OpSec in crypto means operational security: the habits, systems, and decisions you use to protect keys, devices, accounts, identity details, and wallet behavior from theft or manipulation. It is broader than wallet choice alone. A strong hardware wallet helps, but poor OpSec can still expose you through phishing, social engineering, device compromise, account recovery abuse, or careless public information sharing.
A useful mental model is to think of OpSec as the security of your whole operating environment, not just the security of one device. In crypto, attackers often target the person, the account stack, or the workflow around the wallet long before they try to target the wallet itself.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
For a closely related follow-up, see Self Custody vs Custodial Wallets: Which Fits Your Risk?.
- OpSec is about the full environment: It includes devices, accounts, recovery methods, communications, and behavior, not only wallets.
- Crypto losses often come from operational failure: Poor verification, weak account hygiene, or risky habits often matter more than protocol-level issues.
- Good tools cannot replace bad habits: A hardware wallet, strong password, or secure app does not protect you if you approve the wrong action or trust the wrong person.
- Threat modeling matters: Your OpSec should match what you hold, how often you move funds, and what kind of attacker you realistically care about.
- The goal is reducing attack paths: Better OpSec means fewer easy routes to your assets, accounts, and identity.
What OpSec Actually Covers
Operational security covers the real-world conditions around your crypto activity. That includes where your seed phrases live, what device you use to sign transactions, how your exchange accounts recover access, how public your balances and identity are, and what kind of links, files, or messages you allow into your workflow.
For a closely related follow-up, see How Much Crypto Should You Keep on an Exchange? A Safer Framework.
This is why OpSec matters even for technically strong users. A secure wallet setup can still fail if the surrounding system is weak. The wallet may be safe, but the email account, phone number, browser, or support workflow around it may not be.
Why OpSec Matters So Much in Crypto
Crypto is unusually sensitive to operational mistakes because transactions are hard to reverse, recovery options are limited, and attackers are strongly incentivized to go after people who control private keys or high-value accounts. Unlike many traditional systems, there may be no chargeback, no fraud desk, and no easy “undo” after a successful theft.
Real-world example: a user may have strong key storage but still lose funds because an exchange login was recovered through a weak email account, or because a fake support contact pushed the user into revealing information outside the wallet flow itself. The cryptography held. The operational layer failed.
What Good Operational Security Usually Includes
- Key protection: Seed phrases and private keys are stored offline and are never typed into random sites or support chats.
- Device hygiene: High-value wallet actions are kept away from messy browsers, unnecessary extensions, and high-risk downloads.
- Account security: Email, exchange logins, and recovery paths are hardened because they are often targeted directly.
- Behavioral discipline: The user verifies before signing, slows down under urgency, and treats unsolicited contact as suspicious.
- Privacy awareness: Public sharing of balances, wallet structure, travel plans, or device habits is limited so attackers have less targeting context.
Why Threat Models Matter
OpSec is not one fixed checklist that applies equally to everyone. It depends on what you are protecting and from whom. Someone holding a modest amount for long-term savings has a different threat model from a protocol developer, active trader, or public-facing founder. The right question is not “What is the maximum security setup possible?” but “What attack paths are actually relevant to my situation?”
Operator insight: users often either underreact or overreact. Some ignore obvious risks because they think attackers only target whales. Others create elaborate systems they cannot manage consistently. Good OpSec sits between those extremes. It is realistic, repeatable, and matched to the actual value and exposure involved.
How It Connects to Real Theft Paths
The most relevant local baseline is How Crypto Gets Stolen. That article explains the main routes attackers use. OpSec is the discipline of closing or narrowing those routes before they are tested against you.
For example, phishing attacks exploit verification failure. Social engineering exploits communication and trust failure. Device malware exploits hygiene failure. SIM swapping exploits account-recovery weakness. OpSec in crypto is the broader practice of not letting those surrounding layers become the cheapest path to loss.

What OpSec in Crypto Is Not
It is not just “being paranoid.” It is not just using a hardware wallet. It is not just memorizing scam slogans. And it is not a promise that nothing bad can happen. OpSec is a risk-reduction practice, not a perfect shield.
This distinction matters because some users confuse security products with security behavior. A strong device can be part of good OpSec, but a good device used inside a weak routine still leaves real attack paths open.
Common Areas Where OpSec Breaks Down
- Communication channels: Users trust DMs, private chats, or spoofed support workflows too quickly.
- Recovery paths: Email, SMS recovery, or weak password reuse make stronger wallet layers less meaningful.
- Device crossover: The same laptop or browser is used for everything from random downloads to high-value signing.
- Public oversharing: Holdings, travel habits, wallet screenshots, or infrastructure details reveal targeting clues.
- Workflow urgency: Users rush through approvals, bridge steps, mint pages, or login alerts without stopping to verify.
How It Relates to Phishing and Social Engineering
Phishing and social engineering are some of the clearest examples of poor OpSec being exploited. If you want the narrower follow-ups, the best local references are What Is Crypto Phishing? and Social Engineering in Crypto. Those explain the attack categories. OpSec is the broader habit system that makes those attacks harder to land in the first place.
