Last Updated on April 14, 2026 by Snout0x
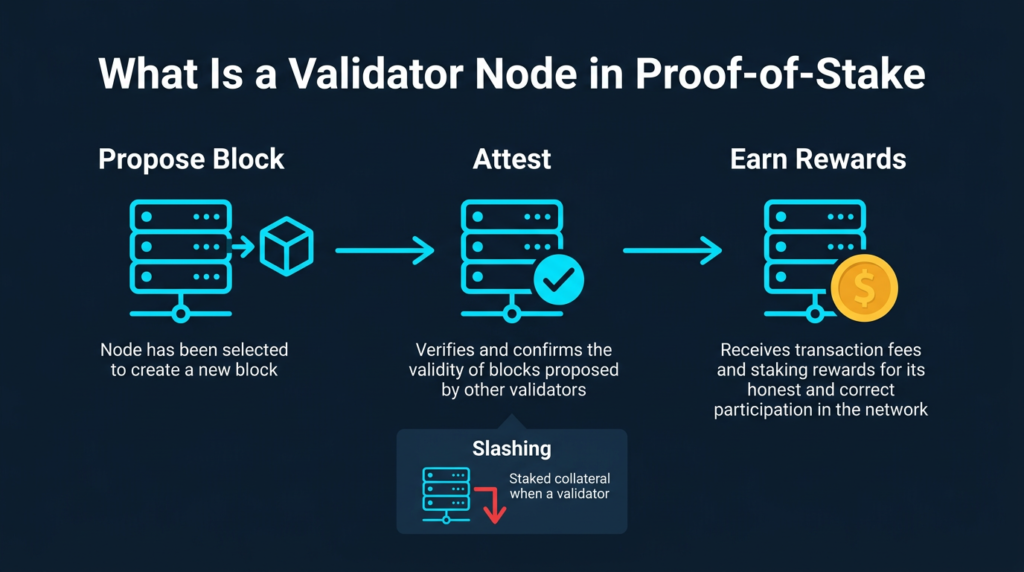
A validator node is a computer running software that participates in a proof-of-stake blockchain by proposing and verifying new blocks. Validators are selected based on the amount of cryptocurrency they have locked up as collateral, replacing the energy-intensive competition used in proof-of-work mining. When a validator performs its duties correctly, it earns rewards. When it behaves dishonestly or stays offline for extended periods, it loses a portion of its staked funds through a process called slashing.
This content is for educational purposes only and should not be considered financial or investment advice.
Simple Definition
A validator node is a piece of software running on a computer that verifies transactions and creates new blocks on a proof-of-stake blockchain. To become a validator, the operator must lock up a minimum amount of the network’s native token as collateral. That locked collateral is called a stake, and it creates a direct financial incentive to behave honestly. If a validator acts against the rules, the network destroys part of its stake.
Unlike proof-of-work miners who compete through raw computational power, validators are selected algorithmically based on their staked balance, randomness, and other protocol-specific factors. Different blockchains use different selection mechanisms, but the core principle is consistent: staked collateral replaces hardware investment as the cost of participation in consensus.
The term “validator” refers both to the software process and to the entity operating it. A single operator can run multiple validator instances, and some services aggregate thousands of validators under one organisation.
Why It Matters
Validator nodes are the security layer of proof-of-stake blockchains. They do not just process transactions. They collectively reach consensus on the canonical state of the chain. Without active validators, no new blocks are added and no transactions are finalized.
The design makes economic attacks expensive. To manipulate consensus on a large proof-of-stake network, an attacker would need to control enough validators to hold a supermajority of staked tokens. On Ethereum, this represents billions of dollars in capital that would also lose substantial value if the attack succeeded. The attacker’s collateral is at risk from the same network they are trying to corrupt.
Validators also generate yield. This is the mechanism behind staking rewards. When someone stakes ETH, SOL, ADA, or other proof-of-stake assets, they are funding a validator and earning a share of the block rewards it produces. Understanding this connection matters for anyone evaluating crypto passive income strategies, because the sustainability of staking yields depends directly on how validator economics function at the protocol level.
Not all staking yield is equal. A validator earning 4% annually on Ethereum operates under different risk parameters than a validator on a newer chain promising 15%. Before treating staking as a reliable income source, read about why high APY figures in crypto are often a warning sign rather than a feature.
