Last Updated on March 13, 2026 by Snout0x
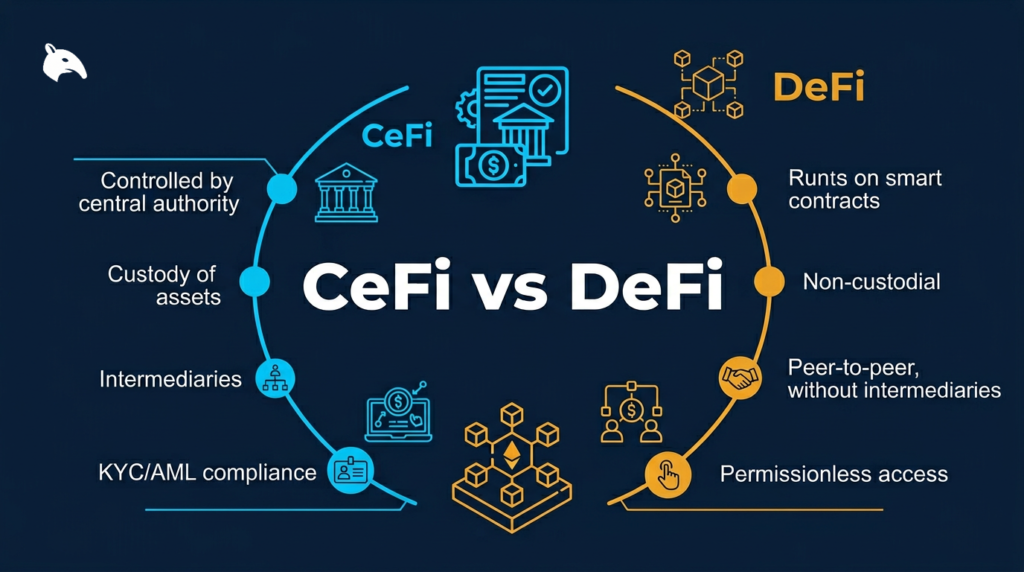
The debate around CeFi vs DeFi shapes how millions of crypto users store, trade, and earn on their holdings in 2026. Both systems exist because neither is complete on its own. Centralized Finance platforms provide the familiarity, customer support, and fiat access that bring most new users into crypto.
Decentralized Finance protocols offer transparency, direct asset control, and open access that more experienced users often prefer. Understanding how each system works, where each one carries real risk, and how to combine them intelligently is the foundation of a durable crypto strategy.
This article is for informational purposes only and does not constitute financial, legal, or tax advice. Always research any platform, wallet, or protocol thoroughly before depositing funds or signing transactions.
Key Takeaways
- The Core Trade-Off: CeFi requires trusting a company with custody and operations. DeFi requires trusting smart contracts while managing your own keys and security practices.
- CeFi Strengths: Centralized exchanges offer fiat on-ramps, account recovery, customer support, and simpler interfaces for beginners.
- DeFi Strengths: Decentralized protocols offer on-chain transparency, self-custody, and permissionless access without a central intermediary.
- The Practical Approach: Many users buy through CeFi, then move long-term holdings to self-custody or selected DeFi protocols to reduce counterparty risk.
- Tax Reality: Tax obligations still apply whether you use a CEX or a DEX. Once activity spreads across multiple chains and wallets, automated tracking becomes far more practical than manual spreadsheets.
What Is CeFi? Centralized Finance in 2026
Centralized Finance describes crypto services that operate through a company acting as a custodian or intermediary. When you open an account on Coinbase, Kraken, or Binance, you are usually not holding the crypto directly. The platform controls the wallets and private keys. You control an account login and a claim on the platform’s internal ledger.
This model resembles traditional finance in an important way. The company accepts deposits, manages custody, processes withdrawals, and often provides matching engines, order routing, and compliance systems behind the scenes. In exchange, users get convenience. The trade-off is trust.
If you need a refresher on the ownership side of this equation, see What Is a Private Key in Crypto? and What Is Self-Custody in Crypto?.
How CeFi Platforms Work
When you deposit Bitcoin onto a centralized exchange, the platform credits your account balance in its internal database. The actual coins are typically pooled in wallets controlled by the company. That is why CeFi platforms can feel so fast. Most user activity is handled internally until deposits or withdrawals touch the blockchain.
