Last Updated on March 16, 2026 by Snout0x
Rug pull warning signs are usually visible before the collapse happens, but most buyers never look in the right places. They see a fast chart, a loud community, a few influencer posts, and assume momentum means legitimacy.
That assumption gets people trapped. A crypto rug pull is rarely a random accident. It is usually a project structure designed so insiders can extract liquidity, dump supply, or restrict exits once enough retail money arrives.
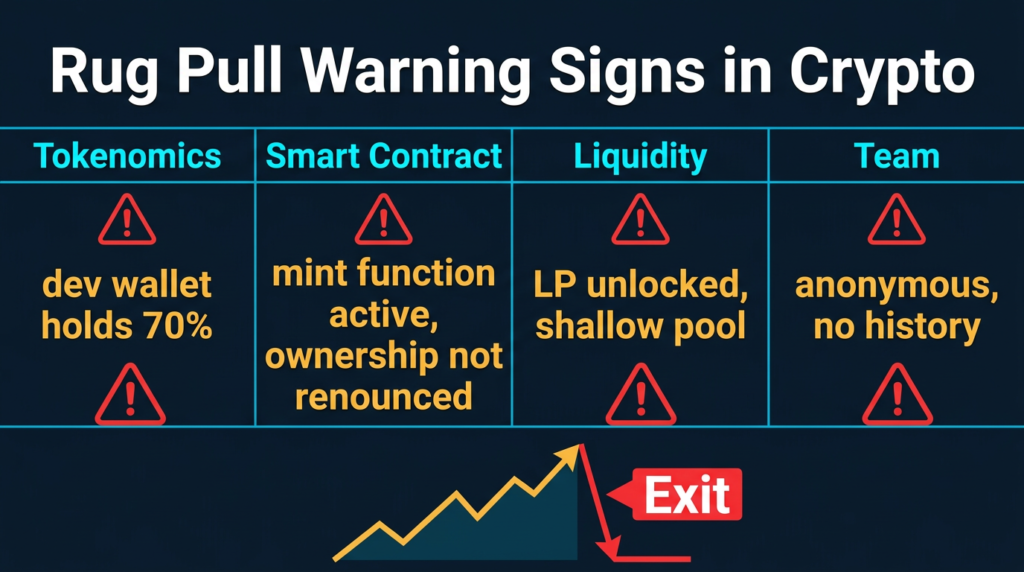
The warning signs tend to appear in the same areas: token distribution, smart contract permissions, liquidity control, and team behavior. This guide explains what to check before buying a new token, which red flags matter most, and how to separate ordinary speculation from a project that is structurally dangerous.
Disclaimer: This content is for educational and informational purposes only and does not constitute financial, investment, tax, or legal advice. Crypto assets are volatile and high risk. Always verify project details independently before committing capital.
Affiliate Disclosure: Some links in this article may be affiliate links. If you choose to use them, I may earn a commission at no additional cost to you.
Key Takeaways
- Most rug pulls leave structural evidence before the final collapse: concentrated supply, weak liquidity protection, dangerous admin permissions, and manipulative promotion often appear early.
- Smart contract risk matters as much as marketing risk: mint functions, blacklist powers, sell restrictions, tax changes, and upgradeable logic can give developers technical control over your outcome.
- Liquidity control is one of the biggest warning areas: if the team can remove liquidity or controls most of the pool, the token can become effectively untradeable in minutes.
- Retail investors can verify a lot without being developers: explorers, DEX analytics tools, and contract scanners reveal many common pre-rug signals.
- No single red flag proves fraud by itself: the highest-risk projects usually combine weak tokenomics, weak transparency, weak contract design, and pressure-driven marketing.
The Most Common Rug Pull Warning Signs
The most common crypto rug pull warning signs include extremely concentrated token supply, liquidity that is not meaningfully locked, smart contracts with mint or blacklist permissions, developer wallets holding large allocations, anonymous teams with no visible history, and aggressive marketing designed to rush buyers before they verify anything.
Most fraudulent tokens do not rely on one hidden trick. They rely on several red flags appearing at the same time. The more of these signals you find together, the more cautious you should be.