How It Works
A validator node operates in a continuous cycle. The exact terminology varies across blockchains, but the underlying logic is broadly consistent across Ethereum, Solana, Cardano, Avalanche, and other proof-of-stake networks.
The Validator Lifecycle
- Deposit: The operator sends the minimum required stake to the network’s staking contract or deposit address. On Ethereum, this is 32 ETH sent to the official deposit contract.
- Activation queue: The deposit is processed and the validator enters an activation queue. Queue length depends on how many validators are joining the network at that time.
- Attestation: Once active, the validator regularly votes on the current state of the chain, confirming agreement with blocks being proposed by other validators. These votes are called attestations.
- Block proposal: Occasionally, the validator is pseudorandomly selected to propose a new block. Not every validator proposes every block. Selection depends on the network’s randomness mechanism.
- Finalization: When enough validators attest to a checkpoint, it becomes finalized. Finalized blocks cannot be reversed without destroying a massive portion of staked collateral across the network.
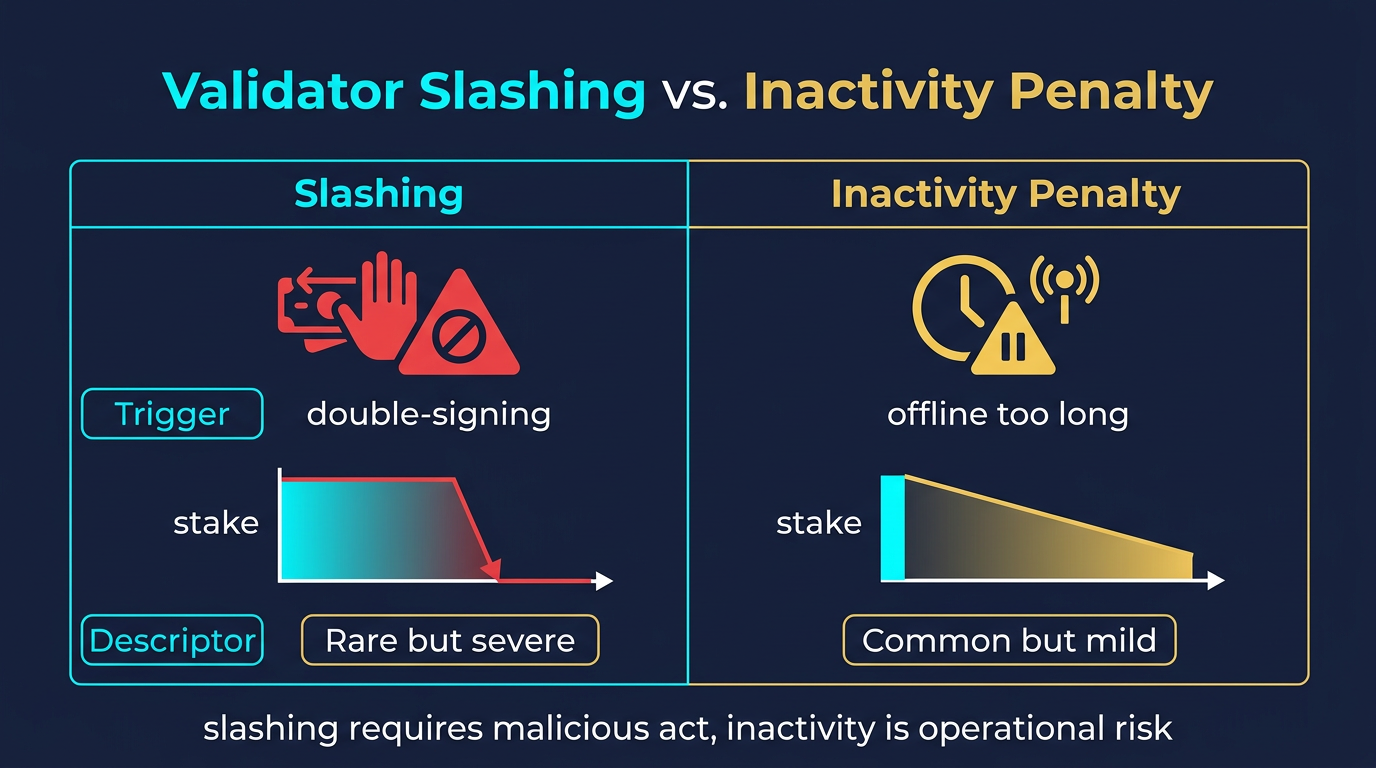
The validator must remain online and respond within defined time windows. Missing attestations results in small inactivity penalties that slowly erode rewards. Deliberately malicious actions, such as proposing two conflicting blocks for the same slot, trigger slashing.
