Most crypto theft does not start with someone “hacking the blockchain.” It starts with an attacker finding a path to your credentials, your approvals, your device, or your judgment. The technical details vary, but the pattern is consistent: gain trust or access, get the user to reveal something or sign something, then move funds before the victim understands what happened.
The useful way to think about crypto theft is not as one giant category but as a handful of recurring attack paths. Some attacks steal secrets such as recovery phrases. Some abuse wallet permissions the victim signs willingly. Some compromise devices or online accounts. Others manipulate people directly through urgency, authority, or fake support. Knowing these categories helps you defend the correct weak point instead of relying on generic security advice.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- Most theft paths target the user, not the chain: Attackers usually steal credentials, approvals, sessions, or account access rather than breaking blockchain cryptography.
- Crypto theft often happens in stages: Delivery, trust-building, credential capture, signing, and fund movement are commonly separate parts of the same attack chain.
- Seed phrase theft and malicious approvals are different risks: One gives full wallet control; the other grants ongoing permission to drain specific assets.
- Device and account security still matter: Malware, browser compromise, and exchange account takeover remain major real-world loss paths.
- The best defenses are layered: Good wallet separation, cautious signing, strong account security, and slower decision-making protect different failure points.
The Main Theft Paths Attackers Use
A clear mental model is to treat crypto theft like a route map rather than a single trick. The attacker does not need every route. They only need one route that reaches something valuable. That route may go through your seed phrase, your wallet approvals, your browser, your exchange login, or your emotions. The destination is the same: control over assets.
Another useful mental model is that attackers usually look for the cheapest point of control. If your long-term wallet is secure, they may target your exchange login. If your exchange account is hardened, they may try to get you to sign a malicious approval. If you resist suspicious links, they may try fake support or malware instead. Security works best when you stop thinking in terms of one perfect tool and start thinking in terms of multiple doors that all need reasonable locks.
1. Seed phrase and credential theft
This is the most direct route. If an attacker gets your recovery phrase, private key, or exchange credentials, the security problem is largely over. They can restore the wallet, sign from it, or log into the account and begin withdrawals. The theft usually happens through fake wallet recovery pages, impersonated support, spoofed emails, counterfeit wallet apps, or credential-reset traps.
For the wallet-specific version of this, crypto wallet phishing attacks is the most relevant local follow-up. The important distinction is simple: legitimate services do not need your seed phrase to “verify,” “unlock,” or “repair” your wallet.
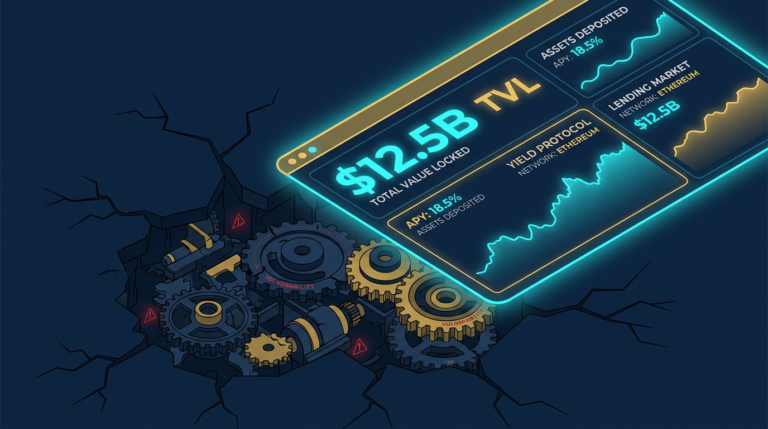
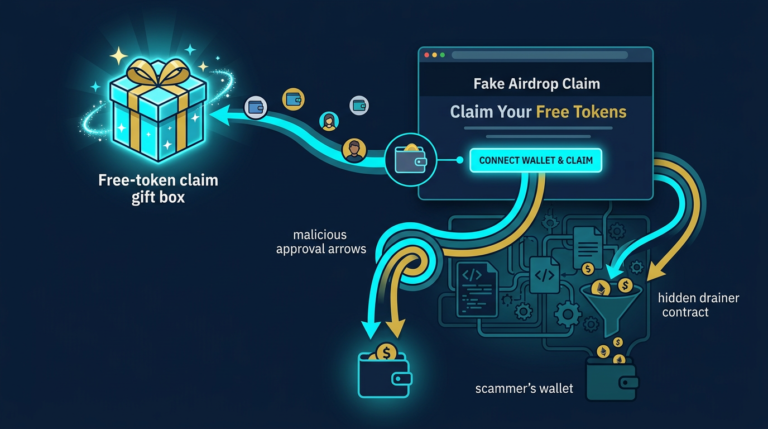
2. Malicious signing and wallet drainers
Not all theft requires stealing secrets. On EVM chains especially, attackers can trick users into signing approvals or permit-style messages that grant token access to malicious contracts. That is the mechanism behind many wallet drainers. The user keeps the keys, but the attacker gains authorized spending power over assets because the victim signed the wrong prompt.
One operator insight is that this path often feels safer than seed phrase theft right before the loss happens. The user thinks, “At least I did not reveal my recovery words.” But if the signed permission is broad enough, the practical result can still be a drained wallet. That is why approval review matters as much as password hygiene.
The best detailed reference here is What Is a Crypto Drainer?. For the overlap between deceptive links and malicious approvals, Phishing vs Smart Contract Drains explains the difference clearly.
3. Malware and device compromise
Sometimes the attacker targets the machine instead of the wallet flow. Malware can steal browser sessions, monitor clipboard activity, swap copied addresses, capture keystrokes, or search local files for wallet backups and exported keys. A compromised device can quietly bypass a lot of user caution because the attacker sees what the user sees and alters what the user thinks is normal.