What a Rug Pull Looks Like in Practice
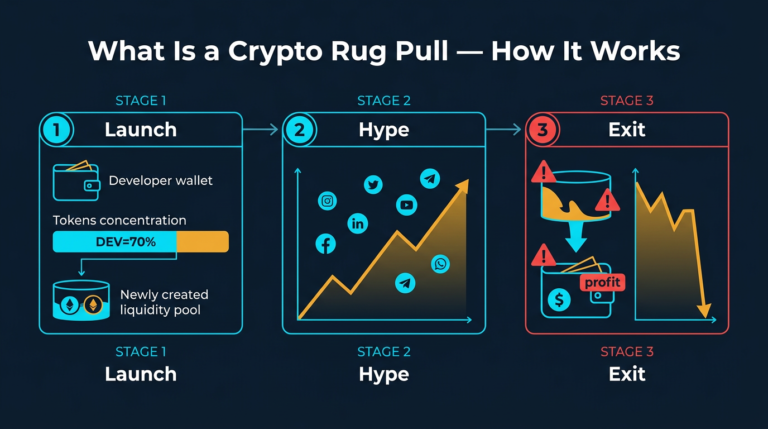
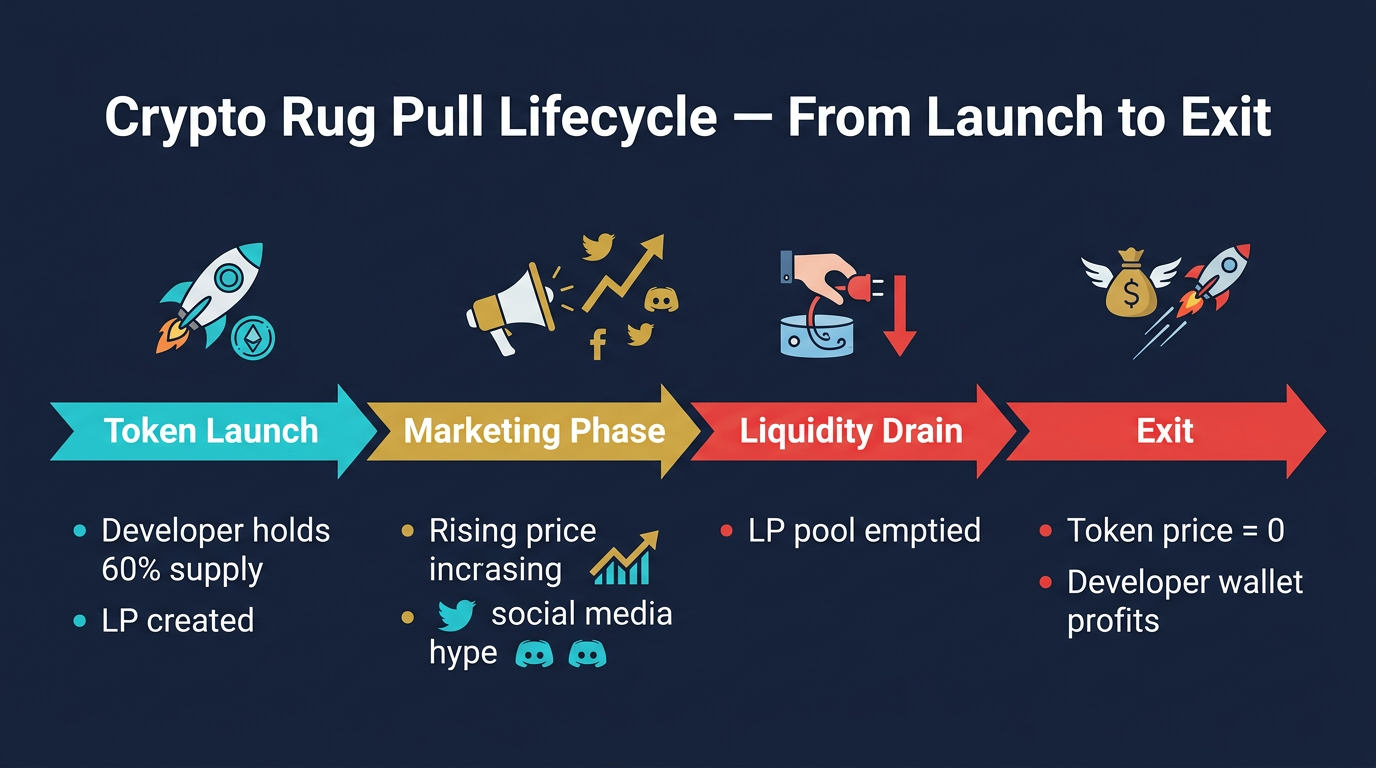
A rug pull usually follows a familiar sequence. First, a new token is deployed and paired with a legitimate asset such as ETH, SOL, BNB, or a stablecoin. Then the project is wrapped in branding, a roadmap, and a narrative strong enough to attract fast attention.
