Last Updated on April 16, 2026 by Snout0x
Cross-chain bridge hacks are not random bad luck. They are a predictable result of trying to move value between blockchains that do not natively trust each other. A bridge has to prove that assets locked or burned on one chain justify releasing or minting assets on another. That extra verification layer becomes a rich target because it concentrates funds, trust assumptions, and complex code in one place.
For users, the risk is easy to underestimate. A bridge often looks like a convenient swap form with a destination chain selector, but under the surface it may depend on validator signatures, message relayers, smart contracts, wrapped assets, liquidity pools, or admin keys. If any of those pieces fail, the result can be delayed withdrawals, broken wrapped assets, or outright loss. That is why bridge incidents have repeatedly become some of the largest hacks in crypto.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- Bridges create a new trust layer: They do not magically move coins between chains; they rely on verification systems that can fail, be exploited, or be misconfigured.
- Attackers target the weakest bridge component: That may be smart-contract logic, validator keys, message verification, or operational controls around upgrades and admins.
- User losses are not always immediate theft: A bridge failure can also leave users stuck with wrapped assets, delayed redemptions, or frozen funds on the destination chain.
- Bridge risk is different from wallet risk: Even if your wallet is secure, the protocol moving value between chains can still break underneath you.
- Safer bridge use is procedural: Small test transfers, chain verification, token verification, and bridge selection matter more than convenience or hype.
Why Bridges Keep Becoming High-Value Targets
A bridge is valuable to attackers for the same reason a central bank vault is valuable: it holds or controls a lot of transferable value in one place. Many bridges custody large pools of assets on the source chain while issuing wrapped or mirrored representations on the destination chain. That means a successful exploit can let an attacker mint unbacked assets, drain locked collateral, or bypass message verification and withdraw funds without a legitimate deposit on the other side.
Bridges also sit at the intersection of multiple systems. They may combine smart contracts, validator networks, relayers, liquidity managers, off-chain services, and admin controls. Each additional layer is another place where assumptions can break. Even if the code on one chain is strong, weak key management or flawed message validation elsewhere can still compromise the whole system.
Bridges aggregate complexity and funds at the same time
Most DeFi protocols only have to protect assets on one chain and within one set of consensus rules. A bridge has to protect value while translating state across two or more chains with different architectures and finality assumptions. That translation is exactly where risk multiplies. The system must decide which deposits are real, when they are final, who signs off on them, and how the destination side should respond.
One operator insight is that bridge design is often judged by speed and token support, while the real question should be how much additional trust the bridge introduces. Fast user experience can hide a deeply centralized validator set or a fragile relayer path. The easier the interface looks, the more important it is to ask what machinery is carrying the risk behind it.
How Bridges Actually Move Value Across Chains
Most users talk about “moving” tokens between chains, but the token itself usually does not travel. A simple mental model is to think of a bridge as a warehouse receipt system, not a teleportation tunnel. On the source chain, value is locked, burned, or escrowed. On the destination chain, a new claim is issued or released based on proof that the first action really happened. If the proof system is weak, the destination chain can be tricked into releasing value it should not release.
Lock-and-mint and burn-and-release models
In a lock-and-mint model, your original asset is locked on chain A and a wrapped version is minted on chain B. In a burn-and-release model, a wrapped asset on chain B is destroyed so the original can be released on chain A. Both models require trustworthy proof that the first step happened correctly. If the system validates fake messages or compromised signatures, it can mint or release assets without real backing.
