The most common crypto security mistakes are not exotic technical failures. They are ordinary habits that quietly widen attack paths: storing sensitive data in the wrong place, trusting the wrong channel, using weak account recovery, mixing high-value storage with risky activity, and reacting too quickly under pressure. Most losses happen when one of those habits gives an attacker a cheaper route than breaking the wallet itself.
A practical way to think about it is this: bad OpSec usually does not fail all at once. It fails through one avoidable shortcut at the wrong moment. That is why fixing a few repeat mistakes often improves security more than buying another product.
This content is for educational purposes only and should not be considered financial or investment advice.
Why These Mistakes Matter So Much
Crypto is unforgiving to operational mistakes because theft is often fast, recovery is limited, and many attack paths work by abusing the user’s environment instead of attacking the chain directly. If you want the broader definition layer first, the clean local baseline is What Is OpSec in Crypto?. This article focuses on the mistakes that repeatedly break that model in practice.
Real-world pattern: users often think the danger starts when money moves. In reality, the failure often starts earlier, when a password is reused, a screenshot is uploaded, a DM is trusted, or a wallet gets used in too many roles at once.
Mistake 1: Storing Recovery-Critical Data in Convenient Places
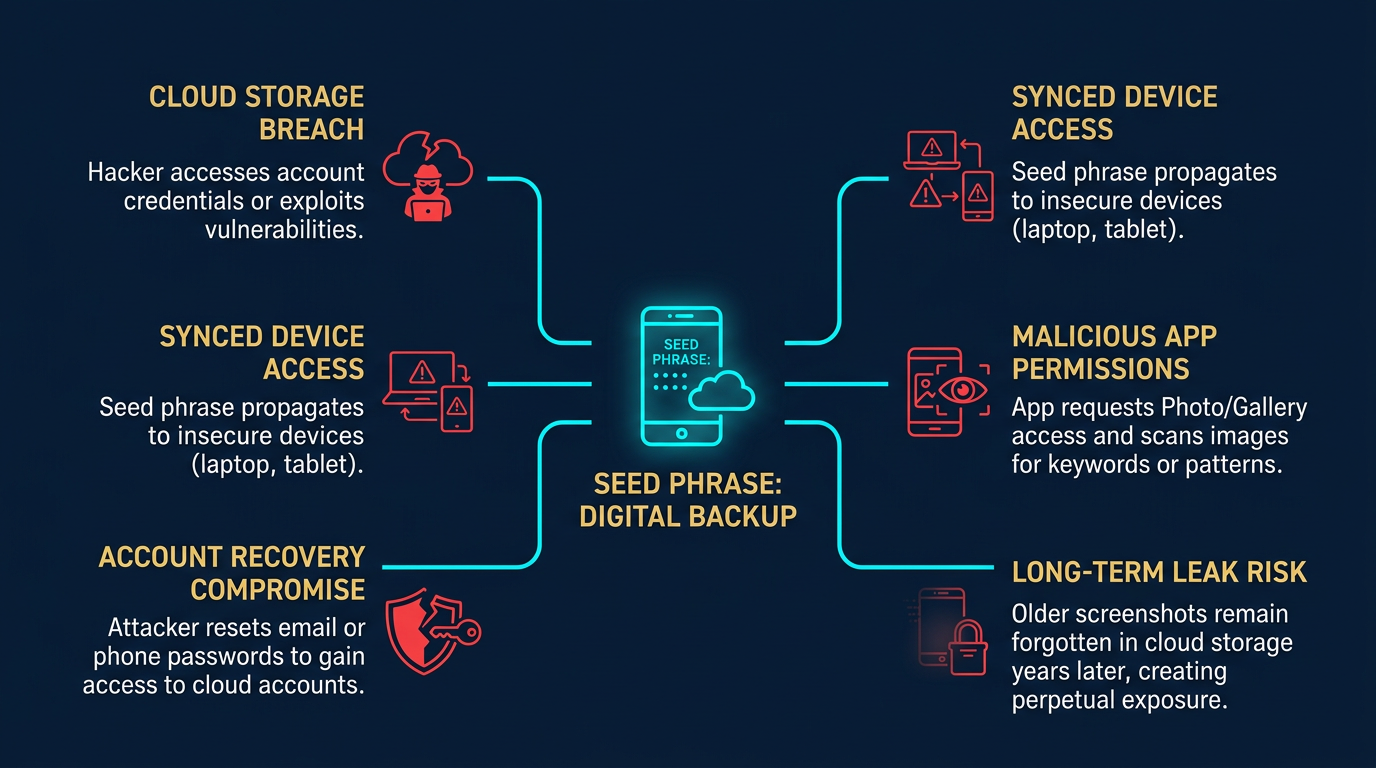
One of the most dangerous mistakes is putting sensitive information where convenience tools can reach it. Screenshots of seed phrases, private notes in cloud apps, saved photos, emailed backups, or plaintext password files create theft paths that bypass otherwise strong wallet choices.
Real-world example: a user writes down a recovery phrase but also takes a phone screenshot “just in case.” The wallet may be secure, but now the seed phrase may sync to cloud photo backups, appear in device search, or become exposed during account takeover. The backup step meant to reduce risk has created a second attack surface instead.
Mistake 2: Using One Wallet for Storage, DeFi, and Experiments
When one wallet holds long-term assets, signs DeFi approvals, tests new dapps, and receives routine transfers, a single mistake can touch everything. This is one of the most common structural failures in crypto security because it feels efficient until the day one bad interaction matters.
For a closely related follow-up, see How to Choose a Crypto Wallet: A Practical Security Framework.
The practical fix is role-based separation. The best local bridge is What Is a Multi-Wallet Strategy in Crypto?, followed by How to Structure a Multi-Wallet Setup. If risky activity deserves access, it should usually happen in a wallet that does not also protect meaningful long-term value.
