Last Updated on April 18, 2026 by Snout0x
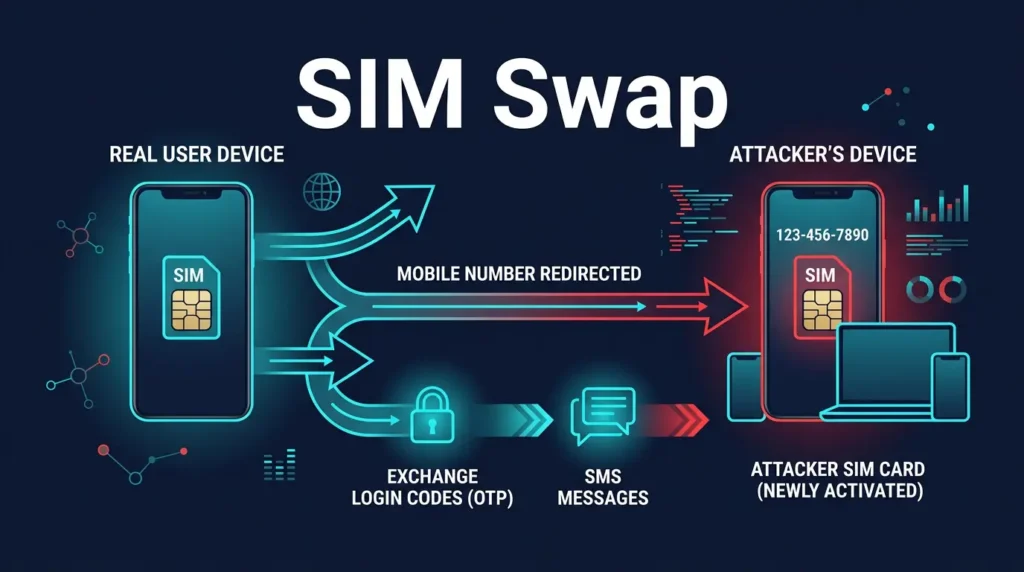
A SIM swap attack in crypto is an account-takeover attack where an attacker gains control of your phone number by convincing a mobile carrier to move it to a SIM card they control. Once that happens, text messages and calls meant for you may start reaching the attacker instead. In crypto, that matters because many exchange accounts, email accounts, and recovery flows still rely on SMS codes or phone-number verification.
The key idea is that the attacker is not breaking the blockchain itself. They are attacking the identity layer around your accounts. If your phone number is part of login, password reset, or withdrawal confirmation, the number becomes a weak point. A SIM swap turns that weak point into direct access leverage.
This content is for educational purposes only and should not be considered financial or investment advice.
Key Takeaways
- A SIM swap is a phone-number takeover: The attacker gains control of your mobile number through the carrier layer.
- It matters most for account-based crypto systems: Exchanges, broker apps, and email accounts are the main targets.
- SMS 2FA is the weak point: If security codes depend on the phone number, the attacker may receive them.
- The blockchain is not being hacked: The attack targets recovery, login, and identity flows around your accounts.
- Authenticator apps and security keys reduce this path: They are usually stronger than SMS for meaningful crypto accounts.
