Last Updated on April 12, 2026 by Snout0x
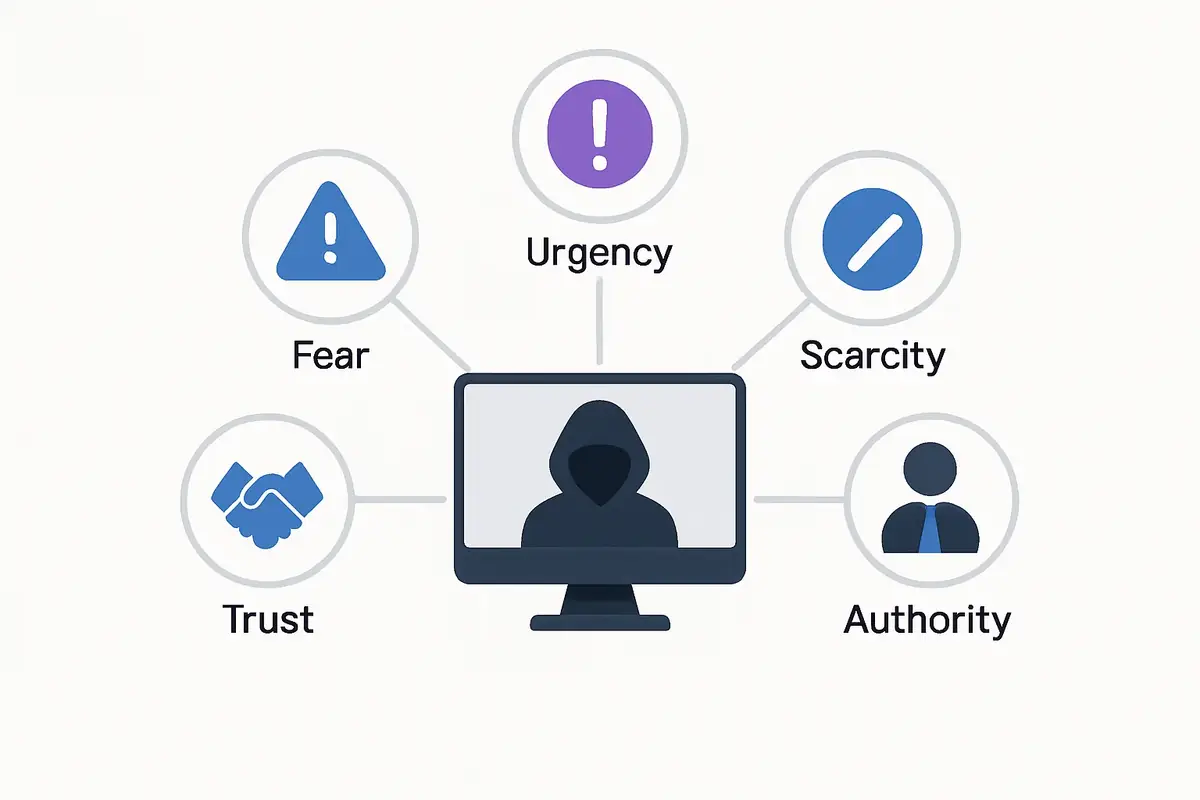
Most crypto security discussions focus on technical vulnerabilities: smart contract bugs, phishing sites, malware. But social engineering in crypto often begins not with a technical exploit, but with a conversation. These attacks bypass all technical defenses by targeting the human operator instead. They exploit psychological patterns that are universal: trust in authority, fear of missing out, urgency, and desire to help others. Understanding how these tactics work, why they are effective, and what specific forms they take in the crypto context is essential for anyone managing meaningful crypto assets.
The practical takeaway is that social engineering is usually a behavior attack, not a code attack. The safest response is to slow the interaction down, move verification off the original channel, and refuse any request that asks for secrecy, urgency, remote access, or wallet recovery information.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- Social engineering attacks exploit psychological vulnerabilities rather than technical ones.
