Last Updated on April 19, 2026 by Snout0x
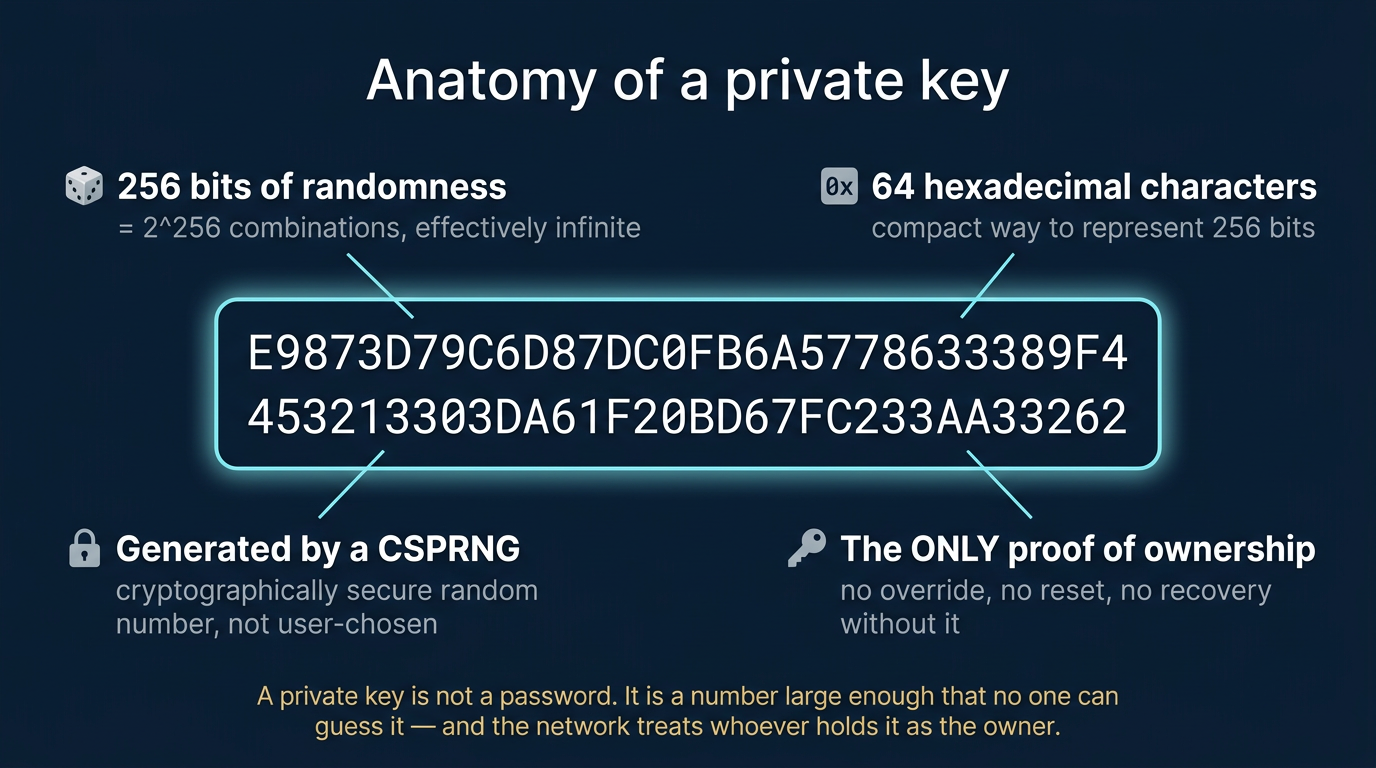
A private key is a cryptographically generated string of characters that grants exclusive control over a blockchain wallet. It is not a password in the traditional sense. It is a mathematical proof of ownership. Anyone who holds a private key can authorize transactions from that wallet, with no further verification required by the network.
This content is for educational purposes only and should not be considered financial or investment advice.
Simple Definition
A private key is a unique cryptographic number that proves ownership of a blockchain address. Whoever holds it can authorize any transaction from that address. There is no override, no reset, and no recovery path without it.
