Last Updated on April 12, 2026 by Snout0x
Crypto wallet phishing attacks go beyond generic credential theft. Attackers build infrastructure specifically designed to exploit how crypto wallets connect to websites, how approvals work, and how users respond to urgency. Understanding these attack patterns is more useful than generic security warnings, because the mechanics determine what defenses actually matter.
In practice, the core defense is to distrust surprise links, refuse any website that asks for recovery words, and read approvals on the wallet’s trusted screen before signing. Most wallet phishing succeeds because it gets you to trust the wrong interface at speed, not because it breaks the wallet cryptography itself.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- Wallet phishing targets seed phrases, private keys, and malicious token approvals.
- Fake websites mimic wallet interfaces to capture seed phrases entered during fake “recovery” prompts.
- Approval phishing tricks users into signing transactions that grant unlimited token transfer rights to attackers.
- Hardware wallets protect against remote key theft but not against approval-based drains or seed phrase disclosure.
- Always verify the full URL and never enter a seed phrase into any web interface.
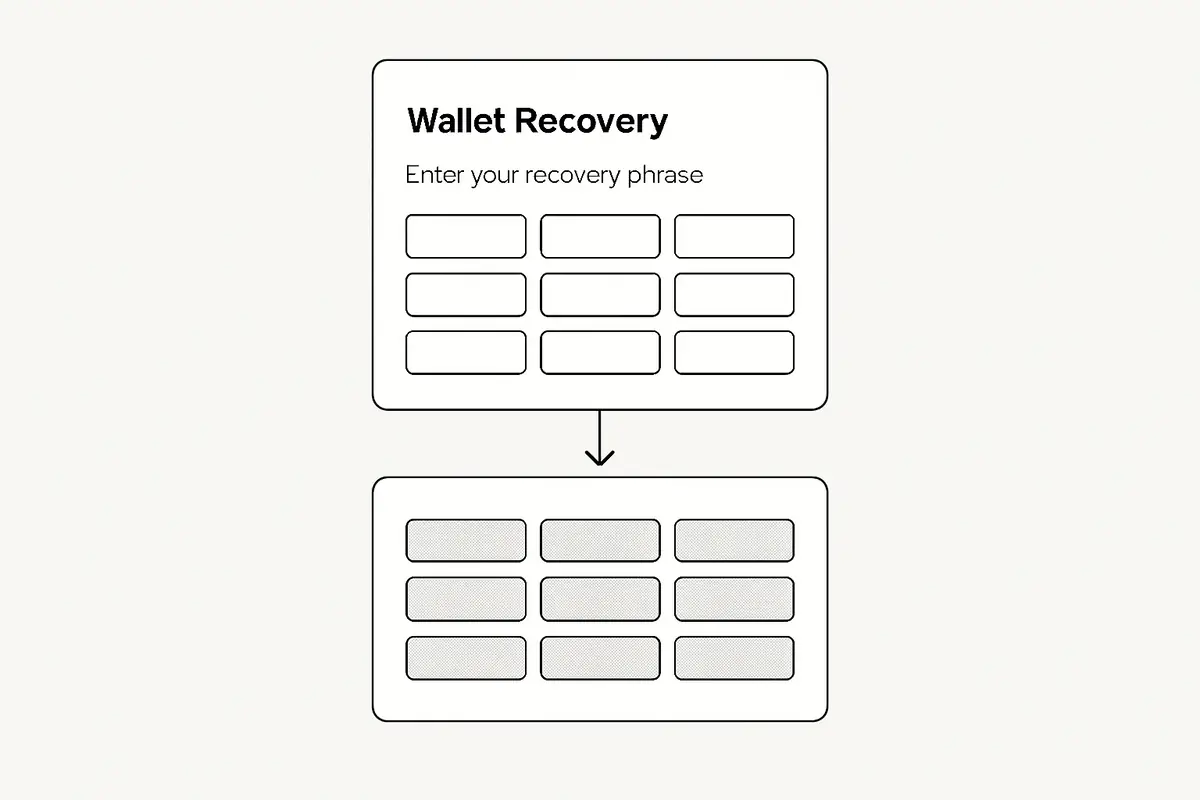
Seed Phrase Phishing
The simplest and most damaging attack type. An attacker builds a replica of a wallet setup or recovery page and routes traffic to it via paid search ads, email links, or social media posts. Users who land on the fake page and enter their seed phrase hand over complete wallet control.
