Last Updated on April 14, 2026 by Snout0x
Most crypto theft articles use “phishing” and “smart contract drain” interchangeably. They should not. These are two distinct attack categories that work through different mechanisms, exploit different vulnerabilities, and require different defenses. Conflating them leads to incomplete mental models, which means users protect themselves against one type while remaining completely exposed to the other. This article breaks down how each attack works and where they diverge.
The fastest way to separate them is this: phishing asks you to reveal something secret, while a smart contract drain asks you to sign something dangerous. If you know which of those two things is happening, the correct defense becomes much easier to apply in real time.
This content is for educational purposes only and should not be considered financial or investment advice.
This article may contain affiliate links. If you purchase through these links, Snout0x may earn a commission at no additional cost to you.
Key Takeaways
- Phishing attacks target credentials, recovery phrases, or private keys through deception.
- Smart contract drain attacks exploit signed token approvals to transfer funds via on-chain mechanics.
- Phishing requires the victim to hand over information. Drain attacks require only a signature on a malicious transaction.
- A hardware wallet does not prevent phishing if the recovery phrase is disclosed on a fake site.
- Revoke.cash and similar approval managers are specific defenses against drain attacks, not phishing.
How Classic Phishing Works
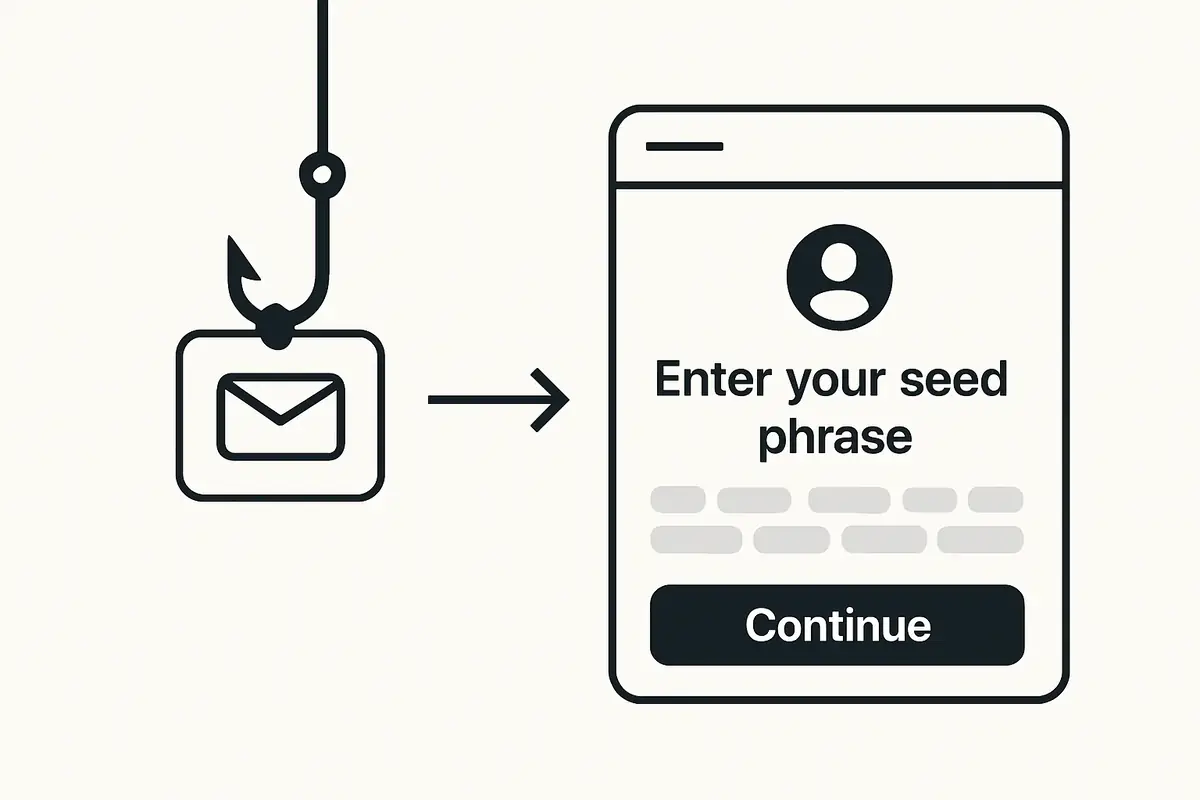
Traditional phishing in crypto follows a straightforward deception pattern: the attacker impersonates a trusted interface and the victim enters sensitive information. The attack does not require any smart contract interaction and does not need the victim to sign a transaction.
