Last Updated on April 17, 2026 by Snout0x
Transaction signing is the mechanism by which you prove to the Bitcoin or Ethereum network that you have the right to spend specific funds, without revealing the private key that grants that right. It is one of the most fundamental operations in crypto. Every on-chain transaction you send must be signed before the network will process it. Understanding how signing works explains why hardware wallets exist, why private key security is non-negotiable, and why no one should ever need to share a private key to prove ownership.
A simple mental model helps here: signing is like stamping an instruction with a secret seal that only the real owner possesses. The network can check that the seal is valid, but it does not need to see the secret seal itself. That is why signing proves control without exposing the private key.
This content is for educational purposes only and should not be considered financial or investment advice.
Transaction signing is how your wallet proves a transaction is authorized without ever revealing the private key. Your private key produces a unique signature over the transaction data; the network checks that signature using only public information. The signature authorizes that exact transaction — not your account in general — which is why what you sign matters as much as the fact that you signed it.
The Problem Signing Solves
Blockchains are public ledgers. Anyone can see all transactions and all addresses. There is no gatekeeper checking passports or logging in with passwords. So how does the network know that the person sending a transaction is actually the one who controls the funds at the source address?
The answer is cryptographic signatures. The private key for an address can produce a signature over transaction data that anyone can verify using the corresponding public key, without needing the private key itself. The network validates this signature before accepting the transaction. If the signature is invalid, the transaction is rejected.
This means you never need to broadcast your private key to spend funds. You produce a signature with it, broadcast the signature and the transaction, and the network verifies both independently using publicly available data.
How Digital Signatures Work
Bitcoin uses the Elliptic Curve Digital Signature Algorithm (ECDSA) over the secp256k1 curve. Ethereum uses the same algorithm. The mathematics are beyond this article’s scope, but the important operational properties are these:
- A signature is produced by combining your private key with the transaction data (specifically, a hash of the transaction).
- The result is a unique signature specific to that private key and that specific transaction hash.
- Anyone who has your public key can verify that the signature is valid for the given transaction hash.
- The private key cannot be derived from the signature or the public key in any reasonable time frame.
- Signing a different transaction produces a completely different signature, even with the same private key.
This last property is important: a valid signature for one transaction cannot be reused for another. Each transaction must be signed independently, which prevents replay attacks where an old signature is resubmitted.
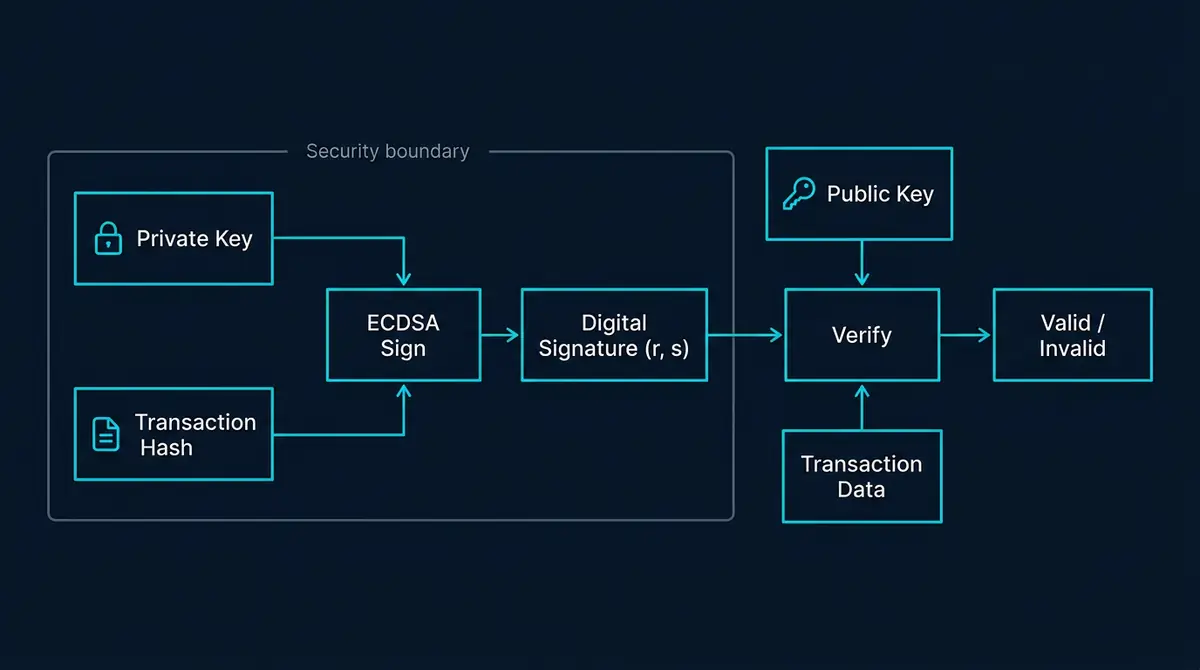
What a Transaction Signature Contains
A Bitcoin ECDSA signature contains two values, conventionally called r and s. These are large integers derived from the signing algorithm. Together with the transaction hash and the signer’s public key, the network can verify authenticity.