Blockchain analytics research has repeatedly shown that crypto scams and fraudulent token schemes have caused major investor losses across multiple market cycles. Rug pulls keep working because the structure is simple: build excitement, attract liquidity, and exit before most buyers understand what they actually bought.
Next comes distribution and promotion. Insiders hold large parts of the supply, liquidity is set up in a way the public rarely examines, and social channels create urgency around a launch, presale, listing, or rapid price move. By the time most buyers arrive, the critical control points were already built into the project.
The exit can happen in different ways. In a hard rug, liquidity is pulled quickly and the market collapses. In a soft rug, insiders sell large allocations over time into retail demand. In a contract-based rug, hidden permissions are used to mint supply, trap sellers, change taxes, or redirect value.
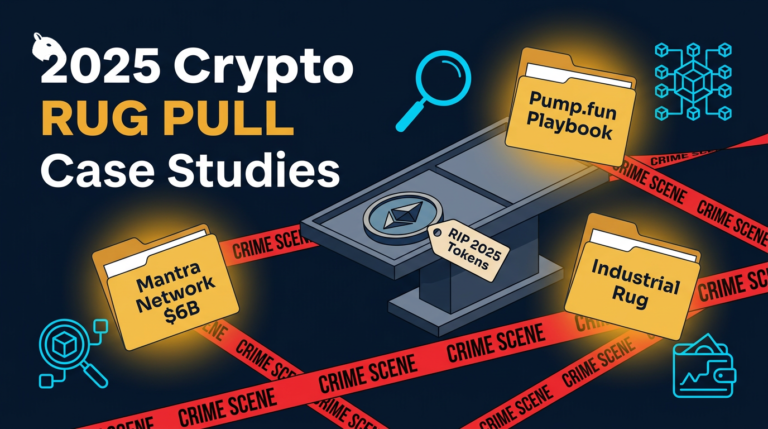
Different method, same result: retail capital goes in, insiders extract value, and late buyers are left holding a token with no real exit path. For real documented examples, see the breakdown of the biggest crypto rug pulls of 2025.
Quick Pre-Buy Checklist
If you only spend five minutes checking a new token, these are the first things worth verifying before anything else:
- Who holds the top wallet allocations?
- Is the liquidity locked, and how much of the pool is actually locked?
- Is the contract source code verified and readable?
- Can the owner mint, pause, block sells, change taxes, or upgrade the logic?
- Does the team have a verifiable history that predates this token launch?
- Is the entire pitch built on urgency, influencer promotion, and vague promises?
A project does not need to fail every one of these checks to be dangerous. The real problem is when several of them fail at the same time.
| Check | What to Look For | Why It Matters |
|---|---|---|
| Token supply | Top wallets hold modest percentages or are clearly identified | Reduces insider dump risk |
| Liquidity | Verifiable lock with meaningful pool coverage and duration | Reduces sudden liquidity removal risk |
| Contract permissions | No dangerous mint, blacklist, pause, or hidden sell controls | Reduces technical trap risk |
| Team history | Verifiable prior work, public record, or credible reputation | Reduces anonymous exit-scam risk |
| Marketing style | Clear information instead of pure hype and forced urgency | Reduces emotional decision-making pressure |
Rug Pull Warning Signs in Tokenomics and Supply
Tokenomics is often the fastest place to spot structural danger. If supply is heavily concentrated in a few wallets, those wallets can crash the market whenever they choose. That does not automatically prove the project is fraudulent, but it creates a fragile setup where insiders control outcomes that retail holders cannot defend against.
One of the first checks should be the top holders list on the relevant blockchain explorer. If a small number of wallets control a large share of the circulating supply, you need to understand who those wallets are. Are they vesting contracts, exchange wallets, treasury addresses with public controls, or simply insider wallets that can dump freely?