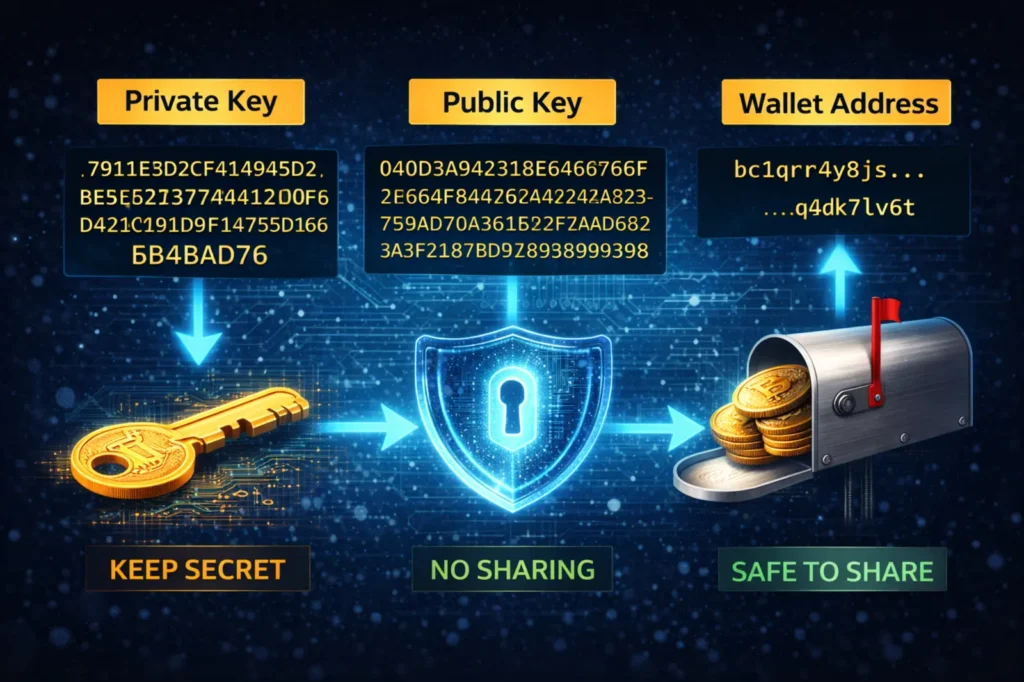
A private key is a 256-bit number, usually represented as a 64-character hexadecimal string. It is generated randomly when a new wallet is created and is mathematically linked to a public key, which in turn produces the wallet address used to receive funds.
The relationship between these values moves in one direction only. Your wallet address is derived from your public key. Your public key is derived from your private key. You can share your public address with anyone without risk. You must never share your private key with anyone, under any circumstances.
A useful comparison: the public address is like a mailbox. Anyone can deposit funds into it. The private key is the only physical key that opens it. Without that key, the mailbox is permanently sealed. There is no locksmith on a blockchain.
Why It Matters
Blockchain networks do not have customer support, password resets, or account recovery processes. Ownership on a blockchain is determined entirely by cryptographic proof. That proof is the private key.
When you hold crypto on an exchange, the exchange holds private keys on your behalf. You have an account balance in their system, not direct ownership of on-chain assets. This is what the phrase “not your keys, not your coins” means in practice. If that exchange freezes withdrawals, becomes insolvent, or suffers a breach, your ability to access those funds depends entirely on what that company does next. The self-custody survival guide covers this risk in detail.
When you move to self-custody, the responsibility shifts entirely to you. The private key becomes the only mechanism that proves your right to authorize transactions. Lose it, and that proof is gone. There is no recovery path at the protocol level. Funds in a wallet whose private key is unknown are permanently inaccessible, regardless of their value.
This is why private key management sits at the foundation of every serious approach to crypto security. It is not an advanced topic. It is the baseline concept every crypto holder needs to understand before moving any funds off a custodial platform.
How It Works
When a blockchain transaction is broadcast, the network needs to verify that the person initiating it actually owns the sending wallet. This verification happens through public key cryptography, without any central authority involved.