The public key itself is derived from the private key through elliptic curve multiplication. Your Bitcoin or Ethereum address is derived from the public key through one or more hash operations. This chain (private key to public key to address) means that knowing an address tells you nothing useful about the private key, but the private key controls the address completely.
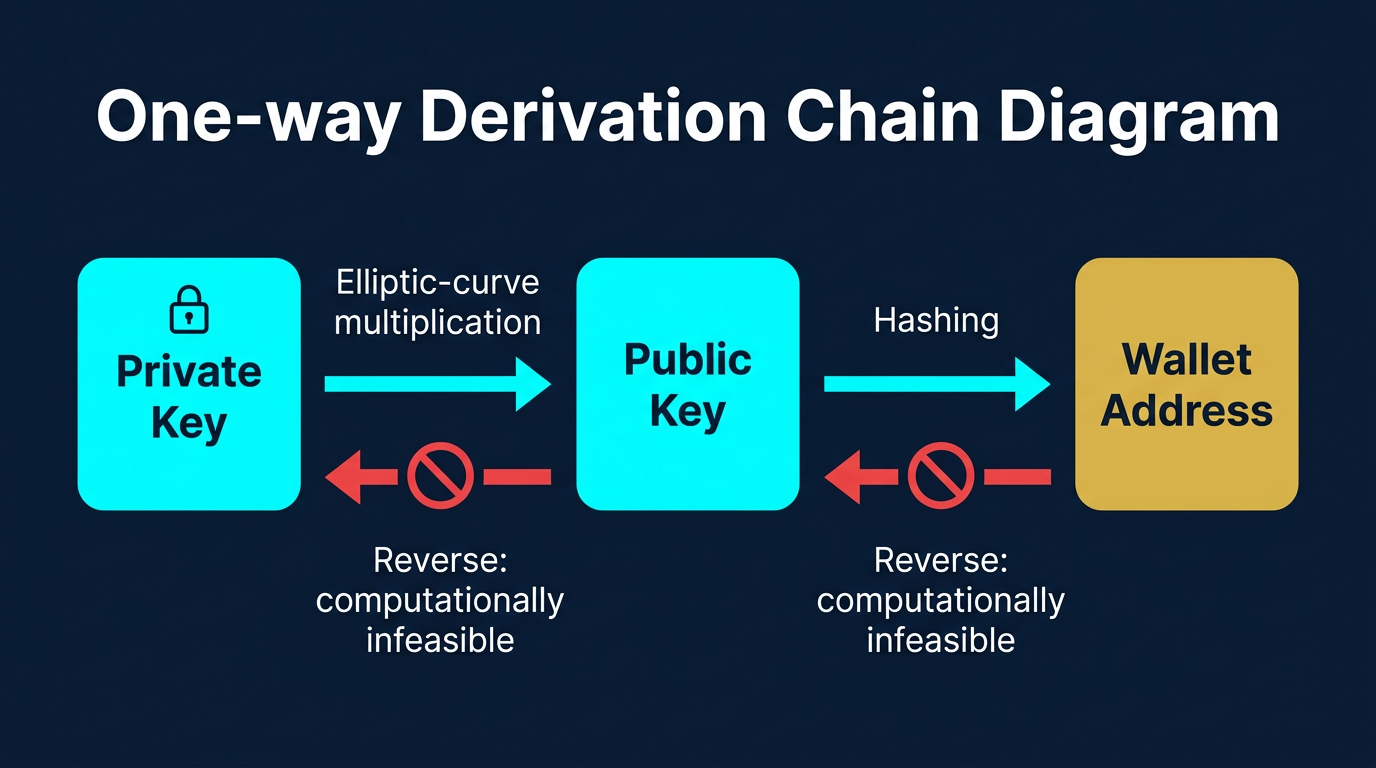
For a detailed look at how public keys relate to wallet addresses, see How Public Keys Become Wallet Addresses.