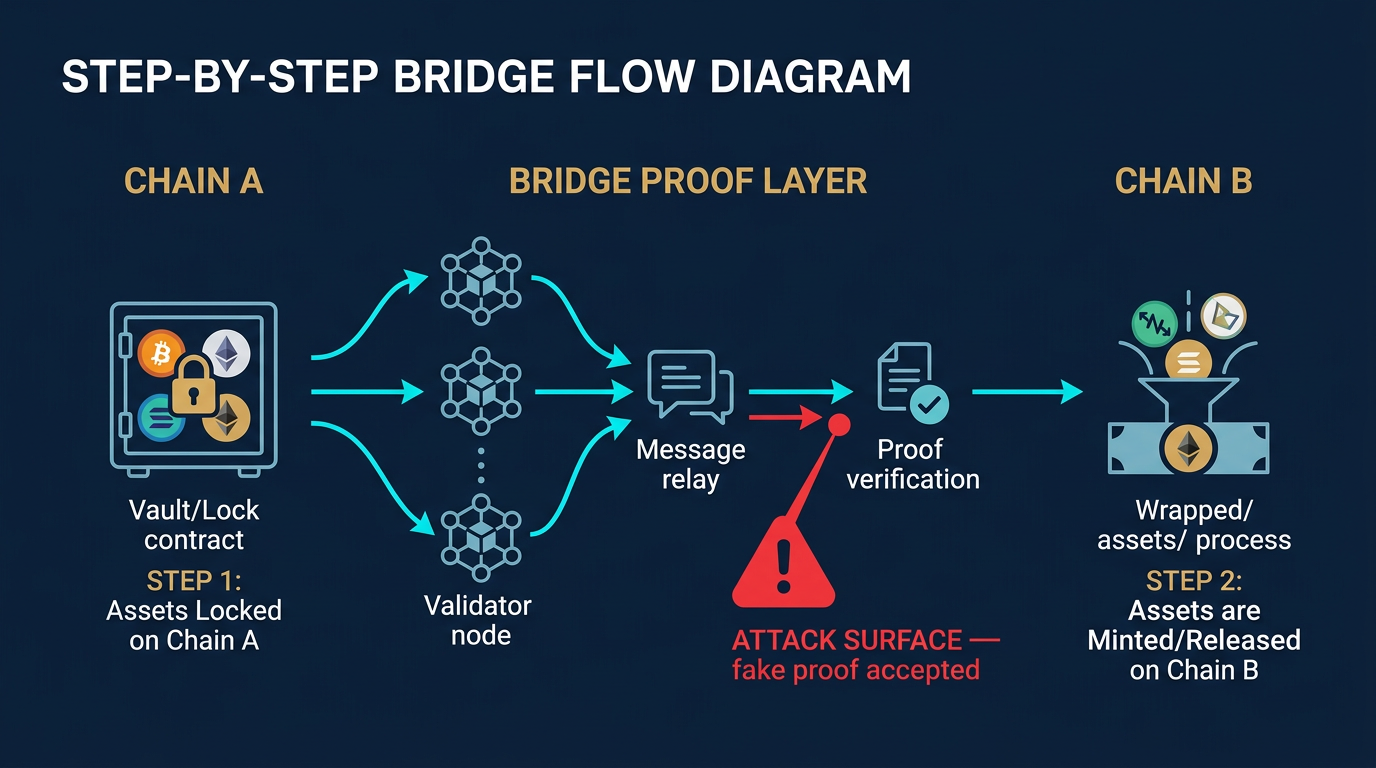
This is why bridges differ from simple wallet transfers. When you send coins inside one chain, the network itself verifies the transaction. With a bridge, an extra system must interpret one chain’s state and convince another chain to act on it. That extra interpreter is the attack surface.
Validator, multisig, and messaging assumptions
Some bridges rely on a validator or guardian set that signs messages confirming deposits. Others use multisig-controlled releases, light-client verification, or liquidity-pool routing. The security question is always the same: who decides that the cross-chain message is valid, and what happens if that party or mechanism is wrong? In many historic exploits, the attacker did not need to break both chains. They only needed to break the bridge’s proof layer.
A second operator insight is that bridges often inherit the weakest combination of their own logic plus the chains they connect. If one side has slower finality, thin monitoring, or unreliable infrastructure, the bridge can become operationally fragile even before any explicit exploit occurs. Users who treat bridges like neutral plumbing miss the fact that they are really trust systems with their own failure modes.