Legitimate wallet software never needs you to enter your seed phrase into a web interface. Setup and recovery happen on the device or in the locally installed app. Any web page asking for your full recovery phrase is an attack.
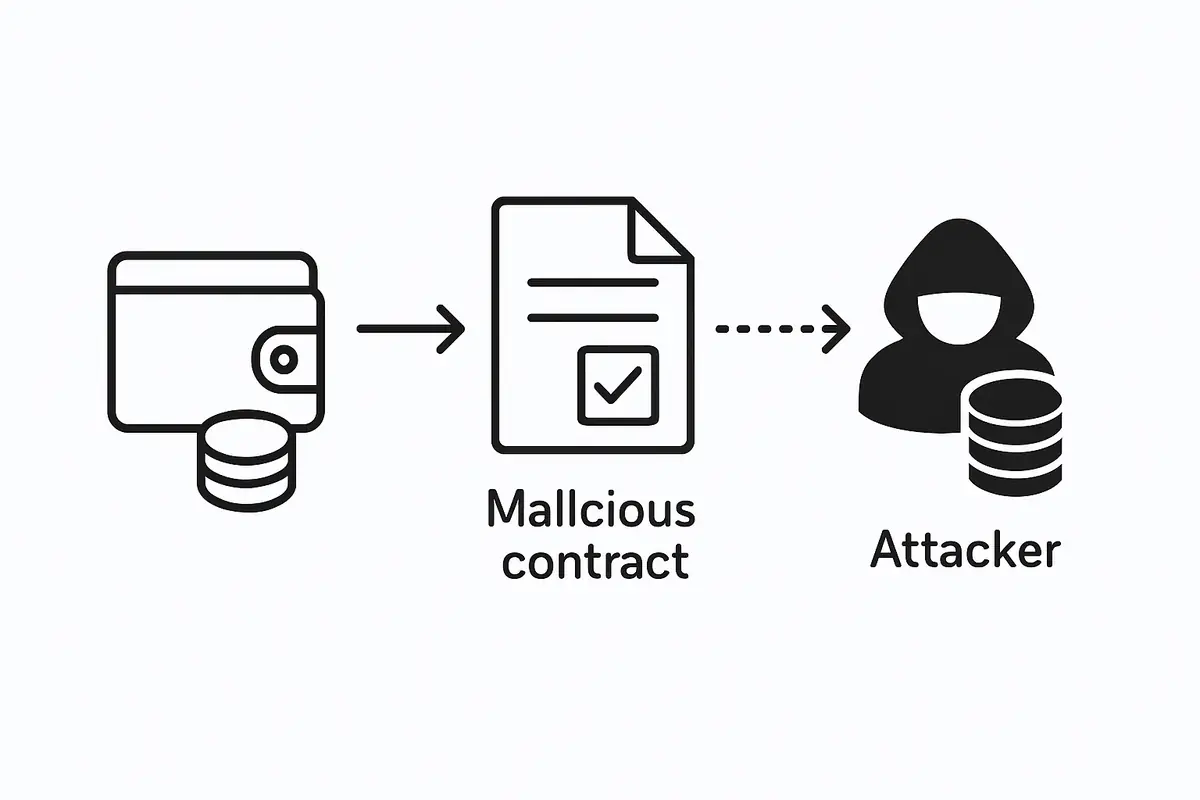
Approval Phishing (Token Drain Attacks)
DeFi wallets interact with smart contracts by signing approval transactions. A legitimate approval authorizes a specific contract to spend a specific token on your behalf up to a defined amount. An approval phishing attack tricks you into signing an unlimited approval for an attacker-controlled contract.
For a concrete hardware example, see Best Crypto Hardware Wallets: Security Ranking and Buyer Guide.
Once the unlimited approval is in place, the attacker can call the contract at any time to drain the approved tokens from your wallet, without needing your key or any further action from you. The approval sits on-chain permanently until you revoke it.
These attacks are delivered through fake airdrop sites, counterfeit DeFi interfaces, compromised official Discord announcements, and malicious links in NFT metadata. For a comparison between phishing and more technically complex drain attacks, see Phishing vs Smart Contract Drains.
