Last Updated on April 16, 2026 by Snout0x
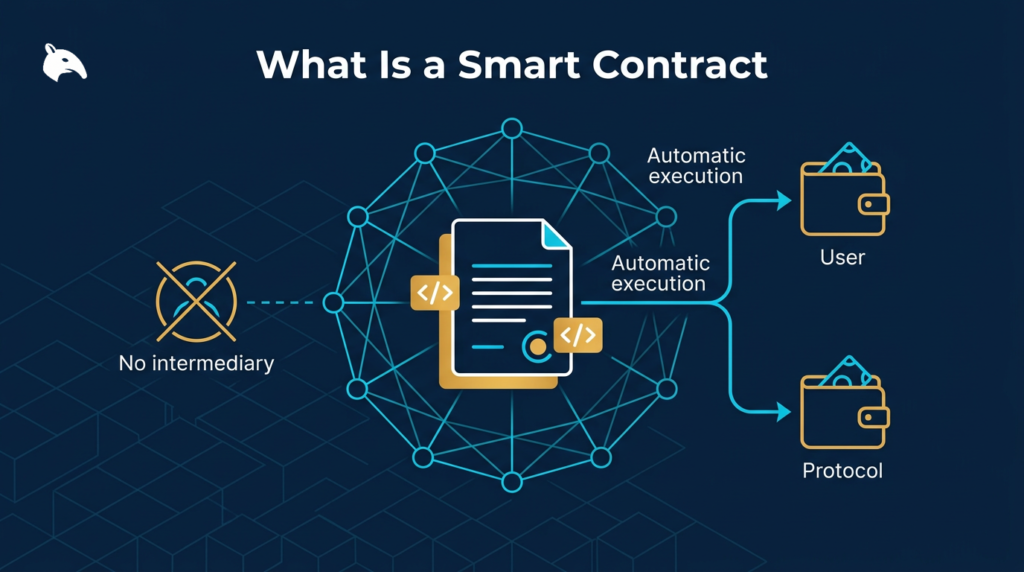
A smart contract is a program that runs on a blockchain. Like a traditional contract, it encodes rules and conditions. Unlike a traditional contract, it executes those rules automatically and permissionlessly, without requiring a court, an intermediary, or either party’s active participation at the time of execution. If the conditions coded into the contract are met, the contract executes. If they are not met, it does not. No human judgment is required in between.
A simple way to think about a smart contract is as a vending machine on a blockchain. If you insert the right input, the machine delivers the programmed output. If you do not, it does nothing. The important difference is that the machine is public, verifiable, and runs the same way for everyone who uses it.
For the broader overview around this topic, see What Is Blockchain?.
This content is for educational purposes only and should not be considered financial or investment advice.
Where This Code Lives
A smart contract is code deployed to a blockchain that executes automatically when its conditions are met. No one can stop it, modify it, or reverse its outputs once the transaction triggers it.
Smart contracts are most prominently associated with Ethereum, which was the first blockchain to provide a general-purpose environment for deploying them. On Ethereum, smart contracts are programs compiled into bytecode and deployed to a specific address on the blockchain. Once deployed, the code is immutable (unless specific upgrade patterns are designed in). Anyone can interact with the contract by sending a transaction to its address, paying gas fees to execute its logic.
Many other blockchains now support smart contracts: Solana, BNB Chain, Avalanche, Polkadot, and others. Each has a different execution environment with different programming languages and performance characteristics, but the core concept is the same: code that lives on the blockchain and executes deterministically when called.