The sequence works as follows:
- A wallet is created. The wallet software generates a private key using a cryptographically secure random number generator.
- The public key is derived from the private key using elliptic curve multiplication. This is a one-way mathematical function. It is computationally infeasible to reverse the process and recover the private key from a public key.
- This asymmetric cryptographic model is formally defined in standards such as the NIST Digital Signature Standard, which outlines how digital signatures verify authenticity without revealing private key material.
- The wallet address is derived from the public key through a hashing function. This is the address you share when receiving funds.
- When you send a transaction, your wallet uses the private key to create a digital signature specific to that transaction. The signature proves authorization without ever exposing the private key itself.
- The network verifies the signature against your public key. If it matches, the transaction is valid and broadcast to the chain.
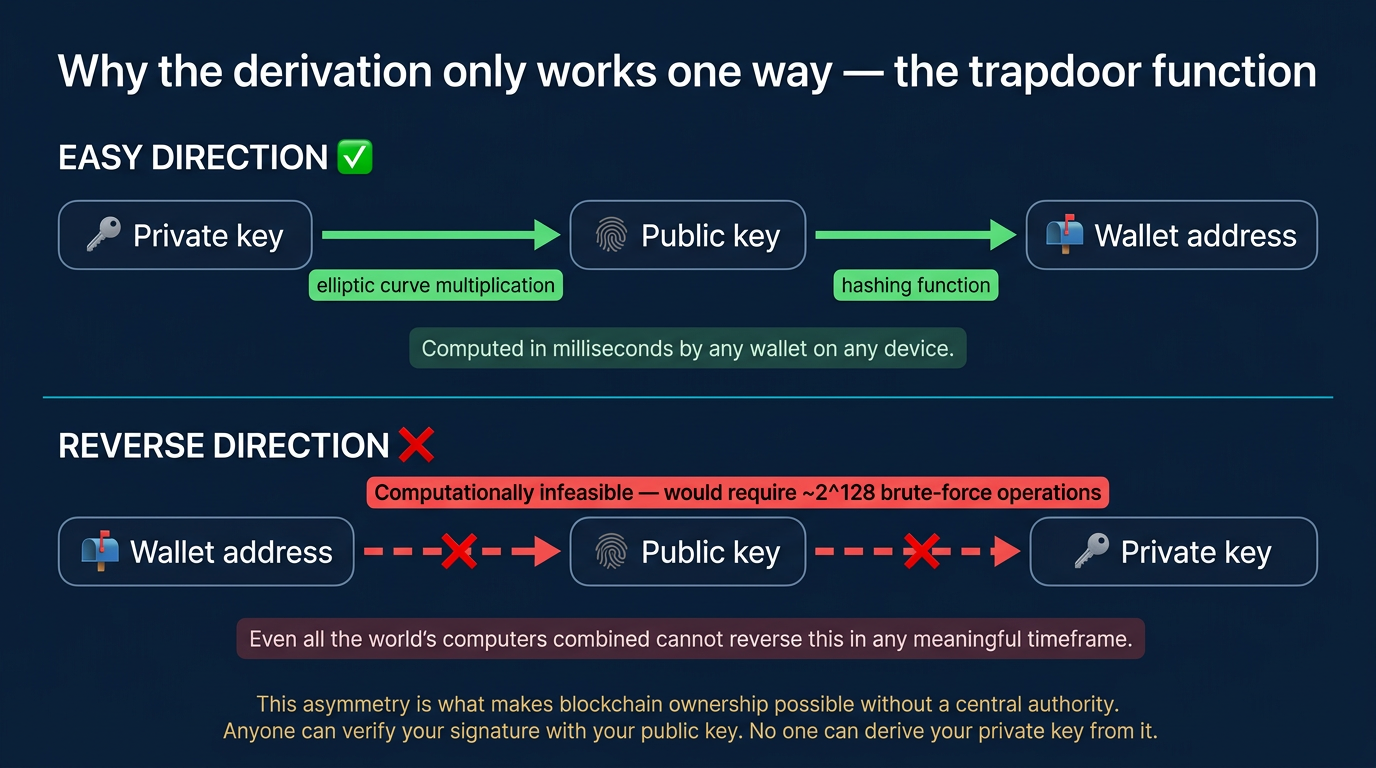
This is why blockchain transactions are trustless. No institution needs to verify your identity or approve your transfer. The cryptographic math handles verification directly.