One operator insight is that approval phishing usually feels routine right before it becomes expensive. The page looks familiar, the token is one you already hold, and the requested approval appears to be a normal DeFi step. That is why readable spender details and approval amounts matter more than the site’s visual polish.
How Attackers Deliver Attacks
- Search engine ads. Attackers pay for ads that appear above the real site in search results, directing users to convincing fakes.
- Email from spoofed addresses. Emails claiming to be from Ledger, Metamask, or other wallet brands with urgent action required.
- Compromised Discord channels. Official project Discord servers are regularly hacked to post malicious minting or airdrop links.
- Fake support DMs. Scammers monitoring wallet-related hashtags or forums reach out offering help with a “solution” that involves a malicious link.
- Malicious browser extensions. Fake versions of popular wallet extensions available on extension stores.
A second operator insight is that delivery channels often stack. A user may first see a fake search ad, then land on a polished copy of a real site, then get pushed into a rushed approval by a timer or a fake support message. Treating each stage as harmless on its own is how the full attack chain succeeds.
Practical Usage: Check Links and Approvals Before You Sign
A practical workflow is simple: if a wallet page comes from a search result, ad, DM, or Discord post, stop and reopen the destination from a saved bookmark or the project’s official site. Before approving anything, compare the domain carefully, confirm the app you expected to use, and read the spender and amount on the wallet or hardware wallet screen. If the approval is unlimited or the contract is unfamiliar, reject it and investigate before trying again.
For a closely related follow-up, see Exchange Withdrawals Will Pause Again.
A useful threshold routine is to split wallets by role. Keep one lower-value wallet for experiments, a separate wallet for serious on-chain activity, and a colder wallet that never connects to random links at all. That way one phishing mistake does not automatically expose the balances you intended to protect for the long term.
- Bookmark the real URLs for wallets and DeFi interfaces you use and always navigate from bookmarks rather than search results.
- Never enter a seed phrase into any website or browser extension under any circumstances.
- Read approval transactions carefully on the hardware wallet screen before confirming. Unlimited approvals (with very large amounts or “max uint256”) should be refused.
- Revoke active approvals regularly using tools like Revoke.cash or Etherscan’s token approval checker.
- Use a dedicated browser profile or device for high-value DeFi interactions.
A concrete scenario: if a Discord announcement suddenly promotes a “limited airdrop” and the page asks for wallet connection plus an unlimited token approval, the safe response is not to “double-check quickly.” It is to close the page, reopen the real project from your own bookmark, and confirm through official channels that the campaign exists at all. Phishing defense is mostly disciplined interruption of urgency.
Risks and Common Mistakes
The most dangerous mistake is speed. Attackers create urgency so users skip the verification step. Slowing down to check the URL, re-read the transaction details on the hardware wallet screen, or search for a second opinion breaks the attack loop.
Another common mistake is assuming a hardware wallet makes approvals safe. The hardware wallet signs whatever transaction the app presents. If the app is malicious or if the URL is a fake, the transaction details may look legitimate in the app but send funds to an attacker’s contract. The hardware wallet only helps if you read what is displayed on the device screen itself.
Frequently Asked Questions
Can a hardware wallet prevent approval phishing?
Only partially. A hardware wallet shows transaction details on its trusted screen. If you read the approval details there and notice an unlimited amount going to an unknown address, you can refuse. But if you sign without checking, the approval goes through regardless of the wallet type.
How do I know if I have malicious approvals on my wallet?
Connect your wallet address to Revoke.cash or the Etherscan token approval checker. These tools show all active approvals by token and spender. Revoke any approval from contracts you do not recognize or no longer use.
Are cold wallets safe from phishing?
Cold wallets protect against remote key extraction. But if a cold wallet user is phished into entering their seed phrase on a fake site or signs an approval transaction without reading the details, the cold wallet does not prevent the loss.
Can I recover funds after an approval drain?
No. Blockchain transactions are irreversible. Once an approval drain is executed, the funds are gone. The only action you can take is to revoke remaining approvals immediately and move remaining assets to a new wallet that has never been exposed.
How is wallet phishing different from exchange phishing?
Exchange phishing captures login credentials and may be reversed by the exchange if caught quickly (exchanges can freeze accounts). Wallet phishing captures keys or approvals and executes irreversible on-chain transactions. There is no customer support or reversal mechanism in self-custody wallets.