Hot vs. Cold Wallets 2026: The Ultimate Security Guide to Not Getting Rekt
Last Updated: February 15, 2026 Author: Snout0x
Transparency Note: This guide contains affiliate links. If you buy a wallet through my link, I may earn a commission at no extra cost to you. This supports the blog and helps me keep the content free. Disclaimer: This is not financial advice (NFA). I am not a financial advisor. This content is for educational and entertainment purposes only. I’m just a guy in the trenches sharing my personal research. Crypto is a volatile asset class; your money is your responsibility. Always do your own research (DYOR) before making any investment.
Think your crypto is safe? In 2026, exchange hacks and AI phishing are industrialized. Learn the brutal truth about Hot vs. Cold wallets, why “Not Your Keys, Not Your Crypto” is your only defense, and how to pick a fortress for your bags.
Key Takeaways: The 2026 Security Doctrine
-
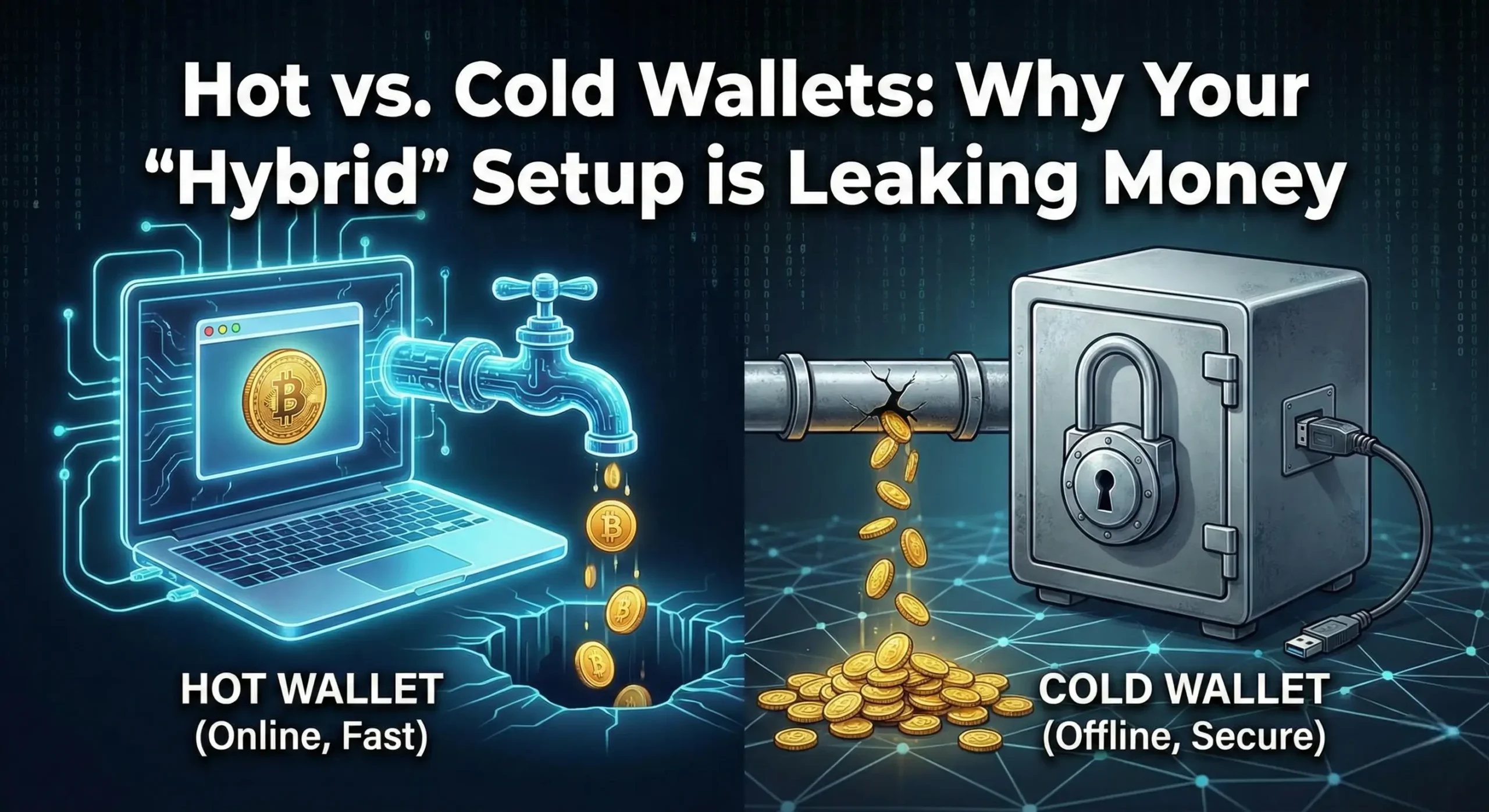
The “Cash vs. Vault” Rule: Hot Wallets (MetaMask, Phantom) are like carrying cash in a clear bag—fast but vulnerable. Cold Wallets (Ledger, Trezor) are buried vaults. Your private keys never touch the internet, making remote hacking impossible.