How On-Chain Code Executes
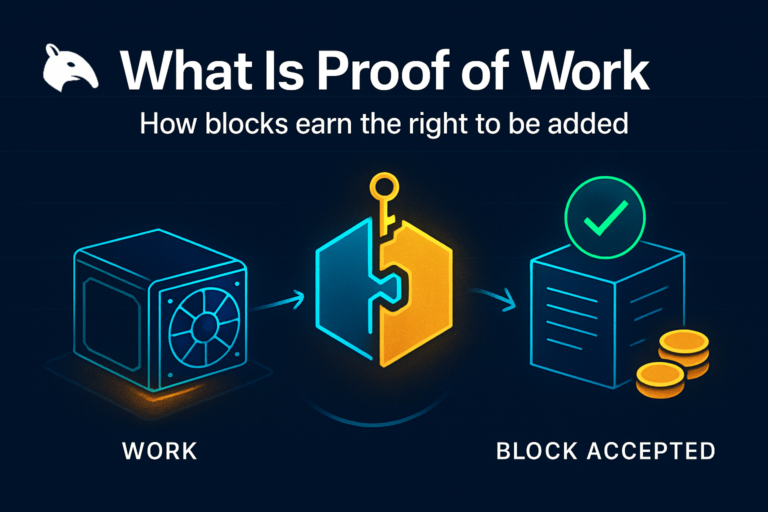
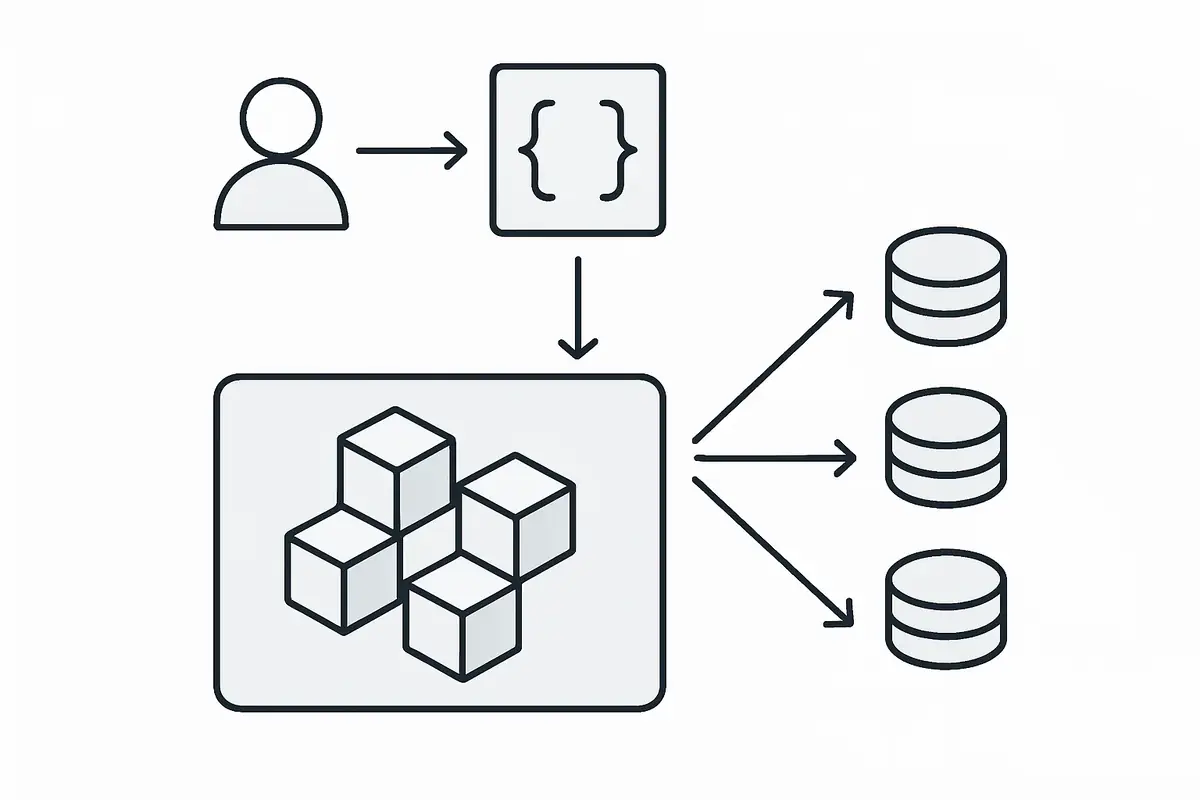
When you interact with a smart contract, you send a transaction to the contract’s address. The transaction includes any input data the contract needs (function arguments) and any ETH to send as part of the interaction. Miners and validators include this transaction in a block. When the block is processed, every node in the network executes the contract’s code in sequence and updates the blockchain state based on the result.
Every node gets the exact same result because the execution is deterministic: given the same inputs and the same state, the contract always produces the same output. This determinism is what allows a global network of independent nodes to reach consensus on what the contract did without trusting each other.
The intuitive point is that the blockchain is not trusting the contract because it is “smart.” It is trusting it because every node can verify the same execution path independently. That is why deterministic code matters more than clever code in this environment.
Practical Usage: Reading What the Code Will Do
In practice, most users do not deploy on-chain programs themselves. They interact with them through wallets, decentralized exchanges, lending apps, and token approval prompts. The practical check is to treat every contract interaction like a permission request: verify the contract address, read what action is being requested, and understand whether you are sending funds, granting an approval, or only signing a message.
For a closely related follow-up, see UTXO Consolidation Explained: What It Is and When to Do It.
In practice, most smart-contract risk shows up as wallet prompts. The useful check is to ask what the code is being allowed to do to your assets right now. If the answer is unclear, the interaction is not ready to sign.
For the exploit side of this idea, What Is a Crypto Drainer? is the more relevant local follow-up. Drainers work precisely because ordinary wallet actions can call smart-contract functions that users do not fully understand.
For example, before confirming a token approval in a wallet, check whether the request is for an exact spend amount or an unlimited allowance. Before swapping on a decentralized exchange, verify that the contract you are about to call is the official one used by that protocol. These small checks are how ordinary users apply the concept safely rather than treating all contract prompts as interchangeable.