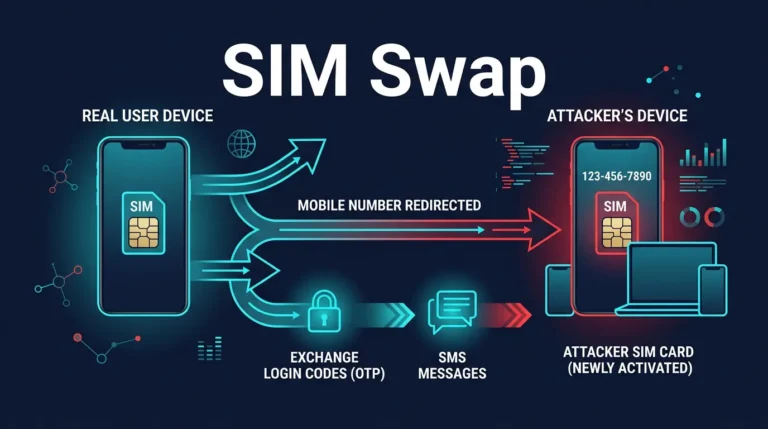
The most common vectors are fake wallet recovery sites, which ask for your recovery phrase under the pretense of restoring access, phishing emails with links to fake exchange login pages, and Discord or Telegram messages from fake support staff directing users to “verification” sites that capture everything typed into them.
Once the attacker has the seed phrase or private key, they control the wallet permanently. Every address derived from that seed phrase is compromised. The attacker can drain balances at any time, and there is no on-chain mechanism to revoke their access short of moving funds to a completely new wallet with a fresh seed phrase.
The key characteristic of phishing is that the victim is tricked into disclosing something secret. The attack does not happen at the smart contract layer. It happens at the human layer, through social engineering and imitation. For a deeper look at how phishing attacks reach wallet users specifically, see Crypto Wallet Phishing Attacks.
How Smart Contract Drain Attacks Work
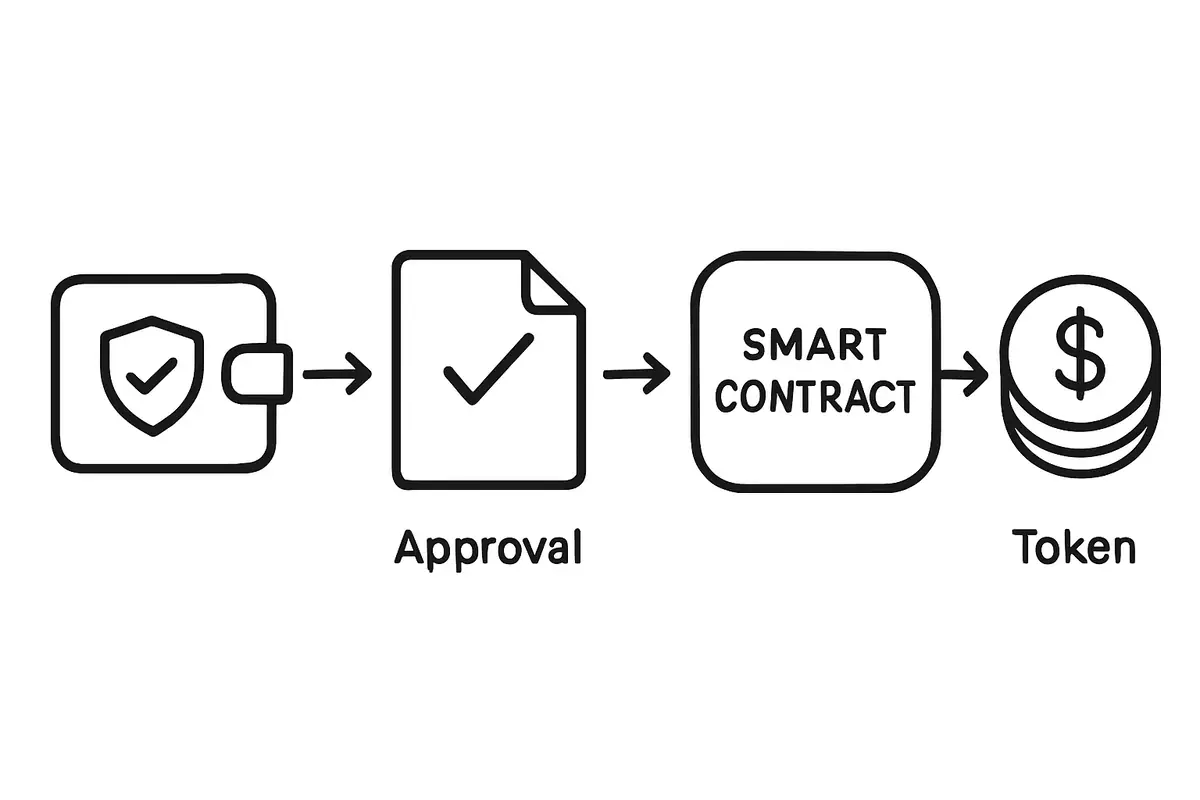
Smart contract drain attacks are fundamentally different. The attacker does not need your seed phrase or your private key. They need you to sign one specific transaction: an approval granting their contract the right to spend your tokens.