-
The 90/10 Strategy: Never keep your whole stack online. Keep 90% of your net worth in Cold Storage for long-term preservation and only 10% in Hot Wallets for daily trading and gas fees.
-
The “Industrialized” Threat: Hacking is no longer just a lone teenager. In 2026, AI-driven phishing and Deepfake Identity Synthesis can bypass biometric security. If you rely solely on passwords or face ID, you are outgunned.
-
The “Not Your Keys” Reality: If your funds are on an exchange, you do not own them; you have an IOU. As seen in the Bybit and Global-e incidents, even “secure” platforms are targets for supply chain attacks.
-
The Quantum Horizon: Security is moving beyond simple passwords. The shift to Quantum-Resistant signing (like in the Trezor Safe 7) and Air-Gapped hardware (SafePal S1) is now mandatory to protect against future decryption threats.
The 2026 Reality Check: Beyond the Script Kiddies
It’s 2026, and the industry has evolved into a digital battlefield. We aren’t just dodging sketchy Telegram links anymore; we’re fighting Deepfake Identity Synthesis where AI can clone your voice and face in real-time to bypass biometric “security” during a support call. In fact, deepfake attacks now account for nearly 40% of all biometric fraud attempts.
In early 2025, the Bybit hack orchestrated by the Lazarus Group drained $1.5 billion in a single afternoon. They didn’t even attack the exchange’s main vault directly; they compromised a third-party multi-sig vendor (Safe{Wallet}) and used social engineering to trick executives into signing “routine” transactions.
If you’re still relying on an exchange’s “2FA” or a hot wallet, you aren’t a HODLer; you’re an unpaid intern for a criminal organization. Digital sovereignty is no longer a luxury; it’s the only way to survive the macroeconomic debt collapse.
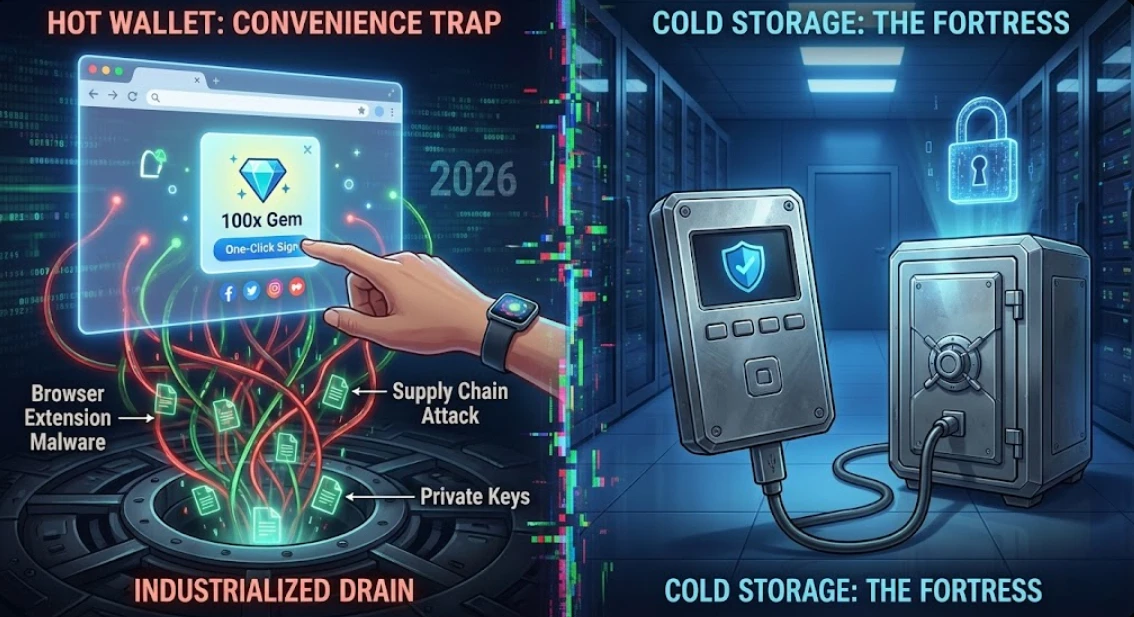
What is Cold Storage? (The Fortress)
Cold storage is the act of keeping your private keys the literal DNA of your wealth completely disconnected from the internet. When you use a cold wallet, your private keys are generated inside a secure chip that has no physical way to “speak” to the web. This is the Air Gap.
