Last Updated on March 14, 2026 by Snout0x
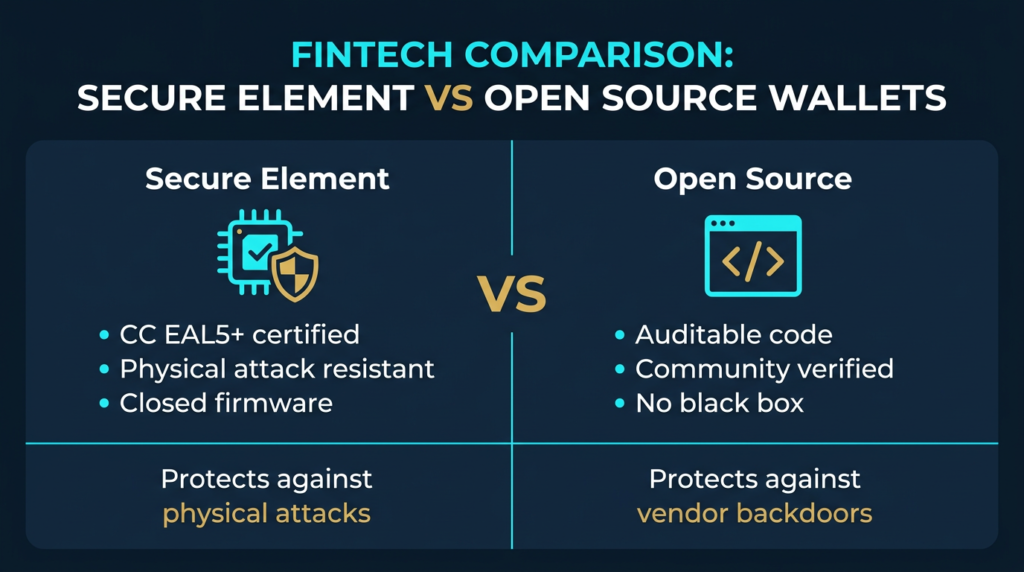
Hardware wallet security sits on two competing philosophies. Secure element wallets embed a tamper-resistant chip that stores or protects key material inside a hardened hardware boundary.
Open-source wallets take a different approach: the firmware code is publicly available, auditable by anyone, and verifiable against what the manufacturer claims the device actually does.
Both approaches have real security value. Neither is universally superior.
The right choice depends on which threat matters more to you, and this article explains the secure element vs open source trade-off clearly, without flattening the differences into marketing slogans.
Disclaimer: This content is for educational and informational purposes only and does not constitute financial, investment, tax, or legal advice. Cryptocurrency markets are volatile and involve risk. Always conduct your own research and consult a qualified professional before making financial decisions.
Affiliate Disclosure: Some links in this article may be affiliate links. If you choose to use them, I may earn a commission at no additional cost to you.
Key Takeaways
- Secure element wallets use a hardened chip to resist physical extraction of secrets and other low-level hardware attacks.
- Open-source wallets let researchers inspect firmware behaviour publicly instead of relying only on vendor claims.
- Secure elements generally win on physical attack resistance, while open-source firmware wins on transparency and independent verification.
- Several modern wallets now combine both approaches: a secure element for hardware protection and open firmware for auditability.
- Your threat model matters more than brand loyalty or spec-sheet slogans when choosing between the two designs.
What Is a Secure Element Wallet?
A secure element (SE) is a dedicated chip designed to protect sensitive cryptographic operations inside a hardened environment. Depending on the wallet architecture, it may store private keys directly, protect key material indirectly, enforce PIN attempt limits, or handle part of the signing and attestation process.
The core idea is the same: sensitive operations happen inside a chip built to resist physical tampering better than a standard microcontroller.
Secure elements used in hardware wallets are commonly certified under the Common Criteria security evaluation framework, often at the EAL5+ or EAL6+ level.
That matters because these certifications are tied to specific hardware attack classes such as voltage glitching, fault injection, and side-channel analysis. Certification is not magic, but it does mean the chip was designed and evaluated with physical extraction resistance in mind.