Ethereum and EVM-compatible blockchains use an ERC-20 approval mechanism. When you interact with a DeFi protocol, you typically grant it permission to spend a specific amount of a specific token on your behalf. This approval is recorded on-chain and persists indefinitely until revoked. A malicious approval granting unlimited access to your tokens allows the attacker to transfer every token in your wallet at any time after the approval is signed.
The delivery method for these attacks has evolved significantly. Initially, drain attacks required users to visit a fake DeFi interface. Today, attackers embed malicious approval requests in:
- Fake airdrop claim pages promoted through paid social media ads.
- NFT metadata that triggers a wallet prompt when the NFT is viewed.
- Fake governance voting links posted in compromised official Discord servers.
- Malicious browser extensions that inject approval prompts into legitimate DeFi interfaces.
- Wallet connect requests from unknown dApps listed in wallet browser directories.
The critical distinction: you do not disclose anything secret. Your private key stays in your wallet. The attack works by using the legitimate permission system of the Ethereum protocol against you. Once the approval is signed, the attacker can call the approved contract any time to transfer your tokens, without any further interaction from you.
Side-by-Side Comparison
The differences between these two attack types affect not just how they work but what you need to do to protect yourself against each. Here is how they compare directly:
- What the attacker needs from you: Phishing requires your seed phrase or private key. Drain attacks require only a signed approval transaction.
- What they steal: Phishing gives complete wallet control permanently. Drain attacks steal specific approved token balances.
- How detection works: Phishing events are visible when you notice your wallet is drained without any transaction you initiated. Drain approvals can sit silently for days before being executed.
- How they are delivered: Phishing uses fake sites and social engineering. Drain attacks use malicious transaction requests via dApps, airdrop sites, and compromised Discord links.
- Hardware wallet protection: A hardware wallet does not prevent seed phrase phishing if you type the phrase into a fake site. It can prevent drain attacks if you read the transaction details on the device screen and refuse suspicious approvals.
- Recovery options: Neither has good recovery options after execution. But drain attacks can sometimes be mitigated by revoking the approval before the attacker acts, if you catch the malicious signature quickly.
The decision framework is practical rather than academic. If a page, message, or support chat wants you to type a secret, you are in phishing territory and the correct move is to stop immediately. If a dApp or wallet popup wants you to sign an approval, you are in drain territory and the correct move is to inspect the spender, amount, and purpose before confirming. Both steal funds, but they do not ask the victim to do the same thing.
Defenses for Each Attack Type
Because these attacks exploit different vulnerabilities, the defenses are different. Knowing which defense applies to which threat helps you allocate your attention correctly.
Defending Against Phishing
- Never enter a seed phrase into any website or browser extension under any circumstances.
- Navigate to wallets and exchanges directly from bookmarks rather than from search results or email links.
- Verify URLs character by character before entering any credentials.
- Treat all unsolicited DMs offering help as potential phishing vectors.
Defending Against Smart Contract Drains
- Read every approval transaction on your hardware wallet screen before signing. Unlimited approvals (max uint256 amounts) to unknown contracts should be refused.
