Last Updated on April 16, 2026 by Snout0x
Rug pull warning signs are often visible before an exit scam occurs, but most investors miss them because they focus on price momentum instead of project structure. A crypto rug pull is fraud where project developers drain investor funds and disappear, leaving the token worthless. These exits follow repeatable structural patterns that leave evidence in the tokenomics, smart contract code, liquidity setup, and team behavior before a single dollar is lost. This guide covers the specific signals to verify before committing capital to any new project.
This content is for educational purposes only and should not be considered financial or investment advice.
Every rug pull leaves structural evidence in the contract before the exit happens.
Key Takeaways
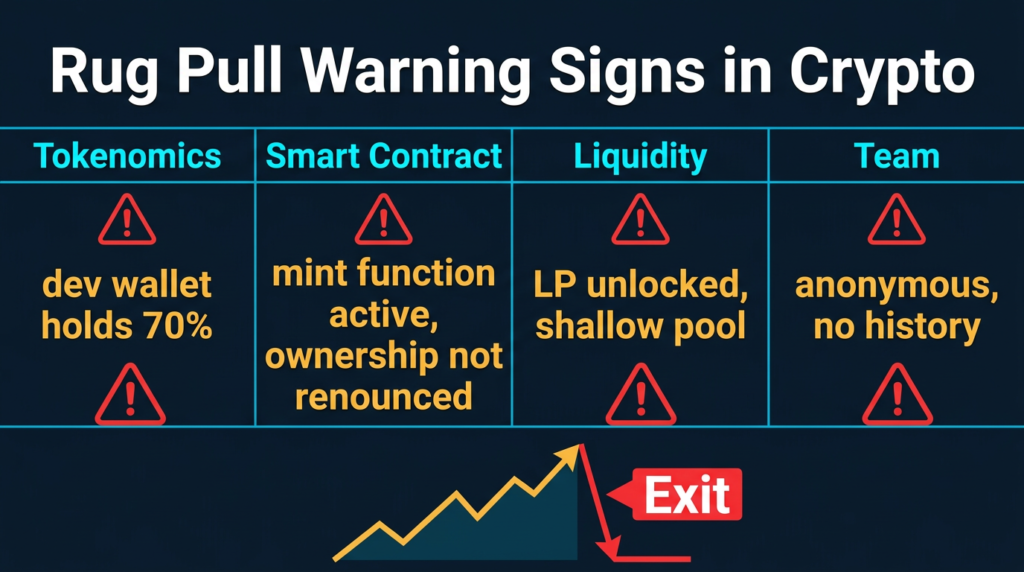
- Rug pull warning signs are frequently visible before collapse, including concentrated token ownership, unlocked liquidity, and teams with no verifiable identity or track record.
- Smart contracts with active mint functions, sell restrictions, or unrenounced ownership give developers technical control that can be used to execute an exit at any time.
- Liquidity that is not time-locked can be withdrawn instantly, making the token unsellable and crashing the price to zero without warning.
- On-chain tools including token scanners, DEX analytics, and blockchain explorers allow investors to verify contract safety and wallet concentration before buying.
- Social manipulation tactics such as artificial urgency, coordinated influencer promotion, and critical question suppression are consistent operational patterns in rug pull projects.