This architecture makes CeFi operationally efficient, but it also creates a structural weakness. If the company has poor risk controls, insufficient reserves, weak custody practices, or aggressive lending exposure, users may discover too late that the balance shown on-screen was only as reliable as the institution behind it.
The Case for Using CeFi
CeFi has real strengths, especially for beginners and for users who need regular movement between fiat and crypto.
Fiat on-ramps are the clearest advantage. Bank transfers, debit card purchases, recurring buys, and local payment rails are typically handled by centralized exchanges. For most users, CeFi is the easiest bridge between the banking system and public blockchains.
Account recovery is another practical benefit. Losing access to a CeFi account is stressful, but it is often fixable through identity verification and support channels. Losing access to a self-custody wallet can mean permanent loss if you do not control the recovery phrase.
Compliance and reporting also matter. Some users need transaction records, account statements, or more traditional interfaces for tax, banking, or business reasons. CeFi platforms make that easier than a fragmented DeFi workflow spread across multiple chains and wallets.
Select platforms may also offer limited insurance coverage for certain custodial events or fiat balances, but this should never be confused with blanket protection for all deposited crypto. The details vary, and users should read those terms carefully.
The Risks of CeFi
The central risk of CeFi is counterparty risk. Your assets are only as safe as the company that holds them, secures them, and manages them.
FTX showed how quickly this risk can become catastrophic. In November 2022, the exchange halted withdrawals and collapsed into bankruptcy after a major liquidity crisis became public. Billions in customer funds were tied up because users did not actually control the assets they believed they owned.
Celsius demonstrated a similar problem through a different pitch. It marketed yield as if it were a safe savings product, while directing user deposits into risky strategies and loans. When losses mounted and liquidity tightened, withdrawals were frozen and users were trapped in bankruptcy proceedings.
A major driver behind both failures was re-hypothecation: using customer deposits as collateral or investment capital elsewhere. When those positions fail, users discover that the “balance” on their dashboard was dependent on the institution remaining solvent.
Regulatory exposure is another real factor. CeFi companies operate under specific jurisdictions. Accounts can be frozen, services can be restricted, and withdrawals can be interrupted during enforcement actions, compliance reviews, or legal disputes.
For a practical breakdown of this risk, see Exchange Withdrawals Will Pause Again: The 2026 Self-Custody Survival Guide.
What Is DeFi? Decentralized Finance in 2026
Decentralized Finance describes financial protocols that run on public blockchains through smart contracts rather than a traditional company-operated backend. Protocols such as Uniswap, Aave, Lido, and Jupiter allow users to trade, lend, borrow, or stake without opening a standard custodial account.
In DeFi, you typically connect a self-custody wallet and interact directly with code. There is no support desk approving transactions on your behalf. There is also no company standing between you and the protocol in the same way as a centralized exchange.
How DeFi Protocols Work
When you use a decentralized exchange such as Uniswap, you connect a wallet and sign a transaction. That transaction is sent to a blockchain where a smart contract executes the logic. The contract checks the rules, processes the swap, and sends the resulting assets back to your wallet if the conditions are met.
Many DeFi protocols replace centralized order books with liquidity pools. Users deposit token pairs into shared pools, and traders swap against those reserves. Liquidity providers earn fees, while the protocol logic handles the pricing and execution on-chain.
The result is a system that is more transparent, but also less forgiving. There is usually no manual reversal if you sign the wrong transaction, approve the wrong contract, or send assets to the wrong chain.
The Case for Using DeFi
Transparency is one of DeFi’s strongest structural advantages. Activity happens on-chain, which means users can inspect transaction history, pool balances, token approvals, and smart contract interactions directly through block explorers and analytics tools.
Self-custody is another key benefit. Your assets remain under your control until you actively sign a transaction or deposit them into a protocol contract. No company can quietly lend your exchange balance to an external borrower without the same kind of visible on-chain interaction.
Permissionless access also matters. In many DeFi systems, a funded wallet and internet connection are enough to participate. There is no standard account creation process, and no centralized operator deciding whether your region, bank, or identity profile is acceptable.
The Risks of DeFi
DeFi shifts risk away from institutional solvency and toward technical risk, operational security, and user responsibility.