- Common vectors include fake support agents, impersonated influencers, romance scams, SIM swapping, and insider threats.
- Urgency and authority are the two most consistently used psychological levers in crypto social engineering.
- Technical security measures such as hardware wallets and 2FA do not protect against attacks that convince you to perform actions yourself.
- Mandatory slowing down and independent verification are the most effective defenses.
How Social Engineering in Crypto Works Psychologically
Social engineering works by exploiting cognitive shortcuts that humans rely on to make decisions quickly. These shortcuts are useful in everyday life but create vulnerabilities when a sophisticated actor deliberately manipulates them.
The key psychological mechanisms in play are:
- Authority. People comply with requests from apparent authority figures. Fake support agents impersonating MetaMask, Coinbase, or Ledger exploit this. A message claiming to come from “MetaMask Security Team” triggers a compliance response that a message from an unknown stranger does not.
- Urgency. Manufactured time pressure disables careful thinking. “Your account will be locked in 10 minutes unless you verify your recovery phrase” creates panic that leads people to act before they verify the source.
- Social proof. Fake testimonials, fabricated screenshots of profits, and bot-generated endorsements create an illusion that others are benefiting from a scam.
- Reciprocity. A small initial gesture (fake free tokens, helpful advice) creates a social obligation to reciprocate that attackers then leverage for a larger ask.
- Liking and trust. Romance scams and long-term relationship-building exploit genuine emotional attachment over weeks or months before making the financial ask.
The effectiveness of social engineering does not depend on the target being unsophisticated. Security professionals, developers, and experienced traders have all been successfully social engineered. The tactics adapt to the target’s apparent level of technical knowledge.
Common Social Engineering Attacks in Crypto
These attack types differ in format, but they tend to follow the same sequence: establish false trust, create a reason to act quickly, then move the victim into a private channel or off-platform workflow where verification gets weaker. That is why articles like Clipboard Hijacking Malware and Crypto Wallet Phishing Attacks overlap so heavily with social engineering even when the final theft mechanism is different.
For a closely related follow-up, see Hardware Wallet Supply Chain Attack: What to Check.
For a closely related follow-up, see Crypto Approval Scams Explained: How Token Approvals Drain Wallets.
For a closely related follow-up, see Phishing vs Smart Contract Drains: Two Different Ways Attackers Steal Crypto.
Fake Support Agents
This is the most common social engineering attack on crypto users. You post in a Discord server, Telegram group, or Reddit thread about a wallet issue. Within minutes, someone with a username like “MetaMask_Official_Support” or “Binance_Support_Team” contacts you via DM, offering to help. They ask for your seed phrase or direct you to a “wallet verification site” that captures it.
The critical fact: no legitimate crypto company will contact you via DM to ask for your seed phrase. No support team needs it. The seed phrase is for your use only, and requesting it is always a scam.
Influencer Impersonation and Giveaway Scams
Attackers create social media accounts with usernames nearly identical to well-known figures (Elon Musk, Vitalik Buterin, prominent crypto YouTubers) and post “send 1 ETH, receive 2 ETH back” promotions. The fake accounts may have hundreds of thousands of followers (purchased) and manufactured engagement. Victims send crypto expecting to receive double back and receive nothing.
A variation targets users who comment on legitimate posts: bots create fake replies from the influencer’s “official giveaway account” that appear in the thread. The double-your-money promise has never been legitimate in any cryptocurrency context, ever.
Romance Scams (Pig Butchering)
Pig butchering scams are extended social engineering operations that can run for weeks or months. The attacker builds a genuine-seeming relationship with the victim through a dating app, WhatsApp, or LinkedIn. After trust is established, they introduce a “crypto investment opportunity” that has been returning excellent profits. They help the victim make initial investments and show convincing (fake) returns. When the victim tries to withdraw funds, they are told a “tax fee” is required. Multiple rounds of additional payments follow before the victim realizes the platform is completely fraudulent.