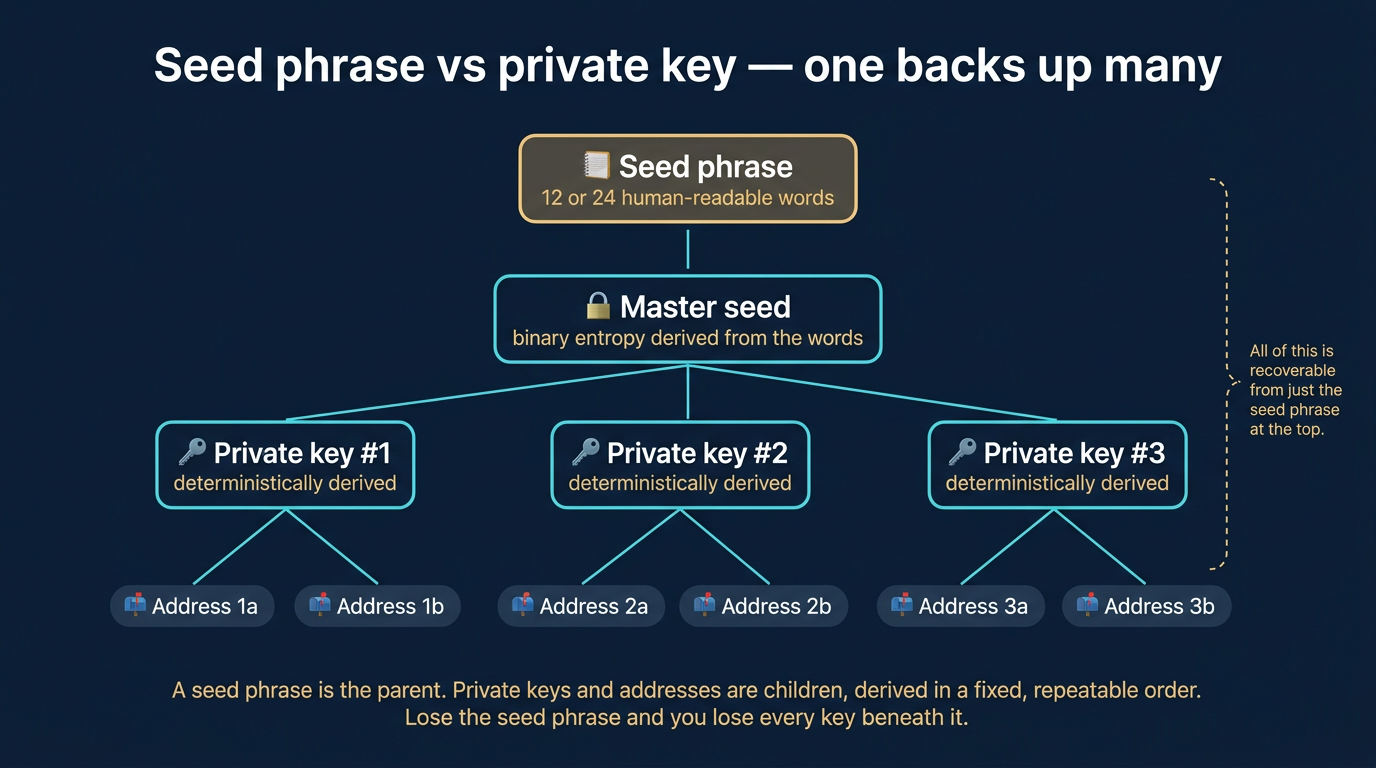
Most users never interact with a raw private key. Wallet software handles the signing process in the background. Many wallets represent the key material as a seed phrase instead, a set of 12 or 24 human-readable words that encodes the master seed used to generate private keys for that wallet. The seed phrase and private key are different but closely related. Understanding how they connect is essential for anyone managing their own custody.