The Neighborhood Analogy: > * A Hot Wallet: Like carrying $100k in cash in a clear plastic bag while walking through a crowded terminal.
-
A Cold Wallet: Like having that same wealth locked inside a 10-ton safe buried in an undisclosed bunker. Even if the thief knows the safe exists, they can’t touch the contents without your physical key and the “location” of the bunker.
The Architecture of Isolation: The Postman Protocol
In 2026, true cold storage utilizes Secure Elements (SE) specialized silicon (often EAL6+ certified) designed to resist physical tampering and side-channel attacks. When you “sign” a transaction, your computer acts as a blind postman:
-
The Drop: The PC sends the raw, unsigned data (the letter) to the wallet.
-
The Signing: The chip signs it internally (stamps the wax seal) in total darkness, often using a “false operation” alongside the real one to confuse power-analysis attacks.
-
The Delivery: Only the finalized digital signature is sent back out.
Your private key never not even for a millisecond leaves that piece of silicon. This is how we maintain OpSec in a world where AI-enabled scams are now notably more profitable than traditional ones.
Why 2026 is the Year of the “Bunker”
We’ve graduated to Industrialized Drainers. Large-scale criminal organizations like “Inferno Drainer” now use automated AI bots to scan for exposed keys and weak signatures 24/7. These bots can now bypass traditional “Know Your Customer” (KYC) checks using synthetic identities that are practically indistinguishable from real humans.
Cold storage turns your compromised, virus-ridden PC into a harmless “courier.” It can see the transaction, but it cannot alter it or steal the “ink” (your private key) used to sign it. This is how you sleep during a supply shock.
Hot vs. Cold: Why the Choice Matters Now
The Convenience Trap: The Rise of Industrialized Drains
Hot wallets are addictive. They’re built into your browser, integrated with your social media, and one click away from every “100x gem.” But in 2026, browser extension malware has become the #1 cause of wallet drains.
This isn’t just about clicking a bad link. Attackers are now deploying Supply Chain Attacks where they purchase popular, legitimate browser extensions and push malicious updates through the official Chrome or Firefox stores. You think you’re just updating your “ad blocker” or “dark mode” tool, but in reality, you’ve just installed a keylogger specifically designed to watch for your MetaMask password.
Because hot wallets keep your private keys in your browser’s local storage, they are “online” by definition. In 2026, we’ve seen “Extension Hollowing” where a malicious script hides inside a legitimate app’s code, waiting for you to unlock your wallet so it can exfiltrate your mnemonic phrase to a remote server. The convenience of “Click, sign, done” is exactly what hackers use to bait the trap.
The Sovereignty Shift: The Quantum Shadow
Cold wallets like the Trezor Safe 7 are now leading the Sovereignty Shift by adding Quantum-Resistant features. You might think quantum computers are a “future problem,” but in 2026, the threat model has shifted to “Harvest Now, Decrypt Later” (HNDL).
Adversaries ranging from state-level actors to elite cyber-cartels are currently scraping and storing massive amounts of encrypted blockchain data. Their goal is simple: wait. They are betting that in 5 to 10 years, quantum computers will be powerful enough to run Shor’s Algorithm, which can derive a private key from a public key in seconds.
