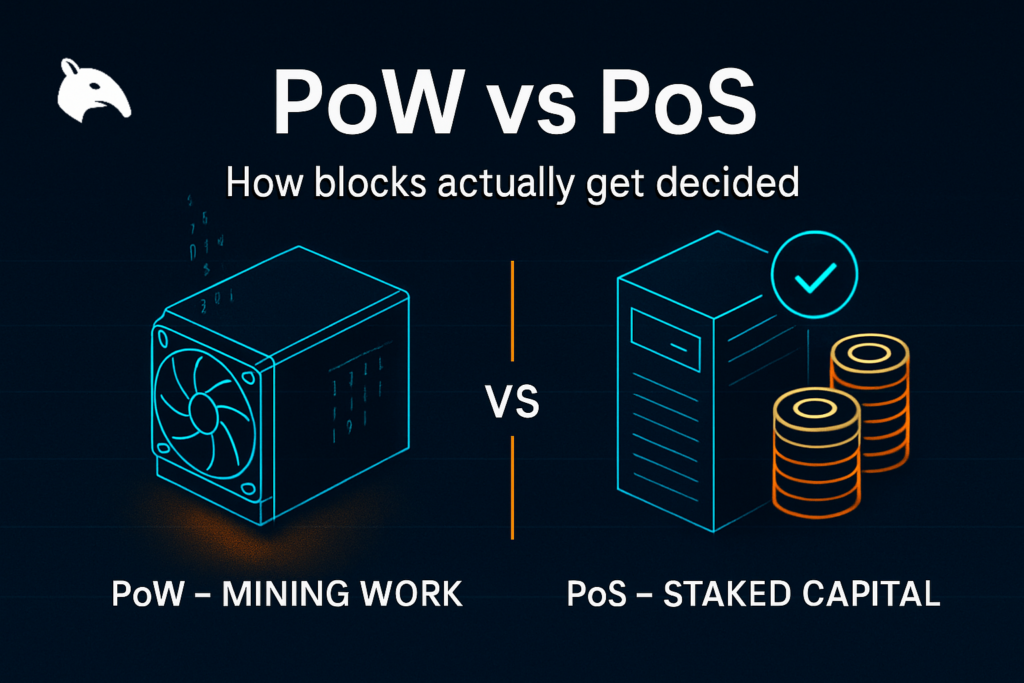
Proof of work and proof of stake are the two most important blockchain consensus models, but they secure networks in very different ways. Proof of work relies on miners spending electricity and hardware resources to compete for block production. Proof of stake relies on validators locking capital as collateral and risking penalties if they behave dishonestly. Both are trying to solve the same problem: how do many independent participants agree on blockchain history without trusting a central operator?
The useful comparison is not “which one is better in all cases.” It is which trade-offs each model makes. PoW externalizes security cost into energy and hardware. PoS internalizes security cost into staked capital and slashing risk. Understanding that difference is more valuable than repeating surface-level debates about speed or branding.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- Both models secure consensus, but they price attack cost differently: PoW uses physical computation; PoS uses bonded capital.
- PoW relies on miners, hashrate, and difficulty: Security comes from the cost of producing enough work to outcompete the honest chain.
- PoS relies on validators, stake, and slashing: Security comes from the cost of acquiring and risking enough stake to influence consensus.
- User trade-offs are not just about speed: Decentralization, client diversity, operator concentration, and failure modes matter as much as throughput.
- The right comparison is model versus model, not marketing versus marketing: Every chain still depends on how the chosen model is implemented in practice.
What Problem Both Models Are Solving
A blockchain needs a way to decide which transactions are valid, which block comes next, and which chain history everyone should recognize as canonical. Without a consensus mechanism, different participants could keep incompatible ledgers and the system would not have one reliable state.
Both models solve this by making dishonest participation expensive. The difference is where that cost sits. One useful mental model is to think of consensus as a system for pricing bad behavior. PoW makes you pay in energy and hardware competition. PoS makes you pay in locked capital that can be penalized or diluted by bad behavior.