How Rug Pull Projects Are Engineered
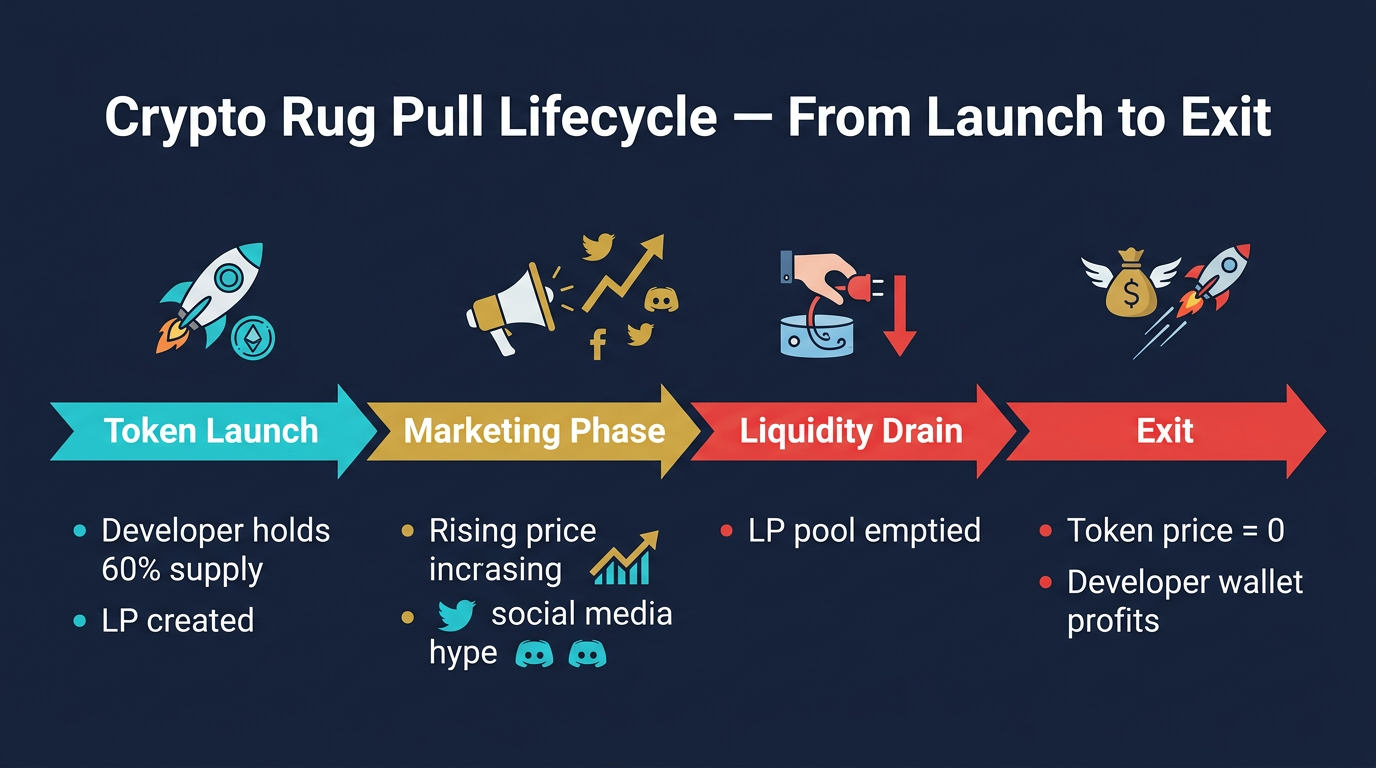
Rug pulls do not happen randomly. They follow a consistent operational model designed to extract maximum capital from retail investors before exiting. Understanding the sequence is the foundation for identifying rug pull warning signs at each stage.
The process begins with token deployment. A developer creates a smart contract on a low-fee blockchain such as Ethereum, BNB Chain, or Solana. The token is given a name, branding, and a roadmap with promises of future utility. A portion of the supply is allocated to the team under labels like “development fund,” “ecosystem reserve,” or “marketing wallet.” These allocations are usually not time-locked, meaning they can be sold at any point.
Liquidity seeding follows. The developer pairs the new token with a legitimate asset such as ETH or a stablecoin on a decentralized exchange. This creates a tradeable market and allows external investors to buy in. At this stage the developer often holds the majority of both the liquidity position and the token supply.
Marketing then generates price momentum. The project is promoted through X (formerly Twitter), Telegram, YouTube, and sometimes paid influencer campaigns. Promises of exchange listings, airdrops, and ecosystem development create urgency. Retail buyers enter as the token price rises and social media traction builds.