Pig butchering scams account for billions in annual crypto theft globally. They are sophisticated, emotionally devastating, and nearly impossible to recover from once executed. The FBI estimates that these operations, often run by organized crime networks using trafficked labor, are among the highest-volume crypto fraud categories.
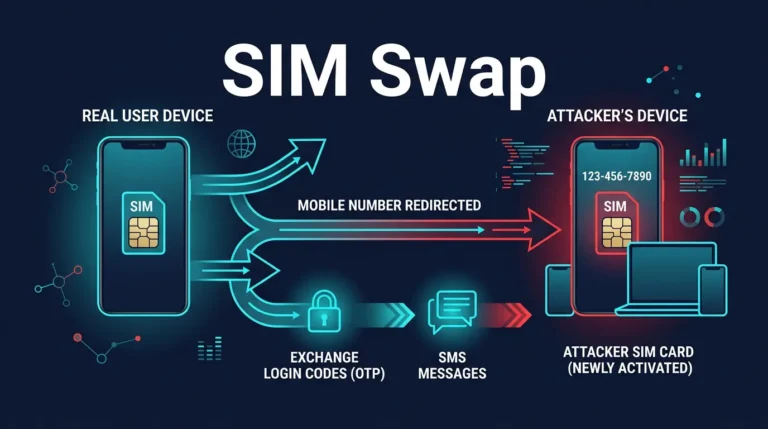
SIM Swapping
SIM swapping is a social engineering attack on mobile carriers. The attacker calls your carrier’s customer support and, using information gathered from social media or previous data breaches, convinces a representative to transfer your phone number to a SIM card they control. Once they have your phone number, they can receive SMS verification codes and reset passwords for your accounts.
This attack is specifically dangerous for crypto users who rely on SMS-based two-factor authentication for exchanges. Using an authenticator app (Google Authenticator, Authy) instead of SMS 2FA is the direct defense. Using a hardware security key (YubiKey) for exchange accounts is stronger still.
Insider Threats and Developer Targeting
DeFi protocol developers and employees have been targeted by sophisticated social engineering operations. Attackers pose as job recruiters from other protocols, investors, or auditors, establishing contact through LinkedIn or professional email. They send test files, repositories, or interview materials that contain malware designed to steal browser session cookies, wallet extension data, or private keys from the developer’s machine.
Multiple major DeFi hacks, including the Ronin Network $625 million breach, involved social engineering of individual employees who were convinced to run malicious code. The attack on Radiant Capital in 2024 similarly began with a PDF sent to a developer that contained malware.
Why Technical Defenses Are Not Enough
This is the uncomfortable truth about social engineering: technical defenses do not protect against attacks that convince you to perform the harmful action yourself. A hardware wallet does not prevent you from sending funds to a scammer’s address willingly. A password manager does not prevent you from giving an attacker your seed phrase under false pretenses. Two-factor authentication does not prevent SIM swapping if your carrier is successfully social engineered.
Technical defenses raise the cost of purely technical attacks. Social engineering is explicitly designed to route around them by targeting the human decision-maker. This is why security awareness and behavioral discipline are as important as technical controls.
Practical Usage: Defending Against Social Engineering
- Slow down when urgency is introduced. Manufactured urgency is the most reliable signal that you are being manipulated. Legitimate systems rarely have 10-minute deadlines for account recovery or fund verification. When urgency appears, deliberately add time to your response.
- Verify independently. If someone claiming to be from Coinbase, MetaMask, or a project contacts you, do not use the contact information they provide. Go directly to the company’s official website and contact support from there.
- Treat all unsolicited contact as suspect. Legitimate protocols and exchanges do not cold-message users about account issues. If you did not initiate the contact, treat it as a potential attack by default.
- Never share your seed phrase. No legitimate purpose ever requires sharing a seed phrase with another person. No amount of authority, urgency, or apparent legitimacy changes this. It is the single rule with no exceptions.
- Use authenticator apps instead of SMS 2FA. This eliminates SIM swapping as an attack vector for your exchange accounts.