- Audit and revoke existing approvals regularly using Revoke.cash or the Etherscan token approval checker.
- Use a dedicated wallet for DeFi interactions that is separate from your long-term cold storage.
- Avoid signing approval transactions from unknown or newly launched dApps until they have an established audit and usage history.
Where the Lines Blur
Some attacks combine both approaches. A phishing site may, instead of asking for a seed phrase, prompt you to connect your wallet and sign a transaction. This moves it from pure phishing into drain territory. Conversely, social engineering can be used to convince you that a drain-triggering transaction is safe to sign.
The common thread is that you are being deceived into taking an action. The defense in both cases is the same at a high level: slow down, read what you are actually being asked to do, and refuse anything unexpected. In phishing this means refusing to enter secrets. In drain attacks this means refusing to sign approvals you do not understand.
Practical Usage
Use a two-question check before every wallet interaction. First: am I being asked to reveal a secret, such as a seed phrase, private key, recovery code, or exchange password? If yes, treat it as phishing and stop immediately. Second: am I being asked to sign an on-chain approval or wallet connection request? If yes, inspect the contract, spender, and approval amount on the wallet screen before confirming. This separates credential theft from approval abuse in a way you can apply in real time.
A practical two-wallet setup helps here: keep one wallet for long-term storage that never connects to random dApps, and a separate wallet for DeFi or airdrop activity. If a phishing page captures credentials for one service or a drain approval hits the active wallet, the blast radius is limited. After any suspicious interaction, review recent approvals with Revoke.cash or the block explorer’s token approval tool before using the wallet again.
The verdict is simple. Phishing is the more absolute catastrophe because once a recovery phrase is disclosed, the whole wallet is compromised and there is nothing to revoke. Smart contract drains are narrower in mechanism but easier to miss because they look like ordinary wallet activity. If you are defending against total wallet takeover, focus first on never entering secrets. If you are defending against DeFi-specific wallet abuse, focus on reading and limiting approvals.
Risks and Common Mistakes
The most common mistake is assuming a hardware wallet makes you fully safe against drain attacks. It does not prevent you from signing a malicious approval if you do not read what the device is asking you to confirm. A hardware wallet’s security guarantee is “nothing is signed without your physical confirmation,” not “all transactions you confirm are safe.” The human reading the screen is the last line of defense.
Another mistake is having a large number of old, forgotten approvals on DeFi wallets. Every unlimited approval is a latent risk. Attackers sometimes wait months before executing a drain. Regularly auditing and revoking approvals is a basic hygiene step that most wallet users neglect.
Sources
- CISA: Avoiding Social Engineering and Phishing Attacks
- MetaMask Support: What Is a Token Approval?
- Revoke.cash: What Are Token Approvals?
Frequently Asked Questions
Can a hardware wallet stop a smart contract drain?
Only if you read the approval transaction carefully on the device screen and refuse suspicious requests. A hardware wallet requires physical confirmation but will sign whatever you approve. The protection lies in the verified display showing you what you are signing, not in automatic filtering of malicious transactions.
If I revoke an approval quickly after signing it, am I safe?
Possibly. If the attacker has not yet executed the drain, revoking the approval removes their ability to do so. However, revocation is itself an on-chain transaction that takes time to confirm. A sophisticated attacker may execute the drain in the same block or very shortly after the approval is signed, before you can revoke.
Does Bitcoin have drain attacks?
Bitcoin does not use the ERC-20 approval model, so drain attacks as described here do not apply. Bitcoin’s UTXO model requires the spender to know and use the private key for each output. The approval permission layer that drain attacks exploit does not exist in Bitcoin’s base protocol.
What is a “drainer kit” and why is it a problem?
Drainer kits are pre-built software packages sold on underground markets that automate the delivery and execution of drain attacks. They lower the technical barrier significantly: someone with minimal programming knowledge can deploy a drain attack using a pre-built kit pointed at a fake dApp or airdrop site. The availability of these kits is why drain attacks have scaled so broadly.
Are Solana or non-EVM chains affected by drain attacks?
Yes. Solana has its own permission model for token accounts, and drain-style attacks have been executed on Solana through malicious dApp connections. The specific mechanics differ from EVM approval drains, but the underlying pattern (tricking users into signing a transaction that authorizes token transfers) applies across most modern smart contract-capable blockchains.