The exit itself takes different forms. In a hard rug, the developer withdraws the entire liquidity position at once, making the token unsellable. In a soft rug, insiders sell their large allocations gradually, allowing the price to collapse over days. In a contract-exploit rug, a backdoor function mints new tokens, blocks retail sells, or redirects funds to the developer’s wallet. Each variation produces the same result: investor capital transferred to developers, worthless tokens left in buyer wallets.
For a breakdown of how these patterns have played out in documented cases, see the analysis of the biggest crypto rug pulls of 2025.
Rug Pull Warning Signs in Tokenomics and Supply Distribution
Tokenomics is the first place to look when evaluating a new project. The way a token’s supply is distributed often reveals whether the project was designed to enrich insiders at investor expense.
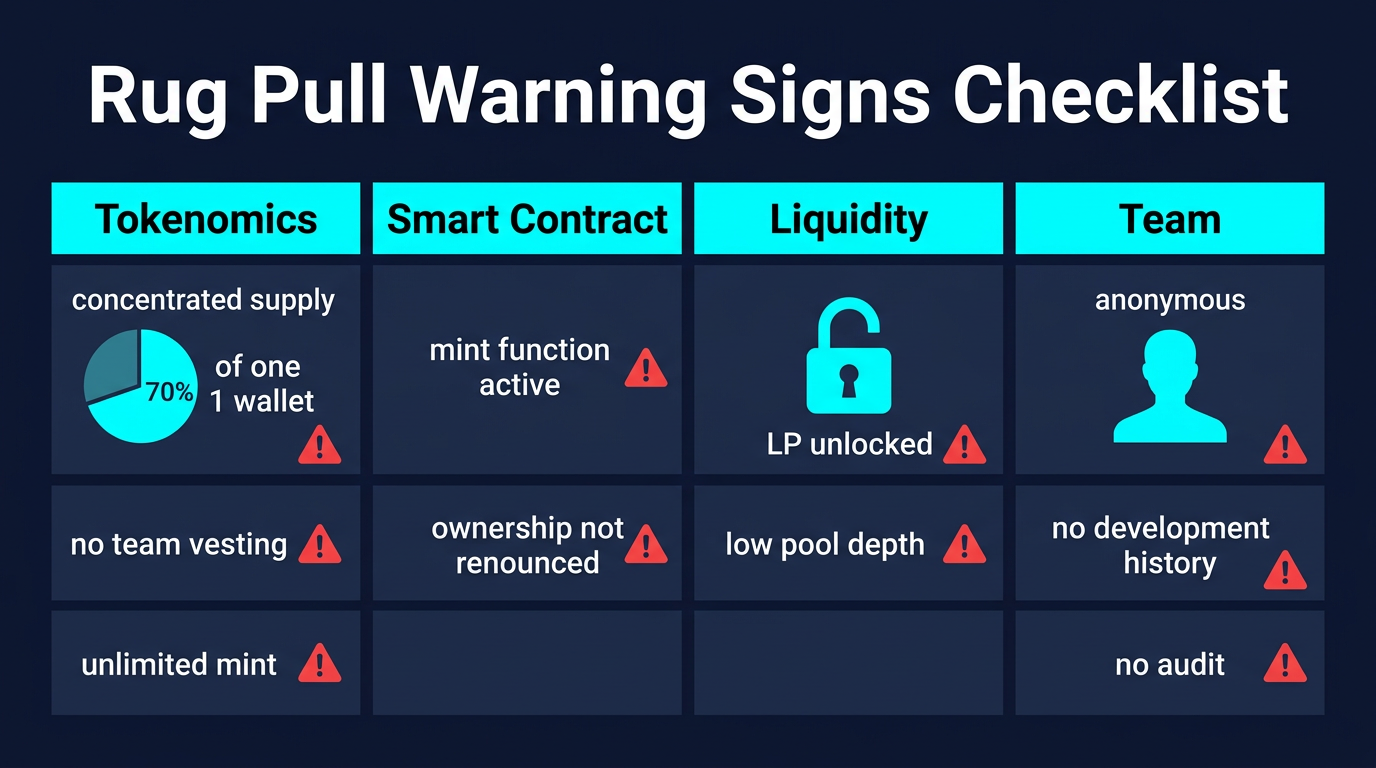
Supply concentration is one of the clearest rug pull warning signs. If a small number of wallets control a large percentage of the total token supply, those holders can coordinate a sell and collapse the price simultaneously. Checking the top wallet holders on a blockchain explorer takes under two minutes. If the top ten wallets collectively hold more than 20 to 30 percent of circulating supply, that concentration warrants careful analysis before entering.