Team allocations also matter. Labels like marketing, ecosystem, treasury, or growth fund sound legitimate, but they mean little unless the tokens are verifiably locked with clear release conditions. If those allocations are fully liquid from day one, insiders can sell into any wave of retail demand.
Weak token utility is another risk factor, but it should be framed correctly. A token with no real product role is not automatically a rug. The real problem is that when a token has no meaningful use beyond speculation, its price depends heavily on continued marketing and fresh buyer flow. That makes manipulation easier and collapse faster when attention fades.
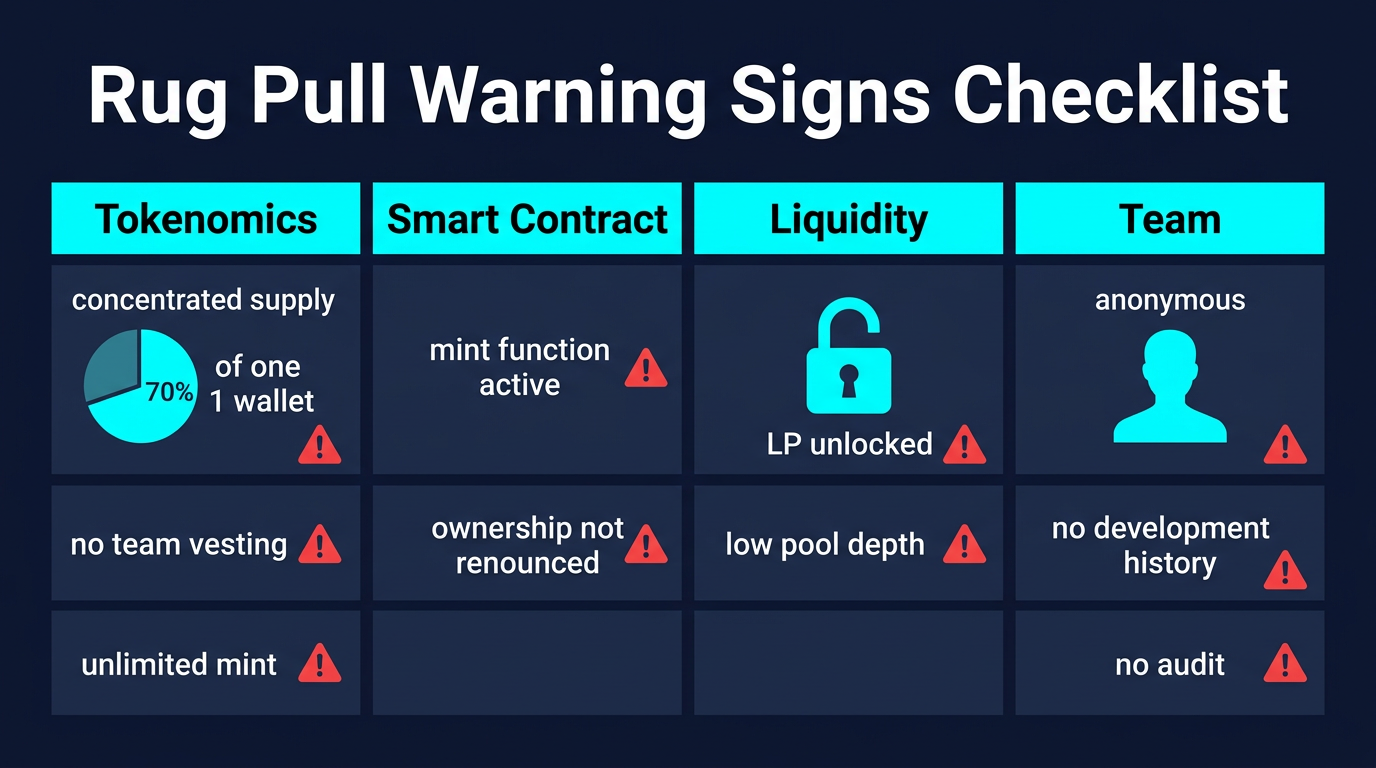
Smart Contract Red Flags
Many rug pulls are not just marketing scams. They are technical setups where the contract already gives developers the power to trap or exploit buyers. That is why contract permissions matter so much.