In a wallet built around a secure element, the host computer sends transaction data to the device, the device validates what should be signed, and the sensitive signing path remains inside protected hardware.
The goal is that your private key is never exposed to your internet-connected computer or casually readable from generic memory.
The trade-off is transparency. Secure element internals are often partly or fully proprietary, which means users cannot audit every layer of what happens inside the chip.
This creates a trust boundary: you benefit from stronger resistance to physical extraction, but you also depend more heavily on vendor claims, certification scope, and implementation honesty.
Ledger is the best-known example of the secure-element-first model. Its devices use a dual-chip design in which a general microcontroller handles interface functions while a certified secure element handles sensitive operations. For a deeper breakdown of how that architecture works in practice, see the Ledger Nano X security analysis.
What Is an Open-Source Hardware Wallet?
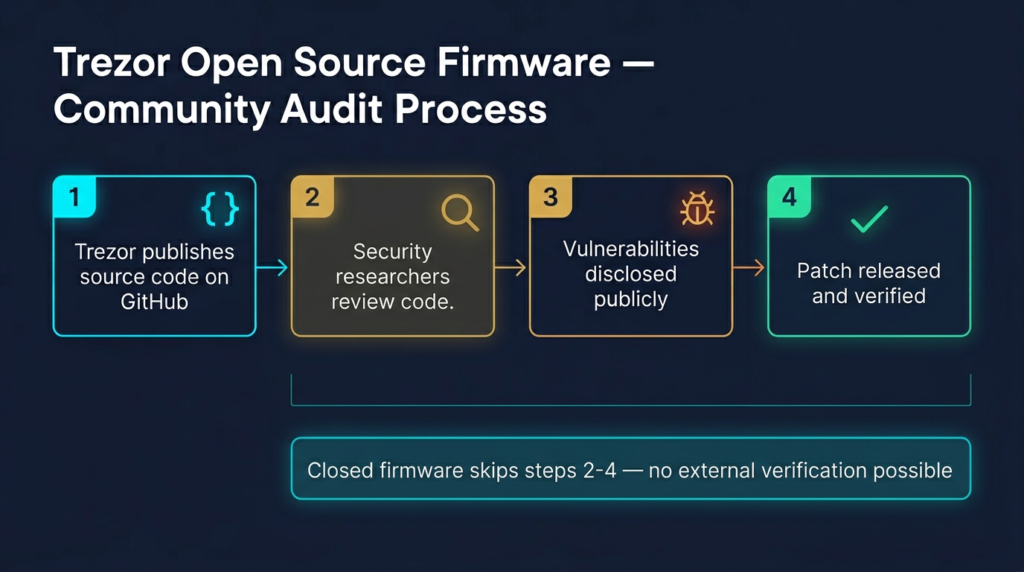
An open-source hardware wallet publishes its firmware code so independent researchers can inspect it, compile it, and compare it against what the vendor distributes. The security argument is straightforward: you should not have to trust a black box if the security-critical code can be verified publicly.
That public visibility matters because hardware wallet security is not just about chips. It is also about transaction parsing, screen verification, address display logic, firmware update behaviour, USB communication, and recovery flows. If those layers are open, researchers can inspect the implementation rather than relying only on marketing claims.
Trezor built its reputation on this philosophy. Earlier Trezor models prioritised openness over secure-element-based hardware isolation, which gave users unusually strong transparency but weaker resistance to advanced physical extraction attacks than wallets built around certified SE chips.
Open-source also makes reproducibility possible. In mature projects, developers can independently verify that the shipped firmware corresponds to the published code. That is a meaningful security property because it narrows the risk that a vendor publishes one thing and distributes another.
The limitation is obvious but important: open-source code is only safer if people actually review it. Public auditability is a security opportunity, not an automatic guarantee. A well-known wallet with active external scrutiny benefits far more from being open than an obscure project that publishes code nobody meaningfully examines.
The Core Security Trade-Off
The secure element vs open source debate is really a debate about two different failure modes: physical compromise and trust compromise.
A physical compromise happens when an attacker gets the device itself and tries to extract secrets through hardware analysis, fault injection, or similar lab-style techniques. Secure elements are specifically built to raise the cost of that attack.
