Last Updated on April 14, 2026 by Snout0x
In crypto, phishing is an attack in which an adversary impersonates a trusted service, wallet interface, or website to trick users into entering their seed phrase, private key, or credentials. It is one of the most common causes of fund loss because the attack targets human behavior rather than protocol vulnerabilities. No software patch can fully protect against a user who enters their seed phrase into a fraudulent site.
This content is for educational purposes only and should not be considered financial or investment advice.
How the Attack Works
The attacker creates a copy of a legitimate site or sends a message that appears to come from a trusted source. The target, believing the site or message is genuine, provides sensitive information. Once entered, seed phrases and private keys are captured and funds are drained immediately.
Common phishing vectors include:
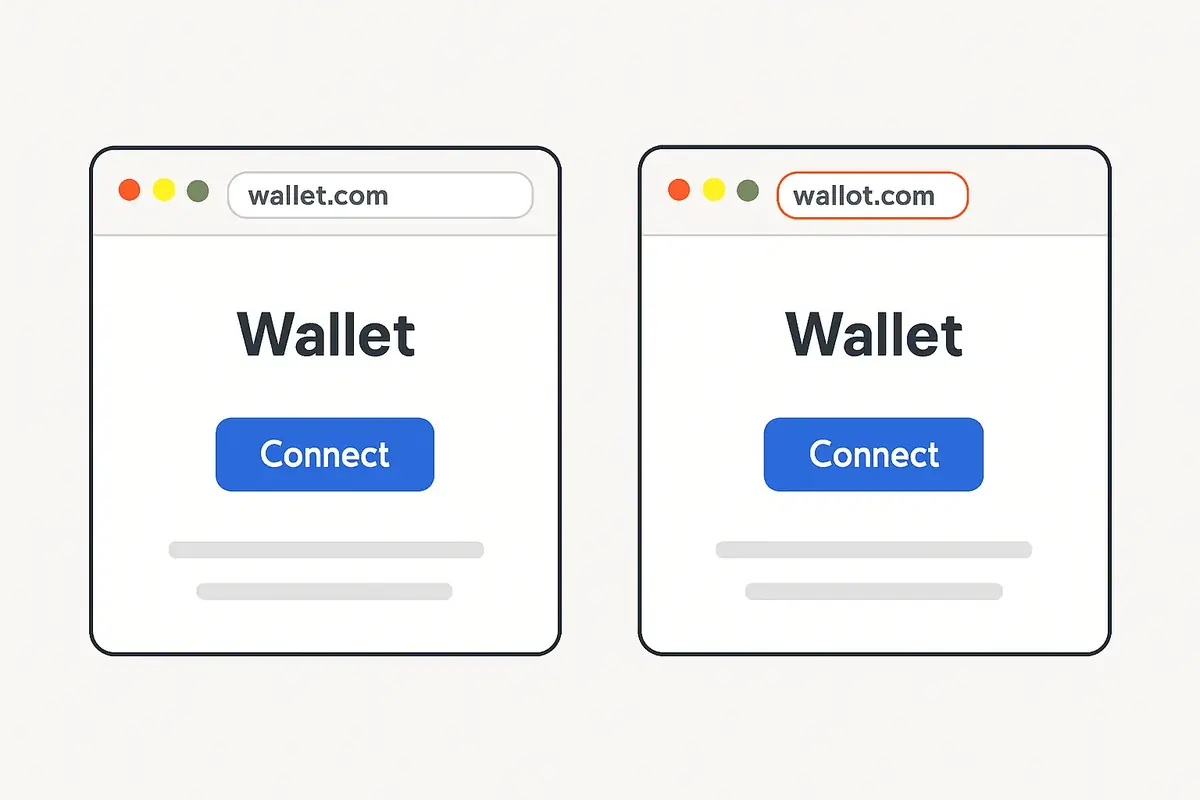
- Fake websites. A domain nearly identical to a real one (e.g. “Iedger.com” instead of “ledger.com”) hosts a copy of the real interface and asks for a seed phrase under the guise of “wallet recovery.”
- Email campaigns. Emails claiming a security alert, account action required, or unauthorized access link to a fraudulent login page.
- Social media impersonation. Fake support accounts on X (formerly Twitter), Discord, and Telegram reach out to users who post wallet issues and offer “help.”
- Malicious browser extensions. Extensions disguised as legitimate wallet tools intercept seed phrase input or inject malicious code into pages.
- Fake wallet apps. Counterfeit app store listings mimic legitimate wallet apps and capture everything entered at setup.
Why Seed Phrases Are the Primary Target
A seed phrase gives access to all keys derived from a wallet. Capturing it gives the attacker permanent, irrevocable control of every address and asset in the wallet hierarchy. Unlike a password, there is no reset mechanism. Once a seed phrase is compromised, the only defense is to move funds to a new wallet before the attacker drains them.
Legitimate hardware wallet vendors, wallet apps, and exchanges never ask for your seed phrase. No support agent, pop-up, or wallet interface needs your seed phrase to function. Any prompt asking for it is a phishing attack.
Practical Usage: How to Check for a Phishing Attempt
- The URL domain is slightly different from the real one (extra characters, different TLD, or misspellings).
- The message creates urgency: “Your wallet will be suspended,” “Verify now,” or “Action required.”
- The interface asks for your seed phrase, private key, or full mnemonic for any reason.
- An unsolicited contact on Discord, Telegram, or Twitter offers support or a special opportunity.
- The SSL certificate is present but the domain name does not match the expected official domain.
Risks and Common Mistakes
The most common mistake is trusting urgency. Attackers engineer situations that make you feel you must act immediately or lose access. Slowing down breaks the psychological loop the attack relies on. A wallet security checklist turns these defensive habits into a repeatable process.
Other mistakes include clicking links in emails or direct messages without independently navigating to the site, installing browser extensions without verifying publisher identity and review count, and joining unofficial Discord servers for wallet support where impersonation is widespread.
If the fake site is pushing a wallet connection or approval prompt rather than asking for a recovery phrase directly, the next concept to understand is What Is a Crypto Drainer. That is a related attack path, but it works through malicious approvals instead of direct credential theft.
Frequently Asked Questions
Can a hardware wallet protect against phishing?
Partially. A hardware wallet keeps private keys offline and requires physical confirmation of transactions. But if you enter your seed phrase into a phishing site, the attacker has the keys and the hardware wallet provides no protection. The device protects against remote signing attacks, not against direct seed phrase disclosure.
Is it phishing if I connect my wallet to a fake site?
Connecting a wallet does not reveal the private key. However, connecting to a malicious site can result in being prompted to approve token permissions (approvals) that allow a contract to transfer your funds. This is a related but distinct attack type, often called a drainer attack.
Why do phishing attacks work so well in crypto?
It exploits trust, urgency, and the complexity of crypto interfaces. Users who are not familiar with how wallet recovery works may believe a site asking for a seed phrase is legitimate. The stakes are high and transactions are irreversible, which pressures users into acting quickly.
What should I do if I entered my seed phrase on a phishing site?
Act immediately. Create a new wallet with a fresh seed phrase and transfer all assets from the compromised wallet as fast as possible. Assume the attacker has the seed phrase and is monitoring the address. Speed is the only variable in your favor at this point. Going forward, a two-wallet setup limits the blast radius if a single wallet is compromised.
Do phishing attacks also target DeFi users?
Yes. DeFi phishing often takes the form of fake governance vote links, fake airdrop sites, or malicious smart contract approval prompts. These attacks reach users through Discord announcements, X posts from compromised official accounts, and fake token claim pages.