Mint functions are one of the first things to examine. If the owner can create new supply after launch, existing holders can be diluted instantly. Some legitimate protocols retain controlled minting for specific reasons, but in a newly launched speculative token, active mint authority should raise immediate questions about who controls it and under what limits.
Sell restrictions are another major danger. These are often disguised as anti-bot, anti-whale, or anti-dump protections. In practice, they can be written so insiders can sell while normal buyers get blocked or heavily penalized. A token that buys normally but sells only under hidden conditions can function like a trap.
Upgradeable or proxy contracts require extra caution. A project can look clean at launch and even point to an audit, but if a single admin key can swap contract logic later, the real risk continues after launch. This does not mean all upgradeable contracts are malicious. It means governance and control structure must be examined, not assumed.
Owner permissions are equally important. If the owner can change taxes, pause trading, blacklist addresses, redirect fees, or alter transfer rules, that control must be treated as a live risk. Ownership renouncement can reduce some attack surfaces, but it does not guarantee the contract is safe if dangerous logic was built in from the start.
For adjacent contract-based fraud patterns, see Phishing vs Smart Contract Drains.
Liquidity Locks and Exit Risk
Liquidity is one of the most important rug-pull checks because it is directly tied to whether investors can actually exit. A token can show a rising price chart and still be structurally unsafe if the team controls the pool.
If liquidity is not locked, the developer can withdraw it whenever they choose. That does not always mean they will, but it means they can. In thin markets, removing most of the liquidity can destroy the effective exit path almost instantly.
Even when a project advertises a liquidity lock, verify the details. The key questions are not just is it locked? but also how much is locked? and until when? A project that locks a small fraction of the pool while controlling the rest has not solved the real risk.
High transaction taxes also belong in this section of due diligence. A token that charges extreme buy and sell fees may be extracting value on every trade. Those fees are sometimes marketed as deflation, marketing support, or automatic liquidity generation. What matters is where the fees actually go and who controls them.
As a rule of thumb, any new token with unclear liquidity ownership, weak lock verification, and aggressive taxes deserves deeper skepticism before capital is committed.
Team Transparency and Social Manipulation
An anonymous team is not automatically fraudulent. Crypto has a long history of pseudonymous builders. The real issue is whether the team has a verifiable track record that existed before the current token launch.
A pseudonymous developer with years of public code contributions, documented protocol work, or recognized involvement in earlier projects represents a very different risk profile from a team that appeared days before launch with no visible history. A polished site and clean branding are not substitutes for a real record of work.
Community behavior also reveals a lot. If Telegram or Discord moderators instantly mute or ban users asking about contract ownership, audit links, vesting, or liquidity control, that is not community health. It is suppression of due diligence.
Artificial urgency is another recurring sign. Limited whitelist spots, countdown timers, last-chance claims, and exchange-listing promises are designed to shorten the time between attention and purchase. That pressure mechanism works because it hijacks the same emotional loop behind FOMO.
Broader manipulation tactics are covered in Social Engineering in Crypto, which fits naturally with the behavioral side of rug-pull risk.
Tools to Check Before Buying
You do not need to be a developer to run a basic rug-pull check. Several tools can surface the most common warning signs in a few minutes.
- Blockchain explorers such as Etherscan, BscScan, and Solscan help you inspect top holders, verify source code, and review contract permissions.
- DEX analytics tools such as DEXTools and DEXScreener help you review liquidity depth, pool behavior, trading anomalies, and holder concentration.
- Contract scanners such as Token Sniffer and RugDoc can flag common patterns like mint authority, honeypot behavior, and ownership risk.
- Lock verification tools can confirm whether liquidity is genuinely time-locked and how much of the pool is covered.
The correct order is simple: first check supply concentration, then liquidity control, then contract permissions, then team credibility. Most retail investors reverse this process and start with the marketing story. That is why they miss the structural risk.
Risks and Common Mistakes
Buying before checking holder concentration. This is one of the easiest checks and one of the most skipped. If insiders control too much of the supply, your downside is tied to their behavior, not just to market conditions.
Assuming a DEX listing means the project was reviewed. It was not. On decentralized exchanges, listing is mostly a function of deployment and liquidity creation, not quality control.
