Last Updated on April 14, 2026 by Snout0x
Mobile wallet security is no longer optional in 2026. As crypto adoption expands, smartphones have become the primary operating system for retail investors. Portfolio tracking, token swaps, NFT approvals, staking, and cross-chain transfers now happen from the same device used for messaging and social media.
This content is for educational purposes only and should not be considered financial or investment advice.
This convergence creates efficiency.
It also concentrates risk.
Last Updated: January 29, 2026 Author: Snout0x
⚠️ DISCLAIMER: I am not a financial advisor. This is not financial advice (NFA). I am just a guy in the trenches trying to stop you from donating your life savings to a hacker in North Korea. Do your own research.
Affiliate Disclosure: Some links in this article may be affiliate links. If you choose to use them, I may earn a commission at no additional cost to you.
New to crypto? Start here: [ Best Crypto Wallets for Beginners 2026: Safe, Easy & Verified].

Delete These Apps: 5 Mobile Wallet Risks Draining Accounts
Introduction
Unlike traditional financial systems, cryptocurrency transactions are final once confirmed on-chain. There is no centralized reversal authority, no fraud desk, and no dispute resolution mechanism capable of undoing a broadcast transaction.
This means operational mistakes and security failures have asymmetric consequences.
In 2026, as multi-chain ecosystems grow and social engineering tactics become more sophisticated, mobile wallet security is no longer optional knowledge. It is foundational self-custody hygiene.
This guide breaks down five critical mobile wallet risks, explains why they work, and outlines practical mitigation strategies appropriate for beginner to intermediate investors.
Hot Wallet vs. Cold Wallet: Know the Difference
Understanding exposure begins with architecture.
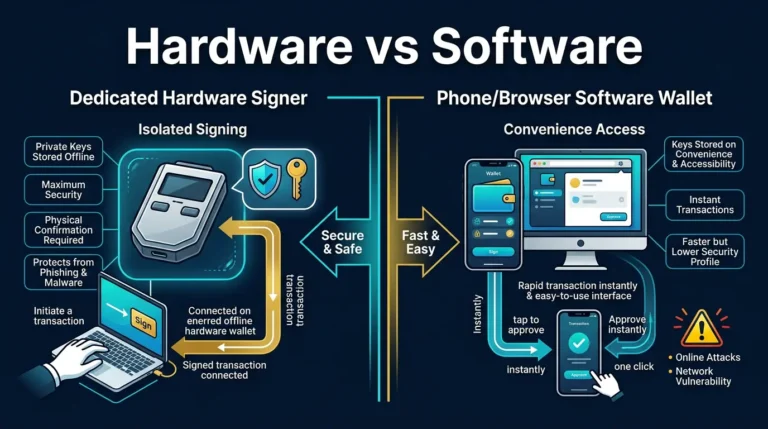
A hot wallet is connected to the internet. Mobile wallets, browser extensions, and exchange-hosted wallets fall into this category.
A cold wallet (hardware wallet) stores private keys offline and requires physical confirmation to authorize transactions. See our guide
Why This Distinction Matters
Hot wallets:
- Continuously interact with internet-connected environments
- Approve smart contracts
- Sign transactions in real time
- Interface with multiple third-party applications
Cold wallets:
- Isolate private keys from online environments
- Require physical device interaction
- Reduce exposure to remote exploits
- Limit attack surface significantly
The core security principle here is attack surface minimization.
A mobile device is:
- Constantly connected
- Running multiple apps
- Receiving background updates
- Handling notifications and messages
Each of these layers introduces complexity and potential vulnerability.
Cold storage does not eliminate risk entirely, but it removes persistent internet exposure which statistically reduces catastrophic loss probability.
If you are storing long-term holdings on a mobile device, you are prioritizing convenience over containment.
Understanding hot versus cold architecture is a core principle of mobile wallet security.
For a deeper explanation, see:
Understanding Cold Storage: Hot vs. Cold Wallets Explained
Most failures in mobile wallet security occur at the intersection of convenience and exposure.
Risk #1: SIM Swap & Account Recovery Exploits
SIM swap attacks remain one of the most financially damaging attack vectors in crypto, as documented in the latest FBI Internet Crime Report.
A SIM swap occurs when an attacker convinces your mobile carrier to transfer your phone number to a SIM card under their control. This can happen through:
- Social engineering of support staff
- Exploiting weak identity verification
- Insider corruption
- Data obtained from prior breaches
Once successful, attackers can:
- Intercept SMS-based authentication codes
- Reset email passwords
- Initiate exchange account recovery
- Disable security notifications
- Lock users out of accounts
Why This Works
Many platforms treat possession of a phone number as identity verification.
