To reduce SIM swap risk in crypto, the most effective move is to stop depending on your phone number for important account security wherever you can. If your exchange, email, or recovery flows rely on SMS, your mobile carrier becomes part of your custody and identity stack. That does not mean a SIM swap is guaranteed. It means the blast radius is larger than most users realize.
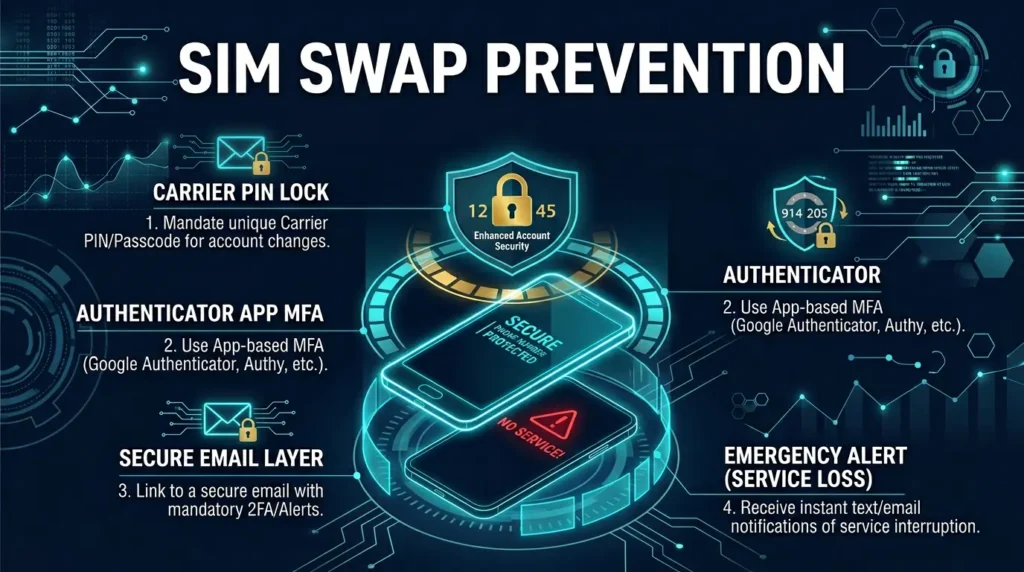
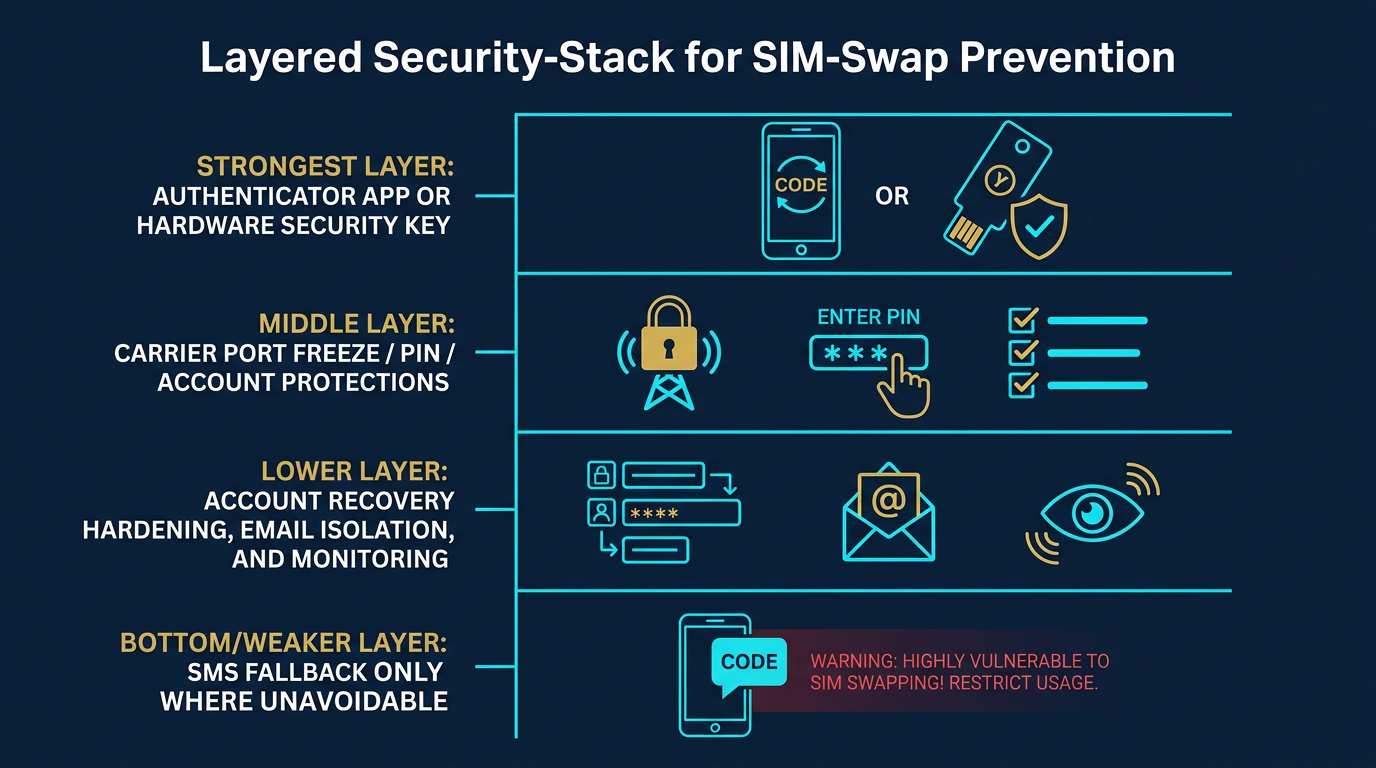
The practical goal is not to make your phone number invisible. It is to keep a phone-number takeover from turning into exchange access, email recovery, or fund movement. That means replacing SMS with stronger second factors where possible, hardening the carrier account itself, separating sensitive accounts from casual online exposure, and treating sudden service loss like a real security event.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- Move away from SMS where possible: Authenticator apps and security keys usually reduce exposure more than carrier-based codes.
- Your carrier account needs protection too: Account PINs, port-out locks, and added verification reduce easy takeover paths.
- Email deserves equal priority: If email can reset exchange access, protecting it is part of SIM-swap defense.
- Account separation matters: High-value accounts should not share the same casual recovery and contact setup as low-value accounts.
- Sudden service loss can be an emergency signal: Treat it as a possible security incident, not just as a connectivity problem.
Start With the Biggest Security Upgrade
The single most useful upgrade is to stop using SMS as the main second factor for meaningful crypto accounts when a stronger option exists. Authenticator apps usually reduce carrier dependence, and hardware security keys can be stronger still where supported. This does not make the account unattackable, but it does close one of the most common identity-layer routes, which is why SIM swaps feature prominently in breakdowns of how crypto gets stolen.
The best local foundation pages for this are What Is a SIM Swap Attack in Crypto?, What Is 2FA in Crypto?, and SMS vs Authenticator 2FA for Crypto.
Harden the Carrier Account Itself