Common Mistakes
The most frequent private key losses are not caused by sophisticated attacks. They result from operational errors that expose key material unnecessarily or eliminate recovery options.
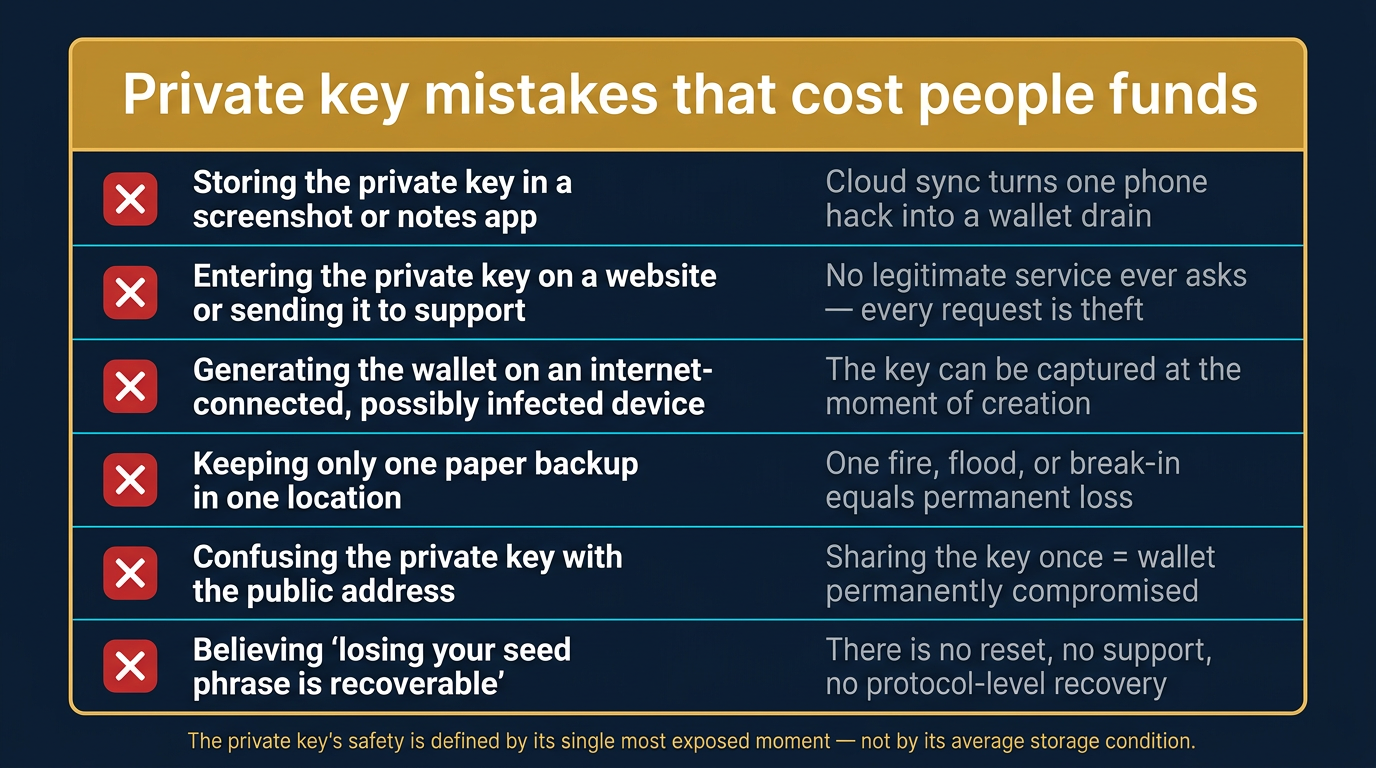
Storing a private key in a screenshot. Screenshots on mobile devices sync automatically to cloud storage in most default configurations. A compromised email or cloud account then becomes a compromised wallet.