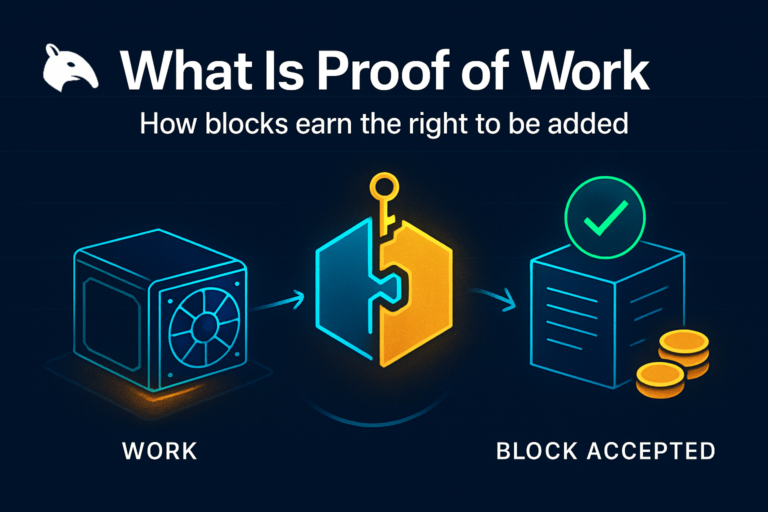
How PoW Works
In proof of work, miners gather transactions, build candidate blocks, and compete to find a valid hash below the current difficulty target. Finding that hash requires brute-force computation. The successful miner earns the right to propose the next block and collect block rewards plus transaction fees, assuming the rest of the network accepts the block as valid.
The security intuition is straightforward: rewriting history means reproducing or outpacing the honest network’s ongoing work. That becomes expensive because it requires real-world energy, hardware, and operational capacity. The most relevant local reference for the mechanism itself is What Is Proof of Work?.
How PoS Works
In proof of stake, validators lock tokens as collateral and are selected to propose or attest to blocks according to protocol rules. If they behave honestly and stay online, they earn rewards. If they sign conflicting messages, remain unavailable for too long, or violate consensus rules, they can lose rewards or part of their stake through penalties or slashing.
The corresponding intuition is that validators do not prove commitment by burning energy. They prove commitment by putting capital at risk. For the role-specific detail behind that, the best local follow-up is What Is a Validator Node?.
The Core Difference: External Cost vs Bonded Capital
The deepest difference between the two models is where security cost lives. PoW pushes cost outward into hardware and electricity. PoS pushes cost inward into staked capital and penalty rules. Both create economic resistance to attack, but they do so through different resource assumptions.
A practical mental model is to compare them like two forms of collateral. PoW says, “Show me that you burned scarce real-world resources.” PoS says, “Show me that you locked scarce in-system capital and can be punished if you cheat.” Neither approach is free. They simply anchor trust in different places.
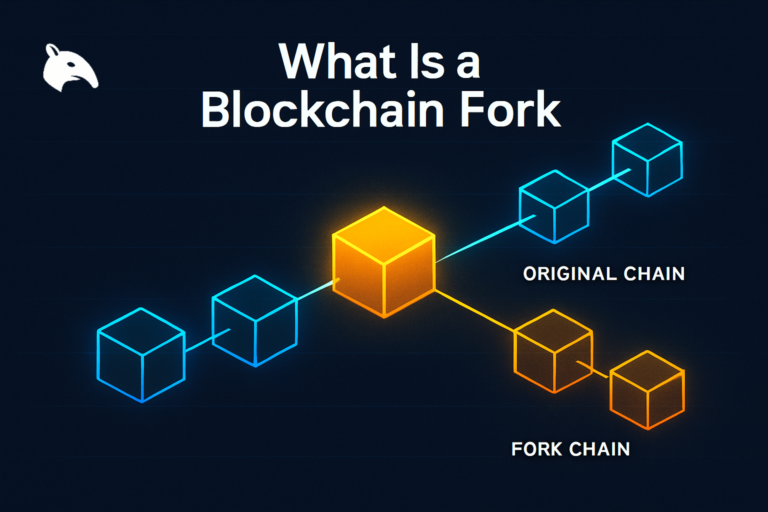
One operator insight is that this difference changes how people argue about security. PoW debates often revolve around energy, mining concentration, and hardware access, and disagreements on those trade-offs have historically led to blockchain forks. PoS debates often revolve around stake concentration, slashing design, governance power, and custody intermediaries. The attack surfaces are not identical because the security budget is not identical.
Security Trade-Offs
PoW security strengths and weaknesses
PoW has a strong physical-cost property. Attacking the chain generally requires access to large amounts of specialized hardware and energy. That makes attack cost visible and external to the blockchain itself. It also means the network’s security can be discussed in terms of hashrate, power cost, and mining infrastructure.
The weaknesses are operational concentration and industrial scale. Mining can centralize around regions with cheap power, large facilities, or major equipment suppliers. A chain may be decentralized in theory but still depend heavily on a limited set of mining pools, jurisdictions, or ASIC manufacturers in practice.
PoS security strengths and weaknesses
PoS reduces dependence on large energy expenditure and can make validator participation more accessible in some systems. It also makes malicious behavior punishable at the protocol level through slashing or stake penalties. That means a dishonest participant can lose the very capital used to secure the network.