What This Code Can Do
- Hold and transfer funds. A smart contract can hold ETH or tokens and release them when conditions are met (time locks, multisig approvals, oracle price feeds).
- Issue and manage tokens. ERC-20 and ERC-721 tokens are smart contracts. The token’s supply, transfer rules, and ownership records are all managed by contract code.
- Enable decentralized exchanges. Uniswap, Curve, and other DEXs are smart contracts that hold liquidity pools and execute trades algorithmically without a centralized order book.
- Automate lending. Aave and Compound are smart contracts that automate borrowing and lending: managing collateral, interest rates, and liquidation triggers entirely on-chain.
- Encode governance. DAOs use smart contracts to count votes, execute proposals, and manage protocol treasuries based on token holder participation.
What This Code Cannot Do
Smart contracts cannot access data outside the blockchain on their own. They cannot check a website, fetch a stock price, or read a news feed. To bring external data on-chain, they use oracles: services that read external data and provide it to smart contracts through on-chain transactions. Chainlink is the most widely used oracle network.
Smart contracts cannot be reversed. Once deployed, the code runs exactly as written. A bug in the contract is permanent unless the contract was designed with an upgrade mechanism. The 2016 DAO hack on Ethereum resulted in $60 million of ETH being drained because of a reentrancy bug in the contract code. The only resolution was a contentious hard fork of Ethereum itself to reverse the transactions, which led to the creation of Ethereum Classic. Most bugs today are handled by deploying new contracts and migrating users, not by reversing transactions.
Understanding smart contracts also helps explain how drain attacks work. Token approvals, which are used by drainers to transfer funds, are themselves a function of ERC-20 smart contracts. For more on this, see What Is a Crypto Drainer.
Risks and Common Mistakes
Smart contracts introduce specific security risks that traditional software does not:
For a closely related follow-up, see Bitcoin vs Ethereum Transaction Model: Two Different Ways Blockchains Track Value.
For a closely related follow-up, see Wallet Address Reuse Risks: What It Exposes On-Chain.
- Code immutability. Bugs are permanent unless upgrade patterns were designed in from the start. A single vulnerability can drain a protocol’s entire treasury.
- Oracle manipulation. Contracts that rely on price oracles can be attacked by manipulating the oracle’s input, causing the contract to execute at artificial prices.
- Reentrancy. A malicious contract can call back into the victim contract during a transaction, repeating withdrawals before balances are updated. This was the DAO hack’s mechanism.
- Economic design flaws. Even technically correct code can behave unexpectedly under adversarial market conditions. Flash loan attacks use large temporary loans to manipulate on-chain prices and exploit economic assumptions in protocols.
These risks are why security audits from reputable firms are important signals before interacting with new DeFi protocols. An unaudited protocol may have working code, but its correctness has not been independently verified.
A common mistake is assuming that a popular interface makes the underlying code safe. For example, a user may connect a wallet to a new yield app, see a polished dashboard, and approve an unlimited token allowance without checking whether the contract has been audited or whether the approval can later be abused. The consequence is not theoretical: if the logic is flawed or malicious, funds can be drained exactly as authorized, with no central party able to reverse it.
That is also why “code is law” is only half the story. The code will enforce the rules exactly as written, but users still have to judge whether those rules are safe, fair, and correctly implemented before they interact with them.
Frequently Asked Questions
Who can deploy a smart contract?
Anyone with the ability to pay gas fees can deploy a smart contract on a permissionless blockchain like Ethereum. There is no application process, no regulatory approval, and no identity verification required. This openness is what makes DeFi permissionless but also what allows malicious contracts to be deployed freely.
Can smart contracts be hacked?
Not in the traditional sense of “someone breaks into a server.” Smart contract exploits target bugs in the code logic. If the code has a vulnerability, an attacker can interact with the contract in a way that triggers the vulnerable behavior. The contract executes as written, but the attacker structured the input to produce an unintended and profitable outcome.
Are smart contracts legally binding?
This is an evolving legal question. The code executes automatically and on-chain regardless of legal status. Whether a smart contract constitutes a legally enforceable agreement depends on jurisdiction, the parties involved, and the nature of the interaction. Some jurisdictions (Wyoming, Wyoming DAO LLC law, for example) have begun creating legal frameworks for smart contract-based entities. Most contract interactions in DeFi lack the specific legal prerequisites for traditional contract enforceability.
What language are smart contracts written in?
Ethereum smart contracts are most commonly written in Solidity, a high-level language designed for EVM bytecode compilation. Vyper is a simpler, more security-focused alternative. Solana uses Rust or C for its programs. Other ecosystems have their own languages. The compiled bytecode, not the source code, runs on the blockchain, though source code verification (Etherscan verified contracts) allows users to review the original logic.