How public keys become wallet addresses is one of the most important concepts in cryptocurrency security. When someone sends you crypto, they are not sending it directly to your public key. Instead, they send it to a wallet address, a shorter identifier derived from the public key through cryptographic hashing and encoding.
This design allows blockchains to verify ownership of funds without exposing sensitive cryptographic keys on the blockchain. It also explains why wallet addresses look random, why wallets generate new addresses automatically, and why address reuse can weaken privacy.
Understanding how this derivation process works helps investors better understand wallet security, transaction verification, and how modern crypto wallets protect users.
Disclaimer: This content is for educational and informational purposes only and does not constitute financial, investment, tax, or legal advice. Cryptocurrency markets are volatile and involve risk. Always conduct your own research and consult a qualified professional before making financial decisions.
Affiliate Disclosure: Some links in this article may be affiliate links. If you choose to use them, I may earn a commission at no additional cost to you.
Key Takeaways
- Wallet addresses are derived from public keys using cryptographic hash functions.
- Bitcoin addresses use SHA-256 and RIPEMD-160 hashing.
- Ethereum addresses are derived from the Keccak-256 hash of a public key.
- Checksums help detect accidental address typing errors.
- HD wallets generate many addresses from a single seed phrase.
How Public Keys Become Wallet Addresses in Simple Terms
Cryptocurrency wallets follow a simple chain of cryptographic derivation:
- Private key
- Public key
- Wallet address
The private key is a randomly generated 256-bit number that proves ownership of funds. Wallet software uses elliptic curve cryptography to derive a corresponding public key from this private key.
The public key allows the network to verify signatures without exposing the private key itself. From that public key, the wallet generates a wallet address through hashing and encoding rules defined by the blockchain protocol.
These transformations are intentionally one-way. While a public key can be derived from a private key, reversing modern cryptographic hashes to recover the original key is considered computationally infeasible.
Key Derivation Flow: From Private Key to Wallet Address
The transformation from private key to wallet address follows a predictable cryptographic flow. Each step derives a new value while preserving the mathematical relationship between them.
- Private Key → Public Key (elliptic curve cryptography)
- Public Key → Hash (SHA-256 / RIPEMD-160 or Keccak-256)
- Hash → Address Format (Base58Check or hexadecimal)
This layered process protects the private key while still allowing anyone to send funds to the correct destination address.
Public Key vs Wallet Address
A common beginner misunderstanding is thinking a public key and wallet address are the same thing. They are related, but they serve different roles.
| Component | Role | Visibility |
|---|---|---|
| Private Key | Controls ownership of funds | Must remain secret |
| Public Key | Verifies digital signatures | Revealed when spending funds |
| Wallet Address | Destination used to receive crypto | Shared publicly |
In simple terms, a wallet address is a user-friendly identifier derived from the public key.
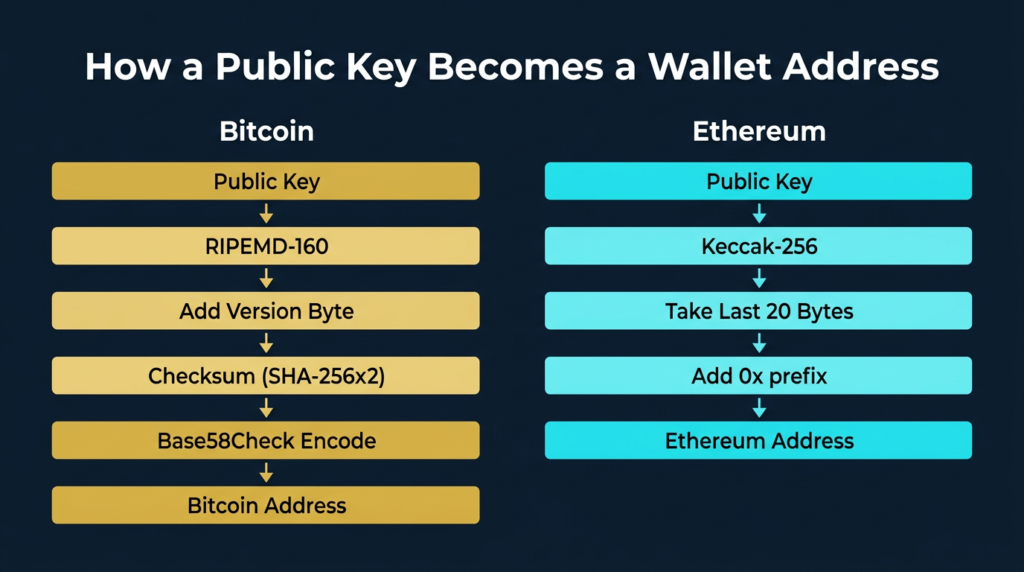
Step by Step: How Bitcoin Creates an Address
Bitcoin addresses are created through a sequence of cryptographic transformations designed to produce a compact, error-resistant identifier.