Real-world scenario: a user receives an urgent wallet-warning DM, clicks a verification link, and moves into a private support flow. The attack works not because the site had extraordinary technical power, but because the user’s communication and verification OpSec failed first.
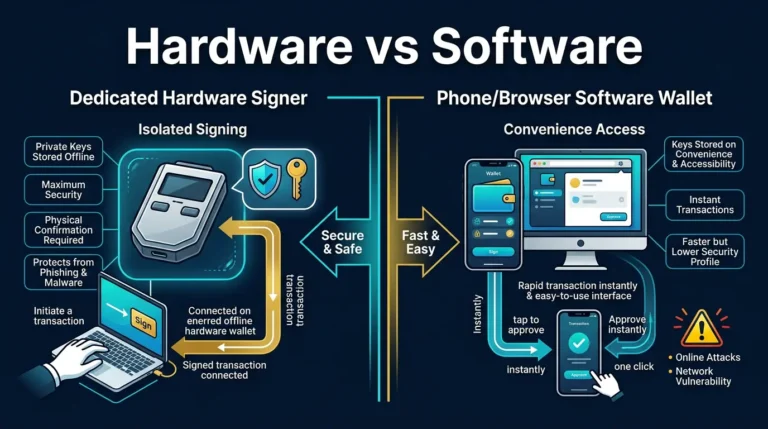
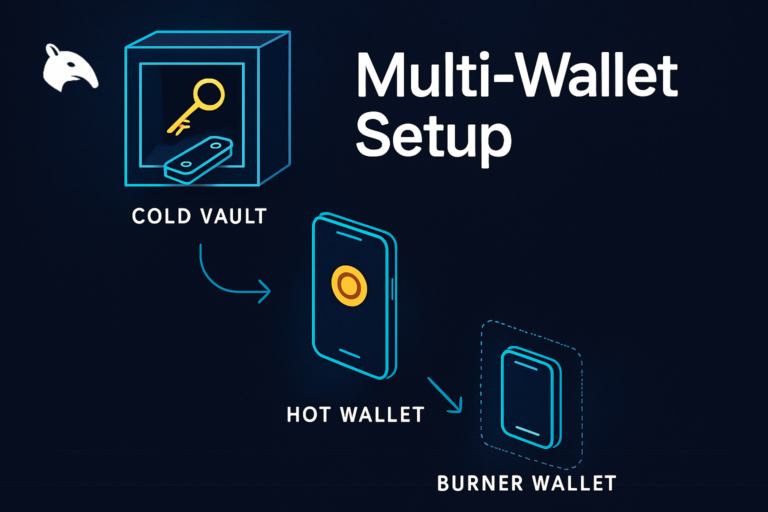
How Wallet and Account Separation Improve OpSec
Role-based separation is one of the most practical OpSec upgrades because it limits how much any one compromise can reach. Different wallets for storage, routine activity, and riskier experiments reduce the chance that one bad interaction exposes everything. The most relevant local bridge here is What Is a Multi-Wallet Strategy in Crypto?.
Similarly, separate account layers matter too. A hardened email for exchange recovery, stronger MFA choices, and less public overlap between online identity and custody details all improve the operating environment around the wallet, not just the wallet itself.
Practical Usage: How to Think About Your Own OpSec
A practical shortcut is this: good OpSec means the attacker has to beat more than one weak habit to reach anything important.
Risks and Common Mistakes
- Treating OpSec like a product purchase: A user may buy a hardware wallet or security tool and assume the problem is solved, even though the surrounding accounts, recovery paths, and behavior remain weak.
- Ignoring the account layer: A carefully protected wallet can still be undermined if the email, exchange login, or phone number tied to recovery is easy to take over.
- Over-sharing publicly: Posting balances, device setups, travel timing, or wallet screenshots can give attackers targeting context they did not have before.
- Reacting under urgency: Many operational failures happen when the user treats speed as more important than verification during a login scare, support message, mint, or wallet alert.
Sources
- CISA: Operational Security Basics
- CISA: Secure Our World
- FBI IC3: North Korea Aggressively Targeting Crypto Industry with Well-Disguised Social Engineering Attacks
Frequently Asked Questions
What does OpSec mean in crypto?
It means operational security: protecting the devices, accounts, keys, recovery paths, and habits around your crypto activity so attackers have fewer ways to reach your assets.
Is OpSec in crypto just about wallets?
No. It also includes email security, exchange account recovery, device hygiene, identity exposure, communication habits, and how you verify requests before signing or logging in.
Why is OpSec important in crypto?
It is important because many crypto losses happen through phishing, social engineering, malware, account takeover, or operational mistakes rather than through broken blockchain security.
Does a hardware wallet solve OpSec by itself?
No. A hardware wallet improves one part of security, but weak email recovery, sloppy signing, risky browser behavior, or poor verification habits can still create other attack paths.
What is the first step to better OpSec in crypto?
The first step is identifying what assets and accounts matter most, then asking what the easiest realistic path to compromise currently is. Good OpSec starts with that map.