Vesting schedules are equally important. Legitimate projects impose time-based vesting on team and investor allocations, meaning those tokens cannot be transferred or sold for a defined period after launch. When no vesting exists, the development team holds fully liquid tokens from day one and can sell into any price increase without restriction.
Pre-minted allocations labeled vaguely as “marketing,” “treasury,” or “growth fund” without transparent on-chain lock mechanisms are common in projects designed to rug. These pools accumulate through investor buys and are liquidated once retail liquidity reaches a target depth. There is no on-chain guarantee these funds will be used for the stated purpose unless they are locked in a verifiable smart contract with defined release conditions.
Token utility matters structurally, not just as a marketing claim. When a token has no technical function within a protocol and exists solely as a speculative instrument, there is no mechanism to support its value. The only thing holding the price is continued buyer demand. Once the developer stops manufacturing that demand, collapse follows.
Smart Contract Code Flags That Precede a Rug
The smart contract is where many rug pulls are technically pre-constructed. Certain code patterns give developers the ability to execute an exit regardless of what the public-facing roadmap promises.
Active mint functions that have not been burned or renounced allow the contract owner to create additional tokens after launch. If new supply can be issued on demand, the developer can dilute all existing holders instantly or create artificial sell pressure to crash the price. A legitimate project either removes this function entirely post-launch or ensures it is controlled by a transparent governance mechanism.
Transfer restriction functions are a common sell-block mechanism. A function written into the contract can prevent specific wallet addresses from executing sell transactions. This is sometimes presented as an “anti-bot” or “anti-dump” feature, but functionally it can block all retail sellers while insiders exit freely. The result is that investors hold tokens they cannot sell while the price drops to zero.
Proxy or upgradeable contracts introduce ongoing risk even after deployment. Upgradeable contract patterns allow the developer to replace the contract’s logic at any time. A project can appear safe at launch, pass an audit, and then have the underlying logic swapped post-audit to include malicious functions. Unless the upgrade mechanism itself is controlled by a multi-signature wallet or governance contract, one private key controls the entire contract behavior.
Contract ownership that has not been renounced is an active risk vector. Admin functions can change tax rates, modify transfer logic, pause trading, or trigger emergency withdrawal functions. Renouncing ownership transfers control to a null address, eliminating this attack surface permanently. When a developer claims their project is decentralized but retains contract ownership, that claim is not technically accurate.
The absence of a third-party audit does not automatically indicate fraud, but it removes one verification layer. Reputable firms such as CertiK, PeckShield, and Hacken publish their reports publicly. When a project claims to be audited but no verifiable report exists, that claim cannot be confirmed. An audit covers the contract code at the time of review only. Post-audit upgrades, new deployments, or liquidity manipulation fall outside its scope.
Team Anonymity and Community Management Tactics
Anonymity is standard in crypto and does not by itself indicate fraud. Pseudonymous developers have built legitimate protocols with billions in total value locked. What matters is whether an anonymous team has a verifiable track record that predates the current project.
Pseudonymous developers with years of public commit history on GitHub, documented contributions to established protocols, and a developer community reputation represent a different risk profile from a team that appeared two weeks before token launch with no prior activity. A polished website and professionally designed whitepaper do not substitute for verifiable development history.
Technical transparency is a meaningful signal. Legitimate builders typically maintain public development logs, testnet deployments, changelogs, and open-source repositories. When a team’s public communications consist entirely of price discussion, marketing announcements, and influencer collaborations but lack any evidence of working code or documented technical progress, that absence is informative.