The weaknesses often show up around stake concentration, custodial staking services, validator-client monoculture, and governance influence. If too much stake collects under a few operators, exchanges, or liquid-staking providers, the system’s formal openness can still mask a narrower power structure underneath.
A second operator insight is that PoS often looks cleaner at the surface because there is less visible physical infrastructure. But invisible concentration is still concentration. When stake, custody, or client usage clusters too heavily, the risk simply moves from mining warehouses to validator and governance bottlenecks.
Decentralization Trade-Offs
Decentralization is not one number. It includes who can participate, how expensive participation is, how easy it is to validate independently, and how much control gets concentrated in practice. PoW and PoS score differently on those dimensions.
- PoW participation cost: Competitive mining usually requires major hardware investment, but full-node verification can remain relatively independent of mining.
- PoS participation cost: Validation may require less physical infrastructure, but meaningful influence can cluster with large token holders or staking intermediaries.
- PoW validation separation: The people producing blocks and the people validating rules are often more clearly separated.
- PoS capital concentration risk: Wealth concentration, exchange staking, or liquid-staking dominance can create outsized influence.
That is why simplistic claims such as “PoS is automatically centralized” or “PoW is automatically decentralized” are too weak. The real answer depends on network design, client diversity, operator behavior, and how users actually interact with the chain.
What Regular Users Should Actually Care About
Most users are not choosing between mining rigs and validator infrastructure. They are choosing which systems to trust with assets, which trade-offs make sense for their use case, and what kinds of failures are more likely to matter for them. From that perspective, the key questions are practical.
- How hard is the chain to attack economically?
- How concentrated are block production and rule enforcement?
- Can ordinary users verify the chain independently?
- What happens if major operators fail, collude, or go offline?
- What kind of trade-offs is the network making to achieve speed, cost, and scale?
For a long-term investor, the consensus model matters because it shapes security assumptions. For an active user, it matters because it influences uptime, finality, fee behavior, validator or miner concentration, and what kinds of infrastructure risk sit beneath the wallet interface.
Practical Usage: How to Compare PoW and PoS Without Getting Misled
A practical comparison starts by refusing one-dimensional arguments. Low fees alone do not settle the question. High energy use alone does not settle the question. The better method is to compare what each system is asking participants to risk, who is likely to accumulate influence, and how easy it is for outside users to verify the chain independently.
- Use PoW when you want to analyze external security cost: Focus on hashrate, mining difficulty, hardware concentration, and node enforcement.
- Use PoS when you want to analyze bonded-capital security: Focus on validator concentration, staking distribution, slashing design, and custody concentration.
- Do not confuse performance with consensus quality: Throughput and UX improvements can come from many layers besides the base consensus model.
- Check implementation, not just ideology: The real trade-offs show up in how the chain is run, not only in how the whitepaper describes it.
- Read consensus as one part of the system: Wallet infrastructure, client diversity, governance, and application design still matter after the consensus choice is made.
A good operator frame is to ask: “If things go wrong, what resource would an attacker need to dominate, and who would be in a position to stop or reject that attempt?” That question reveals the difference between external work-based security and internal stake-based security much better than slogan-level debate.
Risks and Common Mistakes
- Treating energy use as the whole PoW story: Energy is part of the cost model, but the real issue is how that cost translates into attack resistance and rule enforcement.
- Treating staking yield as the whole PoS story: Yield can distract from validator concentration, slashing risk, and dependence on large operators.
- Assuming consensus alone determines everything: Wallet design, governance, client diversity, and infrastructure concentration still shape the chain’s real-world behavior.
- Reading decentralization from marketing claims: Many networks look open on paper while relying heavily on a small set of miners, validators, exchanges, or service providers.
- Using one metric to decide the whole debate: Hashrate, APY, fees, or throughput alone are all too narrow to explain the real trade-offs.
Sources
Frequently Asked Questions
What is the difference between PoW and PoS?
PoW secures a chain through costly computation performed by miners, while PoS secures a chain through validators locking capital at risk. Both aim to secure consensus, but they price attack cost differently.
Is PoW more secure than PoS?
Not automatically. PoW and PoS create security through different mechanisms and different concentration risks. The better question is how well a specific chain implements its chosen model.
Why do people criticize PoW?
Critics usually focus on energy use, mining concentration, and hardware barriers. Supporters argue that those costs are part of what gives the model its credible attack resistance.
Why do people criticize PoS?
Critics often point to stake concentration, large custodial validators, and governance influence. Supporters argue that PoS lowers operational barriers and can punish bad validator behavior directly through slashing.
Which consensus model should users trust more?
Users should trust implementation quality, decentralization in practice, and independent verifiability more than slogans. The consensus label matters, but how the actual network is operated matters just as much.