Last Updated on March 13, 2026 by Snout0x
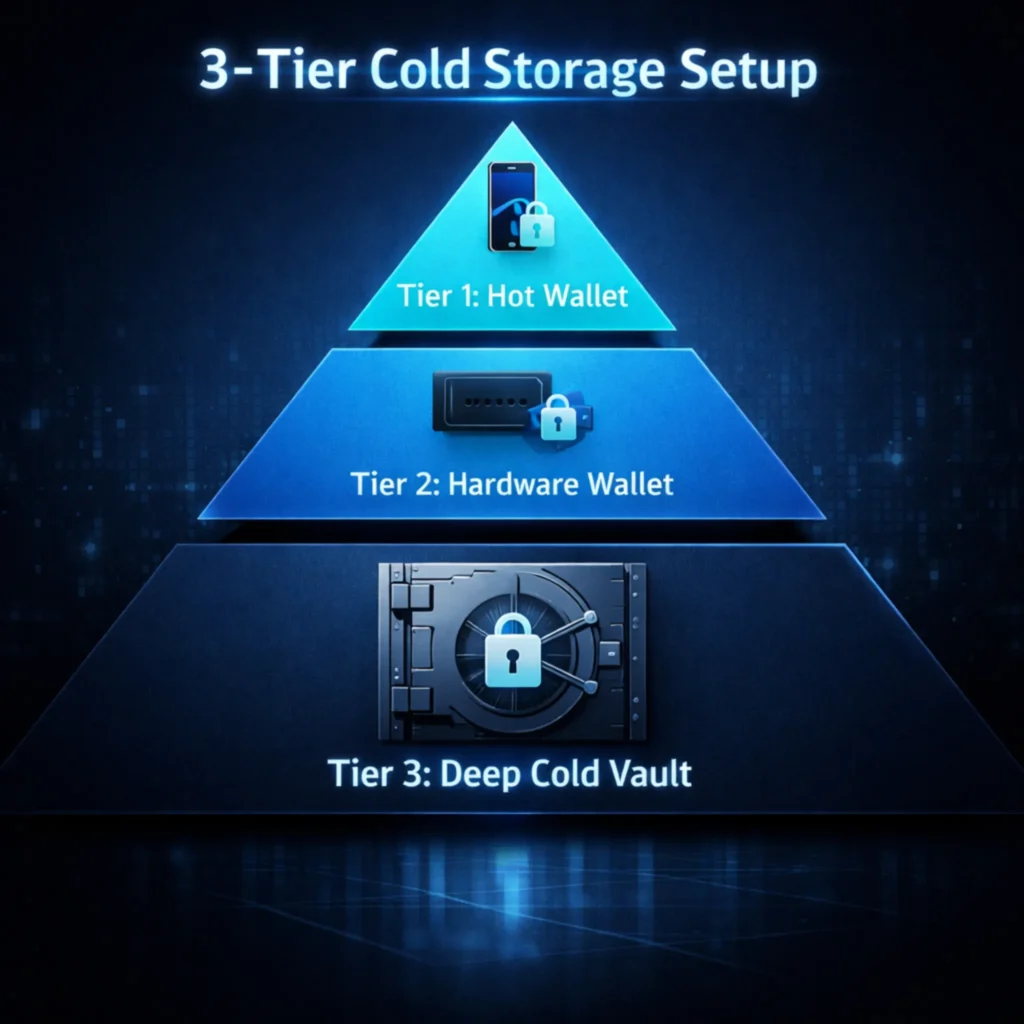
A 3-tier cold storage setup organizes your crypto holdings across three distinct layers, each with a different level of accessibility and protection. The core idea is that not all of your assets should be equally easy to reach, because accessibility and security move in opposite directions. This structure applies basic risk management logic to wallet design and helps limit the damage from a single point of failure, whether that is a hardware compromise, a phishing event, or a physical loss. It is practical, scalable, and well-suited to anyone holding meaningful amounts of crypto over the long term.
Disclaimer: This content is for educational and informational purposes only and does not constitute financial, investment, tax, or legal advice. Cryptocurrency markets are volatile and involve risk. Always conduct your own research and consult a qualified professional before making financial decisions.
Affiliate Disclosure: Some links in this article may be affiliate links. If you choose to use them, I may earn a commission at no additional cost to you.
Key Takeaways
- A 3-tier setup separates holdings into an operational layer, a primary cold storage layer, and a deep cold storage layer.