Artificial urgency is a social manipulation tactic used consistently in rug pull operations. Phrases like “presale closes in 24 hours,” “whitelist spots are limited,” and “last chance before CEX listing” are designed to disable rational analysis by creating time pressure. This is the same psychological mechanism that drives FOMO-driven investment decisions in broader crypto markets, applied deliberately to prevent due diligence.
Community channel behavior is also informative. Telegram and Discord channels that immediately ban or mute users who ask about the contract code, the audit status, or the team’s identity are signaling that critical inquiry is unwanted. Banning questions about technical structure is not an anti-FUD measure. It is suppression of the verification process that would reveal risk.
Liquidity Lock Status and Trading Pattern Analysis
Liquidity status is one of the most directly verifiable rug pull warning signs and one of the most frequently overlooked by retail investors.
When a developer creates a trading pair on a decentralized exchange, the liquidity pool position can either be locked in a time-locked smart contract or held directly in the developer’s wallet. Unlocked liquidity means the developer can remove it at any moment. The price impact of a full liquidity withdrawal on a token with low market depth is immediate and catastrophic, typically reducing the token price by 90 percent or more within seconds.
Liquidity lock services such as Team.Finance and Unicrypt allow developers to deposit liquidity pool tokens into a third-party contract with a defined release date. When a project advertises a lock, both the contract and its expiry date should be verifiable on-chain. The amount locked relative to total pool size matters equally. A lock covering 20 percent of total liquidity while 80 percent remains in developer wallets provides minimal protection. The relevant figure is the percentage of pool depth locked, not the absolute dollar amount.
Trading patterns before a rug often show specific anomalies. A chart displaying rapid, consistent price increases with very few sell transactions indicates possible wash trading, where the same wallets repeatedly buy and sell to manufacture price momentum and create the appearance of organic demand. This attracts external buyers who provide the exit liquidity the developer needs.
Transaction tax rates embedded in the contract are another data point. Some contracts charge 20 to 30 percent on buys and sells, framed as a deflation mechanism or automatic liquidity generation. High transaction taxes extract value from investors on every trade and, depending on how the contract is written, can be redirected to developer wallets rather than to the stated purpose. Taxes above 10 percent on both sides should be examined carefully for where the collected funds actually go.
On-Chain Verification Tools Investors Can Use
Several publicly available tools allow investors to examine a project’s contract and liquidity data before buying. Using these tools does not require programming knowledge and takes a few minutes per project.
Token Sniffer and RugDoc scan smart contracts for known malicious functions and assign a risk score. These scanners check for common patterns including active mint functions, honeypot sell restrictions, and ownership status. They are not exhaustive and can be evaded by sophisticated developers, but they flag the most common attack patterns and eliminate obvious high-risk contracts quickly.
DEXTools and DEXScreener provide real-time trading data including wallet concentration metrics, transaction histories, liquidity pool size, and market cap to liquidity ratios. A project with $500,000 in displayed market cap but only $8,000 in total liquidity has almost no exit depth for investors. If a large holder sells or liquidity is pulled, there is insufficient depth to absorb any selling pressure at current prices.
Etherscan, BscScan, and Solscan allow direct contract inspection depending on the blockchain. If the contract’s source code is verified and published, it can be read directly in the browser without any technical tools. Unverified contracts, where only the bytecode is visible, make independent verification impossible and represent a structural yellow flag.
For broader context on fraud patterns, Chainalysis research consistently identifies DeFi protocols as the primary source of crypto fraud by total value stolen. Their annual crypto crime reports provide aggregated data on rug pull frequency, average loss sizes, and the blockchain ecosystems where fraudulent projects concentrate. The FBI Internet Crime Complaint Center (IC3) also tracks investment fraud losses including crypto scams and publishes annual figures that document the scale of these schemes.
Common Mistakes That Increase Rug Pull Exposure
Understanding rug pull warning signs is only useful if the verification process is applied before capital is committed. Several behavioral patterns consistently increase the probability of exposure.