Saving a private key in an email or a notes app. Email accounts are primary phishing targets. Cloud-synced notes carry the same exposure profile as any online account. Neither is an appropriate place to store key material.
Entering a private key on a website. No legitimate wallet service, exchange, or support team will ever request your private key. Any platform or person asking for one is attempting theft. This pattern appears in a wide range of documented losses, including the scenarios covered in this guide to unsafe crypto habits that cost users money.
Generate a wallet on an internet-connected device. Keys generated on a device already infected with malware may be captured at the moment of creation. Offline key generation significantly reduces this exposure.
Keeping only one backup copy. A single paper copy stored in one location is one house fire or one break-in away from a permanent loss. Redundancy across secure, physically separate locations is a practical requirement, not an optional extra.
Confusing a public address with a private key. New users sometimes share a private key when someone asks for their wallet address. The two are entirely different. A public address is safe to share. A private key shared even once should be considered permanently compromised, and funds in that wallet should be moved immediately.
Security and Risk Considerations
Private key security is the primary attack surface in self-custody. Understanding the threat profile for each storage approach helps users make decisions appropriate to their situation and holdings.
Hardware wallets store private keys on a dedicated physical device that never exposes them to an internet-connected computer. Transaction signing happens inside the device itself. Even if the connected computer is compromised, the private key remains isolated. This is why hardware wallets are the standard recommendation for significant holdings. Whether a hardware device is truly isolated from external exposure is a question the article on cold storage paranoia examines directly.
Software wallets store private keys on the device running the wallet application. Mobile and desktop wallets are more convenient for frequent transactions but carry greater exposure. Device compromise, unauthorized physical access, or malware can expose the key without the user’s knowledge.
Passphrase protection is an optional layer supported by many wallets. A crypto passphrase adds a user-defined word or phrase on top of the key material, creating a separate wallet that cannot be accessed without both. This significantly limits the damage from a physical seed phrase exposure, but introduces its own management requirements. A forgotten passphrase is as final as a lost private key.
Physical storage risks apply to users keeping private keys or seed phrases written on paper or stamped on metal. These copies are only as secure as their physical location. A backup stored in a single place with no redundancy is a single point of failure against fire, flooding, and theft. All three have caused real, documented losses.
Third-party custody transfers the private key risk to another entity. When a platform holds keys on your behalf, that platform becomes the target for attackers, regulators, and creditors. Exchange hacks, platform insolvencies, and withdrawal freezes have all resulted in users losing access to funds they believed were theirs. Understanding when and how to take self-custody is a foundational security decision.
Operational security is where most actual losses occur. The most sophisticated hardware setup can be undermined by a single careless moment: entering a key on a phishing site, responding to a fake support agent, or copying a key to the clipboard while screen-sharing. The private key’s security is defined by the most exposed moment in its entire history. Practices that minimize exposure moments are what separate secure custody from wishful thinking.
Frequently Asked Questions
What happens if I lose my private key?
If you lose your private key and have no backup such as a seed phrase, the funds in that wallet are permanently inaccessible. There is no recovery mechanism at the blockchain level. No company, developer, or authority can restore access.
Is a private key the same as a seed phrase?
No, but they are closely related. A seed phrase encodes the master seed used to derive private keys for a wallet. From a single seed phrase, multiple private keys can be generated. Losing your seed phrase is functionally equivalent to losing your private keys for most practical purposes.
Can someone steal my crypto using only my public wallet address?
No. A public address can only be used to receive funds. Moving funds out of a wallet requires the private key. Sharing your public address is safe and is required for receiving any crypto.
Should I store my private key digitally?
Digital storage carries a significant risk unless the storage medium is encrypted, completely offline, and physically secured. For most users, offline storage on paper or metal with physically separate backup copies is the recommended approach.
What is the difference between a private key and a passphrase?
A private key is generated by the wallet and constitutes cryptographic proof of ownership. A passphrase is an optional, user-defined addition that creates a separate wallet layer on top of the key material. The passphrase does not replace the private key. It adds authentication requirement on top of it.