If your email uses SMS recovery and your exchange uses email-based password resets, control of your phone number becomes equivalent to control of your digital identity.
This attack bypasses cryptographic security entirely. It exploits human systems.
Secondary Risk: Cascading Account Compromise
SIM swaps often begin with email compromise.
Once attackers control your primary email, they can:
- Reset exchange credentials
- Access cloud backups
- Retrieve stored documents
- Change recovery options
Crypto security is only as strong as the weakest recovery layer.
How to Reduce This Risk
- Replace SMS 2FA with hardware-based authentication keys.
- Enable SIM lock or port freeze with your carrier.
- Remove phone numbers as recovery methods when possible.
- Secure email accounts with hardware authentication and unique passwords.
- Use a dedicated email for financial accounts.
The goal is to eliminate dependency on telecom-based identity verification.
Risk #2: Malicious Apps & Address Poisoning
Modern smartphones run dozens of applications, many with elevated permissions.
Clipboard hijacking malware monitors copied wallet addresses and substitutes attacker-controlled lookalike addresses.
More advanced variants involve “address poisoning,” where attackers send small transactions from visually similar addresses to populate your transaction history.
Why This Works
Wallet addresses are long and difficult to verify manually. Most users:
- Check only the first few characters
- Check only the last few characters
- Rely on memory
- Rush during transactions
Attackers generate vanity addresses matching visible edges to increase success probability.
In multi-chain ecosystems, this risk multiplies due to similar token tickers across networks.
Behavioral Vulnerability
Many losses occur not because of malware sophistication, but because of procedural shortcuts:
- Copying from the transaction history without verifying
- Trusting auto-filled addresses
- Skipping test transactions
Irreversibility amplifies small mistakes.
How to Reduce This Risk
- Verify middle characters of addresses, not just edges.
- Use address whitelisting for recurring transfers.
- Prefer QR scanning when feasible.
- Regularly review wallet permissions.
- Limit installation of non-essential applications.
- Avoid storing seed phrases digitally.
Address discipline is a low-effort, high-impact defense.
Risk #3: Public WiFi & “Evil Twin” Networks
Public WiFi introduces network-layer vulnerabilities.
An “Evil Twin” attack replicates a legitimate WiFi network name but routes traffic through attacker-controlled hardware. Devices often auto-connect to stronger signals.
Attackers may:
- Serve phishing login pages
- Capture credentials
- Inject malicious scripts
- Monitor unencrypted traffic
Why This Works
Users often assume:
- Familiar network names are safe
- HTTPS eliminates all risk
- A coffee shop environment is benign
While encryption reduces direct interception, phishing and credential harvesting remain viable within compromised network environments.
Network trust assumptions are frequently misplaced.
Compound Risk with Wallet Usage
When connecting to exchanges, approving smart contracts, or accessing DeFi interfaces, network integrity matters.
Even a well-designed wallet cannot protect against credential theft caused by phishing overlays delivered through malicious access points.
How to Reduce This Risk
- Disable auto-join for public networks.
- Use cellular data for financial transactions.
- Use reputable VPNs with kill-switch functionality.
- Avoid conducting sensitive financial activity on public WiFi.
- Manually verify website URLs before login.
The safest public network transaction is the one you postpone.
Risk #4: Physical Device Compromise
Crypto risk is not purely digital.
If your phone is stolen while unlocked, attackers may immediately access wallet apps and transfer funds. If forced to unlock a device under coercion, similar exposure exists.
Unlike traditional banks, blockchain transactions settle quickly and cannot be reversed.
Why This Works
Mobile wallets prioritize usability:
- Quick biometric access
- Seamless transaction approvals
- Cached sessions
If large balances are stored on the device, physical possession becomes equivalent to financial control.
Travel & Opportunistic Theft
Risk increases during:
- Travel
- Public transportation
- Conferences
- High-density environments
Mobile devices are among the most frequently stolen personal items globally.
How to Reduce This Risk
- Use strong alphanumeric passcodes.
- Enable wallet-level PIN or secondary authentication.
- Enable device auto-lock with short timeout.
- Use hidden wallets or passphrase features when available.
- Store only limited funds on mobile devices.
Risk scales with value stored.
Risk #5: Irreversible Transactions & Network Errors
Blockchain transactions are deterministic. Once signed and confirmed, they cannot be undone.
