A bridge in crypto is a system that lets users move value or messages between blockchains that do not natively share state. If you want to use an asset from one chain on another chain, the chains cannot simply “see” each other and update balances directly. A bridge provides the extra verification layer that interprets what happened on chain A and causes an appropriate action on chain B.
The simplest way to think about a bridge is that it is not a teleportation tunnel for coins. It is an accounting system that tries to keep two chains in sync about who should control value after a cross-chain action. That distinction matters because the bridge itself becomes a trust and security layer, not just a neutral convenience tool.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- A bridge connects chains that do not natively trust each other: It provides the proof or coordination needed to represent value across networks.
- Assets usually do not literally move between chains: They are often locked, burned, minted, released, or represented in a wrapped form.
- Bridges add a new trust layer: Users depend not only on the destination chain but also on the bridge’s contracts, validators, relayers, or liquidity design.
- Different bridge models have different risks: Lock-and-mint, burn-and-release, and liquidity-routing designs do not fail in the same way.
- Bridge risk is infrastructural: Even with a secure wallet, a weak bridge can still expose your funds or leave you holding impaired wrapped assets.
Why Bridges Exist
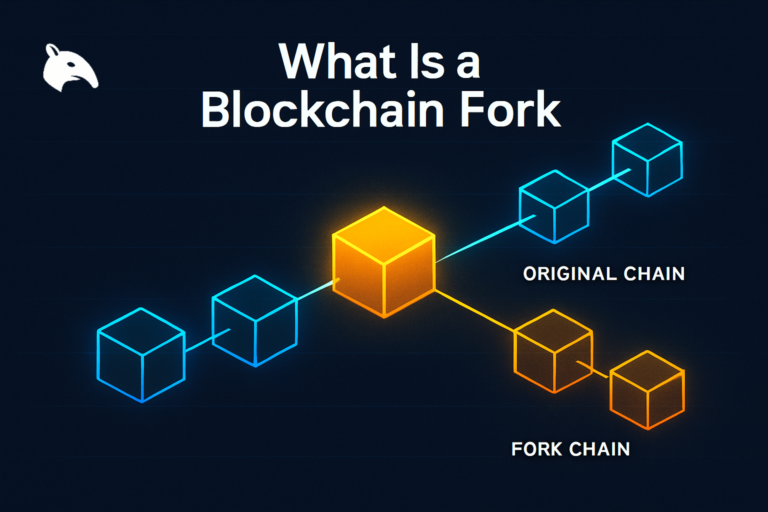
Blockchains are separate systems. Bitcoin does not natively track Ethereum balances. Ethereum does not automatically know what happened on Solana. That separation is part of why these networks can remain independently verifiable, but it also means assets and applications are fragmented across ecosystems.
Bridges exist because users want to move activity between those ecosystems. They may want to use BTC-derived liquidity on another chain, move stablecoins into a lower-fee environment, or shift capital to a new application that only exists elsewhere. A bridge tries to make that cross-chain movement possible without requiring the underlying chains to merge into one system.
A useful mental model is to think of a bridge like a warehouse receipt system. You deposit something valuable into secure storage, then receive a receipt that can be used elsewhere. The receipt is useful only because people trust that the original value is really locked and redeemable. If that trust breaks, the receipt can stop being worth what users assumed.
How a Bridge Actually Works
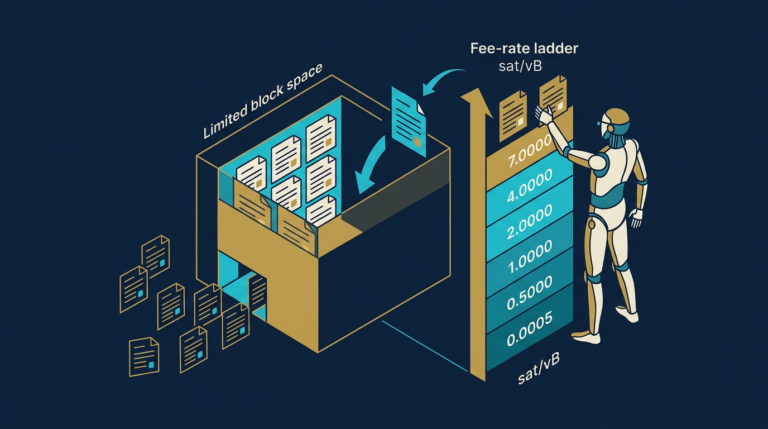
Most bridges do not move the original token itself from one chain to another. Instead, they observe an event on the source chain and create or release a corresponding claim on the destination chain. That process can involve smart contracts, validator signatures, relayers, multisigs, or liquidity pools.
The key point is that a bridge must answer one hard question: how can chain B trust that something really happened on chain A? Everything else in bridge design flows from that question.
Lock-and-mint
In a lock-and-mint model, the original asset is locked on the source chain and a wrapped version is minted on the destination chain. For example, a bridge may lock tokens in a contract on one network and issue a corresponding wrapped token on another. The wrapped token is valuable only if users believe it is truly backed by the locked original.
Burn-and-release
In a burn-and-release model, the wrapped version on one chain is destroyed so that the original locked asset can be released back on the other chain. This is effectively the reverse path of a lock-and-mint design. The bridge must verify that the burn really happened before releasing value.