- Do not open files from strangers. PDF files, compressed archives, and executables from unsolicited contacts are high-risk delivery mechanisms for credential-stealing malware.
An operator rule that works well is to never solve a wallet or exchange problem inside the same channel where it appeared. If the issue starts in Telegram, Discord, X replies, email, or LinkedIn, stop there and move to the official support route yourself. Another useful habit is to treat any request that changes the communication pattern, for example “switch to DM,” “download this file,” or “use this special recovery portal,” as a strong escalation signal rather than a convenience.
A concrete example: you post in a wallet Discord saying a transfer looks delayed, an “admin” DMs immediately, and the conversation shifts to a private site that asks you to reconnect or verify recovery details. That entire sequence is the attack. The speed of the response and the move to a private workflow are not proof of help. They are often the strongest proof of manipulation.
A second example is recruiter targeting. If an unsolicited contact sends a “test assignment” file, PDF, or repository before you have even had a real interview, assume the file is hostile until verified through a separate company contact path. That simple rule blocks a surprising amount of high-end social engineering aimed at developers and protocol teams.
Risks and Common Mistakes
The most persistent mistake is assuming social engineering only affects unsophisticated users. The attacks that have caused the largest losses in crypto history frequently targeted experienced professionals who knew about cybersecurity. Sophisticated targets attract sophisticated attacks, not cruder ones. The defense is not more technical knowledge; it is behavioral consistency, specifically the habit of verifying independently before acting.
For a closely related follow-up, see Exchange Withdrawals Will Pause Again.
Another common mistake is oversharing personal information on social media and in public crypto forums. Information about your portfolio size, the wallets you use, your exchange accounts, and your location all feeds into the reconnaissance phase of social engineering attacks. The less information available about you, the fewer angles attackers have to approach from.
For the specific tactics used in wallet-targeted phishing attacks, which overlap significantly with social engineering techniques, see What Is Crypto Phishing. For users protecting active self-custody setups, Clipboard Hijacking Malware is another relevant follow-up because many social-engineering flows end in malware delivery or address substitution.
Sources
- FBI Internet Crime Complaint Center (IC3)
- CISA: Avoiding Social Engineering and Phishing Attacks
- Chainalysis Crypto Crime Report
Frequently Asked Questions
Crypto transactions are irreversible and pseudonymous. There is no chargeback mechanism and no central authority to appeal to. This makes successful theft permanent in a way that traditional fraud is not. Attackers are strongly incentivized to target crypto users for this reason, and the potential payout per successful attack is higher than in many other fraud categories.
In the US, the FBI’s Internet Crime Complaint Center (IC3) accepts crypto fraud reports. Chainalysis and other blockchain analytics firms sometimes assist in tracking stolen funds. However, the practical recovery rate from social engineering crypto theft is extremely low. Reporting is important for aggregate data collection and law enforcement awareness, but victims should not expect fund recovery.
How do I know if a DeFi project’s Discord is compromised?
Watch for these signals: unexpected “mint” or “whitelist” announcements posted in channels by admins (compromised accounts post urgency-driven messages), links that do not match the project’s official domain, and admin accounts with recently changed usernames or profile pictures. When in doubt, verify any link from Discord against the project’s official Twitter/X account or website before clicking.
Not entirely, but it protects against different threats than social engineering. 2FA prevents unauthorized access to accounts using only stolen passwords. It does not prevent SIM swapping (use authenticator app, not SMS). It does not prevent you from willingly handing funds to a scammer. 2FA is a necessary layer but not sufficient on its own.
What is the pig butchering scam and how widespread is it?
Pig butchering (sha zhu pan) is a long-con romance-style social engineering operation where trust is built over weeks before a fraudulent investment platform is introduced. FBI data suggests these operations extracted over $3.5 billion from US victims in 2023 alone. They are primarily run from Southeast Asian operation centers using trafficked labor, and they represent the largest category of crypto fraud by dollar value in recent years.