- Start with the compressed public key.
- Apply SHA-256 hashing.
- Apply RIPEMD-160 hashing to produce the public key hash.
- Add a version byte identifying the network.
- Create a checksum using double SHA-256.
- Encode the result using Base58Check.
The final result is the familiar Bitcoin address beginning with 1, 3, or bc1.
Bitcoin’s address system reflects the network’s underlying transaction design. A deeper explanation can be found in Bitcoin vs Ethereum transaction models.
How Ethereum Generates Addresses
Ethereum uses a simpler derivation process.
- Start with the uncompressed public key.
- Hash it using Keccak-256.
- Take the final 20 bytes of the hash.
- Add the 0x prefix.
This produces the familiar hexadecimal address format used across Ethereum and most EVM-compatible networks.
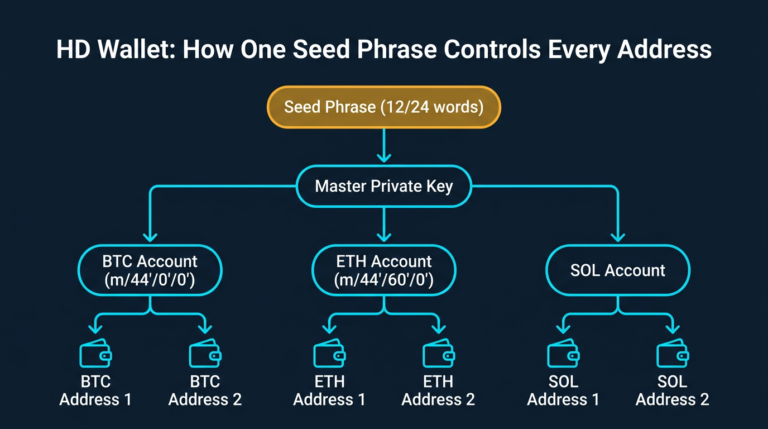
HD Wallets and Multiple Addresses from One Seed
Modern wallets use hierarchical deterministic architecture. From a single seed phrase, a wallet can derive a large tree of private keys and addresses.
This allows wallets to generate new receiving addresses automatically while remaining recoverable from one backup phrase.
Using new addresses improves privacy because it limits how much transaction history becomes associated with a single address. However, blockchain analysis can sometimes link addresses together through spending patterns, which is why good operational security remains essential for self-custody.
Risks and Common Mistakes
Sending funds on the wrong network. Some chains share similar address formats. Sending assets to the correct address on the wrong chain can make recovery difficult.
Clipboard hijacking malware. Certain malware replaces copied wallet addresses with attacker addresses during paste operations. Learn how this attack works in clipboard hijacking malware explained.
Assuming checksums prevent all mistakes. Checksums detect typing errors but cannot prevent malicious address substitution.
Address reuse harming privacy. Reusing a wallet address exposes its entire transaction history. Following a strong crypto wallet security checklist helps reduce avoidable risks.
Conclusion
Wallet addresses are not random identifiers. They are derived from public keys through carefully designed cryptographic transformations.
Bitcoin and Ethereum implement different address formats, but both rely on the same principle: protecting private keys while providing a safe way to receive transactions.
Understanding how public keys become wallet addresses helps users better understand wallet security, transaction verification, and the underlying cryptography that powers digital assets.
Continue Learning
- Understanding ownership: What Is a Private Key in Crypto?
- Protecting your funds: What Is Self-Custody in Crypto?
- How transactions are authorized: What Is Transaction Signing in Crypto