evaluating it as part of a self-custody security setup.
Simple Definition
A passphrase is an additional input in the cryptographic key derivation process. It produces a completely different wallet from the same seed phrase. Standard seed phrases use 12 or 24 words, and the passphrase acts as an unofficial extra word added on top, which is why the “25th word” label stuck.
Unlike your seed phrase, the passphrase is not generated by the device. You create it yourself. It can be any combination of letters, numbers, and special characters, at any length. There is no word list, no dictionary constraint, and no system-imposed format.
Most hardware wallets support the BIP39 passphrase feature but disable it by default. Enabling it is a deliberate step. It does not happen automatically during setup, and many users never touch it at all.
Why It Matters
The passphrase matters because it separates your real holdings from the wallet your seed phrase opens on its own. Without a passphrase, anyone who finds your seed phrase backup has complete access to your funds. That is a well-understood risk in self-custody. Adding a passphrase means the seed phrase alone is no longer sufficient. An attacker would need both pieces. If they are stored separately, the chance of both being compromised at the same time is substantially lower.
There is also a plausible deniability use case. When you use a passphrase, your base seed phrase wallet still exists and opens normally without it. If someone forces you to open your wallet, you can open the base wallet, which might hold a small amount, while your real funds remain in the passphrase-protected wallet. No technical method exists to confirm whether a passphrase wallet is present.
That use case is real but niche. Most average users do not face coercion scenarios. The passphrase is most relevant for people holding significant crypto in cold storage, traveling internationally with hardware wallets, or facing realistic physical security threats. For everyone else, the complexity often outweighs the benefit.
How It Works
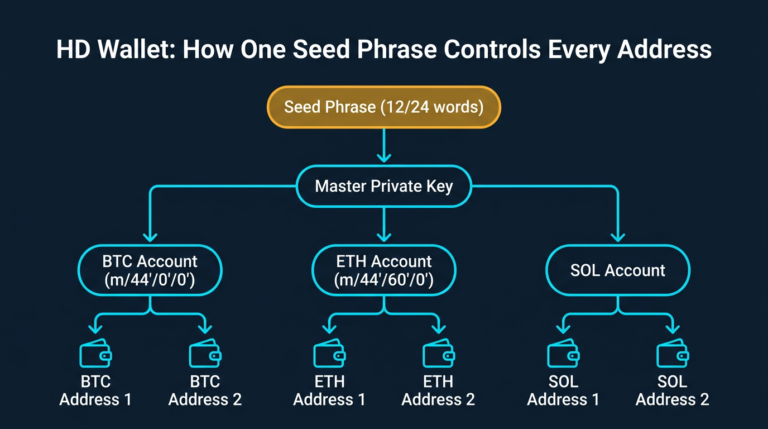
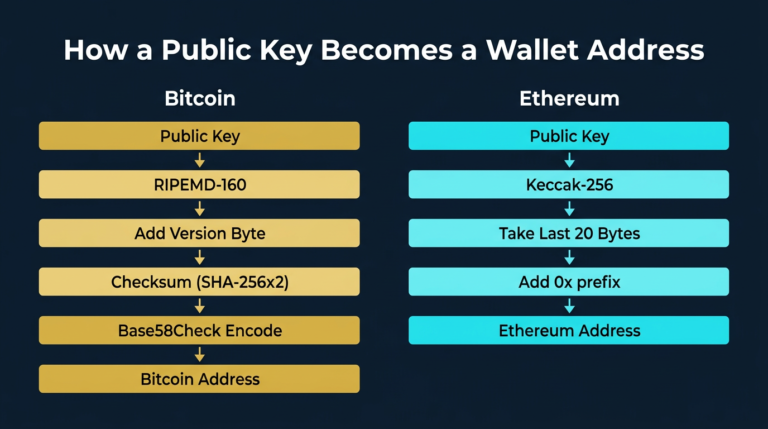
The BIP39 standard governs how seed phrases and passphrases are combined to generate wallet keys. During wallet derivation, the process converts your seed phrase mnemonic into a binary seed using a function called PBKDF2. The passphrase is fed into that function alongside the mnemonic as a separate input.
The result is a 512-bit seed that produces a completely different master private key from what the seed phrase alone generates. Change one character in the passphrase and you get an entirely unrelated wallet. Case sensitivity applies. Spaces count. Every character matters.
The system does not validate the passphrase. If you enter the wrong one, the device opens a different wallet without any error message or warning. That wallet will be empty if it has never been funded. The device has no way to tell you whether the passphrase was correct. It simply derives whatever wallet corresponds to your input.
This is intentional. It is the design feature that enables plausible deniability. It is also what makes typos and memory errors genuinely dangerous. A single forgotten capital letter means a different wallet address, not a recoverable mistake.
The passphrase is never stored on the device. Every time you access a passphrase-protected wallet, you enter it manually. The device derives the wallet on the fly and clears it from memory when the session ends.