Why Hardware Wallets Exist for Signing
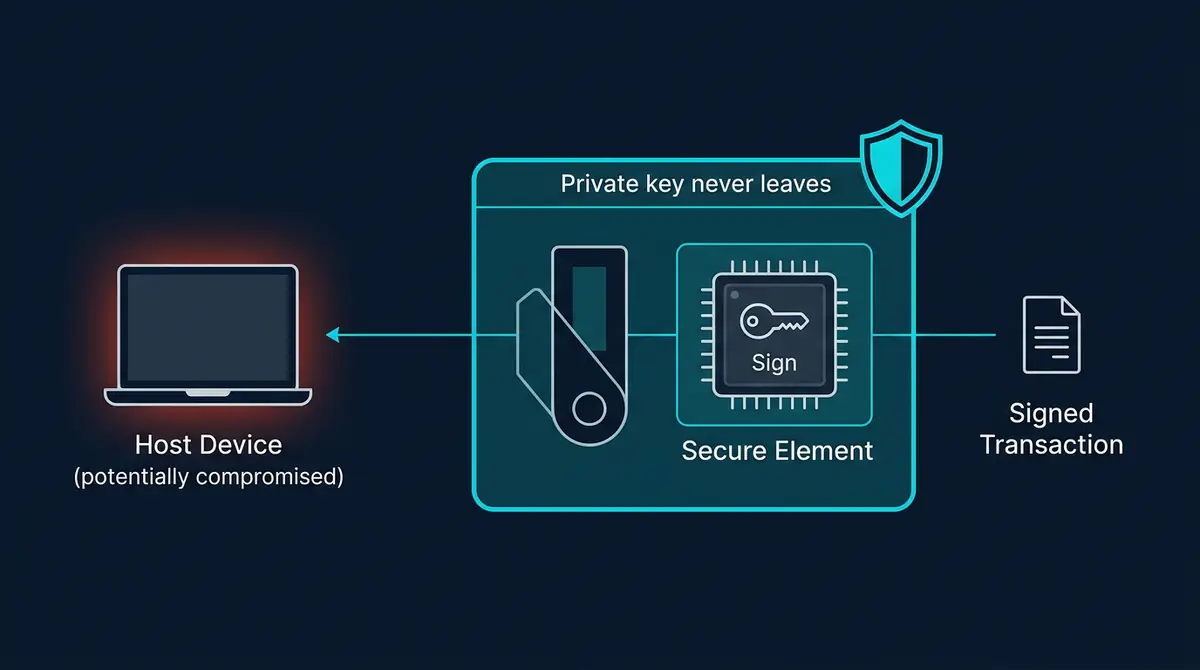
The private key must be present in memory at the moment of signing. On a regular computer or phone, the private key is somewhere in RAM during the signing operation, which means any malware running on that device could in principle read it. Once the malware has the private key, it has permanent, unconditional control over the associated funds.
Hardware wallets solve this by performing the signing operation inside an isolated secure element. The transaction data enters the device, the signing happens inside the chip, and only the signature exits. The private key never leaves the secure hardware environment. Even if the computer connected to the hardware wallet is fully compromised by malware, the malware cannot access the key because signing happens inside the device, not on the host computer.
This is the core security argument for hardware wallets. They are not primarily about encryption or password protection. They are about physically isolating the signing operation from any device that might be compromised. The private key never traverses a data path that malware can observe. If you want the device-level explanation behind that, What Is a Hardware Wallet? is the most relevant local follow-up.
Practical Usage: Check What You Are Signing
A hardware wallet can only protect you against malicious transactions if you can read what you are signing. “Blind signing” is the practice of confirming a transaction on a hardware wallet without a meaningful human-readable display of what the transaction actually does.
This is a real problem with complex DeFi transactions. Some wallets cannot decode the full contract interaction and simply show a binary hash or a warning message. When users confirm these without understanding the content, they may be signing malicious approval transactions that drain tokens, or other harmful operations that the device cannot display in readable form.