If you are using old-school ECDSA (Elliptic Curve Digital Signature Algorithm) signatures, your “cold” wealth might be visible to the future’s biggest crowbar. The Sovereignty Shift is about migrating to NIST-standardized post-quantum cryptography (like ML-DSA or SLH-DSA). By using a wallet that supports these hybrid signature schemes today, you aren’t just protecting your money from today’s script kiddies; you’re protecting your 2030 portfolio from the most powerful computers ever built.
If you aren’t thinking about the quantum horizon today, you’re essentially leaving your vault door unlocked for the future.
The Air-Gap Reality Check
The ultimate form of this shift is the QR-code based Air-Gap.
Wallets like the SafePal S1 take the “fortress” analogy literally. They have no Bluetooth, no WiFi, and no USB data pins.
You initiate a transaction on your phone, it shows a QR code, you scan it with the wallet’s camera to sign it, and the wallet shows a return QR code for your phone to scan.
In a world where Zero-Click exploits can take over a smartphone just by receiving a hidden text message, having a device that physically cannot talk to a network is the only way to achieve true peace of mind.
In the 2026 trenches, “Cold” isn’t just a state of mind it’s a physical necessity.
The 2026 Cold Storage Arsenal: Top Recommendations
You don’t just buy a wallet; you buy a philosophy. Here is the low-down on the big three.
Trezor Safe 7: The “Don’t Trust, Verify” King
Trezor is the gold standard for transparency. The Safe 7 is fully open-source, meaning anyone can audit the code. In 2026, they introduced the TROPIC01 Secure Element, which fixed the old physical vulnerability issues while keeping everything auditable. It’s the “purest” form of self-custody.
-
Best For: Long-term HODLers and Bitcoin maximalists.
Ledger Nano X: The Mobile Degen’s Choice
Ledger dominates the NFT and altcoin space. The Nano X is sleek, has Bluetooth, and works flawlessly with your phone. However, the 2026 Global-e data breach reminded us that while Ledger’s hardware is safe, their corporate database is a target. If you can handle the “closed-source” drama, it’s the most convenient device on the market.
-
Best For: Active traders and NFT hunters.
SafePal S1: The Air-Gapped Trench Warrior
If you’re paranoid (like me), SafePal is the way. The S1 is 100% air-gapped. It has no Bluetooth, no WiFi, and no USB connection for signing. It uses a camera to scan QR codes. If anyone tries to physically open the chip, it has a self-destruct mechanism. All this for under $50.
-
Best For: High-security on a budget.
Deep Dives to Level Up Your Knowledge
-
Ledger Nano X vs. Trezor Safe 7: The 2026 Showdown: A brutal side-by-side comparison of the two titans.
-
7 Essential Crypto Tools 2026: My updated list of what I actually use to survive the trenches.
-
Best Crypto Wallets for Beginners 2026: Safe, easy, and verified options for new fish.
-
Mobile Wallet Security 2026: 5 Critical Risks: Why your iPhone is a ticking time bomb for your stack.
-
2026 Crypto Passive Income Audit: How I’m earning yield safely without risking the “bunker” funds.
Follow the grind on X: @Snout0x for daily reality checks, sarcastic macro insights, and the occasional “I told you so” when the next hot wallet exploit drops.
FAQ
Is a “Hot Wallet” really that dangerous?
Snout0x says: It’s not dangerous until it is. It’s like driving without a seatbelt. You’re fine for years until you hit a patch of ice (or a malicious dApp). Use them for gas money, not your life savings.
Can I use a hardware wallet and still get hacked?
Snout0x says: Yes, but only if you’re the weak link. If you type your 24-word seed phrase into a “support website” or a fake airdrop page, no hardware in the world can save you. The device protects the key; you have to protect your brain.
What happened in the 2026 Ledger leak?
Snout0x says: It wasn’t a hack of the wallets. It was a breach of a third-party payment processor (Global-e). Hackers got names and emails. Your crypto is safe, but your inbox is now a warzone for phishing. Stay alert.
Why is Trezor Safe 7 more expensive than the Safe 3?
Snout0x says: You’re paying for the Quantum-Ready hardware and the color touchscreen. If you’re just starting, the Safe 3 is a great entry, but the Safe 7 is the “forever” wallet.

Subscribe to our newsletter
Enjoy exclusive special deals available only to our subscribers.