If the phone number still matters to any important account, the carrier account needs its own defenses. Many providers offer some combination of an account PIN, extra identity verification, port-out protection, or other lock settings that make unauthorized SIM changes harder. The names vary by carrier, but the principle is the same: do not let phone-number transfer depend only on basic personal details that may already be exposed elsewhere.
Operator insight: users often spend more time choosing an authenticator app than reviewing the carrier account that can still undermine SMS recovery. If the number remains in the recovery chain, the carrier deserves real attention.
Protect the Email Behind the Exchange
For many users, the email account is the real control point. If the inbox can reset exchange passwords, approve recovery, or confirm withdrawals, then protecting email is part of preventing SIM-swap damage. A weak inbox can make a strong exchange setup less meaningful.
A practical rule is to secure the exchange email with at least the same seriousness as the exchange itself: strong unique password, stronger-than-SMS second factor where possible, and no casual reuse of that inbox across risky signups and low-value accounts.
Reduce Phone Number Dependence Across the Stack
- Remove SMS 2FA where stronger options exist: Especially for email and exchanges.
- Review recovery methods: Make sure phone-number recovery is not the automatic fallback everywhere.
- Check withdrawal and reset settings: Some platforms still rely on phone confirmation even when login 2FA is stronger.
- Avoid using one number as the universal recovery anchor: Centralized recovery creates concentrated failure risk.
The general goal is to keep number control from becoming account control. If the phone remains in the stack, reduce what the number alone can do.
Use Account Separation Intentionally
Not every service deserves the same identity setup. A high-value exchange account, the email that resets it, and any financial recovery channels should be treated differently from casual online accounts. Separation helps because it reduces the amount of personal context and reset authority attached to one number, one inbox, or one device path.
Real-world example: if the same phone number and inbox are tied to your exchange, social profiles, shopping sites, and random app signups, an attacker has more public context, more reset routes, and more support surfaces to exploit. The less central your main number is, the lower the blast radius if it is targeted.