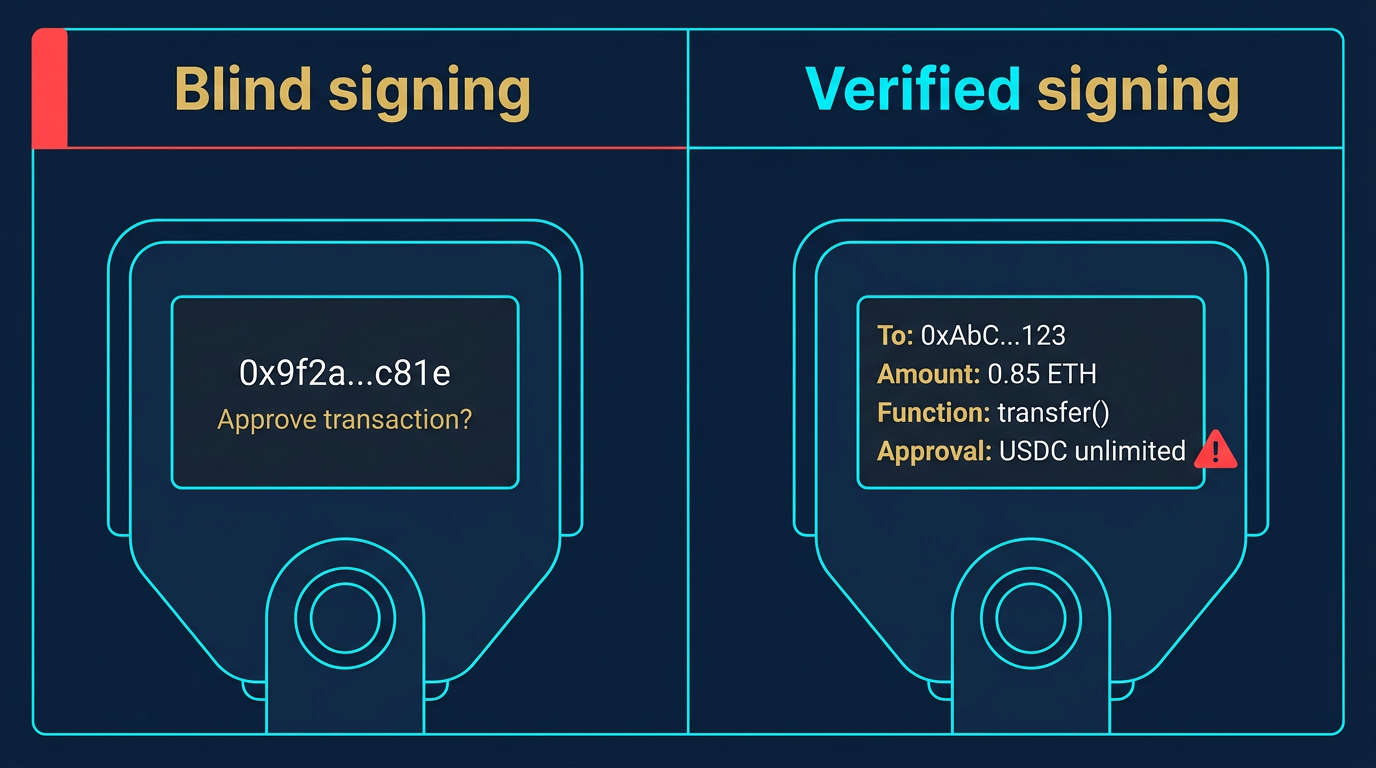
The best defense is to use hardware wallets with clear screens that can parse and display transactions in human-readable format. Always refuse to sign any transaction the device cannot fully display. If you want the practical trust-boundary explanation for that, see Hardware Wallet Screen Security.
Risks and Common Mistakes
The biggest mistake is treating signing like a generic confirmation step instead of the act that authorizes movement of funds. In practice, users get into trouble when they sign quickly inside a browser wallet, especially after being rushed by an airdrop, support message, or fake mint page. If the data being signed is malicious, the network treats that authorization as valid even if the user misunderstood it.
Blind signing is the other major risk. If the wallet shows only a hash, truncated address, or vague warning, you do not have enough information to judge the transaction safely. The consequence can be approving token spending, interacting with the wrong contract, or sending funds to an attacker-controlled address. The practical defense is to stop and use a device or interface that can display the full transaction details clearly.
Frequently Asked Questions
Can a signature be forged?
Not practically. Forging an ECDSA signature without the private key requires solving the elliptic curve discrete logarithm problem, which is computationally infeasible with current and foreseeable technology. This is the mathematical assumption on which all of Bitcoin and Ethereum’s security rests.
What is the difference between signing and encrypting?
Signing proves authorship and authenticity (this specific data was approved by the holder of this private key). Encryption hides content from unauthorized readers. Transaction signing in Bitcoin and Ethereum is not encryption. The transaction data itself is broadcast publicly. The signature just proves the sender authorized it.
What is a multisig transaction?
A multisignature (multisig) transaction requires signatures from multiple private keys before it is considered valid. For example, a 2-of-3 multisig requires any two of three specified private keys to sign. This is used by teams managing shared funds, by individuals wanting redundancy, and by custody services as a security layer.
Does signing reveal my private key?
No. The ECDSA algorithm is designed so that the private key cannot be recovered from the signature. You are mathematically producing a proof of knowledge without revealing the knowledge itself. This is a property called zero-knowledge in a practical sense, though technically ECDSA is not a formal zero-knowledge proof scheme.
What happens if someone steals my signature?
A signature is only valid for the specific transaction it was created for. Replaying a signature from a confirmed transaction does not allow the attacker to do anything new; the transaction is already confirmed and the inputs are spent. This is why signatures are tied to specific transaction hashes rather than being general-purpose authorizations.