Common user errors include:
- Sending assets on unsupported networks
- Confusing wrapped tokens with native tokens
- Sending funds to contract addresses
- Misreading bridge instructions
- Misinterpreting address formats
As ecosystems become more complex, user error probability increases.
Why This Works
Cross-chain ecosystems create identical asset tickers across multiple networks. Wallet interfaces abstract complexity, but user responsibility remains.
The blockchain does not assess context. It executes instructions.
The “Pre-Flight” Protocol
Before confirming significant transactions:
- Verify network compatibility on both sides.
- Confirm token standard (ERC-20, BEP-20, etc.).
- Send a small test transaction first.
- Pause and review transaction details carefully.
- Avoid acting under urgency.
A one-minute verification routine can prevent irreversible loss.
Common Mistakes Mobile Wallet Users Make
Most mobile wallet security failures occur at the intersection of technology and behavior.
Frequent mistakes include:
- Storing full portfolios in hot wallets.
- Ignoring wallet permission revocations.
- Reusing passwords across services.
- Failing to back up seed phrases securely.
- Approving contracts without reviewing details.
- Acting on urgency-based messages.
Security discipline outperforms advanced technical knowledge.
For a complete list of security habits to audit, see:
Crypto Wallet Hygiene Checklist: 15 Rules to Avoid Getting Hacked
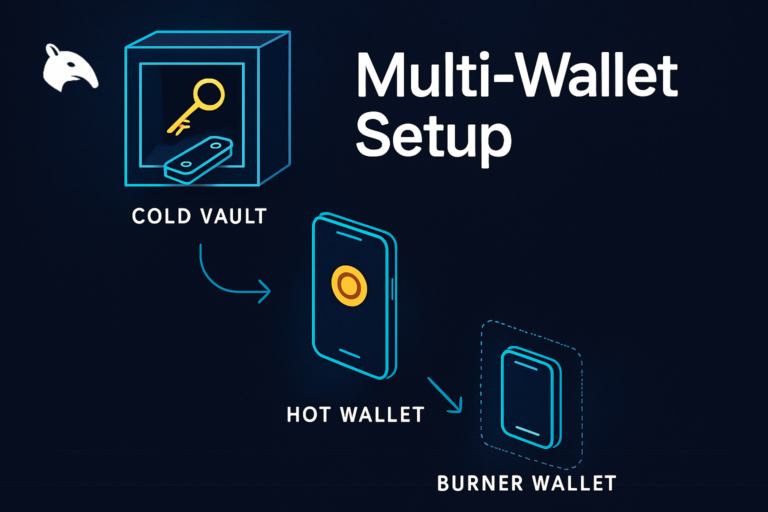
The Practical Solution: Separate Spending from Storage
The safest framework is the separation of roles.
Mobile wallet:
- Small working balance
- Daily transactions
- DeFi interaction
Hardware wallet:
- Long-term holdings
- High-value assets
- Reduced online exposure
Hardware wallets isolate private keys and require physical confirmation for signing.
Even if your mobile device is compromised, the attacker cannot sign transactions without the physical hardware device.
For hardware wallet comparisons, see:
- [Ledger Nano X Review 2026: Is It Still the Best Hardware Wallet?]
- [Ledger Nano X vs. Trezor Safe 7: Which Wins in 2026?]
- [Best Crypto Wallets for Beginners 2026: Safe, Easy & Verified]
- [Exchange Withdrawals Will Pause Again: The 2026 Self-Custody Survival Guide]
Reducing exposure is more effective than responding after loss.
Frequently Asked Questions
Are mobile wallets safe for small amounts?
Yes, when balances are limited and proper security practices are followed.
Is SMS 2FA better than no 2FA?
Yes, but hardware-based authentication provides significantly stronger protection.
Can a VPN eliminate WiFi risk?
No. It reduces interception risk but does not eliminate phishing or social engineering threats.
What is address poisoning?
An attack where lookalike addresses are introduced into transaction history to trick users into copying incorrect destinations.
Is Face ID sufficient protection?
Biometrics improve convenience but should be combined with layered security practices.
Do beginners need hardware wallets?
If holdings exceed what you can afford to lose, hardware storage should be strongly considered.
Final Thoughts
Mobile wallets are powerful tools.
They are not vaults.
Mobile wallet security is about reducing exposure, minimizing attack surface, and building layered defenses.
Operational discipline is more important than fear.
Structure reduces risk. Separation reduces damage. Verification prevents catastrophe.
Self-custody rewards responsibility.