Clipboard hijacking is a simple example: you copy a legitimate wallet address, but malware replaces it with the attacker’s address before you paste. The transfer looks routine until it settles to the wrong destination. More advanced malware targets browser extensions, saved credentials, or developer machines that have access to treasury systems and deployment keys.
A second operator insight is that device compromise can turn small habits into big exposure. Downloading random extensions, mixing personal browsing with high-value wallet use, or treating a general-purpose laptop as a custody device all widen the attack surface long before the theft becomes visible.
4. Social engineering and impersonation
Many attacks begin with persuasion rather than code. Fake support agents, romance scams, recruiter lures, impersonated founders, and urgent “security alerts” all work by moving the victim into a rushed decision environment. Once the attacker has enough trust, they can route the victim toward phrase entry, malicious signing, remote-access software, or fraudulent investment deposits.
This is why social engineering in crypto overlaps with almost every other attack type. Social engineering is often the delivery layer that gets the victim to cooperate with the real theft mechanism.
5. Exchange account takeover
Crypto also gets stolen through centralized accounts. If an attacker compromises your exchange login, email, or SMS-based recovery path, they may not need your wallet at all. They can reset passwords, bypass weak two-factor setups, sell assets, and withdraw funds to addresses they control. SIM swapping and email compromise are especially relevant here because many users still rely on them for account recovery.
This is one reason long-term holdings are better protected in self-custody setups designed for storage rather than convenience. But self-custody only helps if the user also protects the device, recovery process, and signing habits around it.
How Attack Chains Usually Work in Practice
Most real theft incidents are chains, not single events. A user sees a fake ad, lands on a cloned site, connects a wallet, signs a malicious approval, then later discovers assets missing. Or a victim answers a fake support DM, installs remote-access software, logs into an exchange, and loses access within minutes. Looking only at the final step can make the incident seem random. Looking at the full chain reveals where the defense failed first.
That is why the most accurate summary is not “hackers stole my crypto out of nowhere.” In most cases, attackers either captured something secret, abused something authorized, or took over an environment the user depended on. The chain may have been sophisticated, but the path still fits one of those categories.
Practical Usage: How to Reduce the Biggest Theft Paths
The right defensive workflow is to match your habits to the attack path. Different risks need different controls. A hardware wallet helps against remote key theft, but not against careless signing. Strong exchange security helps against account takeover, but not against fake wallet recovery forms. Good security is less about one product and more about putting the right friction in the right place.
- Protect recovery information absolutely: Never type a seed phrase into a website, DM workflow, or “support” form. Store it offline and treat any request for it as an attack.
- Review wallet prompts like money movement: Check spender, amount, destination, and contract purpose before signing. If the action is unclear, reject it.
- Separate wallets by role: Use one wallet for long-term storage, a different one for active DeFi, and a smaller one for experiments or unknown links.
- Harden exchange accounts: Use strong unique passwords, app-based or hardware-key MFA, and a locked-down email account with its own strong security.
- Reduce device exposure: Keep high-value wallet activity away from random downloads, unnecessary browser extensions, and mixed-use devices.
A practical operator routine is to ask one question before every sensitive action: “What exactly could this step give away if it is malicious?” If the answer is “my full wallet,” “my exchange account,” or “ongoing token access,” stop and verify outside the original channel. That pause interrupts a remarkable number of attack chains.
For the more specific wallet-side defenses behind this overview, the best follow-ups are token approval risks, fake airdrop scams, and fake wallet apps explained.
Risks and Common Mistakes
- Assuming theft always looks technical: Many large losses begin with ordinary-looking messages, support chats, or login workflows rather than obvious “hacker” behavior.
- Using one wallet for everything: Combining storage, experimentation, and daily use in one place raises the cost of any single mistake.
- Trusting familiar interfaces too quickly: A polished app, known logo, or realistic site layout is weak evidence of legitimacy.
- Underestimating device and account hygiene: Browser security, email security, and MFA choices directly affect crypto loss risk.
- Trying to solve every risk with one tool: No wallet, exchange, or app can fully compensate for weak verification habits across all attack paths.
Sources
- FBI: Operation Level Up
- FBI IC3: North Korea Aggressively Targeting Crypto Industry with Well-Disguised Social Engineering Attacks
- Chainalysis: Understanding Crypto Drainers
- FBI: Internet Crime Report
Frequently Asked Questions
What is the most common way crypto gets stolen?
Common theft paths include seed phrase phishing, malicious wallet approvals, exchange account takeover, and social engineering that pushes users into unsafe actions. The exact route varies, but most losses come from stolen credentials, abused permissions, or compromised accounts rather than broken blockchain security.
Can hackers steal crypto without my seed phrase?
Yes. Attackers can steal through malicious approvals, exchange login compromise, SIM swapping, browser malware, remote access, and other account-takeover paths. A seed phrase is one high-value target, but it is not the only route to loss.
Do hardware wallets stop all crypto theft?
No. Hardware wallets are very useful against remote key theft, but they do not protect against every attack type. They cannot fully protect you from fake support scams, exchange account compromise, or malicious approvals if you sign without verifying what is on the trusted screen.
Because convincing a user to cooperate is often easier than breaking technical security. Social engineering creates trust, urgency, or confusion that leads the victim into revealing credentials, signing approvals, or weakening their own defenses.
What is the best first defense against crypto theft?
The best first defense is layered verification: protect recovery information, slow down before signing, separate wallets by role, harden exchange and email accounts, and avoid treating any unexpected request as routine. The more valuable the action, the more independent verification it should require.