Minimum Staking Requirements by Network
| Network | Minimum Stake | Notes |
|---|---|---|
| Ethereum | 32 ETH | Fixed minimum per validator instance |
| Solana | No fixed minimum | Hardware and operational costs are significant; typically run by professionals |
| Cardano | No fixed minimum | Stake pools use a delegation model; most users delegate rather than operate |
| Avalanche | 2,000 AVAX | Fixed minimum for primary network validators |
For most individual users, the capital requirement for solo Ethereum validation is the primary barrier. Staking pools and liquid staking protocols solve this by aggregating smaller deposits and running validators on behalf of depositors. For a broader overview of how staking compares across networks, see best staking coins for low-risk yields.
Solo Validation vs. Pooled Staking vs. Liquid Staking
| Method | Who Runs the Node | Minimum Entry | Reward Share | Key Control |
|---|---|---|---|---|
| Solo validation | You | Network minimum (e.g. 32 ETH) | Full rewards minus operational costs | Full control |
| Staking pool | Pool operator | Usually no minimum | Proportional share minus pool fee | Custodial or semi-custodial |
| Liquid staking | Protocol (e.g. Lido, Rocket Pool) | Usually no minimum | Proportional share minus protocol fee | Non-custodial, smart contract risk |
Ethereum’s official staking documentation provides authoritative guidance on running a solo validator: ethereum.org/en/staking/.
Common Mistakes
Confusing Delegation With Running a Validator
When someone “stakes” on a centralized exchange or through a liquid staking platform, they are not operating a validator. They are delegating their tokens to someone else’s validator and receiving a share of rewards minus fees. The distinction matters because the risks differ significantly. Delegation carries platform risk; solo validation carries operational and slashing risk.
Underestimating Uptime Requirements
Validators must be online consistently. Operators who set up a node and leave it unattended face accumulating inactivity penalties that quietly erode staking rewards over time. Running a validator is an operational commitment, not a one-time setup.
Using a Single Client Implementation
Most proof-of-stake blockchains have multiple independent client implementations. If the majority of validators run the same client and that client contains a critical bug, the network can experience a correlated failure. Running a minority client reduces this systemic risk for the network and for individual operators whose nodes might otherwise be swept up in a mass slashing event caused by a majority-client fault.
Running Duplicate Validator Instances
Operators sometimes attempt to eliminate downtime risk by running the same validator key on two machines simultaneously. This approach triggers slashing. The network interprets dual signing as a deliberate attempt to produce conflicting blocks and imposes severe penalties. Validator keys must run on exactly one active machine at any given time.
Treating Validator Keys Like Wallet Keys
Validator key management is different from managing a standard wallet. On Ethereum, validators use two separate keys: a signing key (used continuously during operation) and a withdrawal key (used only when exiting the validator set). Storing both keys in the same location or failing to secure the withdrawal key separately introduces unnecessary risk. Understanding self-custody principles provides foundational context for managing these keys correctly.
Security and Risk Considerations
The primary financial risk for validator operators is slashing. Slashing events destroy a portion of staked collateral and can result in forced ejection from the validator set. Slashing is triggered by two categories of provable misbehavior:
- Equivocation: Signing two different blocks for the same slot, which suggests the validator is trying to create a fork.
- Surround votes: Attesting to blocks in a way that contradicts previous attestations, indicating an attempt to rewrite history.
Beyond slashing, operators face several infrastructure risks:
- Key compromise: If the validator signing key is stolen, an attacker could deliberately trigger a slashable offense to destroy the operator’s staked collateral.
- Infrastructure failure: Cloud-hosted validators depend on provider uptime. Power outages, connectivity failures, and hardware faults all cause inactivity penalties.
- Client software lag: Running an outdated client after a protocol upgrade can disconnect the validator from the canonical chain, causing missed attestations and potential compatibility issues.
- Correlated slashing: During large slashing events, the network applies a correlation penalty that increases the slash amount when many validators are slashed simultaneously. Solo validators are less exposed to this than large staking pools.