- Each tier has a defined purpose, a risk tolerance, and an access frequency. Mixing these up defeats the structure.
- Tier 3 should hold the majority of long-term holdings and require deliberate effort to access.
- Seed phrases for each tier must be stored separately and never combined or cross-referenced.
- Compromise at one tier should have no effect on the others.
What Is a 3-Tier Cold Storage Setup?
A 3-tier cold storage setup is a structured approach to wallet organization, dividing holdings into three layers based on how frequently you access funds and the risk tolerance of each layer. This model is inspired by traditional financial security, where liquidity and risk are managed in separate accounts rather than pooled together.
When choosing between wallet security methods, many users opt for a multisig vs single-sig security comparison to determine the most suitable setup for their needs. This topic has gained significant attention, especially in the management of high-value crypto assets.
The three tiers are as follows: Tier 1 is the operational layer, typically a hot wallet or software wallet used for regular activity. Tier 2 is the primary cold storage layer, usually a hardware wallet holding a portion of your funds and accessed occasionally. Tier 3 is the deep cold storage layer, the vault that holds the majority of long-term holdings behind the strongest physical and operational barriers.
Each tier serves a distinct function, and none replaces the others. The combined structure provides the security needed. If you want to better understand cold storage before building a layered approach, check out our foundational article on what cold storage is in crypto.
Why One Layer Is Not Enough
Most retail investors hold all their crypto in one or two places: an exchange account and, if they are security-conscious, a single hardware wallet. This works until it does not.
The problem with a single-wallet approach is concentration risk. If that one device is lost, stolen, compromised, or physically damaged, everything is at stake simultaneously. A single hardware wallet is still a meaningful improvement over an exchange. But treating one device as the entirety of your security strategy leaves structural gaps.
Physical theft, firmware vulnerabilities, supply chain risks, and user error can all affect a single device. A multi-tier structure means that if one layer is compromised, the others remain intact. The failure is contained rather than total.
The 3-tier model also enforces deliberate behavior. When you must move assets through defined layers to access a large holding, the process slows down. You check more carefully. That friction is a feature. Impulsive decisions account for a significant share of self-custody losses, and structural friction reduces them. The broader case for why self-custody structure matters is detailed in the self-custody survival guide, which covers what happens when exchange access is unavailable.
Tier 1: The Operational Layer
Tier 1 is the only layer that stays connected to the internet regularly. It is designed for activity, not storage. Think of it as a checking account: money moves through it, not into it.
This layer is typically a non-custodial software wallet on your phone or desktop, such as MetaMask, Phantom, or a similar application. Some users also keep a small balance on a hardware wallet that they use frequently, but the defining feature of Tier 1 is regular internet exposure and transaction frequency.
The amount held in Tier 1 should be calibrated to what you are genuinely comfortable losing entirely. Common practice is to keep between 1% and 5% of total holdings at this layer, or a fixed flat amount defined in advance. The ceiling matters more than the exact percentage. Pick a number, document it, and hold to it.
Operationally, Tier 1 requires active hygiene. Token approvals for DeFi contracts should be reviewed and revoked when no longer needed. Wallet addresses should not be shared more widely than necessary. Phishing links, malicious contracts, and drainer exploits are all common attack vectors at this layer, which is exactly why it should hold limited funds. A Tier 1 compromise should be annoying, not catastrophic.
The seed phrase for Tier 1 must be stored separately from Tier 2 and Tier 3. These are independent wallets with independent recovery credentials. Do not combine them or store them in the same physical location.
If you are new to self-custody, the Crypto Wallet Security Checklist: 15 Rules to Avoid Getting Hacked provides a practical framework for protecting your funds before problems occur.
Tier 2: The Primary Cold Storage Layer
Tier 2 is a hardware wallet accessed occasionally rather than daily. It holds a meaningful portion of your holdings, typically in the range of 20% to 40%, depending on your structure, and serves as a working cold storage balance. This is where assets live when they are not in active use but may need to be accessible within a reasonable timeframe.
Hardware wallets used at this layer should be sourced directly from official manufacturers. Pre-owned or third-party marketplace devices carry real supply chain risks. A device that arrives with pre-loaded malware or a pre-seeded phrase can drain the wallet the moment funds arrive. Buy from the manufacturer’s official website and verify device authenticity before use.
When you do use a Tier 2 device, connect it only to a clean, verified computer running official manufacturer software. Public computers, unfamiliar networks, and unverified software are all off-limits. After a transaction, store the device in a physically secure location separate from its seed backup.
