Approval exposure appears whenever you let a smart contract spend tokens from your wallet on your behalf. In DeFi, that permission is often necessary for swaps, lending, staking, or liquidity provision. The danger is that the approval can outlive the single action you intended. If the spender is malicious, compromised, upgraded badly, or simply broader than you realized, the contract may still be able to move your tokens later.
Many users think the risky part is only the final transaction that moves funds. In practice, the approval itself is often the real exposure. Once an allowance exists, the spender can call the token contract again without asking you to reapprove each time. That is why approval risk matters even when the site looked legitimate on the day you signed.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- Approvals are standing permissions: They often remain active after the one action you had in mind is finished.
- Unlimited approvals enlarge blast radius: If the spender is abused later, your whole token balance may be exposed instead of only the amount needed for one transaction.
- Approval risk is broader than outright scams: Legitimate protocols can still become dangerous through contract bugs, governance changes, or compromised frontend workflows.
- Wallet security alone is not enough: A safe device does not cancel a dangerous allowance already recorded on-chain.
- Good habits reduce exposure: Smaller approvals, wallet separation, periodic review, and revocation matter more than trusting your memory.
How Token Approvals Create Risk
On Ethereum and similar chains, ERC-20 tokens are controlled by token contracts, not by your wallet directly. When you want a protocol to swap, lend, or move tokens for you, you first sign an approval that grants an allowance. That approval tells the token contract that a specific spender may use transferFrom up to a defined amount. The convenience is obvious. The risk is that the permission can persist long after your attention moves elsewhere.
A simple mental model is to think of approvals like leaving a debit card on file with a merchant. You may have intended one purchase, but the real question is what that merchant is allowed to pull later and under what conditions. In crypto, that “merchant” may be a smart contract, a router, or an address you do not fully understand. Once the allowance is recorded on-chain, the permission exists whether or not you remember creating it.
Approvals separate permission from execution
This separation is why approvals can be more dangerous than they first appear. The approval transaction may feel routine because no tokens leave your wallet at that moment. But the later transfer can happen without a new confirmation from you if the spender decides to use the allowance. That design is functional for DeFi, yet it means users can create future exposure during a moment that feels low stakes.
If you want the scam-specific version of this pattern, crypto approval scams covers fake sites and malicious lures directly. This article focuses on the broader risk model: approvals themselves can be dangerous even when the initial interaction looked routine.
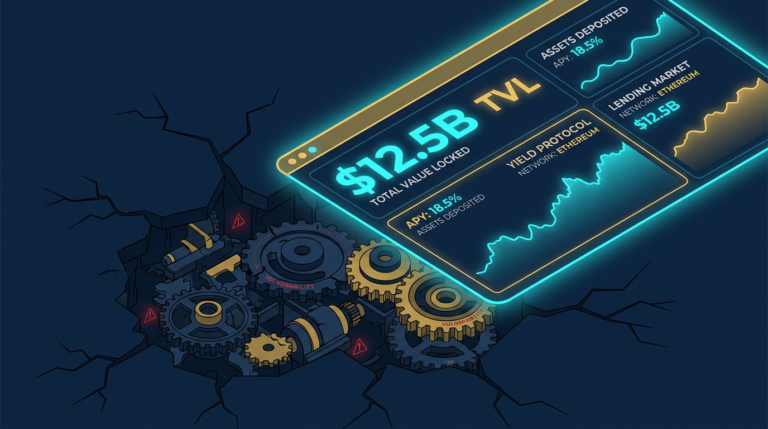
Why Unlimited Approvals Are So Dangerous
An unlimited approval removes the natural cap that would otherwise limit damage. Instead of authorizing a contract to spend exactly the amount needed for one swap or deposit, you allow it to access as much of that token as your wallet holds now or later. That means the exposure can grow over time if you top up the wallet, receive the same token again, or simply forget the approval exists.
Convenience today can become portfolio risk later
Protocols often default to large or unlimited approvals because it reduces friction. You do not need to approve again for every interaction, which makes the app feel smoother. But smoother is not safer. An allowance created for convenience can become a latent vulnerability if the spender contract is exploited, the project changes ownership, the frontend is hijacked, or the user forgets that the approval ever existed.
One operator insight is that approvals become more dangerous as wallets age. A fresh wallet with a few controlled permissions may be manageable. A wallet used for months across DEXs, bridges, launches, mints, and experiments often accumulates old approvals that nobody has reviewed in context. The exposure becomes historical, not just immediate.
The danger is not limited to malicious protocols
Users often think the only bad outcome is being tricked by an obvious scam. In reality, a legitimate protocol can still create approval exposure if its contracts are later exploited, its admin keys are compromised, or its upgrade path introduces a bug. The approval does not care whether the spender became dangerous through fraud, incompetence, or a security incident. The token contract only sees an authorized spender.
This is why approval exposure overlaps with the broader issues discussed in phishing vs smart contract drains. The route to loss may differ, but the underlying theme is the same: permissions and signatures outlast the moment in which you created them.