Buying based on social media signals without independent verification is the most common mistake. A promoted token on X or a viral Telegram alert can represent genuine community interest or a coordinated marketing push designed to attract exit liquidity. Without checking the contract and on-chain data independently, there is no technical basis for distinguishing between them.
Skipping the wallet distribution check is a frequently missed step. Viewing the top holders of a token on a blockchain explorer takes under two minutes and reveals the concentration data that is one of the most reliable structural indicators of rug pull risk. Many documented rug pulls had publicly visible wallet concentration that any investor could have identified before entry.
Assuming a listed token has been vetted is a misunderstanding of how decentralized exchanges work. DEX listings are automatic and permissionless. Unlike centralized exchanges, which apply some form of project review, DEX listings require only that a liquidity pool be created. No review, no approval, no accountability check is involved. A token’s presence on Uniswap or PancakeSwap says nothing about whether the project is legitimate.
Treating influencer promotion as due diligence creates false confidence. Paid promotion in crypto is common and often undisclosed. Influencers have promoted projects they knew were fraudulent or failed to evaluate technically. Their incentive is the promotion fee, not the outcome for their audience. Cross-reference promotion with on-chain verification rather than substituting one for the other.
Social polish is not a proxy for contract integrity. A professional website, organized Telegram server, and polished whitepaper can be produced in days with minimal cost. Technical legitimacy requires a verifiable contract, documented development history, locked liquidity, and a distribution structure that does not concentrate sell pressure in developer wallets. For more on the habits that increase investor exposure to fraud, see 5 Safe Crypto Habits That Will Get You Rekt. For the practical framework, see how to store crypto safely before committing capital to speculative tokens.
A wallet security checklist helps verify your own operational security before interacting with any new project.
Related fraud patterns often accompany rug pull operations. Social engineering, fabricated relationships, and investment pressure through messaging apps are documented tactics described in detail in the breakdown of the pig butchering scam, a separate but structurally adjacent fraud type that uses similar psychological manipulation at a larger scale.
Sources
- Chainalysis Crypto Crime Report. Annual data on DeFi fraud, rug pull volumes, and blockchain crime patterns.
- FBI Internet Crime Complaint Center (IC3). Annual statistics on investment fraud losses including cryptocurrency scams.
Frequently Asked Questions
What is the most reliable rug pull warning sign?
Unlocked liquidity combined with high token concentration in developer wallets is the most structurally reliable pre-rug indicator. Both are verifiable on-chain before any capital is committed. When the developer controls both the liquidity position and a large token allocation, they have the technical ability to execute an exit at any time with no barrier.
Can a project pass an audit and still rug?
Yes. Audits review contract code at the time of the audit. Post-audit contract upgrades, new proxy deployments, or liquidity manipulation fall outside the scope of any prior review. An audit is a point-in-time snapshot, not an ongoing guarantee. Upgradeable contracts can have their logic replaced after an audit is completed, so checking whether a contract is upgradeable remains relevant even for audited projects.
How do I check if a project’s liquidity is locked?
Use the liquidity lock contract directly. Projects that have locked liquidity through services like Team.Finance or Unicrypt will have a verifiable lock contract address. You can look up this address on the relevant blockchain explorer to confirm the amount locked, the expiry date, and whether the lock covers the majority of the pool. A lock claim without a verifiable on-chain reference cannot be independently confirmed.
Are anonymous teams always a rug pull risk?
Not inherently. Many legitimate protocols are built by pseudonymous teams. The relevant distinction is whether the anonymous team has a verifiable development history that predates the current project. A pseudonymous developer with years of public GitHub commits and protocol contributions represents a different risk profile from an account that appeared weeks before token launch. Anonymity without track record, combined with other warning signs, increases risk meaningfully.
What should I do if I think I have been rugged?
Document everything immediately: transaction hashes, project website, social media accounts, and any communications you received. Report to the FBI Internet Crime Complaint Center at ic3.gov and to your country’s financial regulator if the project operated as an investment. Recovery of funds from a rug pull is rare because on-chain transactions are final and the developers are typically anonymous. The primary value of reporting is contributing to documented fraud pattern data used in law enforcement investigations.