Mistake 3: Treating Every Message Like a Customer-Service Workflow
Attackers rarely need to beat the wallet first if they can control the conversation. Fake support DMs, urgent login alerts, impersonated admins, and recruiter-style messages all work because they shift the user into a private problem-solving mode before proper verification happens.
Real-world scenario: a user posts publicly about a wallet issue and receives a fast private reply from “support.” The message looks helpful, moves to a DM, and introduces a verification portal. The attack is already working because the user is treating the original channel as trustworthy. The most relevant local follow-ups are Social Engineering in Crypto and What Is Crypto Phishing?.
Mistake 4: Using Weak Email, Weak 2FA, or Weak Recovery Paths
Many users focus on the wallet but neglect the accounts around it. A weak email account, password reuse, SMS-based recovery, or badly protected exchange login can make a stronger wallet choice feel irrelevant. If the recovery stack is easy to hijack, the wallet is not the only thing that matters anymore.
Operator insight: email security is often treasury security in disguise. If email can reset access to your exchange account, password manager, or cloud storage, then a weak email stack can be a direct path to financial loss even if your wallet device itself never gets touched.
Mistake 5: Mixing High-Value Signing With a Messy Device
High-value activity on a device full of random downloads, browser extensions, cracked software, or general browsing is a recurring OpSec error. The risk is not hypothetical. Malware, clipboard hijackers, browser compromise, and credential theft all become more realistic when the device is treated like both a custody workstation and an entertainment machine.
Real-world example: a user copies a destination address from a trusted source, but malware on the laptop swaps the clipboard value before pasting. The transfer looks routine right up to the point of settlement. The wallet was not weak. The operating environment was.
Mistake 6: Signing Too Fast Because the Amount Looks Small
Users often lower their guard when the transaction value seems trivial. That is exactly why approval-heavy mints, airdrop claims, and “quick test” transactions are dangerous. The direct payment may be small, but the permission or trust relationship created by the signature may be much broader than the user realizes.
This is where Token Approval Risk Explained becomes relevant. A small transaction prompt can still create a larger future exposure if the approval remains active or the spender turns out to be unsafe.
Mistake 7: Never Reviewing Old Wallet History and Approvals
Old wallets often become riskier over time because people remember recent actions better than historical permissions. A wallet that has interacted with many dapps, claims, bridges, or experiments may carry stale approvals, unknown signatures, or confusing history that nobody has audited recently.
Real-world pattern: a wallet used for testing a year ago still holds or later receives meaningful assets, and an old spender relationship becomes relevant again. The problem is not only what the user did today. It is what the wallet was allowed to accumulate over time.
Mistake 8: Sharing Too Much Publicly
Public oversharing creates targeting data. Wallet screenshots, holdings talk, travel announcements, screenshots of device setups, or discussions about recovery methods may feel harmless individually, but together they help attackers choose delivery methods and believable stories.
This matters especially in crypto because attackers often do not need your exact balance to target you. They only need enough context to believe you are worth social engineering, phishing, extortion, or account-recovery pressure.
Practical Usage: Better Replacements for These Habits
- Move recovery-critical data offline: Do not rely on screenshots, cloud notes, or inbox storage for secrets that control funds.
- Separate wallet roles: Storage, daily use, and risky experimentation should not all live in one wallet.
- Harden the account layer: Improve email security, use stronger MFA, and treat recovery settings as part of financial security.
- Use cleaner devices for higher-value activity: Reduce unnecessary extensions, risky downloads, and mixed-use behavior where signing happens.
- Slow every urgent workflow down: Verify outside the original channel before clicking, signing, or entering credentials.
A practical operator routine is to ask after every security-related habit: “If this exact shortcut were exploited, what would the attacker actually gain?” If the answer is “my email,” “my exchange recovery,” “my wallet approval,” or “my seed phrase,” the shortcut is probably too expensive to keep.
If you want a live follow-up that turns these ideas into a routine, the most useful adjacent resource is the crypto wallet security checklist.
Risks and Common Mistakes
- Thinking “small shortcut, small risk”: A tiny convenience choice like saving one screenshot or reusing one email password can create a disproportionately large attack path if it touches recovery or custody.
- Fixing tools but not habits: A user may upgrade wallets or devices while still trusting DMs, using weak recovery channels, or signing too fast under pressure.
- Confusing familiarity with safety: An old wallet, known app, or polished interface can still become dangerous if the surrounding habits are weak or the account layer gets compromised.
- Waiting for a scare before changing behavior: Many operational failures are obvious only in hindsight, so habits should be corrected before a visible incident forces the lesson.
Sources
- CISA: Secure Our World
- FBI IC3: North Korea Aggressively Targeting Crypto Industry with Well-Disguised Social Engineering Attacks
- Chainalysis: Understanding Crypto Drainers
Frequently Asked Questions
What are the most common crypto security mistakes?
Common mistakes include storing sensitive data in cloud tools, trusting unsolicited support messages, relying on weak recovery methods, using one wallet for everything, and signing too quickly without proper verification.
Why do small OpSec mistakes matter so much?
They matter because attackers usually look for the cheapest available route. A small convenience shortcut can become the easiest path to credentials, account recovery, approvals, or wallet access.
Is weak email security really a crypto risk?
Yes. Email often supports exchange recovery, password resets, cloud access, and account notifications, so weak email security can undermine stronger wallet decisions.
Should I use one wallet for everything?
Usually no. Using one wallet for storage, daily activity, and risky experiments increases the cost of any single approval or compromise. Role-based separation is usually safer.
What is the fastest OpSec upgrade most users can make?
Many users get the biggest improvement by hardening email and account recovery, separating wallet roles, and slowing down any urgent message or signing flow before acting.