A trust compromise happens when users must rely on closed vendor-controlled code paths they cannot inspect. Open-source firmware directly addresses that problem by allowing public review of the wallet’s security-critical behaviour.
Neither risk is imaginary. Users really do lose devices, travel with them, or face theft. And users also routinely overestimate what a closed hardware boundary proves about firmware behaviour.
The 2023 backlash around Ledger Recover showed why this distinction matters: many users discovered that “keys never leave the secure element” was not the same as “the architecture can never be updated to export protected key material under a different firmware policy.” That episode did not prove malicious intent, but it did expose how much trust closed firmware still requires.
Understanding what self-custody actually means helps here. Hardware design is one security layer. Trust assumptions, recovery design, and operational habits are another.
Physical Attack Resistance: Where Secure Elements Win
If your threat model includes physical theft, border seizure, hostile inspection, or long-term storage of meaningful value, secure elements provide a real advantage. They are designed for hardware-level resistance in ways generic microcontrollers are not.
This is where Common Criteria matters most. A certified secure element has been evaluated against specific attack methods such as fault injection and side-channel analysis. That does not make extraction impossible, but it changes the attack from “read memory from a commodity chip” into “defeat a hardened chip with tested protections.”
For most casual users, the realistic attacker is not a hardware lab. But for larger holdings, more adversarial environments, or long-term cold storage, physical attack resistance becomes much more relevant. In that context, a secure element is not just a spec-sheet extra. It is part of the wallet’s actual security case.
For a broader view of why physical isolation matters, see what cold storage means in crypto and the best practices for hardware wallet setup.
Code Transparency: Where Open Source Wins
The open-source case is strongest when the main risk is not a stolen device but a hidden firmware capability, weak transaction parsing logic, or vendor-controlled code users cannot inspect. If the firmware is open, the manufacturer has less room to hide behind opaque security claims.
This matters because a hardware wallet is only as trustworthy as the code that interprets transaction data and displays what you are authorising. A secure device that parses data incorrectly or obscures what the user is signing can still produce bad security outcomes.
Open-source firmware also enables reproducible verification in stronger ecosystems. BitBox02 is a good example here: Shift Crypto publishes the firmware openly and documents independent verification, which gives users a practical path to confirming that shipped firmware matches public source code.
The limit is that transparency does not automatically equal safety. Open code still needs competent review, responsible maintenance, and an active security culture around the project. Open-source is a better trust model, but it is not a substitute for rigorous engineering.
Can You Have Both?
Yes, and this is where the market has become more interesting. The cleanest version of the old debate – secure element versus open source – no longer describes every serious wallet on the market.
Trezor’s Safe devices blend open-source design with secure-element-based protection. Trezor Safe 3 and Safe 5 use a certified secure element alongside the company’s open firmware approach, while Trezor Safe 7 adds a dual secure-element architecture that includes TROPIC01, an auditable secure element developed within the SatoshiLabs ecosystem.
BitBox02 also complicates the old binary framing. Its firmware is open-source and reproducibly verifiable, but the device also uses a secure chip in its architecture for added protection. That makes it better understood as a transparency-first hybrid rather than a pure “no secure element” design.
Keystone takes the hybrid idea even further by publicly emphasising open-source firmware, open hardware materials, and open secure-element firmware logic in parts of its stack. That does not eliminate every trust boundary, but it meaningfully narrows the black-box problem compared with traditional closed secure-element designs.
Hybrid models do not eliminate trade-offs completely. If any security-critical layer remains proprietary, a trust boundary still exists. But the best hybrid wallets reduce the gap enough that the old either-or framing is no longer the whole story.
Security Architecture Comparison
| Security Property | SE-first wallet | Open-source-first wallet | Hybrid wallet |
|---|---|---|---|
| Physical attack resistance | Usually strongest | Usually weaker | Stronger than pure open designs |
| Firmware auditability | Often partial | Usually strongest | Varies by implementation |
| Trust in vendor internals | Higher | Lower | Reduced, but not zero |
| Reproducible verification | Often limited | Best case possible | Often partial but meaningful |
| Resistance to advanced hardware extraction | Best case | Lower | Improved relative to pure open designs |
| Best fit | High physical-risk environments | High transparency-demand users | Users who care about both |
Which One Should You Choose?