Where Bridge Exploits Usually Happen
Bridge hacks rarely come from one universal bug. They usually arise from one of a few recurring categories: bad verification logic, compromised validator keys, flawed upgrade paths, broken liquidity controls, or operational mistakes around privileged access. Understanding those categories matters more than memorizing brand names from past incidents because the pattern is what repeats.
Message verification and smart-contract bugs
If the bridge contract incorrectly verifies deposit proofs, signatures, Merkle roots, or message authenticity, an attacker may be able to fabricate a transfer event that never happened. That can allow unbacked minting or unauthorized withdrawals. These bugs are especially dangerous because they can bypass the entire economic model of the bridge. Once false messages are treated as valid, the system can create claims on assets that were never legitimately locked.
This category overlaps with the broader risks described in phishing vs smart contract drains, but bridge exploits are more infrastructural. The target is not usually your personal wallet first. It is the protocol layer deciding whether a cross-chain event is real.
Validator or multisig key compromise
Many bridges depend on a set of validators, guardians, or multisig signers. If enough of those keys are compromised, the attacker can approve fraudulent releases or messages without needing a code bug at all. This is one reason bridge incidents sometimes look more like treasury compromise than pure contract exploitation. The bridge may have sound logic, but the human or operational layer controlling signatures becomes the real weak point.
From a user perspective, this means security cannot be judged from audits alone. A bridge may be well-reviewed in code terms yet still rely on a centralized or poorly protected signer set. If the protocol cannot clearly explain its validator model and key-management assumptions, you should treat that opacity as risk rather than as a missing detail you can safely ignore.
Liquidity, wrapped-asset, and upgrade failures
Not every bridge problem is a dramatic theft. Some failures leave users holding wrapped tokens that no longer redeem cleanly because the backing pool is impaired, the route is paused, or the bridge contract has been upgraded badly. In other cases, the bridge itself survives but the destination asset becomes hard to trust because nobody knows whether it remains fully backed. That creates a quieter but still expensive form of loss.
These problems become more dangerous when users move quickly into downstream DeFi positions. If you bridge assets and immediately use them as collateral, liquidity, or yield capital, a bridge incident can spread into liquidations or forced exits elsewhere. In that sense, bridge risk is often upstream risk that later shows up as portfolio damage in places that seemed unrelated.
What Users Actually Experience During a Bridge Incident
From the outside, bridge hacks are often discussed like technical autopsies. From the user’s perspective, they feel like stuck transactions, missing balances, and uncertainty about whether the destination asset is still worth par. That distinction matters because good security decisions depend on recognizing operational symptoms early, not just understanding the code after the fact.
Pending transfers, paused routes, and broken assumptions
During a bridge incident, the first visible sign may be a paused UI, a transfer that remains pending far longer than normal, or an announcement that certain routes are disabled. The dangerous instinct is to keep retrying with larger amounts or alternative interfaces before you understand what failed. A bridge can be partially operational and still unsafe if the underlying wrapped asset, relayer path, or redemption guarantee is in doubt.
This is also where phishing risk returns. After a bridge incident, fake claim portals and fake support pages often appear, much like the patterns covered in crypto wallet phishing attacks. Users who are already stressed by a missing transfer are more likely to approve emergency transactions, enter seed phrases, or trust unofficial recovery instructions.
The damage can continue after the exploit headline
Even after the main exploit is public, users can still be harmed through depegging wrapped assets, liquidity evaporation, or bad follow-up actions. Someone who bridged to use funds immediately may discover that the received token is no longer accepted at full value. Another user may bridge back into the same route too quickly because they assume the issue is contained. Headlines make exploits visible; they do not automatically make the system safe again.
That is why bridge incidents should be treated like infrastructure failures, not isolated trading opportunities. If you are evaluating whether to use a route after a recent hack, the burden of proof should be on the bridge to demonstrate restored security and liquidity, not on the user to assume normal operations have resumed.