Treating influencer promotion as validation. Paid promotion is common, disclosure is inconsistent, and many promoters never do technical due diligence. Their incentives are not aligned with yours.
Confusing polished branding with technical legitimacy. A website, whitepaper, and active social channels can be produced quickly. Those are marketing assets, not proof of contract safety.
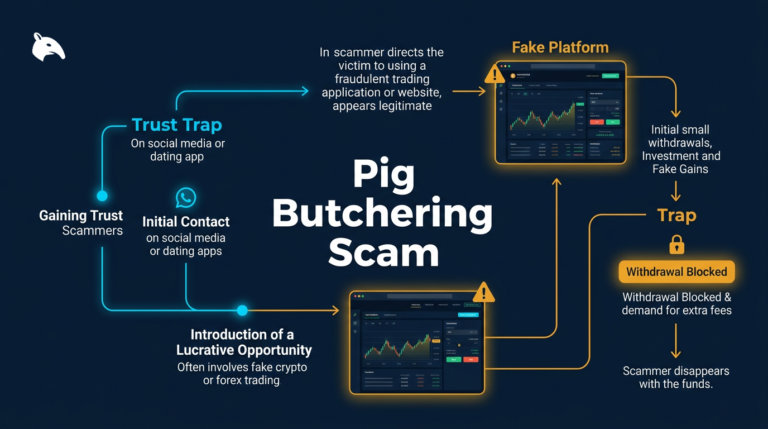
Ignoring adjacent scam patterns. Rug-pull risk often overlaps with wallet phishing, fake communities, and pressure-driven messaging. For a broader fraud comparison, see the pig butchering scam and 5 Safe Crypto Habits That Will Get You Rekt.
What a Beginner Should Actually Do
If you are new, the safest mindset is not trying to detect the perfect early winner. It is trying to avoid structurally bad setups. That means slowing down and treating every new token as guilty until basic verification proves otherwise.
Before buying, check the top holders, verify the contract source, review liquidity lock status, and look for admin powers that can change the rules after launch. If you cannot verify those basics, you do not have enough information to justify the risk.
Legitimate projects survive scrutiny. Fraudulent ones usually depend on you not looking too closely.
Sources
- Chainalysis – Research and reporting on crypto fraud, illicit activity, and ecosystem-level scam patterns.
- FBI Internet Crime Complaint Center (IC3) – Reporting portal and annual data on online investment fraud, including crypto-related losses.
- Etherscan – Blockchain explorer used to verify contract code, holder concentration, and wallet activity.
- CertiK – Public audit and smart contract security research platform.
Conclusion
The most important truth about rug pulls is that they usually do not come out of nowhere. The danger is often visible in supply concentration, liquidity control, contract permissions, and team behavior long before the final collapse.
No single red flag guarantees fraud. But when a token combines insider-heavy distribution, weak transparency, aggressive urgency, and live admin control, you are no longer looking at a normal speculative risk. You are looking at a project structure that can turn against buyers fast.
For retail investors, the goal is not perfect prediction. It is avoiding the obvious traps that were visible all along.
Frequently Asked Questions
What is the biggest rug pull warning sign?
There is no single perfect indicator, but one of the most dangerous combinations is high insider token concentration plus weak liquidity control. If the same small group can dump large allocations and also control most of the liquidity, retail holders are exposed to both price collapse and exit failure at the same time.
Can a token be a rug even if it was audited?
Yes. An audit is useful, but it is not a guarantee. Audits review code at a specific point in time, and they do not protect you from later upgrades, hidden governance concentration, liquidity abuse, or misleading social behavior.
Are anonymous teams always a red flag?
No. Anonymous teams exist across legitimate crypto projects. The important question is whether the team has a verifiable history of real work, public contributions, or prior protocol involvement that existed before the token launch.
How do I check if liquidity is locked?
You need a verifiable on-chain reference for the lock, not just a social media claim. Check the lock contract, the expiration date, and the percentage of the total pool that is covered. A partial lock does not protect the entire market.
What should I do if I think a project is a rug?
Document everything quickly: contract address, transaction hashes, project site, social channels, and any promotional material. Report the activity to relevant platforms and authorities where possible. Fund recovery is often unlikely, so the main goal is preserving evidence and reducing further exposure.