Where Approval Exposure Commonly Comes From
Most risky approvals come from normal user behavior, not from obviously reckless choices. Swapping on a DEX, bridging to another chain, depositing into a vault, and interacting with a token dashboard can all request spending permission. The problem is not that approvals exist. The problem is that users often do not distinguish between a trusted, limited approval for a known task and a broad, persistent approval whose future implications they have not checked.
If you want the foundational definition behind this concept, read What Is a Crypto Drainer? How Wallet Drains Work.
DEX routers, aggregators, and bridge workflows
Approvals frequently appear in DEX routing, token aggregators, and bridge interfaces because these systems need to move tokens programmatically. That is normal. The risk comes from not knowing exactly which spender is being authorized and whether the amount matches your intent. A bridge or router may work through proxy contracts, shared spenders, or upgraded infrastructure that is less transparent than the user interface suggests.
A second operator insight is that the spender name shown in a wallet popup can create false confidence. What matters is the actual contract address and role, not whether the dApp brand feels familiar. If the approval path is unclear, stop and check the spender before assuming the transaction is routine.
Old wallets and forgotten allowances
Some of the most painful approval losses happen in wallets the user thought were inactive. A person tests a protocol months ago, leaves an allowance open, later tops up the same token balance, and only then discovers that the spender still had permission. That delayed effect is one reason approval risk feels different from obvious wallet theft. The vulnerable moment may happen long before the actual drain.
If you already treat one wallet as a general-purpose experiment account, you are halfway to the right model. The next step is to make the separation explicit so high-value holdings are not sitting in the same place as old permissions. The broader storage framework in how to store crypto safely matters here because approval hygiene works best when wallet roles are separate.
Practical Usage: How to Keep Approval Exposure Under Control
Approval safety is mostly process. You usually do not need a perfect technical understanding of every contract, but you do need a routine that limits how much any single approval can hurt you. The best workflow is to assume that every allowance may outlive your memory and to act accordingly.
- Match the approval amount to the task: If you only need to swap a small amount once, avoid approving your full wallet balance when the interface lets you set a smaller limit.
- Use separate wallets by role: Keep a smaller hot wallet for experimentation and a separate wallet for larger holdings so an old approval cannot reach everything you own.
- Review approvals after each DeFi session: After a swap, bridge, or vault interaction, check which token spender was approved and whether it still needs access.
- Revoke stale allowances proactively: Treat old approvals like unused API keys. If the relationship is over, remove the permission instead of hoping it never matters.
- Pause when the spender is unfamiliar: If the wallet prompt does not clearly match the protocol and action you intended, stop and verify before signing.
A practical routine is to make approval review part of the same session in which you created the allowance. Do the swap or deposit, confirm it worked, then open the approval page on a block explorer or revoke tool and check what remains open. That habit is much more reliable than promising yourself you will “clean it up later.”
Another strong habit is to stop using a wallet as soon as you discover an approval you cannot explain. First verify the spender, then revoke if needed, and if the wallet has a messy history of unknown interactions, consider moving clean assets to a fresh address. The point is not paranoia. It is reducing ambiguity before ambiguity becomes loss.
Risks and Common Mistakes
- Assuming the danger ends after the first transaction: The real exposure can continue long after the initial swap, mint, or deposit is complete.
- Approving first and reading later: Users often treat wallet popups like friction instead of like security checkpoints.
- Leaving unlimited approvals in high-value wallets: Even if no scam is involved, a later contract problem can still reach a large balance.
- Forgetting that top-ups reactivate the problem: A stale approval can become relevant again the moment the same token returns to the wallet.
- Confusing device security with permission security: A hardware wallet can protect signing keys, but it does not erase dangerous allowances you already approved.
Sources
- Ethereum.org: ERC-20 Token Standard
- MetaMask Support: What Is a Token Approval?
- Revoke.cash: What Are Token Approvals?
FAQ: Approval Exposure and Allowances
What is a token approval in crypto?
A token approval is permission you give a smart contract or address to spend a specific token from your wallet up to a defined amount. It is commonly used in DeFi so protocols can move tokens for swaps, deposits, or liquidity actions.
Why is unlimited approval risky?
Unlimited approval is risky because it lets the authorized spender access your whole balance of that token, not just the amount needed for one task. If the spender later becomes malicious or compromised, the damage can be much larger than intended.
Can legitimate protocols still create approval risk?
Yes. Even a legitimate protocol can become dangerous if it is exploited, upgraded badly, or controlled through compromised admin paths. An old approval remains dangerous if the spender later becomes unsafe.
How do I reduce approval exposure?
Use smaller approval amounts where possible, separate high-value holdings from experiment wallets, review allowances after DeFi activity, and revoke permissions you no longer need. Those habits reduce blast radius even if one protocol goes wrong.
Does a hardware wallet remove approval risk?
No. A hardware wallet improves key security and transaction verification, but it does not cancel an allowance you already granted. If you approved a dangerous spender, that risk remains until you revoke the permission or move the assets to a clean wallet.