How a SIM Swap Attack Works
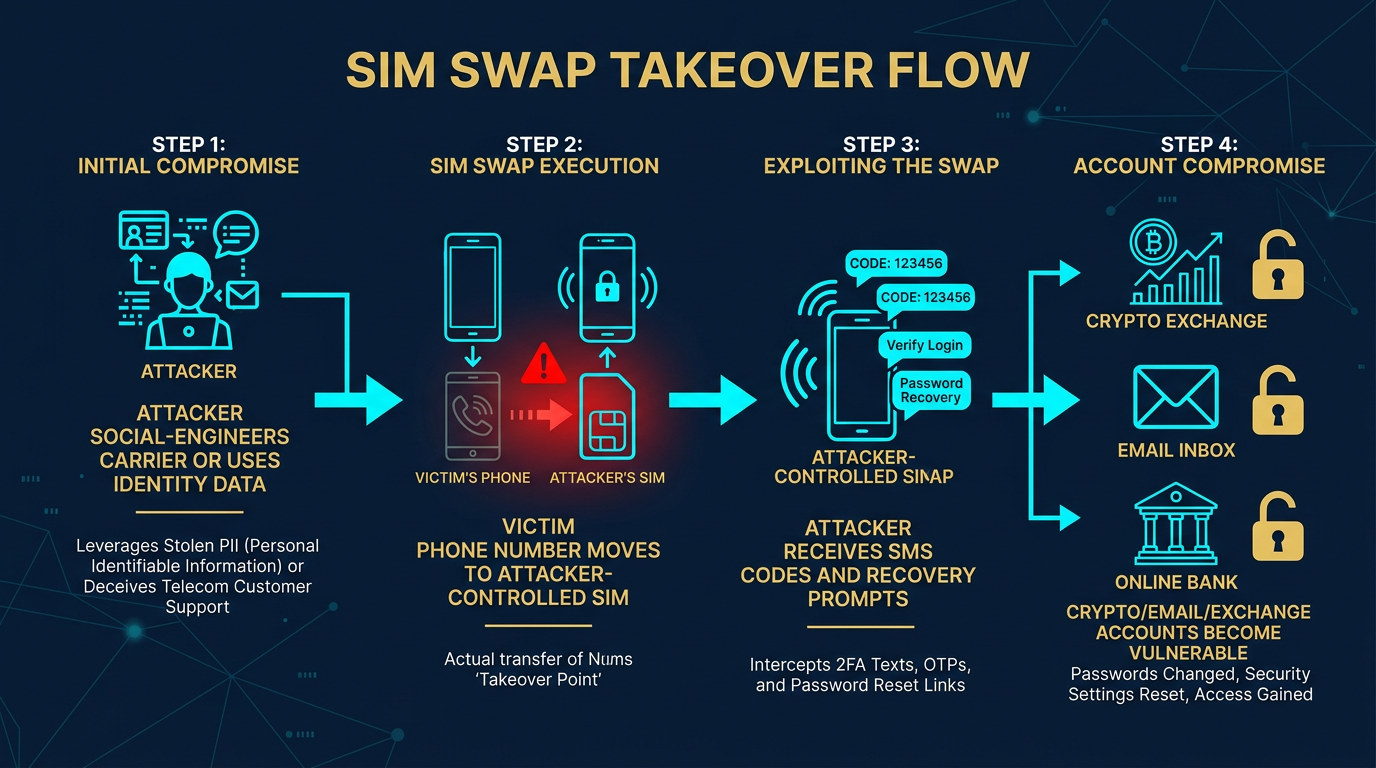
The basic pattern is simple. The attacker gathers enough personal information to impersonate you with the carrier or exploit weak carrier-account support processes. They then persuade the carrier to move your number to a new SIM card or device under their control. After the switch, calls and texts that used to reach your phone may start reaching theirs.
Once the attacker controls the number, they can begin targeting services that treat the phone as proof of identity. That can include SMS login codes, password resets, account unlock requests, and support workflows that assume phone-number control means legitimate ownership.
Why It Is Relevant to Crypto
Crypto accounts are attractive targets because access can turn into withdrawals, trading abuse, or account recovery changes very quickly. If an exchange uses SMS 2FA or a linked email account uses SMS as part of recovery, then the attacker may be able to move from phone-number control to account control faster than in many ordinary consumer services.
This is why the best local foundation pages here are What Is 2FA in Crypto? and SMS vs Authenticator 2FA for Crypto. SIM swaps matter because they attack one of the most common but weaker second-factor choices.
What Attackers Usually Try to Reach
- Exchange accounts: SMS codes, recovery prompts, or withdrawal confirmations may depend on the phone number.