The honest answer is that you should choose based on your threat model, not on brand tribalism.
If your main concern is physical theft or seizure, a wallet with a strong secure-element implementation deserves serious consideration. The hardware protections are designed for exactly that class of risk.
If your main concern is vendor trust and hidden firmware behaviour, a wallet with strong open-source and reproducibility practices is more aligned with that priority. You are reducing the number of black boxes you have to trust.
If both concerns matter – and for many serious self-custody users they do – a hybrid design is usually the most attractive option today. It will not remove every trade-off, but it narrows the gap between physical protection and public auditability more effectively than the older pure models did.
For broader decision help, see the Best Crypto Hardware Wallets security ranking and buyer guide, the Ledger vs Trezor security model comparison, and what an air-gapped wallet is if your threat model leans heavily toward remote attack isolation.
What Secure Element vs Open Source Does Not Settle
This debate does not resolve the most common causes of crypto loss. A secure element will not save you from approving a malicious transaction. Open-source firmware will not save you from storing your seed phrase badly, reusing a compromised computer during setup, or falling for wallet phishing and social engineering.
Hardware wallet architecture is one layer in a broader self-custody system. You still need secure backups, disciplined transaction review, device setup hygiene, and a clear understanding of when to use extra protections like a crypto passphrase.
That is why security-first users should also read the Crypto Wallet Security Checklist, crypto wallet phishing attacks, and social engineering in crypto. The wallet architecture matters, but so does everything around it.
Risks and Common Mistakes
Assuming secure elements remove trust. They improve physical security, but they do not eliminate the need to trust firmware policies and vendor implementation choices.
Assuming open-source automatically means audited. Public code is only meaningfully safer when there is active external review, reproducible builds, and a mature security process.
Ignoring your actual threat model. Many users argue abstractly about architecture without first asking whether their real risk is theft, confiscation, phishing, bad backups, or blind trust in a vendor stack.
Focusing on device specs while neglecting setup hygiene. A strong wallet design still fails if your recovery phrase is exposed, your computer is compromised during setup, or you sign transactions without verifying details on the device screen.
Conclusion
Secure element wallets and open-source wallets solve different security problems. Secure elements are strongest when the risk is physical extraction from a seized or stolen device. Open-source designs are strongest when the risk is hidden firmware behaviour that users cannot inspect.
That is why the best answer is rarely ideological. It is practical. Define your threat model first, then choose the architecture that best addresses it. And if you want both stronger hardware protection and more transparency, the newer hybrid wallets are where the market is heading.
FAQ
Is a secure element always more secure than open-source firmware?
No. A secure element is usually stronger against physical extraction attacks, but open-source firmware is stronger for transparency and independent verification. The better design depends on which threat matters more in your situation.
Can a hardware wallet have both a secure element and open-source firmware?
Yes. Several modern wallets now combine secure-element-based protection with open or largely open firmware design. These hybrid architectures aim to improve physical resistance without giving up as much transparency.
Does open-source firmware mean the wallet has been audited?
No. It means the code can be audited. Whether it actually has been reviewed depends on the project, its community, published audits, and the maturity of its security process.
What did Ledger Recover change in this debate?
It highlighted that closed secure-element architectures still require trust in vendor firmware policy. Many users realised that strong hardware isolation does not automatically mean the architecture can never support key export under a future firmware design.
Which design is best for most retail users?
For many retail users, a strong hybrid design is the most balanced option. But the right answer still depends on whether your bigger concern is physical theft, vendor trust, or simple operational mistakes during self-custody.
Sources
- Bitcoin Developer Documentation – key management and transaction signing fundamentals
- Trezor: Secure Elements in Trezor Safe Devices – official description of Trezor Safe secure-element architecture
- Shift Crypto: BitBox02 Firmware Repository – open-source firmware repository
- Shift Crypto: BitBox02 Firmware Verification – reproducible verification guidance
- Keystone: About Keystone – official overview of Keystone’s open-source security approach