What to Do If Your Phone Suddenly Loses Service
- Assume it could be security-related: Do not treat unexplained service loss as routine until proven otherwise.
- Contact the carrier immediately: Ask whether a SIM change, port request, or account change was made.
- Lock down email and exchange accounts fast: Change passwords and review recent access from a clean device.
- Check for password-reset or login alerts: Email and exchange notifications may show active takeover attempts.
- Reduce exposed balances if needed: If an account may already be compromised, act before the attacker finishes the recovery flow.
Speed matters here. A SIM swap is dangerous because the attacker may move quickly from number control into recovery and withdrawal attempts. Recognizing the warning sign early can make the difference between a contained incident and a successful takeover.
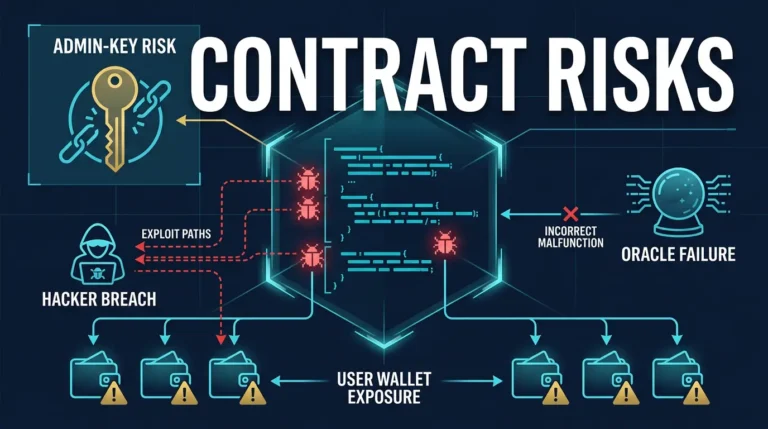
How This Fits Into the Bigger Threat Model
SIM-swap defense is part of account-security hardening, not a complete crypto-security system by itself. It protects against identity and recovery abuse around exchanges, email, and custodial apps. It does not replace phishing discipline, device security, or self-custody best practices.
For the broader attack-behavior side, Crypto Wallet Phishing Attacks and Exchange Custody Risks Explained are the best local companions.
Practical Usage: Best Prevention Checklist
A concrete setup looks like this: your exchange uses an authenticator app instead of SMS, the email behind the exchange also uses a stronger second factor, the carrier account has an account PIN or port-out lock enabled, and the phone number is no longer the automatic fallback for every recovery step. In that setup, taking over the number creates far less immediate leverage because the attacker still has to beat stronger controls upstream.
A practical emergency sequence also helps. If your phone loses service unexpectedly, call the carrier from another device, ask whether a SIM or port request was processed, change the email and exchange passwords from a clean device, and review whether password-reset messages or unfamiliar login alerts already appeared. That kind of response is useful because SIM-swap damage often comes from delay rather than from the number move alone.
A useful operator shortcut is this: the fewer critical actions your phone number can authorize, the less damage a number takeover can do.
Risks and Common Mistakes
- Keeping SMS as the main defense on high-value accounts: Better than nothing, but often weaker than the user assumes.
- Hardening the exchange but not the inbox: Recovery paths can be easier to exploit than the main login itself.
- Ignoring carrier controls: A strong account stack is weaker if the number can still be moved too easily.
- Using one number everywhere: Centralized identity creates wider blast radius in a takeover.
- Reacting too slowly to service loss: Attackers benefit from every minute the phone takeover is treated as a minor inconvenience.
Sources
- CISA: SIM Swapping and Personal Account Risk
- NIST Digital Identity Guidelines
- FBI IC3: Cryptocurrency Theft via SIM Swapping
Frequently Asked Questions
How can crypto users reduce SIM swap risk?
They can reduce it by moving away from SMS, hardening the carrier account, protecting email recovery, and reacting quickly to unexpected loss of service.
What is the best replacement for SMS on exchange accounts?
Authenticator apps are usually the best common upgrade, and hardware security keys can be stronger where supported.
Does a carrier PIN stop every SIM swap?
No, but it can make unauthorized number transfer harder by adding another check at the carrier layer.
Why does email matter in SIM swap prevention?
Email often controls password resets, alerts, and recovery for exchange accounts, so a weak inbox can undermine stronger exchange settings.
What should I do if my phone loses service unexpectedly?
Treat it as a possible security issue, contact the carrier immediately, and review important accounts for password-reset or takeover activity from a clean device.