Practical Usage: How to Reduce Bridge Risk Before You Move Funds
The most effective defense is procedural discipline. You usually cannot audit a bridge yourself, but you can avoid the habits that turn a manageable bridge risk into a portfolio-level mistake. Good bridge usage is less about finding a perfect protocol and more about narrowing blast radius before anything goes wrong.
- Check what you are actually receiving: Confirm whether the destination asset is canonical, wrapped, or dependent on a specific bridge issuer before assuming it is equivalent to the source-chain asset.
- Start with a small test transfer: Verify the route, destination chain, wallet address, and final asset format with a small amount before sending meaningful value.
- Do not bridge your whole working balance at once: Split large transfers into stages so a route failure, wrong network choice, or pause does not trap everything at the same time.
- Verify approvals and destination wallet details: Some bridge UIs require token approvals on the source side. If that workflow looks unfamiliar, stop and review the risks covered in crypto approval scams before signing.
- Know your exit plan on the destination chain: The bridge step is only part of the operation. Confirm that your destination wallet, gas token, and downstream protocol assumptions are already prepared.
A practical operator habit is to settle bridged funds into a safer storage tier once the move is complete rather than leaving them exposed in the same hot wallet you used for the transaction. If the destination chain was only needed for one task, move the remaining balance back into the broader structure you would normally use for custody. The framework in how to store crypto safely matters here because bridge risk and wallet risk compound when funds are left in improvised setups after the transfer.
Another strong rule is to avoid using a bridge simply because social media says a new chain is where the action is. Hype-driven bridging is one of the easiest ways to ignore route quality, token verification, and destination liquidity. If you cannot clearly explain why the transfer needs to happen and what asset you should end up with, the move is not ready.
Risks and Common Mistakes
- Treating bridges like simple wallet sends: A bridge transfer introduces new trust assumptions that do not exist in a normal same-chain transaction.
- Ignoring the destination asset format: Users often assume the bridged token is identical in risk and redeemability to the original asset when it may depend on a specific bridge issuer.
- Sending size before sending a test: A single wrong route, paused bridge, or destination mistake is much easier to fix with a small trial amount than with a treasury-sized move.
- Overlooking approval and phishing risk: Bridge interfaces can ask for token approvals, and incident periods attract fake support sites and recovery scams.
- Stacking bridge risk with downstream leverage: Bridged funds that are immediately used as collateral or liquidity can create losses far beyond the initial bridge problem.
Sources
- Chainlink Documentation: Cross-Chain Bridges and Associated Risks
- Ethereum.org: Bridges
- Coinbase: Nomad Bridge Incident Analysis
FAQ: Cross-Chain Bridge Hacks
Why do cross-chain bridges get hacked so often?
Bridges are frequent targets because they combine large pools of value with complex verification systems. Attackers only need to break the bridge’s trust layer, such as message verification, validator keys, or contract logic, rather than compromise both blockchains directly.
Can a bridge hack affect users even if their wallet is secure?
Yes. A secure wallet protects your keys, but it does not protect you from a compromised bridge protocol. If the bridge itself fails, users can still face stuck transfers, bad wrapped assets, delayed redemptions, or protocol-level loss.
Are bridged tokens always the same as native tokens?
No. Many bridged assets are wrapped claims that depend on the bridge’s custody, liquidity, and redemption model. If the bridge fails, the wrapped asset may trade below face value or become difficult to redeem.
What is the safest way to use a bridge?
The safer approach is to bridge only when necessary, send a small test amount first, verify the exact destination asset and wallet, keep the transfer size limited, and avoid signing unfamiliar approvals during rushed or hype-driven conditions.
Should you avoid bridges entirely?
Not necessarily. Bridges are useful infrastructure, but they should be treated as higher-risk operations than normal same-chain transfers. The decision should depend on whether the move is necessary, how much value is involved, and whether you understand the route’s trust assumptions.