The seed phrase for Tier 2 should be written by hand on paper or, for better durability, stamped onto a metal backup plate. It should not exist anywhere digitally. No photographs. No notes apps. No password managers. No cloud backups. The seed phrase is the actual asset. A digital copy is a digital vulnerability.
For context on how hardware wallet security assumptions frequently do not hold up under scrutiny, the breakdown at Cold Storage Paranoia is worth reading before trusting a Tier 2 setup that has not been tested.
Tier 3: The Deep Cold Storage Layer
Tier 3 is the vault. The majority of long-term holdings belong here, and the design goal is maximum protection at the cost of easy access. That trade-off is deliberate and should be accepted before building this layer.
A robust Tier 3 setup typically includes an air-gapped hardware wallet or a cold-signing device that never connects to the internet during normal operation. Transactions are signed offline and broadcast separately. The attack surface is narrow because the device itself is never directly network-exposed during the signing process.
Seed phrase storage at Tier 3 should use a durable metal backup. Steel or titanium plates that are stamped or engraved resist fire, water, and physical degradation over time. Paper backups are acceptable for Tier 1 and Tier 2, but Tier 3 holdings justify the additional cost of a metal backup.
Geographic distribution is a critical component of Tier 3 seed storage. Keeping a single backup in a single location creates a concentrated physical risk. A common approach is to store independent copies across two or more physically separated, secure locations: a home safe and a bank safety deposit box, for example, or a trusted family member’s location. Any single location can be lost, damaged, or compromised. The seed backup survives if at least one copy is intact.
Some users add a BIP-39 passphrase, often called the 25th word, to their Tier 3 wallet. This creates a separate wallet derived from the same seed but only accessible when both the seed phrase and the passphrase are present. If the seed is somehow discovered, it is not enough to access funds without the passphrase. This adds meaningful protection, but requires careful management of both components independently.
Tier 3 should not be accessed casually. Set a defined review schedule, quarterly or annually, to verify device integrity and confirm recovery still works. Outside of planned reviews or genuine emergencies, this layer should stay untouched. If you have not yet reviewed whether your current wallet structure would benefit from a formal two-wallet baseline first, the guide on what a 2-wallet setup is in crypto provides the foundational framework before adding a third tier.
How Much Goes in Each Tier?
There is no single correct allocation. The right split depends on your total holdings, your transaction frequency, and your risk tolerance. A starting framework looks like this:
- Tier 1 (operational/hot): 1% to 5% of total holdings
- Tier 2 (primary cold storage): 20% to 40% of total holdings
- Tier 3 (deep cold storage): 55% to 79% of total holdings
If you interact with DeFi frequently, Tier 1 may need to be sized slightly larger to support regular operations. If your primary purpose is long-term storage with infrequent transactions, Tier 3 should hold the clear majority. The principle is that less accessible equals better protected, so the dominant share of holdings should always be in the least accessible layer.
Revisit your allocation as total holdings grow. A percentage-based rule that worked at lower values may leave too much in Tier 1 as amounts increase. Define a hard ceiling for each tier and review it periodically.
How to Move Assets Between Tiers
Moving assets between tiers should be treated as a security event. It requires more care than a routine transaction.
Before moving assets from Tier 2 or Tier 3 outward, use a verified and clean device. Do not initiate the move from a computer that has been used for general browsing, gaming, or other unmanaged activity. Double-check the destination address character by character, not just the first and last few. Send a small test transaction before committing a large sum, then verify receipt before proceeding.
When depositing into Tier 3, confirm the receiving address independently using the hardware wallet’s own screen, not the software interface on the computer. Malware can alter what is displayed in a browser or application window without affecting what the device screen shows. These two should always match before you confirm.
Clipboard hijacking is a documented attack vector where malware silently replaces a copied wallet address with an attacker-controlled address. The substitution happens in memory and is not visible to the user. Taking an extra thirty seconds to verify the final six characters of a destination address independently is a meaningful defense. The OWASP Cryptographic Storage Cheat Sheet offers broader reference on secure key and storage handling principles that apply directly to cold storage operations.
Common Mistakes
Building a 3-tier structure sounds straightforward. In practice, several mistakes are common enough to address directly.
Using the Same Seed Phrase Across Tiers
This eliminates the entire benefit of the structure. Each tier must be an independent wallet with its own seed phrase. Compromise at one tier means nothing if the seeds are genuinely separate. Reusing a seed collapses the tiers into a single point of failure.