Smart contract risk is the biggest structural category. Bugs, flawed logic, bad upgrade controls, governance attacks, oracle failures, or bridge design weaknesses can all produce major losses. Audits help, but they do not eliminate this risk.
User error is equally important. Sending funds to the wrong address, signing a malicious approval, losing a seed phrase, or misreading a transaction prompt can result in irreversible loss.
Phishing and wallet-drain attacks are especially dangerous in DeFi because execution is immediate. A single approval or signature on a malicious site can grant access to tokens within seconds. For the security side of that risk, see What Is Crypto Phishing?.
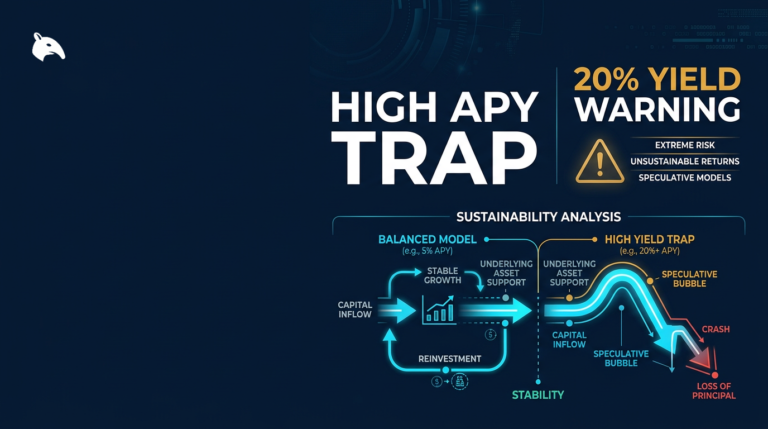
Unsustainable yield is another recurring problem. If a protocol advertises unusually high APY, users should ask where that yield is actually coming from. In many cases, it depends on token incentives, borrowed demand, or emissions that can disappear quickly. For a structured breakdown, see Why 20% APY Is a Trap.
CeFi vs DeFi: A Direct Comparison
The difference between CeFi and DeFi becomes clearer when the systems are compared directly.
| Feature | CeFi | DeFi |
|---|---|---|
| Asset Custody | Company holds keys | User holds keys |
| Account Recovery | Usually possible | No central recovery |
| Fiat On-Ramp | Yes | Usually no |
| Transparency | Limited, company-controlled | Mostly on-chain and auditable |
| Counterparty Type | Institutional | Technical / protocol-level |
| Protocol Failure Risk | Low direct protocol risk, high company risk | Yes, smart contract and design risk |
| User Error Recovery | Sometimes possible | Usually irreversible |
| Regulatory Exposure | High | Varies by chain, interface, and jurisdiction |
| Tax Reporting | Often easier | Usually more complex |
The Counterparty Risk Problem
Counterparty risk is the core conceptual divide between CeFi and DeFi. It refers to the possibility that the system you rely on fails when you need it most.
In CeFi, your counterparty is the company. If the exchange becomes insolvent, mismanages reserves, loses custody control, or is forced to freeze operations, your access to funds is affected directly.
In DeFi, the counterparty is the protocol design and the smart contract logic. Code cannot lie about an off-balance-sheet loan, but it can still contain bugs, dangerous assumptions, governance weaknesses, or exploitable vulnerabilities.
That is why the useful question is not “Which one is safer?” in the abstract. The useful question is which type of risk you actually understand and can manage responsibly.
How to Use Both Systems Without Getting Wrecked
In practice, many experienced users do not choose one system exclusively. They use each one for what it does well and reduce exposure to the areas where it fails.
Step 1: Use CeFi as an Entry Point
Centralized exchanges are still the easiest way to convert fiat into crypto. For many users, this is CeFi’s most legitimate role: onboarding, occasional trading, and moving value between the banking system and blockchain networks.
The practical rule is simple: do not leave more on a centralized platform than you are prepared to see frozen, restricted, or delayed.
Step 2: Move Long-Term Holdings Off the Exchange
Once you have purchased assets, decide where they belong long term. For many users, that means moving savings into self-custody rather than treating an exchange balance as permanent storage.
For long-term storage, a hardware wallet is often the cleanest security upgrade. If you need a starting point, see Best Crypto Wallets for Beginners 2026.
For users seeking yield, DeFi can make sense when the mechanism, protocol, and risk profile are understood clearly. That still requires wallet separation, approval hygiene, and realistic expectations about returns.