Liquidity-routing models
Some bridges use liquidity pools rather than minting wrapped assets. In that model, users deposit on one side and receive funds from pre-positioned liquidity on the destination side. This can feel faster and simpler, but it introduces liquidity-management and routing assumptions in addition to verification risk.
Wrapped Assets and Representation Risk
When users bridge value, what they receive on the destination chain is often not the original native asset. It is a representation of that asset under the bridge’s trust model. That may be a wrapped token, a bridge-specific version, or liquidity paid out from another pool.
This matters because representation is not the same thing as native issuance. A wrapped token can trade below par if users lose confidence in the bridge backing it. The practical risk is not just theft. It is also impaired redeemability, route shutdowns, and uncertainty about whether the claim is still fully backed.
One operator insight is that many users judge destination assets by ticker symbol alone. That is a mistake. A token that looks familiar may still be a bridge-specific wrapped version with very different trust assumptions from the native asset users think they own.
Why Bridges Introduce Extra Risk
A normal transfer within one chain relies on that chain’s own consensus and validation rules. A bridge transfer relies on those rules plus the bridge’s own proof system. That added layer is why bridge risk is different from ordinary wallet or exchange risk.
Some bridges rely on validator or guardian sets. Others rely on multisig signers, message verifiers, or specialized relayer infrastructure. Each model has a different trust surface. If the proof system can be tricked, if keys are compromised, or if the route is badly managed, value on the destination side can become unbacked or inaccessible.
A second mental model helps here: a bridge is like adding a customs checkpoint between two countries that use different legal systems. The checkpoint has to inspect what is coming through and decide whether the receiving country should honor it. If the checkpoint is weak, corrupt, or confused, the whole transfer process becomes unsafe no matter how strong the countries are on their own.
Common Bridge Designs and Trust Assumptions
- Validator-based bridges: Trust depends on the honesty and key security of the validator or guardian set.
- Multisig-controlled bridges: Trust depends on how many signers exist, how keys are stored, and how easy signer compromise would be.
- Light-client or proof-based bridges: Trust depends more on on-chain verification logic and less on a small signer group, but technical complexity can still be high.
- Liquidity network bridges: Trust depends on available liquidity, route management, and the parties coordinating payouts on the destination chain.
No design removes trust entirely. The practical question is where the trust sits, how visible it is, and what happens if it fails.
How Users Experience a Bridge
From the user’s point of view, a bridge often looks simple: connect wallet, choose source chain, choose destination chain, select token, confirm. Underneath that clean interface, the system may be locking collateral, broadcasting cross-chain messages, waiting for finality, routing through liquidity, and issuing a wrapped token with its own contract address.
This gap between interface simplicity and infrastructure complexity is why bridges are often misunderstood. A user may believe they are doing something as straightforward as a normal transfer, when in reality they are interacting with a multi-step trust system that has its own failure modes and operational dependencies.
Practical Usage: How to Use Bridges More Carefully
You do not need to become a bridge auditor to use them more safely, but you do need to treat them as infrastructure rather than as neutral plumbing. The goal is to reduce surprise if the route, wrapped asset, or operational status is not as simple as the interface suggests.
- Check what asset you will receive: Verify whether the destination token is native, wrapped, canonical, or bridge-issued.
- Use small test transfers first: Confirm the route, destination chain, and asset behavior before moving larger amounts.
- Check route status and official links: During incidents, fake bridge recovery pages and phishing links often appear.
- Understand the trust model at a basic level: Know whether the bridge relies on signers, validators, contracts, or liquidity pools.
- Avoid treating bridged assets as risk-free equivalents: A wrapped asset can carry different redemption and counterparty assumptions from the native version.
A practical operator routine is to ask two questions before bridging: “Who is verifying this cross-chain action?” and “What exactly will I hold on the other side?” If either answer is unclear, the transfer is not yet simple enough to trust with size.
Risks and Common Mistakes
- Assuming assets literally move chains: In many cases, users are receiving a representation or liquidity payout, not the original native asset.
- Ignoring wrapped-asset risk: A familiar ticker does not guarantee native backing or equal trust assumptions.
- Treating the bridge like a normal transfer: Cross-chain movement adds a new infrastructure layer with its own failure modes.
- Skipping test transactions: Errors in route selection, token choice, or destination chain become much more expensive at full size.
- Underestimating operational risk after incidents: Even if a UI is live again, redemption, liquidity, and backing assumptions may still be impaired.
Sources
Frequently Asked Questions
What is a bridge in crypto?
A bridge in crypto is a system that lets users move value or messages between separate blockchains by adding an extra verification or coordination layer. It helps one chain recognize an event that happened on another.
Do tokens really move from one chain to another?
Usually not in a literal sense. Many bridges lock or burn an asset on one chain and mint, release, or route a corresponding representation on another chain.
What is a wrapped asset?
A wrapped asset is a token on one chain that represents an asset locked or backed elsewhere. Its value depends on trust that the backing and redemption mechanism still works as intended.
Why are bridges considered risky?
Because they introduce extra trust assumptions, contracts, validators, signers, or liquidity systems beyond the base chains themselves. If that added layer fails, users can face theft, delays, depegging, or failed redemptions.
How can I use a bridge more safely?
Check the asset you will receive, use small test transfers, verify official routes, understand the basic trust model, and avoid assuming a wrapped token is identical to the native asset in every risk scenario.