Storing Seed Phrases Digitally
Photographing a seed phrase, saving it in a notes app, storing it in a password manager, or emailing it to yourself creates a permanent digital exposure. Cloud services, email accounts, and password managers are all potentially accessible to attackers. Seed phrases belong on paper or metal, offline, only. No exceptions.
Putting Too Much in Tier 1
Tier 1 carries the highest exposure of the three layers. Overloading it defeats the structure entirely. Define a maximum for this layer and hold to it even when it feels inconvenient to move funds from Tier 2 for a specific use.
Never Testing Tier 3 Recovery
Some users build a deep cold storage setup and never verify they can actually recover it. Hardware devices fail. Seed backups can be mislabeled or damaged. Before committing large holdings to Tier 3, run a full recovery test on an empty wallet using the seed backup you intend to rely on. Confirm it works before you need it to.
Buying Hardware Wallets from Unofficial Sources
Compromised hardware wallets have been sold through unofficial marketplaces and reseller platforms with pre-installed malware or pre-generated seed phrases that the attacker already controls. Always buy directly from the manufacturer’s official website. The cost of the device is not worth the risk of a counterfeit unit.
Security and Risk Considerations
A 3-tier structure reduces several categories of risk but does not eliminate all of them. Understanding what the structure protects against, and what it does not, is part of using it correctly.
Physical loss remains a real risk at every tier. Hardware devices can be lost, damaged, or destroyed.
The seed phrase backup is what restores access. If the backup is also destroyed or inaccessible, the holdings are permanently unrecoverable. Physical security of seed backups is as important as the wallet device itself, and often receives less attention.
A single copy of a seed phrase stored in a single location creates concentrated physical risk. Fire, flood, theft, or simple misplacement can eliminate that single copy. Distributing backups across multiple secure locations, particularly for Tier 3, removes this single point of failure from the seed storage layer.
Inheritance and emergency access are frequently overlooked in cold storage planning. A 3-tier structure that only one person knows how to navigate is fragile in an emergency. Consider what happens if the account holder becomes incapacitated. Documenting the structure in a sealed, physically secure location accessible to a designated trusted person is a practical step that most users delay indefinitely.
Operational security remains the most common failure point. The seed phrase is the asset. The wallet device is just a tool for accessing it. Treating seed phrase protection with the same seriousness as the holdings themselves is the foundational discipline of any cold storage setup, regardless of how many tiers it has.
For a direct look at how seemingly safe security habits can still create real exposure, the breakdown at 5 “Safe” Crypto Habits That Will Get You Rekt covers behaviors that look correct on the surface but introduce meaningful risk in practice.
Sources
Frequently Asked Questions
What is the difference between Tier 2 and Tier 3 cold storage?
Tier 2 is an accessible hardware wallet used for working cold storage. It holds a portion of holdings that may need to be accessed within a reasonable timeframe. Tier 3 is deep cold storage designed for long-term holdings, typically air-gapped and accessed only during planned reviews or genuine emergencies. The two tiers differ in access frequency, device configuration, and seed backup requirements.
Do I need three separate hardware wallets for a 3-tier setup?
No. Tier 1 is typically a software wallet, not a hardware device. Tier 2 and Tier 3 generally use hardware wallets, but they do not have to be different brands or models. What matters is that they are separate wallets with separate seeds, not the hardware itself. A standard hardware wallet can serve Tier 3 if it is kept offline and stored with appropriate physical controls.
How often should I access Tier 3?
As infrequently as possible. A quarterly or annual review to verify device and backup integrity is reasonable. Routine transactions belong in Tier 1 and Tier 2. Tier 3 should only be accessed when a significant rebalancing is needed or in a genuine emergency. Frequent access increases exposure and defeats the purpose of deep cold storage.
What happens if I lose a hardware wallet in Tier 2 or Tier 3?
As long as the seed phrase backup is intact and accessible, the wallet can be fully recovered on a new device. The hardware device is replaceable. The seed phrase is not. This is why seed backup security matters more than device security at every tier.
Is a BIP-39 passphrase required for Tier 3?
It is not required, but it adds a meaningful layer of protection for significant holdings. If the seed phrase is discovered, a BIP-39 passphrase prevents access without the second factor. The trade-off is added complexity and an additional piece of information that must be stored and protected independently from the seed phrase itself.