For a broader risk-aware passive income framework, see How to Earn Yield on Bitcoin and Staking Crypto in 2026: Risks & Real Yields.
Step 3: Apply Operational Security
If you use DeFi or self-custody at all, operational security is not optional.
- Store recovery phrases offline and never in cloud-connected notes or photo galleries.
- Use a separate wallet for DeFi activity instead of exposing your long-term storage wallet directly.
- Review and revoke old token approvals regularly.
- Verify URLs carefully before connecting a wallet to any protocol interface.
- Do not sign transactions you do not understand.
For a stronger security baseline, see Crypto Wallet Hygiene Checklist: 15 Rules to Avoid Getting Hacked.
Tax Implications for CeFi and DeFi Users
Tax obligations still apply whether you use CeFi, DeFi, or both.
CeFi platforms in regulated jurisdictions may provide transaction summaries or tax forms, but these are often incomplete once funds move across multiple wallets, exchanges, bridges, and chains.
DeFi usually creates even more complexity. Token swaps, liquidity actions, rewards claims, staking events, and bridge transfers can all create tax reporting obligations depending on jurisdiction. The lack of a neatly packaged form does not remove the obligation.
For active users, automated crypto tax software is usually more practical than rebuilding a year of on-chain activity manually. For a dedicated comparison, see Best Crypto Tax Software 2026: CoinLedger Review.
Risks and Common Mistakes
Treating Exchanges as Long-Term Storage
Many users treat an exchange account as if it were a wallet. It is not. An exchange is a service provider and trading venue. Leaving large balances there creates direct institutional exposure.
Ignoring Smart Contract Approval Risk
Approvals are one of the most overlooked risks in DeFi. Granting broad token permissions to a contract can leave assets exposed long after you stop using the protocol. This risk is especially dangerous when users sign first and review later.
Using a Single Wallet for Everything
Mixing long-term holdings and active DeFi usage in one wallet increases the blast radius of any mistake. Separating storage wallets from activity wallets is one of the simplest ways to reduce damage if something goes wrong.
Chasing Yield Without Understanding Its Source
Yield is not free. If a protocol advertises a high APY, users should understand whether that return is funded by real demand, token emissions, leverage, or temporary incentives. If the source is weak, the yield often disappears quickly.
Not Tracking Transactions From the Start
Crypto tax problems usually start long before tax season. Once activity spreads across multiple platforms and chains, reconstructing everything later becomes far harder than tracking it from day one.
Frequently Asked Questions
1. What is the main difference between CeFi and DeFi?
The main difference is custody and control. In CeFi, a company holds assets and processes activity through its own systems. In DeFi, users hold assets in their own wallets and interact directly with on-chain protocols.
2. What does “Not your keys, not your coins” actually mean?
It means ownership in crypto depends on control of the private keys. If an exchange holds the keys, you hold a claim on the platform rather than full direct control of the asset.
3. Is DeFi safer than CeFi?
Not automatically. CeFi concentrates institutional and custodial risk. DeFi concentrates technical and operational risk. Which one feels safer depends largely on the user’s habits, knowledge, and security discipline.
4. What is re-hypothecation and why does it matter in CeFi?
Re-hypothecation means customer assets are reused elsewhere as collateral or investment capital. If those positions fail, the platform may not have enough reserves to satisfy all user withdrawals.
5. Do I have to pay taxes on DeFi transactions?
In many jurisdictions, yes. Swaps, liquidity events, staking rewards, and yield claims can all create reporting obligations. Users should verify local tax treatment rather than assuming DeFi activity is invisible or exempt.
Conclusion
CeFi and DeFi solve different problems. CeFi makes crypto easier to access. DeFi makes financial activity more transparent and more directly controlled by the user.
Neither system removes risk. CeFi introduces company risk, insolvency risk, and regulatory dependency. DeFi introduces smart contract risk, phishing risk, approval risk, and irreversible user error.
For most users, the practical strategy is not blind loyalty to one model. It is understanding where each one is useful, then limiting exposure to the failures each one makes possible.
If you are still building your foundation, start with Crypto Starter Guide 2026.
Join the Neighborhood
For daily market context, risk analysis, and practical crypto strategy, follow @Snout0x on X.
Not your keys, not your coins.