Common Mistakes
The most common mistake is storing the passphrase with the seed phrase. If both are found together, the passphrase provides no protection. They must be stored in physically separate locations, with separate access controls. Same drawer, same safe, same sealed envelope — none of those count as separate.
Choosing a weak passphrase is the second major error.
A passphrase like “bitcoin2024” or a pet name offers almost no resistance against anyone who finds your seed phrase and tries obvious strings. A strong passphrase is long, random, and includes a mix of uppercase, lowercase, numbers, and at least one special character.
Many users skip recovery verification entirely. They set up a passphrase, move funds into the protected wallet, and never confirm they can actually recover access on a second device. The correct approach is to disconnect, reconnect, enter the passphrase, and verify the wallet addresses match before moving any funds. Do it two or three times. The first verification should not happen during an emergency.
Relying on memory alone is a serious mistake that surfaces slowly. A passphrase that feels unforgettable today may be misremembered in five years, particularly under stress or after illness. Record it physically, accurately, noting every character, and store it in a secure location that is separate from your seed phrase backup.
For anyone using a passphrase for plausible deniability, the base wallet also needs to hold some real funds. An obviously empty wallet does not hold up under coercion. Keep a realistic but non-critical amount there.
Security and Risk Considerations
A passphrase reduces the risk that a stolen seed phrase alone is sufficient to drain your wallet. It also creates a second single point of failure. Your seed phrase was already one. Now there are two separate things that must both survive, be accurately stored, and remain accessible. If either is lost, recovery is not possible.
There is no recovery mechanism for a lost passphrase. The device manufacturer cannot help. There is no support escalation. The cryptographic derivation is one-way. Forgotten passphrases have caused permanent fund loss for real users, and no external party can reverse that outcome.
The inheritance problem is also worth considering. If something happens to you, whoever is meant to access your crypto needs to know the passphrase exists and where to find it. A passphrase that was never disclosed and cannot be recovered effectively removes those funds permanently. Estate planning for crypto is already underdeveloped. A passphrase adds complexity to an already difficult problem.
For most users who are still building reliable seed phrase backup habits, a passphrase introduces more operational risk than security benefit. The foundation is getting seed phrase security right. A passphrase is an advanced layer built on top of that, not a shortcut around it. The guide to seed phrases covers that foundation in detail.
The broader self-custody decisions that surround passphrase usage are worth understanding before enabling the feature. Exchange Withdrawals Will Pause Again provides practical framing for moving and holding crypto safely outside an exchange.
The security habits that cause the most problems for self-custody users are covered in 5 “Safe” Crypto Habits That Will Get You Rekt, several of which overlap directly with passphrase misuse patterns.
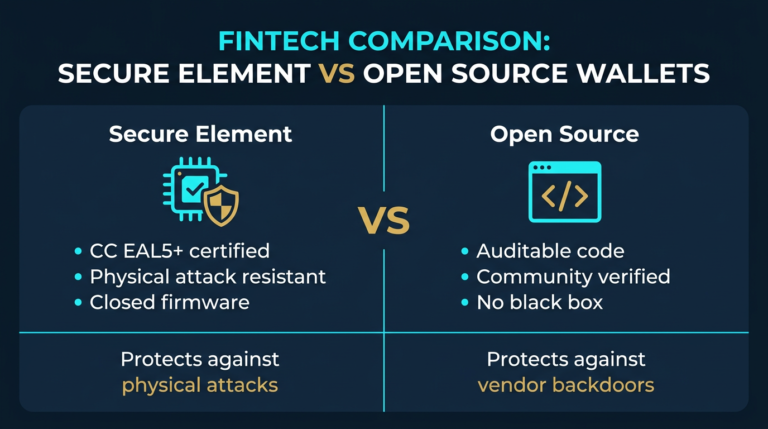
If you are evaluating hardware wallets as part of this setup, Best Crypto Wallets for Beginners covers which devices support BIP39 passphrase functionality and how they compare.
Frequently Asked Questions
What happens if I forget my crypto passphrase?
You lose access to the wallet it protects permanently. There is no recovery option, no support ticket, and no way to reverse the loss. The passphrase is not stored anywhere in the system. If you cannot reproduce it exactly, the funds are inaccessible.
Is the passphrase stored on my hardware wallet?
No. The passphrase is entered manually each time you access the passphrase-protected wallet. After the session ends, it is cleared from device memory. The hardware wallet keeps no record of it.
Can any wallet use a passphrase?
BIP39 passphrase support is common in hardware wallets like Ledger and Trezor and in many open-source software wallets. Not all wallets support it. Confirm your specific wallet and its companion software support BIP39 passphrase entry before relying on it.
Is a passphrase the same as a PIN?
No. A PIN protects access to the physical device. A passphrase is part of the cryptographic key derivation process and directly determines which wallet is generated. They operate at completely different layers of your security setup and protect against different threats.
Does a passphrase protect against seed phrase theft?
Partially. If someone obtains your seed phrase but does not know your passphrase, they can access your base wallet but not your passphrase-protected one. That protection holds only if the passphrase is strong, stored separately, and not inferable from anything near your seed phrase backup.