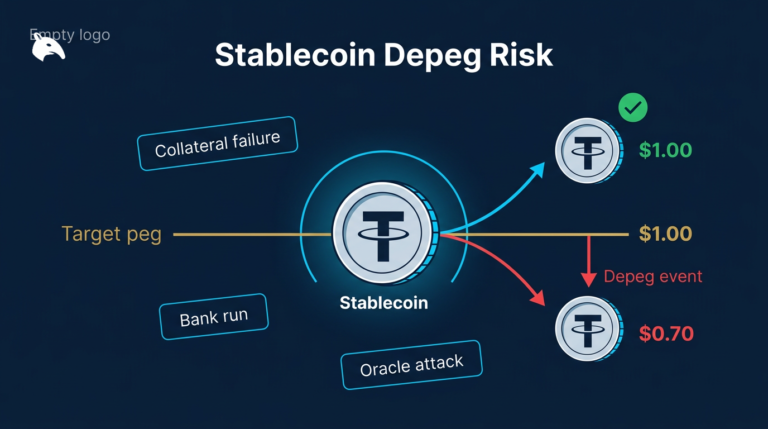
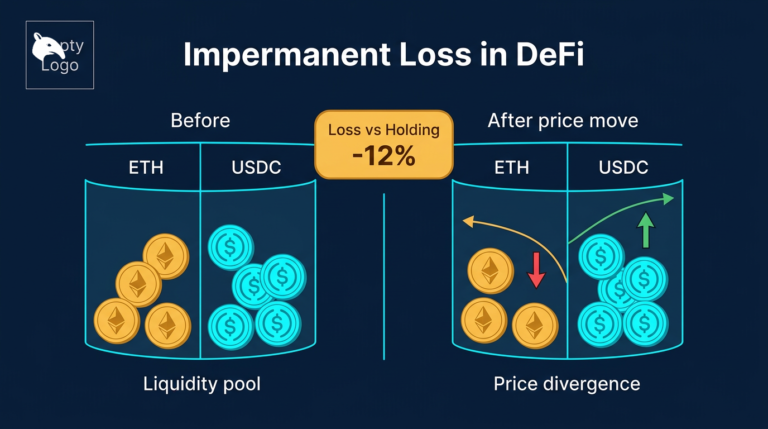
For users who delegate through staking pools or liquid staking protocols rather than running their own nodes, the risks shift. Smart contract vulnerabilities, protocol governance decisions, and custodial exposure replace the operational risks of solo validation. For a detailed look at what can go wrong in staking arrangements, see staking crypto: the real risks and yields.
Frequently Asked Questions
What is the difference between a validator node and a miner?
Miners secure proof-of-work blockchains by expending computational energy to solve cryptographic puzzles. Validators secure proof-of-stake blockchains by locking up token collateral. Miners compete; validators are selected. The economic mechanism is different, but both serve the same purpose: creating new blocks and maintaining consensus.
Do I need to run my own validator to earn staking rewards?
No. Most users earn staking rewards through delegation, staking pools, or liquid staking platforms without ever operating a node directly. Running a solo validator gives full control over the process and keeps the full reward, but it requires technical knowledge, ongoing maintenance, and meeting the network’s minimum stake requirement.
What happens if my validator goes offline?
A validator that goes offline stops earning attestation rewards and begins accumulating inactivity penalties. The penalty rate is proportional to how long the validator is offline and scales more severely if a large portion of the network is simultaneously offline. For brief outages, the financial impact is minor. Extended downtime causes meaningful losses relative to the rewards the validator would have earned.
What is slashing and when does it happen?
Slashing is a penalty mechanism that destroys a portion of a validator’s staked collateral when the validator commits a provably malicious or double-signing act. It does not happen from simply going offline. It is triggered by equivocation (signing conflicting blocks) or contradictory attestations. Accidental slashing most commonly occurs when operators run the same validator key on two machines at once.
Can I lose my entire stake as a validator?
In theory, yes, though in practice a complete loss from slashing alone is extremely unlikely for a solo validator. Slashing penalties start at a minimum floor (roughly 1/32 of the stake on Ethereum for a single incident) and scale up with correlation penalties if many validators are slashed simultaneously. The greater risk of total loss comes from key compromise or catastrophic infrastructure mismanagement rather than from protocol penalties.