- Email accounts: If the inbox can reset exchange access, email becomes a critical target too.
- Broker or payment apps: Any account tied to stored value or transfer authority may become part of the path.
- Support and recovery workflows: Weak identity checks can let an attacker convert number control into broader account changes.
Operator insight: many users think of their phone number as contact information, not as a security dependency. But once SMS is part of login and recovery, the carrier effectively becomes part of the custody model.
What a SIM Swap Does Not Usually Do
A SIM swap does not directly give the attacker your self-custody seed phrase or private keys. It also does not let them break into a hardware wallet by itself. The danger is indirect but powerful: if your exchange, email, or app accounts depend on the phone number, number control can become the first step in taking over systems that do matter financially.
That is why this attack belongs more to the identity and recovery layer than to the wallet-signing layer. It is different from malware, seed-phrase theft, or blind-signing attacks even though all can end in loss. The distinction between identity-layer and code-level attacks is explored more directly in the phishing vs smart contract drains comparison.
Real-World Sequence of a Crypto SIM Swap
A common mistake is not recognizing the service loss as a security signal. If a phone suddenly loses service for no obvious reason, and especially if important accounts use SMS 2FA, that should be treated as a possible account-security emergency.
How This Connects to Phishing and Social Engineering
SIM swaps often depend on information gathered through broader social engineering. Attackers may use phishing, breach data, or public profile details to answer carrier questions convincingly or to target support staff with enough context to sound legitimate. The phone takeover is usually one step in a larger identity attack, not a random isolated trick.
For the behavior side of that, the strongest local follow-up is Crypto Wallet Phishing Attacks. Different attack types, same broader pattern: the attacker is trying to exploit the trust and recovery layers around your assets.
Practical Usage: How to Think About This Risk
- Treat phone-number security as account security: If the number can receive login or reset codes, it is part of the threat model.
- Prefer non-SMS second factors: Authenticator apps and hardware security keys usually reduce SIM-swap exposure.
- Protect the email behind the exchange: Email recovery often matters as much as the exchange login itself.
- Watch for sudden service loss: Unexpected SIM failure can be an urgent warning sign, not just a carrier annoyance.
- Limit value on weaker account stacks: If an important service still depends on SMS, size exposure accordingly.
A useful rule is this: if your phone number can help reset access to money, your mobile carrier is already part of your financial security system whether you intended that or not.
Risks and Common Mistakes
- Assuming SMS is strong enough by default: Better than no second factor, but weaker than alternatives for valuable crypto accounts.
- Ignoring the email account: An attacker may use phone control to recover the inbox that can reset everything else.
- Treating carrier issues as harmless support problems: Sudden service loss can be a real attack indicator.
- Thinking self-custody makes identity-layer attacks irrelevant: Exchange and email access can still matter even for users who mostly self-custody.
- Using one phone number as the sole recovery anchor: Centralizing identity recovery around the number increases blast radius if it is taken over.
Sources
- CISA: SIM Swapping and Personal Account Risk
- FBI IC3: Cryptocurrency Theft via SIM Swapping
- NIST Digital Identity Guidelines
Frequently Asked Questions
What is a SIM swap attack in crypto?
It is an attack where someone takes over your phone number so they can receive SMS codes and recovery prompts tied to crypto-related accounts.
Can a SIM swap steal a self-custody wallet directly?
Not directly. The bigger danger is usually to exchange, email, and account-recovery systems that depend on the phone number.
Why are SIM swaps especially dangerous for exchange users?
Because SMS login codes, password resets, and recovery prompts may all become reachable by the attacker once they control the number.
What is one warning sign of a SIM swap?
A sudden unexplained loss of phone service can be a warning sign, especially if important accounts rely on SMS-based security.
What is the best upgrade from SMS for crypto accounts?
Authenticator apps are usually the best common upgrade, and hardware security keys can be stronger still where supported.